In short, Securonix is a SIEM tool that collects security event logs across multiple servers and provides features such as alerting, as well as AI-powered incident response for automated remediation.
Securonix was developed to ingest and process large amounts of data to develop both security and operational insights for businesses. By using a combination of machine learning, behavior analytics, and manual investigation tools, companies can use Securonix to develop operational intelligence and position themselves proactively to insider threats and cyberattacks.
As a log management tool, Securonix can also be used to conduct forensic analysis against server logs during or after an intrusion or insider attack. While manually combing through dozens of log files could take months, SIEM products like Securonix can ingest those logs into one place to allow for a more comprehensive and time-efficient search.
You can look at Securonix as a holistic security analytics tool.
How does Securonix work?
Rather than using rule sets and signatures, Securonix works by using machine learning and behavioral analytics to find both internal and external threats for proactive and reactive incidence response.
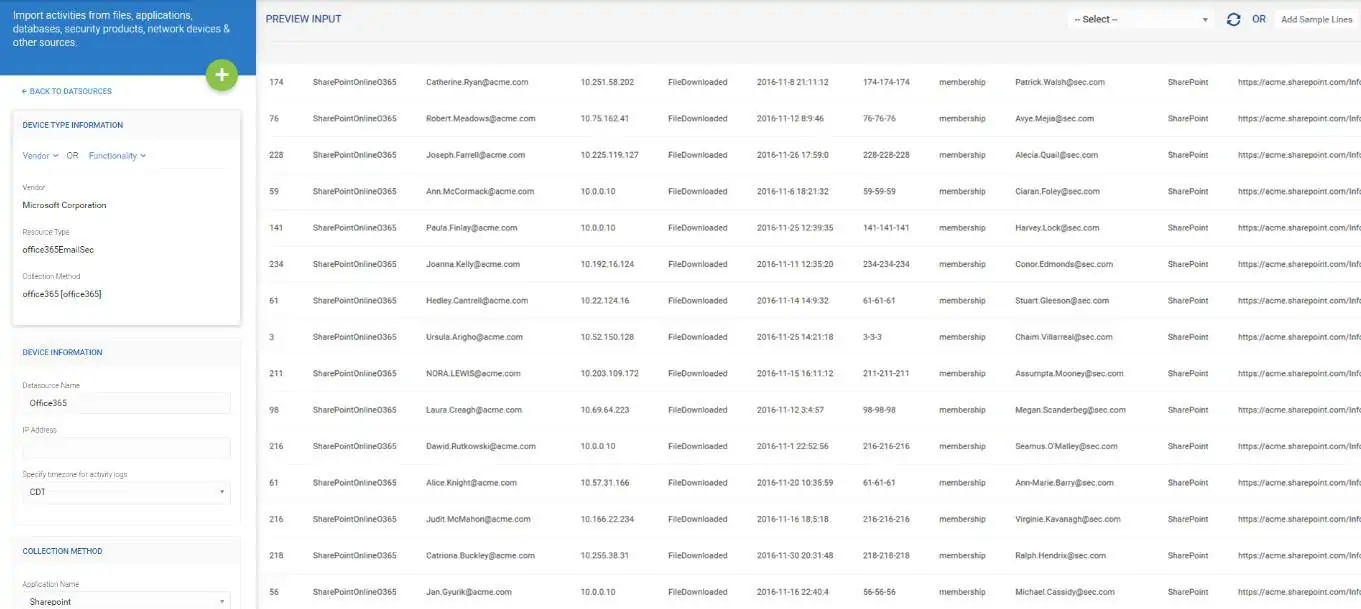
All of this data is gathered by collector agents that are installed on each endpoint that you want to monitor. Currently, Securonix can pull data from dozens of different platforms and can handle unstructured data, LDAP connections, Syslog files, database files, and API connections for more customized solutions.
Once that data is gathered, Securonix uses a process it refers to as ‘entity enrichment’ which is a six-step process that applies context and meaning to unstructured data. This is to better assess where it’s coming from, who generated it, and where that data should be categorized on the threat scale.
This entity enrichment is achieved by cross-referencing other data sets such as Active Directory or HR software to add context such as identity or location from otherwise separate logging events. This contextual data connection helps automatically enhance security insights that would not be available.
For example, by comparing account logon events with geo IP logs you can quickly identify suspicious logins by using a feature such as anomaly detection. This can either alert the security team of a suspicious login or execute a script to disable the account until the event is reviewed.
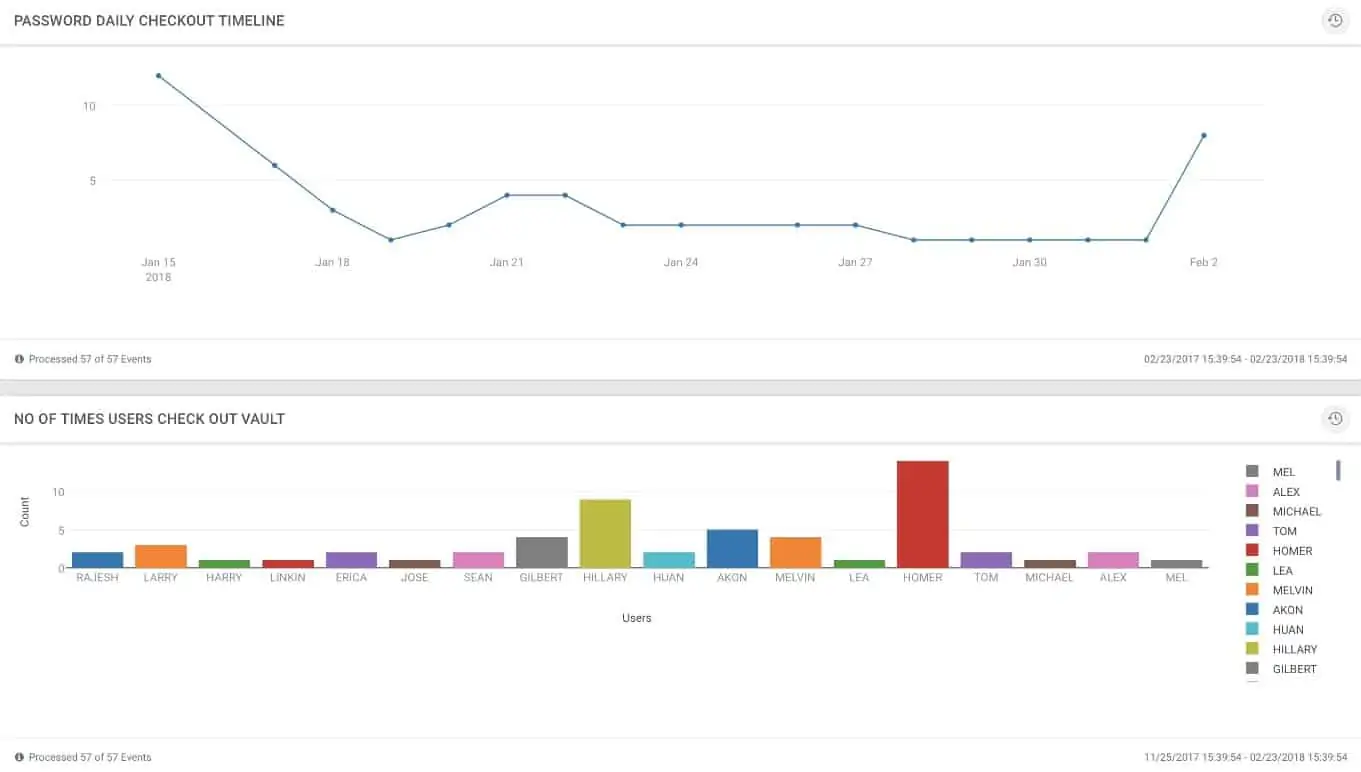
With Securonix you don’t need to rely on log files to trigger an alert or an event. Threat detection techniques such as behavior analysis can measure the historical baseline averages for events across your network, and understand when you’re shifting away from what is considered normal. This can be applied at scale, or to smaller groups such as departments for a more granular peer group analysis.
Other detection techniques such as event rarity monitoring can help alert staff when something is drastically out of the ordinary. This could range from external network intrusion attempts to employees attempting to access systems they shouldn’t be on. It’s this level of context that really gives you insight into whether an event happened by accident, or if there was the intent behind it.
When an entity has reached the end of the enrichment system it is assigned a threat score. This score can be applied to a device, server, or individual and allows you to group threats by severity or manually investigate them one by one.
Response Orchestration goes a step further and allows you to set thresholds on a threat score that automatically triggers a response. For example, if users were to hit a threat level of 60, their account could be disabled, their sessions could be terminated, and an email could be automatically sent to their managers.
Now that we’ve explored how Securonix works, let’s take a look at some of its core features.
Searching For Threats In Securonix
The Securonix platform was built to handle massive amounts of log data both over the long and short term. With some companies generating millions of events per day, searching needs to be both quick and intuitive.
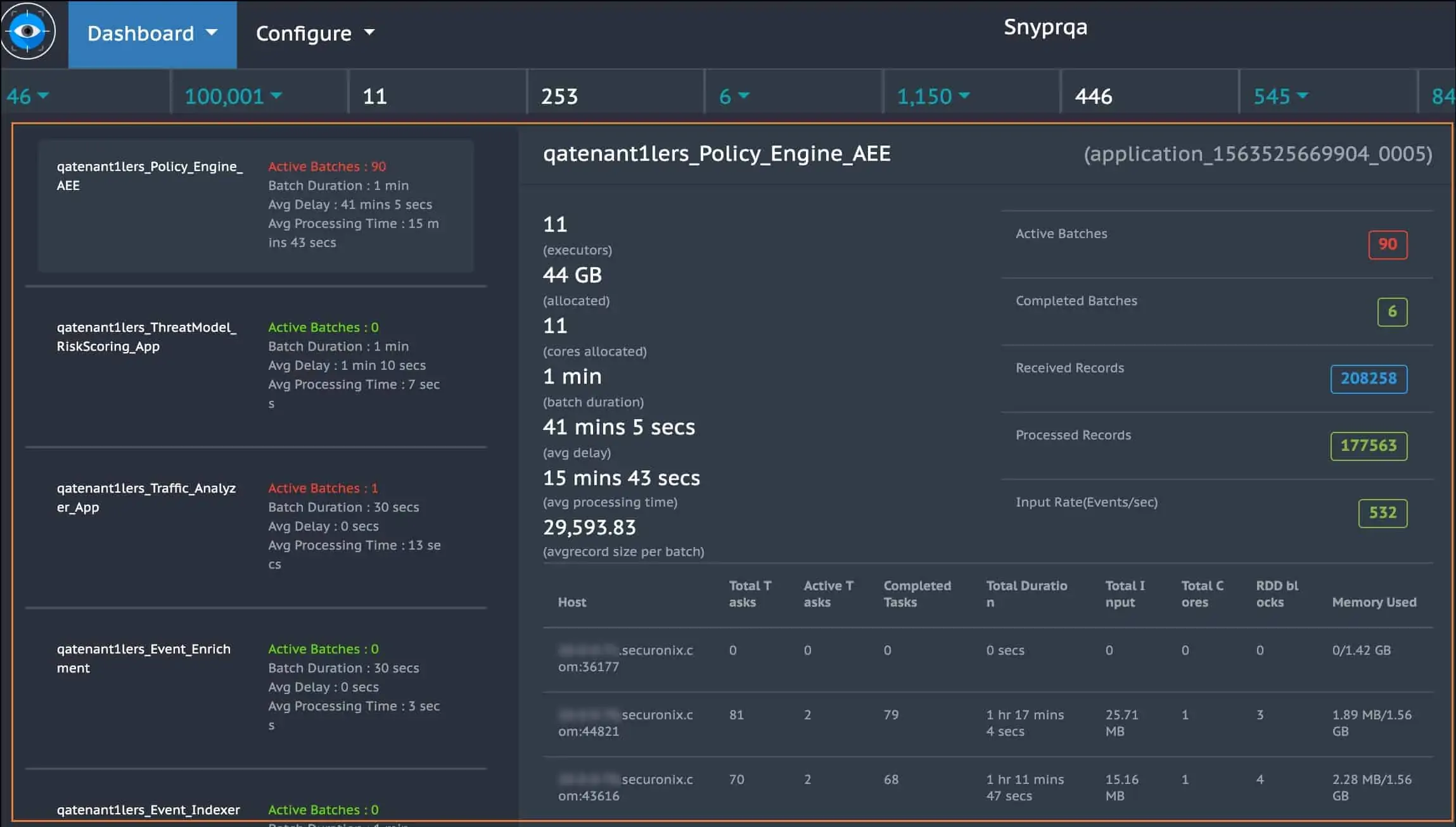
To sift through this data efficiently a tool called SNYPR was created to work in tandem inside the SIEM infrastructure. SNYPR allows you to parse millions of logs and track down threats quickly in real-time.
The dashboard allows for a quick overview of critical events such as a list of Top Violators, Top Threats, and the number of recent threats stopped over time. This dashboard is customizable and can contain different panels depending on the metrics that are important to your day to day operations. You’ll have the opportunity to drill down into any of these panels to view more details on the event and the entity it relates to.
Searches can be performed on a broad scale that encompasses all logs, or more realistically pulled from one or two data sources that you specify. The search function is relatively easy to use but could be improved upon with more predictive autofill features and better autocorrect functions. Searches can be saved for later and shared with your team if you find yourself repeatedly running the same queries.
Even with millions of event records searching and filtering down queries was incredibly fast. Creating graphics from your search query will require you to manually specify a display function rather than toggling on or off the graphical interface, which can make things faster but can also be a hurdle for someone who isn’t as comfortable working with long queries.
Integrations
The true power of Securonix comes from its wide array of available integrations. From these data sources, information can be centralized and then run through data enrichment and security processes. There are dozens of platforms that have a connector framework for Securonix that allow you to see both log data, and other non-technical information. Some big-name integrations include Office365, IBM, Salesforce, and Avaya.
Reporting
Right from the home dashboard, you’ll be able to generate and configure reports to share with your technical team or executives. With Securonix you can share links to live preconfigured dashboards that you set. Alternatively, you share static reports of any ad-hoc information you’d like to configure. Reports are generated through queries, so the process to create a report isn’t much different than making a search.
If you’re looking for quick insights there are a number of built-in reporting packages that include all of the major compliance management reports including PCI DDS, SOX, HIPAA, FISMA, and ISO 27001.
Ease Of Use
Compared to other SIEM tools Securonix proves to be more user friendly than some of its competitors. However, because Securonix has so many layers to it, you could find yourself running into roadblocks when trying to generate meaningful data. The main challenge with SIEM tools like Securonix is that you’re usually only limited by your own ability to create meaningful queries. This makes having in-depth support and documentation vital when comparing tools.
The Securonix platform has several elements that are fairly easy to use, such as configuring a custom dashboard view and creating reports. The onboarding process does have a few more hoops to jump through than solutions like Splunk or Sumo Logic. This is primarily due to the number of sources needed to fully run the data enrichment process, and provide context to events such as identity and location.
Naturally, the more feature-rich your SIEM platform is the more areas there will be to run into problems and areas where further training and education are required. Even with prior experience on other platforms, creating in-depth meaningful queries can still be a challenge with Securonix. There are a few different ways you can help overcome this depending on what your needs are.
Securonix has a healthy amount of documentation that is simple to navigate and covers on-premises, cloud, and multi-tenant environments. Here you’ll not only find basic information and configuration settings for the platform, but also entire guides for administration, automation, and ways to configure your analytics.
Beyond documentation, there are numerous articles detailing how to fix common problems in the Securonix Knowledge Base, which is not public-facing and requires an account to access. There are two types of training sessions you can also sign up for if you need more guidance. Passive training videos are available through your Securonix account and can be done at your own pace. These videos cover the basics and are listed as 100 and 200 level courses.
The remaining training courses award official Securonix certification upon completion and cost upwards of $800.00 (£596.50) to attend. Lastly, there is SNYPR Bootcamp, which is a four-day seminar that covers topics such as threat investigation, monitoring capabilities, and techniques on how to find unique opportunities within your data. This boot camp is currently priced at $3200.00 (£2386.00).
Securonix Pros & Cons
Pros:
- Easy to use – highly intuitive interface
- Robust reporting – supports a wide range of compliance standards
- Integrates into a wide variety of integrations
- Flexible pricing
Cons:
- Can take time to fully explore all features
Securonix Pricing
Unlike most SIEM solutions, Securonix bases its cost primarily on identity rather than events per second, or gigabytes used. This flat pricing approach helps simplify cost projections and allows organizations the freedom to expand without having to worry about exceeding monthly data budgets.
Price is based on standard annual licensing and the number of employees. This helps keep costs predictable and scaling simpler. While this model can help businesses scale, costly annual license fees can be a barrier to entry for growing medium-sized companies. Since pricing is closely tied to the number of employees in your organization the exact amount you’ll pay will vary. The number of employees is used because each employee will have an ‘identity’ built inside of Securonix.
With SIEM products it can be tough to estimate an ROI, especially for a tool as complex as Securonix. While you might not see an exact dollar amount, try to look for improvements in other areas of your business. Many companies who successfully implement SIEM products will see an improvement in SLA, as well as a decrease in tickets overtime. Gaining deep visibility into your network activity may take time, but is well worth it when you compare the average cost of a cyberattack or ransomware outage.
You can test out the cloud-based version of Securonix for free through a 30-day trial.
Why Choose Securonix?
While there are many SEIM products on the market, Securonix positions itself as one of the more flexible tools that are built for enterprise-level companies. Securonix has a unique set of features that almost no other SIEM platform can offer. While your average SIEM can provide event management, Securonix goes deeper by applying artificial intelligence, behavioral analytics, and data enrichment in a way that lets you see threats coming long before they cause damage.
Suecuronix might not be the best option for smaller growing companies. Features like entity identification tend to only show value when applied to large corporate networks. If you have a large network and are not confident in your IT team’s ability to proactively identify threats both internally and externally, Securonix might be what you’ve been looking for.
Securonix Alternatives
If you’re still looking to narrow down your selection, be sure to check out our Best SIEM tools post.
- Exabeam This SIEM is one of the closest alternatives to Securonix on the market. It applies behavioral analytics and security automation based on logging events throughout your environment.
- InsightConnect Built by Rapid7, this tool encompasses proactive log management and automated workflows in a similar manner to Securonix.
- Splunk The Splunk platform aims to make log management simple at an enterprise level. While Splunk shares many similarities to Securonix, it lacks some of the identity analysis and deep behavioral analytic features.
- Sirius This platform offers a wide variety of enterprise-level IT services including network risk management, IoT automation, and asset management. Sirius has many service offerings, but might be more suited to those who are looking for consulting in those areas rather than a managed service.