Note: Skype shut down on May 25th, 2025, and is no longer available. Microsoft recommends switching to Teams, but Zoom is also a solid alternative. Read our guide on how to delete your Skype account and keep your data safe.
Skype is one of the oldest and most popular voice and video chat services on the internet. In March 2020, Microsoft revealed Skype had 40 million daily active users. Although many competitors have surfaced, Skype remains popular around the world.
So is it safe? Is it private? What should Skype users be aware of when they make calls and send messages? This article will answer these questions and more. Note that we’ll be focusing on standard Skype apps rather than Skype for Business.
Microsoft data collection
Microsoft acquired Skype in 2011, so Skype shares a privacy policy with all other consumer Microsoft products. A Microsoft account is required to use Skype. Unfortunately, that makes Skype’s data collection practices very opaque. Skype isn’t even mentioned explicitly in Microsoft’s privacy statement, and that statement doesn’t even specify what information is collected.
That being said, we can interpret the privacy statement to deduce some of the data that Microsoft collects about Skype users.
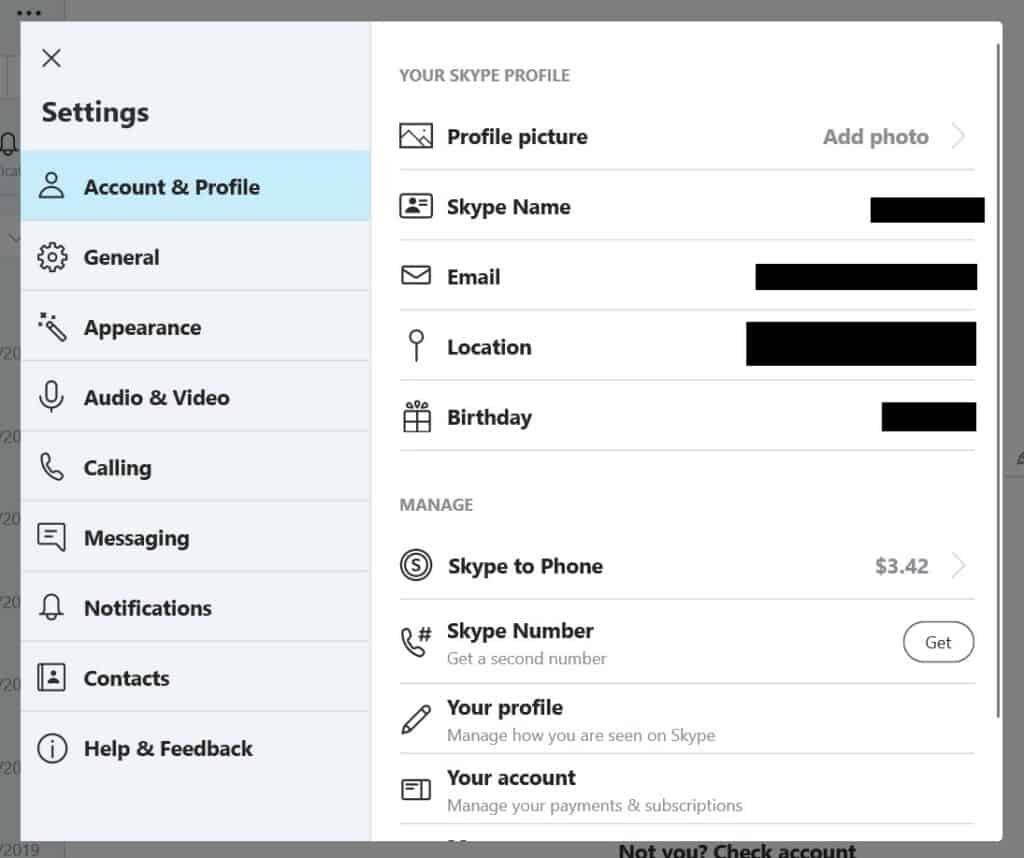
A Skype profile consists of:
- Profile picture
- Username
- Password
- Email address
- Location
- Birth date
- Contact list
If you use Skype to call phones, then Microsoft will also require your payment information.
Microsoft also records user interactions, which might include:
- Who you call
- Time and duration of calls
- Chat history
- Sent and received files
- Phone numbers called
- Activity status
Microsoft says it also obtains data about users from third parties, which might include data brokers.
Microsoft uses personal data for targeted advertising, personalization, research and development, and to improve its products. Your data is shared with Microsoft affiliates, subsidiaries, and vendors. It can also hand over your data in response to a legal request.
You can manage some but not all of the data that Microsoft has about you using its online privacy dashboard.
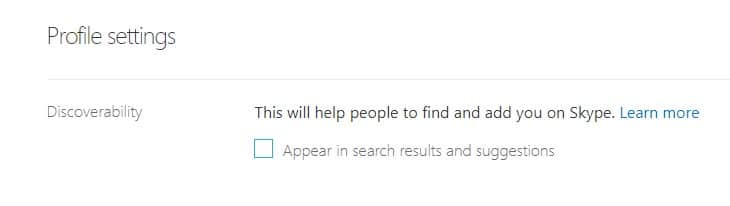
Discoverability
Skype by default makes users easy to find through the search feature. If you don’t want to appear in search results or recommendations, you can disable this option in your profile settings.
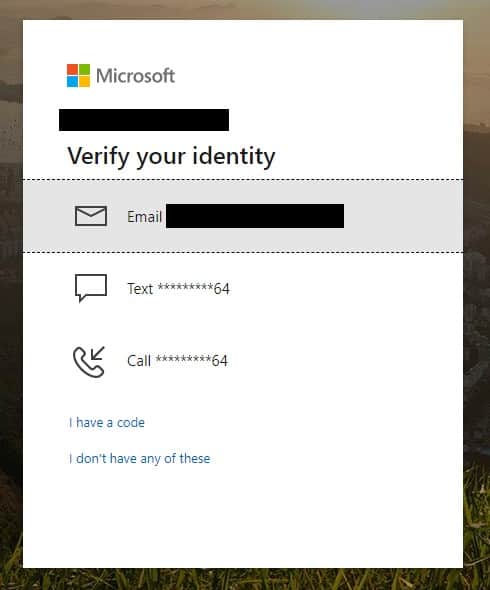
Set up 2FA
Microsoft offers all account holders the option to set up two-factor authentication. We strongly recommend doing so, as it’s a great deterrent for would-be hackers.
Two-factor authentication, also called two-step verification, requires you to enter a one-time code sent via email, text message, or authentication app, in addition to your password.
You can also opt to log in with a security key, which usually comes in the form of a USB device that must be plugged in when logging into your account.
Call recording
Participants in Skype-to-Skype calls can record their calls and store them on Microsoft servers for up to 30 days. This is a built-in feature. During that time, they can download the video to use as they please. All participants will be alerted if a call is being recorded. Screensharing is also recorded.
Encryption
Skype doesn’t use end-to-end encryption by default. That means every message, call, and file can be viewed by Microsoft.
But as of 2018, Skype offers end-to-end encryption if you use the “Private Conversation” feature. To start a Private Conversation, select “New Private Conversation” from the compose menu or the recipient’s profile. The recipient will receive an invite, and all calls and messages in that conversation will be encrypted end-to-end until terminated. Note that users can only participate in one private conversation per device at a time. You can switch the private conversation to another device, but anything sent and received can only be accessed on the device that is currently being used.
By default, voice, video, text, and files sent between Skype users are encrypted, but only between your device and Microsoft’s servers. That data is decrypted once it reaches the server, allowing Microsoft to snoop if it so pleases. Given Microsoft’s history with the NSA, it’s best to assume nothing you do on Skype is kept private.
For each call you make, your Skype client creates a unique 256-bit AES encryption key for that session. This session key exists as long as communication continues and for a fixed time afterward, according to the company. When you place a call, Skype transmits the session key to the person you are calling and that session key is then used to encrypt messages in both directions. Again, this is not end-to-end encryption.
Calls made between Skype and normal landline or mobile phones are not encrypted at all. Voicemails are encrypted when you download them, but they are stored as an unencrypted file on your device.
Instant Messaging
Instant messages sent without using the Private Conversations feature are encrypted with TLS (transport-level security) between your Skype client and Microsoft’s cloud servers — at which point are decrypted.
Mark Gillett, Skype’s chief development and operations officer, said in a BBC article that that the company would give the police and other government authorities access to messages if “a law enforcement entity follows the appropriate procedures” and if doing so was “technically feasible.”
Microsoft pinging URLs
In 2013 an Ars Technica investigation found that Skype “regularly scans message contents for signs of fraud, and company managers may log the results indefinitely. And this can only happen if Microsoft can convert the messages into human-readable form at will.”
Part of the investigation which saw a security researcher create specially crafted URLs which were sent over Skype’s IM system, counters Skype’s claims made in 2007 that it couldn’t conduct wiretaps because of strong encryption and complex peer-to-peer network connections.
Data for training AI
Microsoft uses collected personal data — across all Microsoft products — for training its artificial intelligence systems. In some case, it manually reviews “short snippets of voice data that we have taken steps to de-identify.”
This is the case with the Translator service, which was launched in 2015. This feature provides users with near real-time audio translations during phone and video calls. An article by Motherboard revealed that human contractors were listening to conversations.
Malware
Skype is targeted by certain kinds of malware as well as being a distribution medium for other types of malware. Although all known security vulnerabilities in Skype have been patched, we’ll cover a few past incidents here:
In February 2016, researchers at Palo Alto Networks revealed that a piece of malware called T9000 was specifically targeting Skype users. Once installed the software can record Skype video and audio calls, and upload them along with text chats to a server.
There is a caveat however. Even with the malware installed, the user must still give explicit permission for it to access Skype, though it masks the request so the user doesn’t know it’s malicious.
“The victim must explicitly allow the malware to access Skype for this particular functionality to work. However, since a legitimate process is requesting access, the user may allow this access without realising what is actually happening. Once enabled, the malware will record video calls, audio calls and chat messages,” the researchers said.
Keeping Skype and your operating system up to date is the best way to prevent malware. Antivirus is also helpful.
Spam and phishing
Skype is more than two decades old, which means there are a lot of abandoned accounts out there. If a cybercriminal manages to hijack one of these accounts, they can use it to spread malware and phishing links to everyone in the account’s contact list. This is exacerbated by users who don’t vet their contacts and accept requests from strangers.
In 2019, the Rietspoof malware was spread primarily through Skype spam. This was a Trojan designed to infect systems so it can download more intrusive and potent malware.
Security firm F-Secure in 2016 revealed that criminals were posing as U.S. officials offering help to Swiss nationals find information on how to file for visas to visit the United States. They tricked victims into downloading the QRAT malware.
A simple rule will prevent you from ever falling victim to spam and phishing on Skype: never click on unsolicited links or attachments, especially from contacts you haven’t communicated with in a while.
Skype exposes IP addresses
Skype users can figure out callers’ IP addresses by simply listing all the TCP connections to your device. This can be done with a single command in the Windows Command Prompt, for example.
An IP address is a unique sequence of numbers and decimals that identifies a device and its location. While an IP address in-and-of itself may not be hugely valuable, it could be used together with other personal information against someone.
One workaround to this is to use a VPN to hide your real IP address. When you connect to a VPN server, it looks to the wider internet as if you’re connecting from wherever that server is located. So, for example, if you connect to a VPN server in Sri Lanka, you’ll have a Sri Lankan IP address for the duration of your online session.
TOM Skype
In March 2013, Jeffrey Knockel, a computer-science graduate student at the University of New Mexico, revealed that the special version of Skype which Chinese users are forced to use — known as TOM Skype — was allowing the Chinese government to gather information on its users including information about their political beliefs, as well as censoring what they can say to one another.
In May of the same year, well-regarded Russian publication “Vedomosti” reported that both the national security agency and the police are able to tap Skype conversations without even filing a court order.
Skype alternatives
The days have long gone since Skype was the only VoIP player in the commercial market. Users now have a variety of services to choose from — many of which are more secure. Here are some of the options, ranked from most secure to least secure:
- Signal: If you only need to call one person, Signal is the most secure option out there. It’s a messaging app that prioritizes security and privacy above all else. All calls and messages are encrypted end to end unless the other party is using normal SMS or MMS text messages. However, it only supports calls between two users.
- Facetime: Facetime supports group calls of up to 32 people. It’s one of the only video conferencing apps that offers end-to-end encryption on call with more than two people. You will need a newer iPhone or iPad to use it, though. iMessage is used for text messages. No identifying information is stored by Apple except for who was called and network configurations, which is stored for 30 days.
- WhatsApp – A popular messaging app worldwide, WhatsApp uses Signal’s secure communication protocol to encrypt voice and video calls end to end between users. It’s not quite as hardened as Signal, but it’s more convenient. Text messages are encrypted in the same way. Up to four people can join a video call.
- Google Duo: This app is available for smartphones or in a web browser. It encrypts all calls end to end so that Google has no access to call content. However, Google collects a lot of other information about account holders. Up to 12 people can join a call.
- GoToMeeting, Google Meet, and Zoom – These services work pretty much the same way and offer similar security. They are useful for video conferencing with larger groups of people. GoToMeeting is web-based, meaning everything takes place in your web browser. Zoom requires installing a native app. Google Meet works either way. Invite codes are sent out to participants to join calls. The host has plenty of control over attendee privileges and permissions. TLS encryption is used in transit, but calls are not encrypted end to end between users. GoToMeeting, Google, and Zoom have access to call content when it reaches their servers.


Can a scammer use deepfake Ai generated voice messages on Skype?
So is it safe to perform video calls and could the other party record the ongoing video calls.
Skype is good for social and casual interaction. But for business video calling, I would recommend using tools like R-HUB HD video conferencing servers. It works from behind the firewall, hence better security. Plus works on all platforms.
How is Wire a direct equivalent to Skype when it doesn’t support file transfer?
I know for a certain period of time that skype is not secured at all for personal or business use. That is why I could never rely on it for my company matters and communication. I use Brosix and am quite satisfied with the product. It has many features apart from the chat that help me out in the office. Definitely recommend it to you as an positive alternative of Skype. 🙂
I know for a certain period of time that skype is not secured at all for personal or business use. That is why I could never rely on it for my company matters and communication. I use Brosix and am quite satisfied with the product. It has many features apart from the chat that help me out in the office. Definitely recommend it to you as an positive alternative of Skype.
And then there’s Wire, a pretty direct equivalent to Skype, but with open-source clients and end-to-end encrypttion
+1 for Wire too–it’s the perfect way to wean yourself off Skype and has a good set of additional security features for average users.