You probably have a wifi router in your home to provide internet access to all the family. When people drop by, they ask for the password so they can check something on their smartphone or show off vacation photos stored in the cloud. Before long, a lot of people know your wifi password and people can connect to your router any time they pass by your house. In an apartment building, your router’s signal extends into neighboring apartments.
Unlike physical networks, wifi systems can extend beyond the walls of your home. Once the password for access gets out in the world, it is very difficult to control who can access your home network. Therefore, you need to consider implementing some changes and routines that protect you from intruders, snoopers, and internet carpetbaggers.
You have two major security issues to deal with. The first is that you need to control who can actually get on your network. The second problem is that of the signal footprint. If people outside your home can pick up a signal from your router, they can also capture data and reap all of your passwords.
Here are some simple but important tasks to improve the security of your network.
1. Make a complicated router password
Everyone worries that they won’t be able to remember a password and so just set them up as a string of numbers, such as 11111111. However, difficult passwords that are impossible to remember are good for system security.
You are going to have to give the wifi password to other members of your family and close friends and relatives that visit regularly. However, you can’t control who they might give that password to. Although there are ways to look up a password that has already been set up in any computer’s operating system, not many people know about that utility. Making a complicated password makes it harder to communicate and it is also impossible to guess.
Make life a little harder for those trying to guess your wifi password by using a string of random characters. A wifi password needs to be 12 or 20 charters long and you can get one created for you by using the Comparitech password generator.
See also: How to make and remember strong passwords
Limit access to the password
Although it seems reasonable to give access to the wifi to your children, their friends, and your friends, you shouldn’t feel obliged to give out the password to everyone that enters your home. For example, a visiting salesman is a complete stranger and no matter how well dressed they are, you don’t know what their plans are and you can’t trust them. Someone who is on your property to perform a service, such as a plumber, a gardener, or a decorator doesn’t have the right to ask for the password to your wifi. In these instances, you should be prepared to say “No.”
Commercial visitors shouldn’t need to access your wifi router in order to get information off the internet for their work. Their employers should provide them with a data plan or a USB modem if their business model includes storing data in the cloud.
Change the password frequently
There is no hard and fast rule about how often you should change the router password. However, you should change it on a regular basis. Memorizing a new email or online banking password can be annoying because you have to log in all the time. But because wifi routers typically only require you log in once to be allowed indefinite access, changing a wifi password is less of a nuisance.
Make changing the router password part of your monthly routine. On the first of the month, after breakfast, change the wifi password. If you have a lot of people in and out of your home—during a renovation, for example—change the password weekly. Remember to update the note you kept of the password.
Many modern wifi routers also include an option for setting up a ‘guest network’ with its own SSID and password. This means guests can connect to the internet with their devices, and you don’t have to share your main password.
2. Change the router’s admin credentials
You can access the console of your router from any device connected to the network. Most manufacturers set up the administrator account on routers with the same username and password for every piece of equipment they sell. This is different from simply connecting to the network; it grants you control over the network configuration. With a bit of know-how, anyone connected to the router can guess or Google its login credentials. This makes you vulnerable to a hacker or a young overachiever.
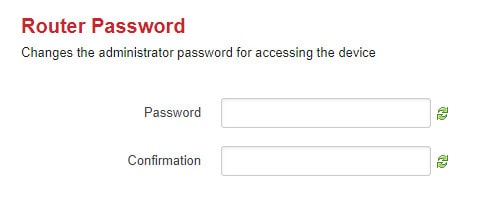
If someone gets into the admin console, they can change the admin password and lock you out. So, change those credentials before some smart-assed friend of your daughter does it. Without access to the administrator account on your router, you will not be able to perform any tasks to improve your wifi security.
The default username and password may be printed in a booklet that came in the box with the router or you may be able to find it in the support pages on the wifi manufacturer’s website. It might even be displayed on the login screen for the router. If you can’t find the username and password anywhere try sys/admin, system/admin, admin/admin, user/user, system/password, and admin/password for the username/password combination. If none of these work, look for your router in this list of default router administrator passwords.
When you find the right combination, you need to look around the menu system for the account details. Change the password of the admin account to a random string of letters and numbers and make it at least 12 characters long. Don’t forget to write that new password down in a safe place before you log out of the console. Because most router consoles are accessed via web browser, a password manager can take care of this for you.
3. Change the network name
As explained in the previous section, router manufacturers produce the same settings for every item of a product line that they produce. Often, a manufacturer will install the exact same administration software on all of its router models. That consistency makes life easy for hackers.
Free network detection software lets hackers see all the surrounding wifi networks. The hacker doesn’t need to know which home the signal comes from because he doesn’t need to break into your house in order to get into your network. Each network is identified by a name, called an SSID.
Router manufacturers often put the brand name or model of the router in the SSID. If you got a router from your internet service provider, the ISP might change that SSID to show their own name instead of the manufacturer. If you bought the router yourself, its SSID will probably identify the manufacturer or even the model of the router.
A hacker can use the information that appears in the SSID to look up the default username and password for the router with little effort. Change the SSID so that it doesn’t give away the router brand or model. Don’t choose an identifier that includes your name, address, or telephone number. Don’t use any other personal information in the name. So, “10BullLane,” “JBDecker Network,” and “Homenet-12281975” are all bad ideas. Avoid making political statements, don’t use offensive language, and don’t provoke hackers with challenges in your SSID. Just make it bland.
Related: Top 10 Intrusion detection tools
Hide the network
Your router doesn’t have to broadcast its SSID. If you block your router from sending out its identifier, your home wifi becomes a hidden network. Those devices that already have connection data stored will still be able to connect, but passers-by won’t see it. In many cases, the network list that others see will include a line that says “Hidden network.” Without knowing the name of the network, it is impossible to connect to it.
Making it impossible for unknown devices to connect to the network presents a problem if you buy a new gadget. However, you can temporarily turn on the SSID broadcast to let your new device see the network. Once you have set up a connection with the password, make the network hidden again. Hiding the network makes it easier to block visitors from getting on the network. If they can’t see your router in their list of available networks, they will be less likely to ask for the password.
4. Strengthen wifi encryption
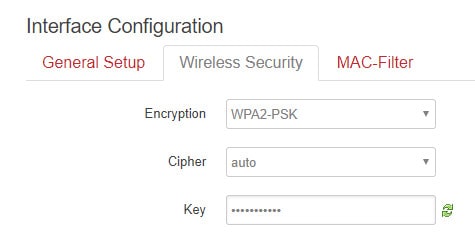
A number of freely available hacker tools can crack weak wifi encryption, which could allow an attacker to intercept, see, and modify your online activity. Three types of wifi protection systems are commonly used to secure transmissions so only the end user’s device and the wifi router can read the contents of a transmission. These are Wired Equivalent Privacy (WEP), Wi-Fi Protected Access (WPA) and Wi-Fi Protected Access 3 (WPA 3).
- WEP was an early attempt to provide a level of security for wireless networks that was equivalent to the security of wired networks. Introduced in the late 1990s, WEP uses what is now considered a relatively weak encryption algorithm, called the RC4 stream cipher. This – and other vulnerabilities – make it unsuitable for modern wireless networks.
- WPA uses stronger encryption algorithms than WEP. The Temporal Key Integrity Protocol (TKIP) dynamically changes encryption keys during a session to enhance security. WPA also uses a more robust authentication process – making it harder for unauthorized users to gain network access.
- WPA2 improved encryption further with the introduction of WPA2, which used the Advanced Encryption Standard (AES). WPA3, which was introduced in 2018, also uses AES. It replaces the Pre-Shared Key (PSK) exchange with Simultaneous Authentication of Equals (SAE), which is more secure. SAE – also known as the Dragonfly Key Exchange — fixes the WPA2 vulnerability to KRACK attacks.
Of these three, you should ideally be using WPA3. If it’s available, it will appear in the list of options in the security drop-down menu of the router dashboard. The Wi-Fi Alliance began certifying WPA3-approved products in 2018, though not all routers made since then are guaranteed to support it.
5. Turn off Plug ‘n Play
The Universal Plug ‘n Play methodology helps devices in your home discover the network and then communicate with the manufacturer for firmware updates and supplies. UPnP is a key element in the creation of the Internet of Things. This is the technology that makes household appliances “smart.” Essentially, smart gadgets can access the internet. UPnP also provides a channel for hackers.
Your router has to cooperate with the UPnP system in order for those household gadgets to get access to the internet. Although the creation of self-tuning devices seemed attractive at first, the absence of password protection for most devices, or the tendency for manufacturers to use the same password for all devices, make these smart pieces of equipment a security vulnerability.
UPnP helps a device get set up, but once you have that thing working, switch off its UPnP capabilities. You should also turn off UPnP compatibility in your router. UPnP has enabled hackers to infect household devices and include them in botnets. A botnet is an army of devices that can be directed to send access requests to one computer all at the same time, thus blocking its availability. This is called a DDoS attack and it is increasingly being used by countries such as Russia and China as a military strategy, so UPnP is even undermining national defense.
6. Turn off Remote Management
The console of a router should only be accessible from devices connected to the network. However, a standard router setting enables remote access. This means that you can access the console over the internet, from another location. Unfortunately, if you can do that, so can anyone else. So, turn off remote access.
7. Limit WPS
Wif-Fi Protected Setup (WPS) offers an easy way to get new devices to recognize the network and connect to the router. WPS uses one of two methods.
If your router has a WPS button on the back, pushing it will send out a signal that adds the device to the network and passes it log in credentials so you don’t have to enter a text password.
An alternative method uses an eight-character numeric code entered into the network settings of the device. WPS enables devices in your home, such as set-top boxes and game consoles, to maintain a presence on the network even when you change the password needed for computers and phones to connect.
WPS presents a security weakness because the code method is easy to crack. If your router has a WPS button, then turn off the WPS code capabilities and rely on the button. If you don’t have the button, turn off WPS completely because the code option is a serious problem for your network security.
8. Keep the router firmware up to date
The router manufacturer should update the firmware on your gateway automatically. However, just as you should make a monthly schedule to change the wifi password, you should also regularly check for updates. The router console should include this option. If not, make it a habit on the first of the month to check the router manufacturer’s website for any updates and install them if they are available.
Another trigger for firmware updates should be any news stories that speak about major virus attacks. Usually, new viruses spread because a hacker discovered a security weakness, called an “exploit.” Hackers sometimes detect these weaknesses before the technology companies. The outbreak of a serious attack will provoke the router producer to check through its firmware code to make sure its equipment is not vulnerable to the new attack. If it is, they will issue a security patch. So, check on the website of your router’s manufacturer whenever these news stories break.
9. Turn on the firewall
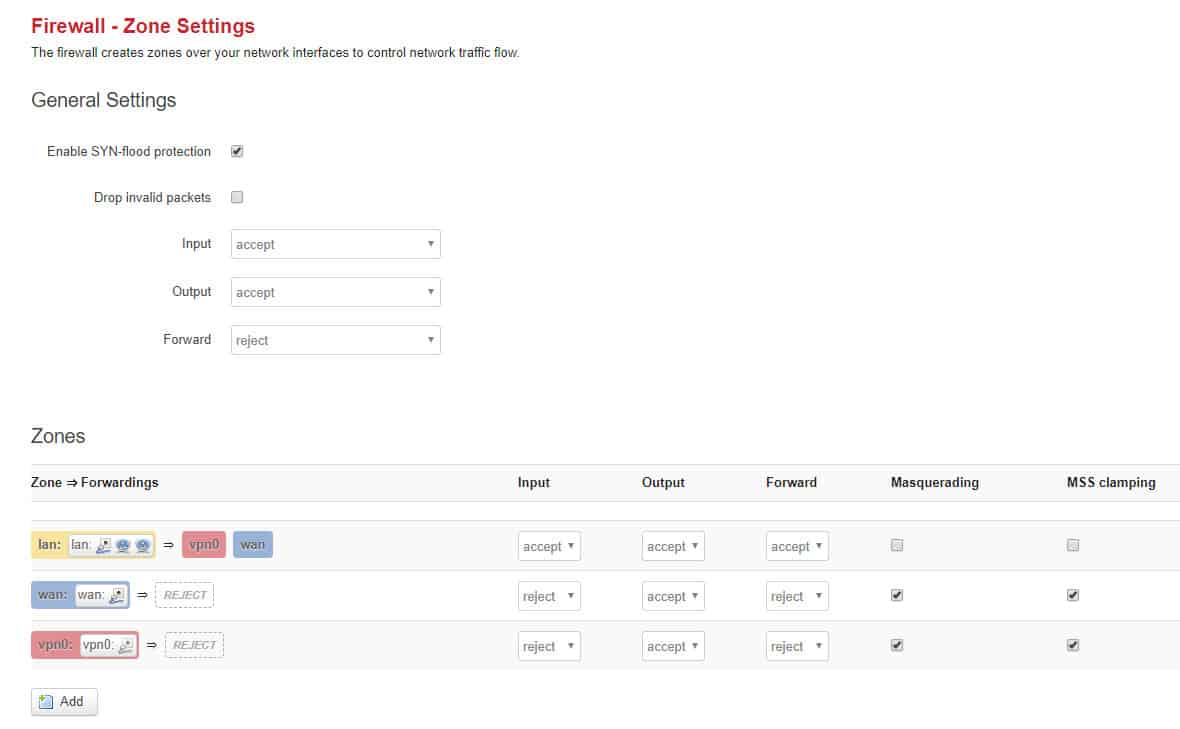
Chances are your wifi router has a firewall on it, but you haven’t turned it on. Browse through the console settings to see if you can find it. If not, visit the Customer Support pages of the router manufacturer’s website. If there is a knowledgebase, you can search the site with the keyword “firewall” and see what information arises.
Wifi routers operate a system called NAT, which stands for “network address translation”. This address manipulation means each computer on your network is allocated an address only known to the router. It doesn’t represent you out on the internet. Instead, the router has its own internet address and that communicates with the outside world. A very fortunate side effect of the NAT system is that it prevents outsiders from identifying the addresses of individual devices on the network. Unsolicited traffic is blocked before it ever reaches end-user devices.
Apart from this protection, routers usually have a hardware firewall. This works a little differently than the software variety that you probably installed on your computer. It is worth turning on.
See also: What is a firewall & why do you need one on your home network?
10. Allocate static addresses
This step is a little technical and you may find it a little awkward to implement. As explained above, all devices on your wireless network have an address. This is called an IP address and it has to be unique. Your computer’s IP address is only unique on your private network. This is why the router uses a public address as well and that one represents you on the internet.
Your router allocates an IP address to each device on the network through a system called the “dynamic host configuration protocol,” or DHCP. Hackers can manipulate DHCP to allocate themselves a network address, making them very difficult to spot.
One of the settings in the console of your router will allow you to change the way that addresses are allocated on your network. To stop the router using DHCP, you need to look at the Network Configuration page of the console. The option you are looking for will probably be a drop-down picklist and will be labeled “WAN connection type” or “address configuration.” The precise settings depend on your model of router. However, you will see that the field is currently set to DHCP. You need to change that to Static IP.
Before you make that change, go to all of the computers and network-enabled devices in your home and note down the IP address that each is currently using. After changing the router to use static IP addresses, go back to each device and allocate it the address that you noted down for it. The effectiveness of changing address allocation is up for debate.
See also: The Definitive Guide to DHCP
11. MAC address filtering
Your router’s console will contain a menu item called “MAC filtering” or “MAC address filtering.” This option will only allow approved devices onto your network. Every device that can connect a network has a MAC address. This is actually the identifier of the network card and it is unique throughout the world. Therefore, no two devices in the world are issued with the same MAC address. MAC stands for “media access controller.” It is made up of six two-digit hexadecimal numbers separated by colons. So it looks like 00:17:5f:9a:28.
You may read that MAC address filtering is a waste of time because it can be sidestepped. This is true up to a point. If you just want to stop neighbors hopping onto your network for free and you can’t keep your kids quiet about the password, then MAC address filtering will provide you with the functionality that you need. If you suspect that one of your neighbors is a hacker, then this technique won’t put up much resistance.
On mobile devices, look in the Network Settings to get the MAC address. On computers, open up a command line window and type in ipconfig /all. This will bring up a list of attributes of the computer, including the MAC address. Make a list of the MAC addresses of all the devices in your house that you want to let onto the network.
Not all MAC address filters are the same
When you go to set up the filtering list pay attention to the instructions on the page because not all MAC filtering systems are exactly the same — the layout depends on your router.
There are two modes to a MAC address filter. These are “allow” and “deny” or they may be labeled “include” and “exclude.” If you don’t see these options, then your router’s MAC filter is of the allow/include variety. If those options are available then select allow/include. There should be a box in the screen where you enter a list of addresses. Usually, a carriage return is enough to separate the records, but you may need to put a comma or a semicolon after each address.
MAC address filtering can be sidelined by a hacker who has a wireless packet sniffer. Every piece of information that goes in or out of a device has its MAC address on it. Although MAC addresses are allocated to the network cards of the world and are centrally controlled so that each is unique in the world, hackers do know how to alter an address. Therefore, the hacker just has to pick one of the MAC addresses that he sees is active on the network and then change his computer’s MAC address to that. However, such tools are not available on mobile devices, so the hacker would have to be sitting with a laptop within range of your router in order to pick up the signal.
12. Turn off the router
If you aren’t using your wifi, you could turn the router off. Sometimes, you might want to leave a big download running overnight. However, most of the time, you aren’t going to be using the network while you are asleep. It is a good idea to turn off all electronics at night and even unplug them. This is a safety measure against sparks causing appliance fires and it also a good practice to save the environment. Many electrical and electronic devices burn electricity even when they are in standby mode. So unplugging everything before you go to bed will reduce your electricity bill and also help save the planet by reducing the demand on power stations.
You could also turn off the router when you go to work. If there are a lot of people in your household, the last person to leave the house in the morning turns the router off and the first one to arrive home in the evening turns the router on.
The reason for this tip should be obvious. The fewer hours that your wifi system is active the less possibility there will be of a hacker attack. It will also deny your piggybacking neighbors access to your wifi for large chunks of the day. If your internet service is metered, this step will bring down your monthly bill.
13. Check on port 32764
Back at the beginning of 2014, it was discovered that the firmware for certain models of router kept a process that listened at port 32764. Having a port “open” is a security vulnerability and when the infosec community discovered the problem, the router companies involved removed the routine that listened for responses at that port. However, in April of that year, a firmware update introduced a procedure to open the port again.
A port is a number that represents an address for an application. In order for a port to be open, it needs a process listening on it. If hackers find out about obscure listening programs they can manipulate the program in order to cause damage to the router or the network.
It seems that access through port 32764 is a requirement for a hardware supplier, called SerComm. You probably didn’t buy a SerComm router, but this manufacturer supplies to Cisco, Netgear, Linksys, and Diamond. You can find a list of at-risk routers here. The good news is that the process that listens on the port can only be activated from within the network. Check if port 32764 is open at this website. If it is open, you need to contact your router supplier for help on this issue. Just closing the port is not a viable solution because it was opened on command without your knowledge and they can just open it again. If the router company can’t supply you with a patch to close off this vulnerability, ask for your money back.
14. Keep your devices healthy
The computers and other devices in your home could provide avenues for hackers to get onto your router. Some of the devices that connect to your network will be portable. Devices such as laptops, tablets, and smartphones are more likely to get infected because they likely connect to other networks and access the internet in public places. There are more possibilities for virus infection and intrusion outside of the house. Equipment that never leaves the house is only exposed to one internet access point and so is less likely to be infected.
You also need to be careful about people transferring files onto your computers with USB memory sticks. File copying offers an access method for viruses. So make sure that your computers have both firewalls and anti-malware software.
Make sure that your software is kept up to date and you allow automatic updates. Patches and new releases for operating systems and applications are often issued to plug security weaknesses.
See also: Best free Antivirus programs for Windows and Mac
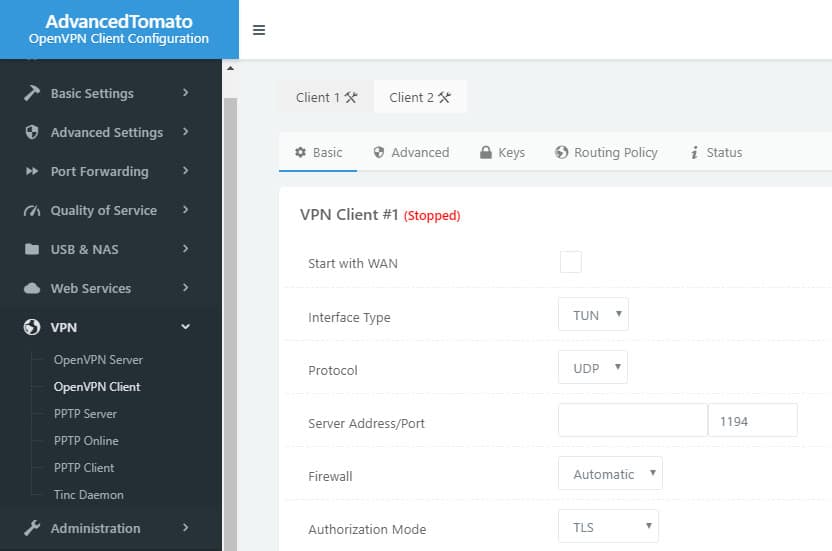
15. Use a VPN

Virtual private networks are primarily used to improve privacy on the internet. However, they also offer security benefits that help protect your router from intrusion. If you or other members of your family frequently use wifi hotspots in public places, such as cafes, using a VPN will help protect your devices from attack by compromised wifi hotspots. Hackers use “Man-in-the-middle” attacks to steal data from other users connected to the same network, and they can also be used to sneak malware onto your devices. When you bring those devices home and connect them to your network, your router becomes an easy target.
A VPN is also a good solution to the problems raised by wireless packet sniffers. A VPN encrypts all of the traffic from and to your computer all the way to a remote server that lies over the internet beyond your wifi router. That means intermediaries will not be able to fool you into a fake connection and won’t be able to get into your data stream by infiltrating your router. The protection offered by the VPN goes through the router, so even if the encryption provided by the router is stripped off, you still have VPN encryption to make your data unreadable.
16. Center your signal footprint

Most people keep their wifi router in the living room because that’s where the hookup is for a cable or phone line. Living rooms often face the street, so placing your router by a front room window sends half of your signal footprint to the outside world.
If you put your wifi router at the far wall of the living room behind the TV, the layout of your house or apartment may mean that the other side of that wall is inside a neighbor’s house. Walls offer greater resistance to radio waves than windows do. However, you are still giving half of your wifi coverage to your neighbors.
Find the central point of your home and place the router there. Keep in mind that the signal area of a wifi router is like a ball — it radiates out above and below as well as horizontally. So, if you have a two-story home, put the router right up by the ceiling on the lower level so upstairs gets service as well.
If your house is larger than the router’s signal footprint, centering the router in the middle of the house will give you the maximum coverage available and prevent the signal from passing outside.
If your house is smaller than the signal footprint, then you have several different options to reduce the signal strength outside of your home’s boundaries. You could use a 5GHz router instead of a 2.4GHz one because these have a smaller range and cannot penetrate walls as well. You can also try reducing the router’s range by wrapping foil around the antennas or even putting it inside a cardboard box. If you’re really dedicated, you can even paint your walls with anti-wifi paint to stop the signal from going outside.
17. Create a Faraday cage
Some homes get terrible cell phone coverage. In many cases, even if you are in an urban area that should get full bars, the signal availability drops as soon as you go indoors. This is not normal. This phenomenon is caused by the material that went into the construction of your home. Any metal in the construction material will attract radio signals and prevent them from passing through the skin of the home into your rooms. This is called a Faraday cage and although it is annoying for creating bad cell phone service indoors, it is great for trapping your wifi signal inside your house.
Construction materials that block your wifi signal from passing outside include foil membrane insulation embedded behind sheetrock in the walls. If your home’s internal walls have that insulation, you will have problems getting the wifi signal away from the room where the router is kept. Metal window frames reduce the amount of signal that passes through the glass of your windows, and reinforced concrete walls that contain metal bars will also prevent the wifi footprint from extending outdoors.
If your house doesn’t contain much metal in its outer walls, you can integrate metals into your decoration to block the wifi from extending outside. Ideas include aluminum cladding, which could go on the outside of the house to protect the walls, give your house a new look, and also block all wifi. Other ideas include curtains that contain metallic thread, copper wall coverings, a metal shelving unit, and metal screens.
If metal wouldn’t feed into your interior design, then check out paint that blocks wifi signals. You could also consider shiny metallic wallpaper printed on foil.
18. Turn off your network when going away for long periods of time
If you’re going on holiday or won’t be needing your home wifi network for a few weeks, you should turn it off. Hackers can’t work their way through your network when it isn’t on. Not only will turning off your router help to reduce security risks but if you unplug it, you can also prevent it from being damaged by power surges.
19. Set up a separate network for IoT devices
IoT devices are becoming more and more common in our homes. We’ve now got smart TVs, smart fridges, our own virtual slaves in Alexa and Google Home, as well as a host of other IoT devices in many of our abodes. With new technology developments and the rollout of 5G, this number is only set to expand. This is concerning in two ways:
- The more IoT devices, the more endpoints, and the greater the number of potential entryways for hackers.
- IoT devices have a poor security track record.
With this in mind, those who are especially security-conscious may want to consider setting up a separate wifi network for their IoT devices. Although it may not technically be part of securing your home network, setting up a second one allows you to separate your home’s digital assets.
By doing so, you can put everything valuable on one network, such as your computers, phones and any important data. On the other network, you can put all of the less secure IoT devices, as well as anything that’s not so important. You could even use this second network for guests, preventing them from introducing threats into your main network
With two separate networks, you can eliminate the risks of poorly secured IoT devices acting as an opening for your main network. If hackers do find their way into your IoT network, all they’ll find is the other IoT devices, and they won’t be able to work their way onto your computers or phones, nor could they steal or mount ransomware attacks on your important data.
Safe wifi
News headlines about ransomware and identity theft are worrying. The thought that someone can intrude into your wifi feels a little like the threat of being attacked or burgled in your own home. You don’t have to be a technical expert in order to improve the security of your home wifi network, you just need to be a little smarter in your habits.
Simple solutions to security problems are usually the best. As you can see, none of the solutions in our list cost money. The majority of these suggestions are common-sense steps that anyone can take. Even the more complicated ideas, such as hiding the network or MAC address filtering, only require you to explore the options available to you in the wifi router’s console.
Make sure you keep your personal data safe from identity thieves and prevent tight-fisted neighbors from stealing your internet by running through the recommendations in this guide.
Do you have some ideas about improving wifi security? If you can think of some good ideas that we have overlooked, leave a message in the comments section below and share your knowledge with the community.
See also:
Image credit: adventure connection via Pixabay, licensed under CC0
This write up is awesome, and is exactly what I need to somehow stop my neighbours in this apartment building from gaining access to my internet.
It’s a security issues no doubt, but my precious bandwidth is being eaten up by these clowns.
Thank you again, will factory reset my router in the morning, and use these recommendations asap!
That was, by far, one of the most thorough, easily understood, and informational post regarding cybersecurity at home. Well done. I have a neighbor or some sort of wifi beacon device within my house that captures every BT/wifi capable device as soon as you step onto my property. It’s not long before the phone is totally taken over with a customer OS overlaying with complete remote access 24/7. Cannot find the beacon or stop it. Any advice??? Has been occurring for 1.5 years.
very important article .. thank you for sharing info
Your articles taught me a lot! This is my 1st comment here, so I just wanted to give you a shout-out and tell you how much I enjoy reading your blog posts.
Your post is a big help for people who is planning to secure the wireless network at home.
This is pretty solid advice overall. However, switching to static addresses could get really messy for mobile devices. Also, I’ve never seen advice like regarding the Faraday Cage. Why not turn the power level down?
In addition, mesh solutions are available that allow for zones of coverage to be made available through a home or business by putting up multiple access points that work together. The power could be turned down on each one so that it provides a specific and controlled coverage area. Such solutions cost more than an all-in-one router, however it’s not as much as you might think. You can get more even 5ghz coverage and wouldn’t have any concentrated strong RF source blasting out in a particular area while trying to cover an entire house.
Thank you for your time in writing About it. Soon I wiil figure out how good it is in my situation. 🙂
Some sort of mistery 🙂 per Last months I am Just continuesly geting troubles or in Router side. Or my PC gets somehow hacked down. The funny part is that I Just want to start locally on PC with hyper-v Virtual mashine that runs Linux to handle as website development enviroment and local server. And tears of fears appears when downloads and content is completely wrong. I have huawei router/switch which is living his own life after 2 +- running hours.
Lan port nr 1 for some reason became marked as “bro” And I have no IPtv on network and WiFi is switched off. Then some magick hapend one day later I noted that on Windows 10 pc, Lan network conections for some reason got theyr own IP adresses out of the sky…
And Then totall mess is going on with pc as whoole.
Avast doesnt sees any suspicious activity or cake sites. So that leaves me without any klue where the heck from all its comming in to me.
After securing acording your prescribed methods. I believe it is a must find some kind of monitoring tool that could be watching who is messing in. If have idea what could be used for that role that would be great.
Fantastic Information, but please I”l like to know can an antivrus help protect home networks from hackers
Hi, Julian,
Antivirus systems sweep for malicious software that has already been installed on endpoints. In order to protect your network from hacker intrusion attempts, you need a firewall. A major entry point that hackers use is through infected websites and disguised downloads. So, pay attention when your browser warns you against accessing a Web page and don’t download attachments on emails from people that you don’t know. Also, be very wary of clicking on links in emails because many of these are fake and used by hackers to gather your credentials to a Web service.
Thanks so much. Very informative.
Great article. Thank you
I just bought a TP-Link WiFi 6 extender to get better coverage on my router network. Is it safe to use? Can it read my data and report that back to this Chinese company?
Hi, Michael,
No, it can’t. A WiFi extender just rebroadcasts signals travelling between Wireless APs and endpoints. That traffic is already encrypted. There are worries that the Chinese can crack WPA2, which is the encryption used on WiFi systems. However, additional encryption is applied to most of your Web traffic through HTTPS and there is no news that the Chinese can crack that. In order to send copies of your traffic out to the Chinese authorities, the extender would need to be able to communicate with your WiFi hub/router and open a connection to the internet. Extenders don’t have that capability — if they did have, they would be switches and not extenders. If you are still worried about this, use a VPN that is on all of the time. This adds an extra layer of encryption to all of your communications that your extender cannot remove. Make sure the VPN uses 4096-bit RSA encryption and 256-bit AES encryption — the Chinese can’t crack those.
Cheers,
Stephen
This is incorrect. It is well within possibilities of current technology for a repeater to snag info and rebroadcast outside the network. USB cables can do this now.
This is such an awesome blog this is very informative blog… this will really helps me alot while connecting wireless network thank you alot!!
me 2 ….
Important information to be shared so everyone can enhance the security of their digital home assets. I would like to read more on the topic regarding how to safeguard your Home Network while still leveraging IoT device functionality.
Hi, bjertel,
IoT devices are a major weakpoint at the moment. Take a look at my article on Breach Detection Systems for more information on major points of weakness in any network. That article is more geared towards businesses, but some of the recommended security systems are also available for home use. For your home network, I would recommend McAffee, Crowdstrike, or Symantec.
Cheers,
Stephen
Excellent article, thank you. It highlighted a few items I need to attend to.
One area that’s worth covering?
What do you think of password managers in general? and any in particular?
I.e. I have Kaspersky Password Manager as part of my general security suite, and my browser of choice is Firefox which also has a password manager built in.
My approach is to not use it for critical sites such as bank accounts but use it for all the other sites. Are there any logons I should avoid automating? e.g. Wi-Fi logon, router and server admin, PC management, etc
What is your opinion? a major security issue best avoided, a great idea that encourages use of more secure long and complex passwords?
Hi, Adrian,
Your strategy of using a password manager is a winner. It is much better to use a password manager that enables you to deploy complex passwords. I understand your concern over the possibility of the password manager itself being compromised. Your choice of Kaspersky was an excellent decision. That business relies on its reputation for security and if its password manager had a security flaw, the whole business would collapse. So they have billions at stake and won’t let it fail.
Its so complicated I prefer to pay someone a techie who can assist with security issues. Is there someone I can rent and at the same time he or she educates me at the same time? Reading all this is great but for an aging woman who prefer in person assistant as I am lost without outside help.
A security lock all my WiFi
much Thanks
All the points explained in this post is really very good and simple to understand.
Great tips on network security. Well worth the time…
Lots of good info here, but no idea how to do most of it!
Amazing artical! Thank you!