“Malware” is another word for nasty programs that mess up computer systems. It’s always changing, like a never-ending battle between the good guys (security pros) and the bad guys (cybercriminals). The malware world shifts a bit yearly, but you can spot some long-term trends if you look at the data.
Even with many anti-malware deterrents, cybercriminals aren’t quitting anytime soon. They’re still in it for the money. But they’re getting sneaky, moving away from old-school malware and targeting new weak spots.
Right now, it looks like hackers are eyeing up two main areas: IoT (all those smart devices) and email for sneaky infections. They’re really focusing on big targets like businesses and governments, especially for ransomware attacks, rather than just your average internet user.
Here’s a rundown of the most interesting malware statistics:
1. Employees with infected machines are spreading viruses more broadly
In 2020, 61 percent of organizations experienced malware activity that spread from one employee to another. In 2021, that number rose to 74 percent, and in 2022, it hit 75 percent — the highest infection rate since the SOES survey began in 2016.
The increase in the employee-to-employee spreading of malware could be for any number of reasons; for instance, phishing attacks are becoming more sophisticated, while employees may encounter more distractions while working from home.
2. Ransomware attacks frequently lead to disruption of business
In its 2020 State of Email Security Report, Mimecast found that 51% of organizations experienced a ransomware attack that led to at least a partial disruption of business operations. This rose to 61% of organizations in 2021.
In its most recent report, Mimecast changed its phrasing, so we can’t directly compare this year’s results. Still, in 2022, 35 percent of respondents blamed a poor degree of cyber-resilience for business-disrupting cyberattacks.
3. Organizations in the US are among the most prepared for cyberattacks
Organizations worldwide report ransomware attacks impacting business, but it seems businesses in the US are increasingly prepared, with 47 percent having cyber-resilience strategies in place. However, in places like the Netherlands, only 21 percent of companies have a plan to deal with any cyberattacks they might face.
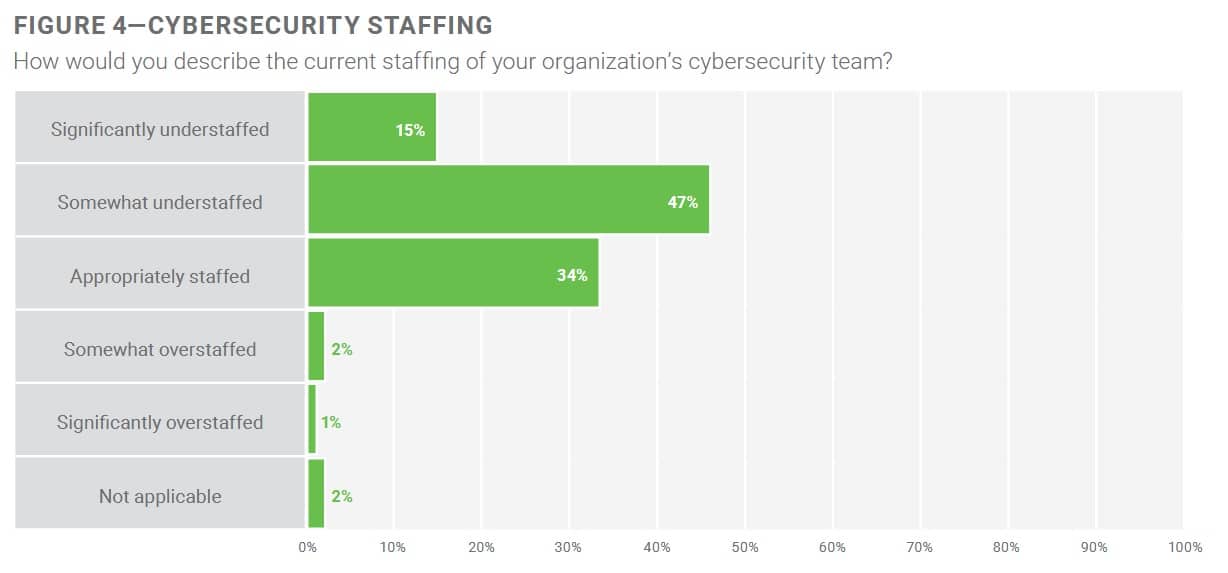
4. Almost 70% of organizations may have understaffed cybersecurity teams
In its 2022 State of Cybersecurity Report, ISACA found that 69 percent of cybersecurity professionals believe their organization’s cybersecurity team is understaffed, up from 61 percent last year. Understaffing among organizations, including businesses and government, could strain existing staff and lead to an increased risk from malware threats.
Almost half (47 percent) reported their organizations were “somewhat” understaffed, while 15 percent reported they were “significantly” understaffed. A further 34 percent reported that their organization is “appropriately” staffed, while just three percent reported being either “somewhat” or “significantly” overstaffed.
The demand for workers is also increasing year-over-year. From C-suite executives to technical and contributors, jobs across the cybersecurity industry continue to go unfilled as demand outpaces the growth in the number of workers with the requisite skills.
5. Malware trends change rapidly
The SecureList IT Threat Evolution report for Q2 of 2022 shows how malware-for-hire is continuing to evolve. It stresses that organized groups increasingly develop cross-platform malware to compromise as many systems as possible on a target network.
This report also highlights vulnerabilities in Windows logging tools, which have recently seen a real resurgence (most famously in the Log4J scandal that saw organizations scrambling to patch various applications).
6. Phishing sites are now an incredibly popular attack method
Phishing sites are typically designed to look like the official version of other websites. PayPal is a commonly-mimicked site, for example, as gaining access to users’ PayPal credentials can be distinctly profitable for hackers. Banking and social media sites are also fairly common targets.
Read more: 70+ common online scams used by cybercriminals.
7. Google continues to squash potentially harmful sites
According to Google’s Transparency Report, 3.849 million browser warnings were shown to users trying to access sites deemed dangerous by Safe Browsing. category, as of August 7, 2022. Additionally, 1.6 million users saw warnings in their search results that said the site they were about to visit might be harmful.
If we examine the larger overall data, we can see that the number of warnings has decreased dramatically over the last decade. It’s unlikely this is because fewer dangerous sites are out there; rather, Google has just gotten better at identifying them and removing them from results, resulting in fewer warnings overall.
8. The number of malware attacks is rising again
In 2020, the number of new malware attacks declined for the first time since 2015. However, according to SonicWall’s 2022 Cyber Threat Report, this was just a temporary dip, with malware attacks now sitting at 10.4 million per year, roughly where they were back in 2018.
9. New malware variants decreasing year-over-year
SonicWall reported 5.4 billion malware attacks took place in 2021, which sounds bad but actually represents a small decrease from the previous year. The first six months of 2022 saw 2.75 billion attacks, and if these numbers hold, we’ll end up with roughly the same annual number of attacks.
10. Domain Generation Algorithms are still hampering malware mitigation efforts
Domain Generation Algorithms, or DGAs, allow malware architects to automatically generate a large number of domain names which then serve as rendezvous points to help control and collect data from the active malware infections. DGAs make investigation and analysis efforts difficult, which in turn makes it difficult to shut down botnets.
Over 40 malware families employ DGAs, including well-known malware including CCleaner, Emotet, and Mirai. SonicWall identified over 172 million randomly-generated domains in 2019.
11. Iran is the most impacted country for malware infections distributed by mobile
Kaspersky Labs reported that of all the users of its mobile security product worldwide, Iran faced the highest number of malware attacks in Q2 2022 with the share of mobile users affected sitting at 26.91 percent. This is actually down almost 10 percent from the quarter prior, when 35.25 of mobiles were attacked.
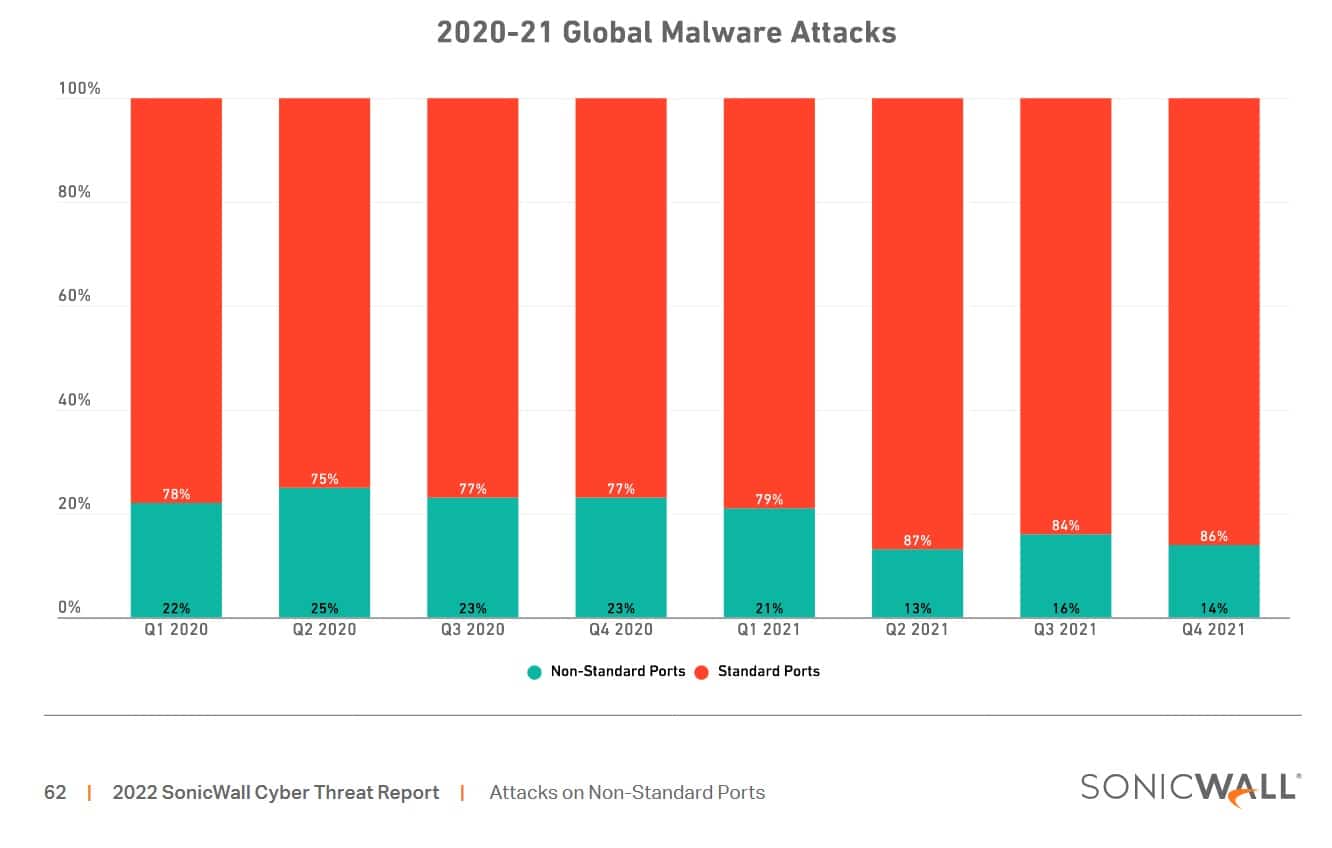
12. Malware attacks on non-standard ports fall by 10 percent
SonicWall’s 2022 report found that attacks on the tens of thousands of non-standard ports available decreased to nine percent in 2021. This is a significant drop since last year and the lowest incidence rate since 2019. The vast majority of attacks still (and likely will remain) a problem for standard ports, such as HTTP (port 80).
13. Ransomware and IoT malware are more common than ever
SonicWall’s 2022 mid-year report shows that the amount of ransomware has actually decreased year-on-year, with an average of around 40 million attacks per month (down from 50.5 million in H1 2021).
However, it’s important to realize that these numbers are already significantly higher than in previous years, largely due to the explosion in ransomware that occured during the COVID-19 pandemic.
14. Over 270,000 new malware variants were detected in 2022
SonicWall identified 270,228 “never-before-seen” malware variants in the first half of 2022 alone. That’s an increase of 45 percent over the same period last year, and averaged out at over 1,500 brand new variants every single day. In March alone, almost 60,000 new variants were discovered, which is a new record.
Related post: Best Malware Detection Tools
15. PDFs and Microsoft Office files were used in almost 30% of new malware detections
In the first half of 2022, about 30% of new malware detections involved PDFs and Microsoft Office files like Word and Excel. This trend highlights cybercriminals’ strategy of using common file types to spread malware, with Microsoft Office files accounting for 10.28% of detections and PDFs for 18.27%.
This shift in malware delivery methods underscores the need for increased vigilance with familiar file types and emphasizes the importance of robust cybersecurity in organizational settings. These findings are detailed in reports by SonicWall, SmartDataWeek, and TechReport.
16. As cryptocurrencies rebounded, so did cryptojacking
Cryptojacking rose by more than 30 percent in the first six months of 2022, which is huge considering it had already increased 19 percent the year prior. The graph below may appear to show that this is a downward trend but SonicWall observed a similar “summer slump” last year before an uptick in cryptojacking towards the end of the year.
The chaotic ups and downs in cryptojacking activity highlight just how much cybercriminals respond to market demands. Malware has always been about achieving the best possible outcome (stolen information and money) with the least amount of effort. An increase in the use of website malware blocking technologies is why phishing sites are far more popular, but cryptojacking also makes for an easy money-making venture for cybercriminals who, for all intents and purposes, follow the same principle as Wall Street brokers: “buy low, sell high”.
17. Coinhive’s shutdown revealed its startling contribution to cryptojacking
Although the Coinhive cryptocurrency mining service was legitimate, it was quickly co-opted by cybercriminals who installed it surreptitiously onto websites to collect cryptocurrency revenue.
Originally launched in 2017, Coinhive voluntarily shut down in March 2019. SonicWall found that after the Coinhive shutdown, cryptojacking hits on its cybersecurity monitoring network fell by 78%.
18. Cerber takes the lead in hackers’ favorite ransomware tool
Notably, Cerber is part of what’s known as “Ransomware as a Service” or RaaS. Cybercriminals can hire others to launch attacks using the Cerber malware and receive around 40 percent of the paid ransom. In 2017, SophosLabs investigated 5 RaaS kits and found that some can be extremely inexpensive (less than $40), while others can exceed several hundred dollars to purchase and employ. However, they’re highly customizable, and hackers appear to operate their ransomware services with a surprising degree of professionalism.
19. Cerber is the top ransomware signature of H1 2022
Cerber reclaimed its crown as the most common ransomware signature in the first half of 2022. It had previously been pushed to second place by Ryuk, but now the tables have once again turned, with Cerber present in 43 million infections. SamSam, which was previously another top contender, has been shunted out of the top three by GandCrab, even though the group behind this officially shut up shop in 2019.

20. 60% of total malware attacks were sent using encrypted traffic
Threat actors like to send malware attacks over encrypted SSL/TLS traffic. Encrypted channels make detection and mitigation more difficult, resulting in higher success rates for the malware packages in question. However, WatchGuard reported that in Q1 2022, 60.1 percent of all detected malware were attacks of this nature, down from 91 percent in Q2 of 2021.
21. Log4j breach shows threats can come from any angle
In 2021, a vulnerability was found in a hugely popular logging tool that allowed attackers to remotely run code on affected systems. The scale of this problem (and its potential impact) was far-reaching, and while a fix was rapidly rolled out, the incident only further illustrates the need for regular software updates and a strong cyber-resilience plan.
22. Universities continue to be appealing targets
In June 2019, the University of California made the headlines after the IT systems at the UCSF School of Medicine were involved in a ransomware attack by the hacking group known as Netwalker. A cure for COVID was the major project the medicines team was working on at the time.
Netwalker had planned to gain access to financial records held by UCSF, who cited billions of dollars in annual revenue. The hacking group demanded a ransom payment of $3 million. The ransom attack wasn’t entirely successful, but Netwalker still managed to negotiate a ransom payment of the bitcoin equivalent to $1,140,895 paid by the medicines group to rectify the damage caused by the cyberattack. The BBC also reported that the hacker group was also responsible for two other university-targeted cyberattacks in 2020.
This is far from the only university targeted, though. Higher education facilities across the states fell victim, with attackers also hitting colleges across Scotland, the Netherlands, and Canada.
23. Enterprises are the main target for ransomware
Coveware noted that professional services were the most common targets for ransomware in Q2 of 2022, accounting for 21.9 percent of all attacks (up from 20.2 percent the previous quarter).
Next in line were public sector organizations (14.4 percent), with healthcare organizations at 10 percent and software services following at 9.4 percent. Financial institutions were significantly less popular this quarter, dropping from 8.9 percent to 6.4 percent in just three months.
24. Educational establishments will often pay huge ransoms
In June 2019, the University of California made headlines after the IT systems at the UCSF School of Medicine were involved in a ransomware attack by the hacking group known as Netwalker. A cure for COVID was the major project the medicines team was working on at the time.
Netwalker had planned to gain access to financial records held by UCSF, which reported billions of dollars in annual revenue. The hacking group demanded a ransom payment of $3 million. The ransom attack wasn’t entirely successful, but Netwalker still managed to negotiate a ransom payment of the bitcoin equivalent to $1,140,895 paid by the medicines group to rectify the damage caused by the cyberattack. The BBC reported that the hacker group was also responsible for two other university-targeted cyberattacks in 2020.
Maastricht University also chose to pay €200,000 to attackers in 2019, though this was later recovered. Meanwhile, the University of Utah paid $457,000 to decrypt data locked by ransomware, though in many cases, victims don’t actually regain access to their files after paying.
25. Ransomware payment demands are increasing in size
One of the biggest reasons hackers appear to prefer ransomware versus more traditional viruses and malware is because of the payoff. Ransomware payments tend to fluctuate in size, but generally always trend upwards. By Q2 of 2022, the average payment was $228,125 with a median of $36,360.
Malware projections for 2024 and beyond
Based on what we’ve seen so far, we can expect to see a few key takeaways for the remainder of the year:
- Malware-infected sites will likely continue to fall out of favor and decrease in volume
- Cybercriminals will continue to target larger enterprises with malware in the hopes of securing a large, one-off payment
- The demanded ransomware payment amount will continue to increase
- The cryptojacking threat to IoT devices will grow, in no small part thanks to the growing number of unsecured IoT devices that consumers purchase in ever-increasing numbers
There’s no telling what new threats may emerge, and how the malware landscape may shift. As major security companies have reported in the past, a fair amount of activity tends to increase in Q4 in most years, which is often associated with the holiday shopping season.
As ever, hackers tend to be reactive instead of proactive, going for low-hanging fruit whenever possible, or easily-exploited vulnerabilities in systems where they can be found. Their tactics tend to change only when their efforts become unprofitable.
It’s also hard to ignore the ever-present danger posed by state-sponsored malware attacks, which are rarely profit-driven and tend to be politically motivated. Such attacks will likely increase in 2024, with all eyes on Russia, China, and North Korea.
FAQs about Malware
What are the most dangerous types of malware?
The most dangerous types of malware include ransomware, spyware, trojans, and worms.
Ransomware is a type of malicious software that attempts to extort money from victims by locking their files or devices until they pay the cyber-attacker a ransom amount. Spyware is malware that allows attackers to monitor activity remotely on an infected computer without the user’s knowledge or consent. Trojans are programs disguised as legitimate software that grants remote access to a user’s system for malicious purposes, such as stealing sensitive information. Finally, Worms are self-replicating code designed to spread across networks and cause disruption. They can be used for various malicious activities, such as deleting files, spreading other malware, or even taking control of computers.
Malware is an ever-evolving threat that requires constant vigilance and proactive security measures to keep users and businesses safe. Therefore, educating yourself on the various types of malware, how they work, and what steps you can take to protect your data from malicious attacks is crucial. It is also essential to ensure that all computer systems are updated with the latest security updates. Doing so can help reduce the risk of falling victim to one of these dangerous threats.
Can I prevent malware attacks entirely?
Preventing malware attacks entirely can be a daunting task. However, you can take several measures to reduce the risk of infection and protect your computer from malicious attacks.
Firstly, be cautious while browsing the internet and avoid visiting suspicious websites. Always check for the secure “https” connection and the lock icon on your browser’s address bar before entering any sensitive information. Using a reputable ad-blocker and keeping pop-ups disabled can also help reduce the risk of malware attacks.
Secondly, strong and unique passwords can significantly reduce the chances of a successful cyberattack. It is recommended that you use a combination of upper- and lowercase letters, numbers, and special characters. Avoid using common words or phrases, and never reuse passwords across multiple accounts.
Thirdly, avoid downloading and opening suspicious email attachments or software from untrusted sources. It’s also crucial to keep your operating system and applications up to date with the latest security patches and updates.
Lastly, trustworthy antivirus software can give your computer extra protection against malware attacks. It can scan and eliminate any malicious programs, block suspicious websites and downloads, and shield you against the latest real-time threats.
While completely preventing malware attacks may be a tall order, adopting these preventive measures can substantially lower the risk of infection. Always stay alert and exercise caution when surfing the web, downloading software, or opening email attachments to keep your computer safe and secure.
How do cybersecurity professionals track and analyze malware?
When it comes to stopping bad guys from messing with our computers, experts can use many different methods to track down and investigate malware. They use both manual and automated techniques to disassemble the code, see what it does, and figure out how it spreads. This helps them determine what the malware is all about and what damage it might do.
To stay up-to-date on all the new threats that are popping up all the time, researchers use a variety of tools like threat intelligence feeds, sandboxing, and behavior analysis. These things help them learn about all the different parts of a malware attack and how they’re put together.
And to understand what’s going on out there, cybersecurity professionals keep an eye on the big picture and look for attack patterns. Sharing what they learn with other experts can help keep everyone safe from future attacks.