Tor and a VPN are both tools that use a combination of proxies and encryption to make it difficult for snoopers to track you. While they share some similarities, the key difference is that Tor is for anonymity, and a VPN is for privacy. The two can be used in tandem to further bolster both privacy and anonymity. This article will cover the best VPNs for the Tor browser and explain how to use a Tor VPN.
We get into a lot of detail below, so if you only have time for a summary, here is our list of the best VPNs for Tor:
- NordVPN Best VPN for Tor. Fastest VPN on the market. Military-grade encryption, with special Tor over VPN servers. 30-day money-back guarantee.
TIP In our testing we found that the cheapest NordVPN plan (Standard) works perfectly for Tor. - Surfshark Best low-cost VPN for Tor. Decent speeds, no connection limits, and impressive unblocking abilities.
- ExpressVPN Fast veteran provider that accepts Bitcoin and has an Onion site. Great for streaming, torrenting, or just general browsing.
- CyberGhost Has excellent security, fast connection speeds, and zero logs. Another good budget VPN for Tor.
- PrivateVPN Simple to use VPN for Tor. Fast servers, and no logs. Also works well with streaming sites.
- IPVanish Advanced security, zero logs, and fast. Also popular with Kodi and torrent users.
Related: What is Tor? How to use it safely
How to use Tor with a VPN
We’ll use Tor Browser as an example, though there are several ways to connect to Tor. With the Tor Browser installed:
Here’s how to use a VPN with Tor:
- Sign up with a VPN. Our top recommendation is NordVPN.
- Download and install the VPN app.
- Run the app and select a VPN server.
- Hit the Connect button and wait for the app to confirm the connection.
- Open the Tor Browser and surf the web.
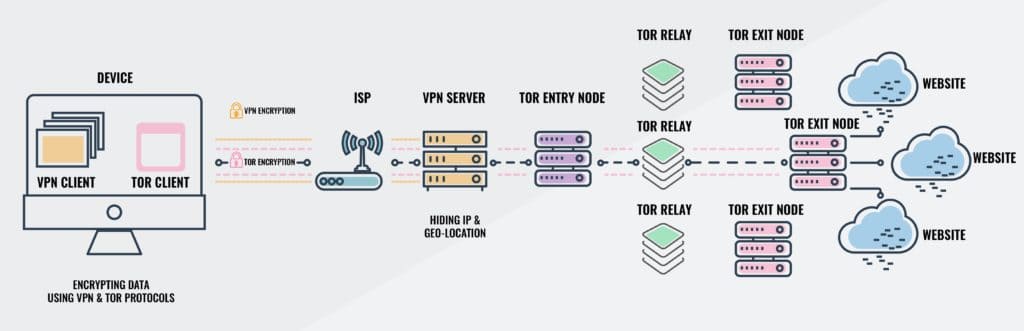
This setup sends your internet traffic first through the VPN server, and then through the Tor network. That means your data goes through two phases of encryption before it ever leaves your device: once by the VPN and then again by Tor. Your internet service provider can’t see what’s in the VPN’s encrypted tunnel and, therefore, cannot detect that Tor is being used.
WANT TO TRY THE TOP VPN RISK FREE?
NordVPN is offering a fully-featured risk-free 30-day trial if you sign up at this page. You can use the VPN rated #1 for Tor without any restrictions, limits, or caps for a month—great if you want to experiment with all of its privacy features before making a decision.
There are no hidden terms—just let customer support within 30 days if you decide NordVPN isn't right for you and you'll receive a full refund. Start your NordVPN trial here.
Best VPNs for Tor browser and the dark web
We’ve evaluated the best VPNs for Tor based on the following criteria:
- Features designed specifically for Tor users
- No logs policy
- Strong encryption
- Anonymous payment methods
- Fast connection speeds
The best VPNs for Tor – At a glance
We’ve compared the most important features of the top VPNs here. Prefer to read the in-depth reviews? Start with NordVPN – our #1 choice for Tor.
| No value | NordVPN | Surfshark | ExpressVPN | CyberGhost | PrivateVPN | IPVanish |
|---|---|---|---|---|---|---|
| Website | NordVPN.com | Surfshark.com | ExpressVPN.com | Cyberghost.com | PrivateVPN.com | IPVanish.com | Ranking for Tor: | 1 | 2 | 3 | 4 | 5 | 6 | Avg Speed (Mbps) | 100+ Mbps | 100+ Mbps | 100+ Mbps | 100+ Mbps | 39 Mbps | 100+ Mbps | Popular Sites Unblocked | 95% | 88% | 86% | 85% | 85% | 70% | Simultaneous Connections | 10 | Unlimited | 8 | 7 | 10 | Unlimited | Devices Supported | Windows, MacOS, iOS, Android, Linux | Windows, MacOS, iOS, Android, Linux, Amazon Fire TV, Apple TV | Windows, MacOS, iOS, Android, Linux, Smart TVs, Routers | Windows, MacOS, Linux, iOS, Android | Windows, MacOS, iOS, Android, Amazon Fire TV | Windows, MacOS, iOS, Android |
| Best deal (per month) | $3.09 Up to 69% off + 3 months FREE | $2.29 Save 85% on a 2 year Starter plan | $6.67 SAVE: 49% + 3 months free | $2.03 SAVE 84% on the 2 year plan | $2.00 Save 85% on a one year plan + 24-months free | $2.75 SAVE 78% on the 2 yr plan |
In addition to the above criteria, we run a wider program of extensive VPN testing and research. You can read more here on our VPN testing methodology.
1. NordVPN

Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
- FireTV
Website: www.NordVPN.com
Money-back guarantee: 30 DAYS
NordVPN gives users access to specialized servers pre-configured with Tor over VPN, which means all traffic is first sent through the VPN and then automatically redirected through the Tor network. This is great if you have apps other than an internet browser that you’d like to use with Tor. A double-VPN option is also available, which could be used with the Tor browser for a total of two VPNs and the Tor network, if you can tolerate the speed hit. NordVPN also boasts a strict zero logs policy and 256-bit AES encryption. The company accepts Bitcoin.
Apps are available for Linux, Windows, MacOS, iOS, and Android.
Note that some experts object to Tor over VPN servers because NordVPN could hypothetically see what users are doing with their Tor connection by analyzing traffic before Tor encrypts it. NordVPN says it keeps zero logs, but if this is a concern, we recommend setting up Tor and the VPN independently.
Pros:
- Onion servers
- No logs
- Extremely high speeds
- Advanced security features
- Accepts bitcoin
Cons:
- A few servers didn’t work
Our score:
BEST FOR TOR:NordVPN is our first choice. Offers Tor-specific servers, exceptionally high speeds and secure connections. What’s more, it comes with a 30-day money-back guarantee, allowing you to try it risk-free.
Read our full NordVPN review.
2. Surfshark
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.Surfshark.com
Money-back guarantee: 30 DAYS
Surfshark has 3,200+ servers in more than 60 countries, so you should be able to get a fast connection regardless of where you are in the world. This VPN has a no-logging policy and secures your traffic with 256-bit AES encryption, a kill switch, and protection against IPv6, DNS, and WebRTC leaks. Making it a solid choice for a Tor browser VPN.
This service also has a couple of more advanced features to keep your online activity hidden. For instance, you can connect to multi-hop servers for even greater anonymity or speed up your other apps by using the split tunneling feature. Surfshark accepts Bitcoin, Ethereum, and Ripple payments, allowing you to sign up almost completely anonymously. Support is available 24/7 over live chat.
Surfshark offers iOS, Android, Linux, MacOS, and Windows apps. It also works with supported routers but must be configured manually.
Pros:
- Puts major emphasis on user security and privacy
- Has no connection limit
- Great unblocking ability
- Keeps no logs
- Good speeds
Cons:
- Menus could be better organized
Our score:
BEST BUDGET OPTION:Surfshark takes your security seriously, keeps no logs, and comes at a very reasonable price. Better still, it offers a 30-day money-back guarantee.
Read our full Surfshark review.
3. ExpressVPN
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.ExpressVPN.com
Money-back guarantee: 30 DAYS
ExpressVPN recently launched a .onion version of its website for users who want to anonymously create an account. The British Virgin Islands-based company accepts Bitcoin and sticks to a strict no-logs policy. Some non-identifying information is logged such as dates (not times), choice of server location, and total amount of data transferred each day. Cutting-edge encryption is used by default including 256-bit AES encryption, 4,096-bit DHE-RSA keys with perfect forward secrecy, and SHA512 authentication.
ExpressVPN is highly rated, fast, user-friendly, and has apps available for Windows, MacOS, Android, iOS, and Linux (command line).
Pros:
- Fast and reliable
- Accepts Bitcoin
- Has a .onion site
- Great security and privacy offering
Cons:
- Slightly more expensive
- Few advanced configuration options
Our score:
SPEEDY AND SECURE:ExpressVPN is fast and versatile, with strong unblocking ability and a ton of security features. Includes a 30-day money-back guarantee.
Read our full review of ExpressVPN.
4. CyberGhost
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.Cyberghost.com
Money-back guarantee: 45 DAYS
CyberGhost doesn’t have any Tor-specific features, but it is the only VPN to earn a perfect score in our security and privacy assessment. For this reason, it pairs well with the Tor Browser. CyberGhost assigns each user a unique anonymous ID, and the email address you use to sign up is encrypted. This prevents third parties from connecting a user’s email address to their CyberGhost account. CyberGhost stores no identifying logs.
The company is based in Romania, which has no mandatory data retention laws. Strong encryption, leak protection, a kill switch, and perfect forward secrecy are all included in the apps, even on mobile. Internet connection speeds are plenty fast enough to handle Tor traffic.
Apps are available for Windows, MacOS, Linux, iOS, and Android. You may connect up to seven devices at a time.
Pros:
- Advanced online security
- Zero logs
- Bitcoin accepted
- Fast
Cons:
- No Tor-specific features
- Could offer more customizable options
Our score:
FAST SPEEDS:With comprehensive protection and one-click unblocking enabled by default, as well as high download speeds and a low cost, CyberGhost is ideal for those new to VPNs. This comes with a 45-day money-back guarantee.
Read our full CyberGhost review.
5. PrivateVPN
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.PrivateVPN.com
Money-back guarantee: 30 DAYS
PrivateVPN’s website has a helpful guide on how to alter the OpenVPN configuration files included in the app so that outgoing internet traffic first passes through the Tor network, and then through the VPN a setup known as “VPN over Tor”. If you want to use the Tor browser to access sites on the clear web that don’t normally allow Tor connections, your IP address will be that of the VPN server, and the site won’t block you. Note that if you don’t want your ISP to see that you’re using Tor, it’s better to use a standard VPN connection with the Tor browser.
PrivateVPN offers great speeds and advanced security, plus a strict no-logs policy. You can connect ten devices simultaneously.
Pros:
- Zero logs
- Fast servers
- Strong encryption
- Supports Tor-over-VPN
Cons:
- Smaller server network
Our score:
UP AND COMER:PrivateVPN is a newer provider that earns its place among the veteran players. It comes with a 30-day money-back guarantee.
Read our full PrivateVPN review.
6. IPVanish
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.IPVanish.com
Money-back guarantee: 30 DAYS
IPVanish is a speedy VPN that doesn’t sacrifice privacy or security. A subscription gets you strong leak protection, unbreakable encryption, and a strict no-logs policy. IPVanish allows any number of simultaneous connections, which is extremely rare for a budget provider. IPVanish apps come with an obfuscation feature that disguises the encrypted VPN tunnel as normal internet traffic. It doesn’t accept Bitcoin, though, so if you want to make an anonymous purchase, look elsewhere.
Apps are available for Windows, MacOS, iOS, and Android.
Pros:
- Fast speeds
- Privacy protection is solid
- No logs
Cons:
- Bitcoin not accepted
- Doesn’t work in China
Our score:
FAST & SECURE:IPVanish offers a great combination of speed and security, plus a 30-day money-back guarantee.
Read our full IPVanish review.
VPNs that Tor users should avoid
HideMyAss
Due to poor logging policies that have led to the arrest of at least one user in the past and more invasive data retention laws recently passed in the UK, England-based VPN provider HideMyAss should be avoided by anyone who values privacy and anonymity.
PureVPN
A man accused of cyberstalking was recently arrested by the FBI thanks in part to records provided by Hong Kong-based VPN provider PureVPN. The individual used PureVPN in an attempt to hide his identity, but the provider handed over logs that ultimately led to his arrest. PureVPN has since updated its privacy policy to state that it keeps absolutely no logs, but Tor users should probably still steer clear if they’re looking for an extra layer of privacy.
Tor over VPN vs VPN over Tor
Should you use VPN over Tor or Tor over VPN? Both have their advantages when it comes to both security and usability. We’ll outline the advantages and disadvantages here.
Tor over VPN
You can use Tor over VPN simply by connecting to a VPN and accessing the internet through the Tor browser. Your traffic is encrypted by both Tor and the VPN before leaving your device. The traffic flow looks like this:
My device –> Encrypted by VPN and Tor –> VPN server –> Tor Network –> Internet
Pros:
- ISP cannot see you are using Tor
- Neither ISP nor VPN can see your traffic*
- Easy to set up. Just connect to thee VPN and turn on the Tor browser
- Access to .onion websites
- Flexibility to use VPN by itself with a normal browser for non-critical tasks
- Tor entry node cannot see real IP address
Cons:
- Websites can block traffic from Tor exit nodes
- VPN can see (and potentially log) your real IP address
- Exposes traffic to compromised Tor exit nodes
*Note that NordVPN and BolehVPN could hypothetically analyze your traffic before it’s encrypted by the Tor network when using their Tor-over-VPN-enabled servers. The trade-off is that all traffic can be routed through Tor without configuring individual apps to be used with Tor.
VPN over Tor
VPN over Tor is more difficult to set up because it requires configuration on the VPN server. As far as we know, only AirVPN offers this capability. The traffic flow looks like this:
My device –> Encrypted by VPN and Tor –> Tor network –> VPN server –> Internet
Pros:
- Neither ISP nor VPN can see your traffic
- Access to websites and apps that normally block traffic from Tor exit nodes
- VPN cannot see your true IP address
- Not vulnerable to compromised Tor exit nodes
- All traffic routed through Tor without individual configuration
- No packet discrimination by Tor exit nodes
Cons:
- ISPs can see you are using Tor
- Difficult setup requires VPN provider’s assistance
- No access to .onion websites
- The Tor entry node sees your real IP address
- Not application-specific, so it’s unable to run P2P or other programs outside of the Tor network without disconnecting from the VPN
See also: Tor vs VPN – What’s the difference?
Our Methodology: Finding the best VPNs for Tor
If you’re using Tor, it’s a safe bet that you’re interested in privacy. However, this isn’t the only thing to think about when looking for a VPN; you’ll also need one with high speeds, consistent performance, and the ability to fly under the radar. Here are the key features we looked for when creating our list of the best VPNs for Tor:
- Security: To make our list, providers must have a minimum of 256-bit encryption, DNS and IPv6 leak protection, and a kill switch. We prioritized VPNs with their own anti-surveillance protocols or cloaking features too, since these hypothetically grant you access to Tor from anywhere in the world.
- Privacy: In addition to the tools above, we require our top VPNs to have a no-logs policy. This ensures that your activities can’t be revealed under any circumstances. Many of the services allow you to pay anonymously too, for a second layer of protection.
- Speed: Tor is notoriously slow, so it’s important we don’t restrict speeds even further by using a sub-par VPN. The services above all performed well in our recent VPN speed testing, although it’s good to bear in mind that they are limited by your base connection speed.
- Unblocking ability: If you’re looking to use Tor somewhere it’s unavailable, or simply access geo-blocked services as you travel, unblocking ability is crucial. We tested the VPNs above against a wide range of platforms including HBO Max, Disney+, BBC iPlayer, and Amazon Prime Video to make sure we only recommend the most versatile.
- Usability: Needless to say, the VPNs above all have apps for the most popular operating systems. Anything that makes the service more user-friendly is a huge bonus. This could be special Tor over VPN servers, 24/7 customer support, or a lack of connection limits.
Looking to find out what other tests we perform? You’re in luck: we have a post that breaks down every step of our VPN testing process.
VPNs for Tor FAQ
Why use a VPN with Tor?
A VPN encrypts all of a device’s traffic and routes it through a remote server in a location of your choosing. This assigns the user a new IP address–a string of numbers and decimals unique to a device that can be used to pinpoint the user’s location. The encryption prevents internet service providers from being able to monitor your activity.
While most good VPN providers offer a “no logs” policy, VPNs still require a degree of trust that the provider won’t record user traffic or give in to corporations, hackers, and governments that demand user information. Your activity is private but not necessarily anonymous.
Tor encrypts the user’s traffic and routes it through several nodes run by volunteers, known as the Tor network. Every time a new website request is sent, the route changes, making it next to impossible for anyone to trace the user. Unlike a VPN service, there’s no central authority that controls the traffic flow, so trust is not necessary.
These entry and exit nodes are well documented, however, so both your ISP and the destination server can easily find out if you’re using Tor. Some ISPs, websites, apps, and governments will block traffic to and from Tor entry and exit nodes altogether. In some countries, simply accessing the Tor network will get your name added to an ISP’s naughty list. That means your activity is anonymous, but not entirely private.
VPNs are faster and thus more suitable for streaming video, torrenting, and other download-intensive tasks. Tor is more suitable for anonymous web browsing and accessing .onion websites on the DarkNet.
For extra protection and more flexibility, Tor and a VPN can be combined. Traffic can be encrypted by both and then channeled first through the Tor network and then over a VPN (VPN over Tor) or vice versa (Tor over VPN). We’ll discuss the pros and cons of both configurations further down, but first, let’s talk about which VPNs are most suitable for Tor users. Note that while combining Tor with a VPN will improve anonymity and privacy, it will have a heavier impact on connection speed and latency than using either one on its own.
Can I use a free VPN with Tor?
Yes, but you might be doing more harm than good. Technically, nothing is stopping you from connecting to a free VPN service and firing up the Tor browser.
Be wary of free VPNs. They look enticing on the surface, but in reality, they often use substandard encryption, lack security, force users to wait in queues to connect, and impose data or bandwidth caps on users. They often have fewer servers and IP addresses, which makes it easier to trace individual users. Many inject advertisements and tracking cookies into users’ browsers, sacrificing their privacy rather than bolstering it.
Is Tor a free VPN?
Tor is free, but it’s not a VPN. Both Tor and VPN are types of encrypted proxies, but there are a few key differences. Tor connections are encrypted several times and pass through several volunteer Tor network nodes in a randomized sequence. Tor can also be used to access .onion sites on the dark web.
A standard VPN, by contrast, encrypts your connection once and routes it through a single server. That server location is operated by the VPN company. A benefit of how a VPN functions is that subscribers can pick from a list of server location options in the VPN app. This gives the user control over where they spoof their IP address, which provides the added benefit of being able to access regional internet services.
Can I be tracked if I use Tor?
Tor has its vulnerabilities and is not immune to attacks that could be used to track users. Most of these attacks involve compromising an exit node—the last server relay in the sequence.
However, such attacks tend to be costly, targeted, and would require a well-resourced adversary to pull off. Tor’s anonymity and security are more than adequate for the vast majority of users.
Bear in mind that users can also be a threat to their own privacy if they’re not careful. Tor can’t prevent tracking if you log in to a website with your real email address and password, for example.
Which is the best free VPN for browsing deep web?
Don’t trust free VPNs with your privacy. It’s better to try a paid VPN and cancel before the guarantee runs out if you don’t want to spend money.
Is using a VPN with Tor legal?
Yes, it is perfectly legal to use a VPN, Tor, or both together in the vast majority of countries. Check out our article on where VPNs are illegal if you’re not sure about the rules where you live.
Disclaimer: We’ve done countless hours of research on this topic but make no claim to be legal experts. Nothing in this post should be taken as legal advice, and we encourage you to do your own due diligence if there’s any doubt about the legality of VPNs (or Tor itself) in your country.
Is Tor safe?
Tor is widely regarded as a secure tool. It uses strong, layered encryption and strips away many would-be vulnerabilities found in other browsers, such as scripts and tracking cookies. Although a well-funded adversary could conceivably pull off a correlation attack to identify Tor users, the vast majority of users will face no such threat.
Should I use Tor for all my browsing?
You can try, but it probably won’t go well. Many websites block connections from Tor exit nodes outright. Tor’s script blocking and cookie deletion make many websites inconvenient or downright dysfunctional. You’ll probably have to wrestle with a lot more CAPTCHAs. On top of all that, Tor connections are slow, so sites will take a long time to load and videos will frequently stop to buffer.
Can I use Tor on iOS and Android?
An official first-party Tor browser is available on the Google Play Store for Android devices. You could also try Orbot, which is third-party but has been around longer.
iOS users only have a third-party option, Onion Browser. It’s an open-source browser endorsed by the Tor Project. However, one must assume that it suffers from the same drawbacks on iOS that have prevented an official Tor Browser on iOS from being released.
Will a VPN hide my IP address when using Tor?
Both your VPN and Tor encrypt your data and hide your IP address. As such, you don’t need a VPN in order to have your IP address hidden when using Tor. Despite this, it doesn’t hurt to connect to a VPN while using Tor because it simply adds an extra layer of protection. Without a VPN, your ISP can see you’re connected to Tor, although they can’t see which websites you’re visiting. However, if you use a VPN, your ISP won’t even be able to see that you’re using Tor.
Is the Tor network legal?
The Tor network is legal in the United States. No law prohibits users from using or connecting to the Tor network. Furthermore, the US government does not consider its access and use illegal, as it has even funded some of its development.
Many people need to understand that using Tor isn’t illegal. Instead, it’s simply an anonymous way to browse the web safely and securely from anyone who can access a few basic technologies like browsers and routers.
It is important to note that while there are plenty of legitimate uses for Tor, some people use it for malicious purposes like buying drugs or trading child pornography – activities that remain illegal regardless of whether they are done through Tor.
Which is better? Tor Over VPN (Onion Over VPN) or VPN Over Tor?
Normally, when you use Tor, only the exit node has access to your unencrypted traffic. Tor over VPN setups prevent this by adding a layer of encryption before the first node, ensuring that nobody on the Tor network ever sees any usable data. In other words, as long as your VPN provider has a no-logs policy, your activities can’t be monitored in any meaningful way.
It’s also possible to reverse this using a VPN over the Tor system. This stops your ISP from seeing that you’re using Tor and lets you use sites that normally block Tor traffic outright. However, there are real downsides, too: VPN over Tor is trickier to set up, doesn’t actually let you browse the dark web, and allows entry nodes to see your real IP address. For this reason, we’d recommend sticking to Onion over VPN instead of degrading your security for very little reward.






I have use pure VPN for years but after reading this article among many others it’s obvious to anyone with sense that they keep logs so thank God I wasn’t doing anything naughty :))
No ProtonVPN? I think its a great combo. Peace 🙂 Happy NEW Year!
IPVanish?
what about ipvanish is it good for tor users?
IPVanish is great, it just doesn’t have anything that makes it particularly well-suited to Tor users over competitors.
No PureVPN in the list? You gotta be kidding me. It is the best I’ve used, beats many names that are in the list.
PureVPN has no added value for Tor users and is not transparent in its encryption practices e.g. authentication and key exchanges, so we can’t recommend it in this list.