When it comes to online crime, there are many forms in which it manifests itself.
Within the corporate world, the greatest perceived risk at this point in time may well be a data breach, due to the publicity afforded to such lately, and the costs and reputational damage attached to such an occurrence.
But, in reality, the far more likely crime likely to be experienced by a firm right now is social engineering, a crime in which the aim is to acquire something of value from a victim, typically information, money, or both.
And recently, a specific type of social engineering has risen hugely in popularity; and that is what we will be looking at today.
Known as CEO Fraud, this type of crime has already proven extremely costly to those companies that have succumbed to it.
CEO Fraud
CEO Fraud is all about deception – the person behind this particular type of scam is looking to convince a company employee that they are a senior and authoritative figure within the organisation, such as a finance director or C-level executive, in the hope that they can then dupe them into sending a vast amount of money their way.
In order to be successful, the attacker will need to be convincing, and that means coming pre-armed with a wealth of information about the company they are targeting.
For the most part, this information will be based around the structure of the organisation, such as the reporting structure and managerial and executive positions and relationships.
Once the key figures have been identified, the next step will be to learn more about these figures – names, email addresses. schedules, when they’ll be travelling or on holiday and, even more importantly, who if anyone has recently joined the company.
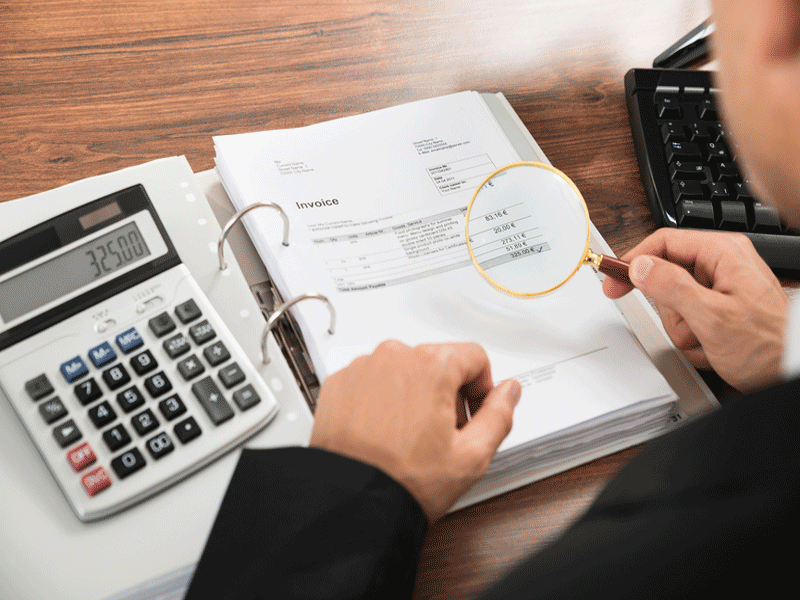
The attacker will also need to discover who within the organisation is responsible for signing off on money transfers, be that an accountant or someone within the finance department.
At this point you may be surprised to learn that much of this information is incredibly easy to find – corporate websites often publish the names, job roles and contact information of their key employees.
Failing that, social networks are often a good secondary source of information – professional networking sites are packed full of juicy information about people of all levels within any given organisation.
Likewise, social sites can also be a great place to turn to for an attacker attempting to determine someone’s movements – people are far too keen in their posting of holiday plans and business trips, given that anyone can read what they have written.
Once an attacker has acquired such information, though, they can commence their attack.
Typically, that involves emailing an appropriate finance employee, preferably someone quite new to the role if possible, and pretending to be the CEO or other high-ranking member within the company, and asking for an urgent money transfer to an account under their control.
Legitimacy will be added through the use of a spoofed email address which will look like the purported sender’s real email address.
The email will say the transfer request is urgent, prompting the victim to respond quickly and without thinking, or at least that will be the attacker’s intent.
And such tactics do work – a vast amount of money has found its way into the criminal underground in this way recently.
How can businesses, especially smaller ones, avoid falling victim to CEO Fraud?
Defending against cyber criminals is not a simple matter at the best of times but there are a number of technical controls which can mitigate the risks posed by many of the attacks faced by businesses today.
Then there are the policies, procedures and processes put in place to guide people toward secure working.
But of course people are people and, as I often say, they are the weakest part of any defensive strategy as they lack the absence of logic found in machines.
Thus defending against CEO Fraud is much easier said than done.
The best advice I can offer is to remain sceptical of, well, everything really – it is our trusting nature that often gets us into trouble, alas.
So if you ever receive an email asking for a large money transfer to be made in a hurry, stop yourself before complying with it. It takes no time at all to check in with the apparent sender of the email – by using their real email address rather than replying to the message you received or by phoning them – and it may just save your company a small fortune.
And if you sit the other side of the boardroom table consider how you may educate your employees about CEO Fraud so they are better prepared to resist it:
- Inform everyone within the organisation if you have been targeted by CEO Fraud. By simply sharing such a rogue email you can highlight everything wrong with it and encourage your staff to be on the lookout in the future.
- Put policies in place that require additional checks and balances to be put into place that prevent any one person signing off on a large transfer of funds
- Encourage extra vigilance at key times – many CEO Fraud and other phishing emails are sent late on a Friday or just prior to public holidays when attackers know attention levels are at their lowest
- Remind people of all levels within the business of the dangers of sharing too much information online, be that on social media or personal blogs