Over the last few years VPN use has exploded with more and more people looking to secure their online privacy. But, with so many VPN services claiming to be the best, how do you choose the right one for you?
In truth, it largely depends on what you want to use a VPN for. Some are good for unblocking, some are good for streaming and gaming, others offer great privacy features. As experts in the VPN industry, following years of testing and reviewing services, we have put together our ultimate list of the best VPNs on the market in 2025. The VPNs on this list generally offer excellent performance and privacy. However, if you have a specific use case in mind, we’d recommend checking out one of our other VPN guides for additional considerations.
If you’re in a rush and need an answer fast, we can tell you that NordVPN is our current pick for the best VPN of 2025. For more information check out our full list summary below.
A summary of the best VPNs
These are the best VPNs in 2025:
- NordVPN: The best overall VPN. Fast speeds. Great for streaming, has lots of servers, and strong security. Comes with a 30-day money-back guarantee for a risk-free trial.
- Surfshark: The best VPN if you’re on a budget. The cheapest VPN on this list. Servers in 100 countries. Allows unlimited simultaneous connections.
- IPVanish: One of the best VPNs for watching TV safely. Ultra-fast provider that works with a huge range of streaming services and allows unlimited connections. Supports Fire TV, Kodi, Android TV, and more.
- ExpressVPN: A top VPN if you want to unblock content. Unblocks region-locked content, works in China, fast speeds, no logs, and impeccable security.
- CyberGhost: A great beginners VPN. A great option for novice users who want all the benefits of a powerful VPN, including speed, security, and unblocking, for a low cost.
- PrivateVPN: An excellent VPN for privacy and security. A new VPN with great speeds. It excels at accessing streaming content, including Netflix.
- Hotspot Shield: Another good free VPN pick. A secure VPN that’s good for streaming with free and paid plans.
- Private Internet Access: The best VPN for Linux users. Great for users who like to fine-tune their VPN to their needs. No device limit.
- VyprVPN: The best VPN for torrenting on our list. A secure, no-logs VPN with an option for extra stealth.
- Windscribe: A versatile VPN pick to cover all your devices. Paid users can use Windscribe’s novice-friendly apps to stream, torrent, and browse securely on an unlimited number of devices.
WANT TO TRY THE TOP VPN RISK FREE?
NordVPN is offering a fully featured, risk-free 30-day trial if you sign up at this page. You can use the VPN rated #1 with no restrictions for a month—great if you need time to test if it’s the right VPN for you.
There are no hidden terms—just contact support within 30 days if you decide NordVPN isn't right for you, and you'll get a full refund. Start your NordVPN trial here.
How we choose The Best VPN:
When putting together our best VPNs for the 2025 list, we ran 5,000+ tests across 300+ VPNs. We checked privacy and security features, performance for tasks like streaming and gaming, and of course their ability to unblock streaming sites like Netflix, Amazon Prime Video, and BBC iPlayer. We also perform regular VPN speed tests from various locations around the world. We’ve even read the small print of over 140 VPN logging policies, so you don’t have to!
In summary, before any VPN is recommended by us, we check for:
- Security and privacy credentials and features
- Speed and reliability for streaming and gaming
- Ability to unblock region-locked content (Netflix, Amazon, Disney+ etc)
- An easy-to-use interface
- Active and responsive customer support
- Great value for money
- Extensive device compatibility (PC/laptop, mobile, Smart TV, etc)
You can read more here on how we test VPNs and our full methodology later in the article.
A Comparison of the best VPNs
| No value | NordVPN | Surfshark | IPVanish | ExpressVPN | CyberGhost | PrivateVPN | Hotspot Shield | Private Internet Access | VyprVPN | Windscribe |
| Website | NordVPN.com | Surfshark.com | IPVanish.com | ExpressVPN.com | Cyberghost.com | PrivateVPN.com | Hotspotshield.com | PrivateInternetAccess.com | VyprVPN.com | windscribe.com | Best VPN Rank: | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | Avg Speed (Mbps) | 100+ Mbps | 100+ Mbps | 100+ Mbps | 100+ Mbps | 100+ Mbps | 74 Mbps | 100+ Mbps | 100+ Mbps | 100+ Mbps | 100+ Mbps | Devices Supported | Windows, MacOS, iOS, Android, Linux | Windows, MacOS, iOS, Android, Linux, Amazon Fire TV, Apple TV | Windows, MacOS, iOS, Android | Windows, MacOS, iOS, Android, Linux, Smart TVs, Routers | Windows, MacOS, Linux, iOS, Android | Windows, MacOS, iOS, Android, Amazon Fire TV | Windows, MacOS, iOS, Android, Linux, Amazon Fire TV, Chrome, Smart TVs, Routers | Windows, MacOS, iOS, Android, Linux | Windows, MacOS, iOS, Android, Linux, QNAP, Chrome OS, Amazon OS, Routers | Windows, MacOS, iOS, Android, Amazon Fire TV | Total number of servers | 8,900 | 4,500+ | 3,200+ | Undisclosed | 8,000+ | 200+ | 1.800 | 1,000+ | 700+ | 480 | Simultaneous Connections | 10 | Unlimited | Unlimited | 14 | 7 | 10 | Up to 10 | Unlimited | 10 | Unlimited |
|---|---|---|---|---|---|---|---|---|---|---|
| Best deal (per month) | $3.09 Up to 76% off 2 year plans + 3 months free | $1.88 Up to 88% OFF + 3 months free | $12.99 Best MONTHLY Deal $12.99 | $2.79 SAVE 78% + 4 months free on 2 year basic plan | $1.75 SAVE 87% on the 2 year plan + 2 months free! | $2.00 Save 85% on a one year plan + 24-months free | $2.99 SAVE 77% OFF 3-YEAR SUBSCRIPTION | $1.75 SAVE 85% on the 2 yr plan + 2 months free | $3 SAVE 80% on the biannual plan | $5.75 $5.75 per month for the annual plan |
Picking the right VPN for you
As we mentioned above, you should pick a VPN based on your intended use case. To help we have created a series of guides based around popular VPN use cases to help illustrate the specific considerations that you should make.
If you have a specific use case in mind, such as gaming, torrenting, streaming, or unblocking, you should check out one of the guides below before deciding:
However, if you want a VPN for all of the above, going with NordVPN or one of the other premium VPNs in our 2025 list should do the job.
Best VPN Services: In-depth reviews
1. NordVPN
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
- FireTV
Website: www.NordVPN.com
Money-back guarantee: 30 DAYS
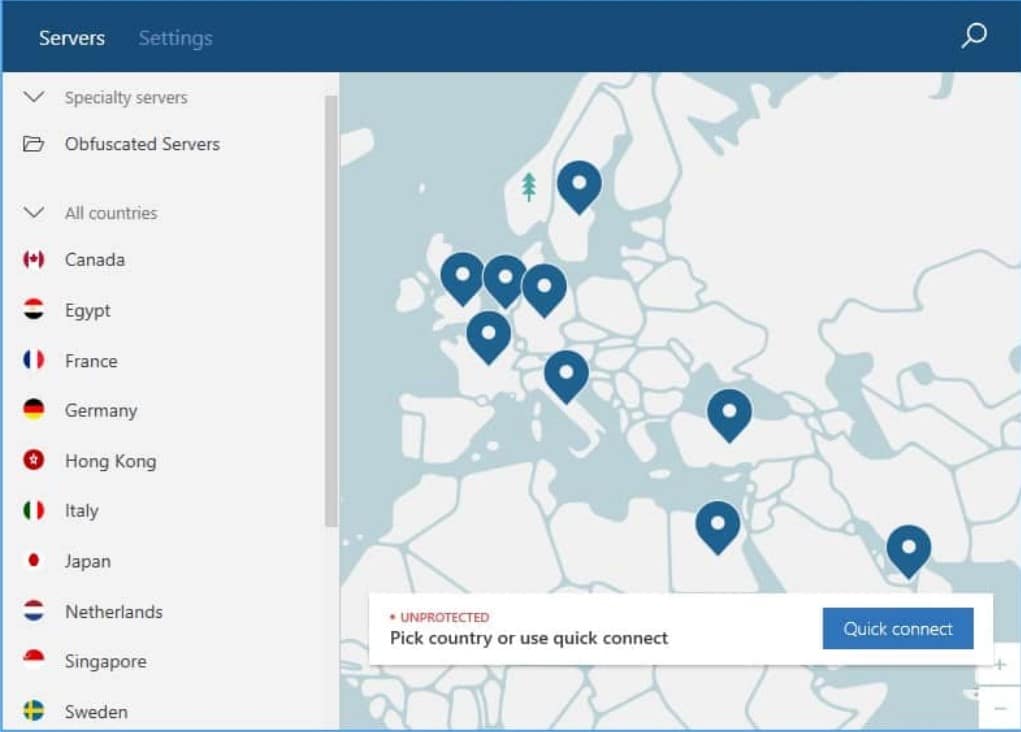
NordVPN is the best VPN, according to our tests. Known for its strong security offering, using powerful encryption, and a true zero-logs policy to keep your activities private. Thanks to its blazing fast servers in 60+ countries, it’s also an excellent everyday choice, suitable for securely chatting, torrenting, or gaming. With up to six simultaneous connections on a single low-price subscription, NordVPN offers one of the best value plans on the market.
Best-in-class streaming features
Most VPNs struggle to support more than a handful of streaming services. That said, NordVPN works with just about every one we’ve tested from BBC iPlayer to Hulu. It was even capable of accessing the British and American Netflix libraries, among many others. Best of all, this service has apps for all major platforms, so you’ll be able to watch them no matter where you go.
Advanced privacy tools
NordVPN uses effectively-uncrackable encryption and protects against IPv6, DNS, and WebRTC leaks. It also boasts a customizable kill switch that lets you decide which apps get cut off in the event of a disconnection. There are two even most impressive features: its Dark Web Monitor (which lets you know if your details have been leaked online) and Threat Protection (which scans for malware, blocks trackers, and prevents you from visiting malicious websites).
Speedy, secure servers
Our tests show NordVPN averages 197 Mbps per second, making it one of the fastest VPNs we’ve reviewed. This is partly due to the service’s custom WireGuard-based protocol, NordLynx, which is faster and lighter than OpenVPN.
It’s also worth noting that NordVPN servers run entirely on volatile memory (RAM) so that no data remnants are left behind upon rebooting and that the server software has not been tampered with. If you’d like, you can even connect to servers designed for tasks like browsing the dark web, encrypting your data twice, or bypassing online censorship.
Pricing
- 2-year plan $95.76 ($3.99 per month)
- 1-year plan $59.88 ($4.99 per month)
- 1-month plan $11.99
Check out our video review of NordVPN below!
Pros:
- Zero logs policy
- Strong security
- Fastest VPN we have tested
- Works with Netflix, Hulu, Prime Video, Disney+, HBO
- Undertaken audits to prove no-logs claims
- 5,000+ servers in 60+ countries
Cons:
- A few unreliable servers
Our score:
BEST VPN SERVICE IN: NordVPN’s simple interface hides its trove of tweakable options and features so you can customize your experience. Great for streaming. Try it risk-free with its 30-day money-back guarantee.
Read our full NordVPN review.
2. Surfshark
Website:
www.Surfshark.com
Money-back guarantee: 30 DAYS

Apps Available:
Surfshark is a newer provider that competes with its more-established rivals at nearly every level, and we’ve given it a top spot because, in terms of bang for your buck, it’s one of the best VPNs out there. For instance, it’s extremely fast and excels at securely accessing stubborn services like Netflix and HBO Max. This VPN is continuously improving its security offering too, and now includes a wide array of privacy tools. And if you look at the longer plans, it’s one of the most cost-effective VPNs on the market today.
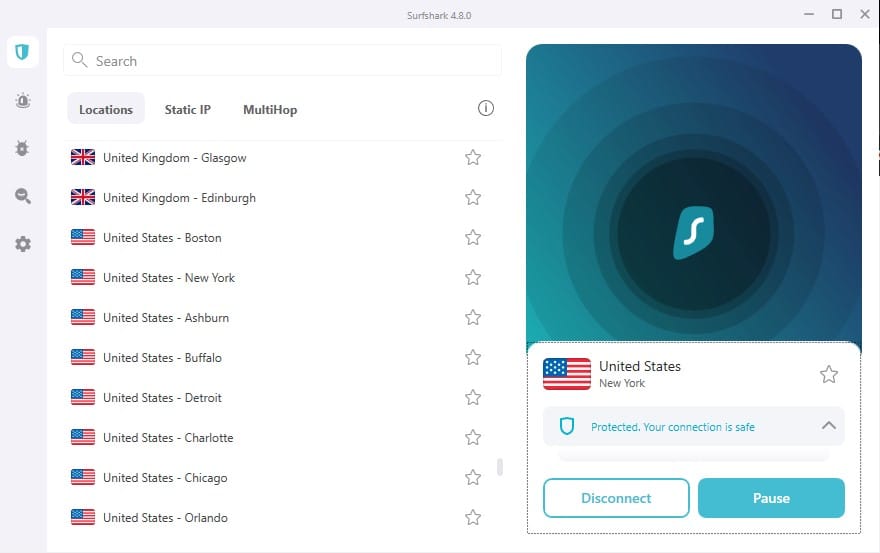
Very user-friendly
This provider makes things as simple as possible. First off, it allows an unlimited number of simultaneous connections. What’s more, Surfshark supports every major operating system and offers free 24/7 support over live chat. We’ve tested it with dozens of streaming services and never had any problems. On that note, any server will work with Netflix, with any from unsupported regions simply redirecting you to the US version.
Anonymity-boosting features
Surfshark is based in the British Virgin Islands, a location with no mandatory data-retention laws. It also follows a strict zero-logs policy which means that it does not record your online activities or any metadata that could personally identify you.
Surfshark doesn’t leak data over IPv6, DNS, or WebRTC, and has a kill switch that halts all traffic if the VPN connection drops for any reason. It now routes your data through multiple servers by default and just recently introduced an IP rotator feature that changes your IP address periodically, making you even harder to track. Users can even pay in cryptocurrency to remove another link between them and the VPN.
A strong all-rounder
With an average speed of over 300 Mbps in our latest tests, Surfshark is suitable for just about any task. As if that wasn’t enough, this VPN has no bandwidth limits and allows you to torrent as much as you like. It even works in countries with extreme online censorship, which is something not many providers can say. Plus, as you might expect, helping users stream Amazon Prime Video is child’s play for a service that’s able to bypass China’s Great Firewall.
Pricing
- 2-year plan $59.76 ($2.49 per month)
- 1-year plan $47.88 ($3.99 per month)
- 1-month plan $12.95
Pros:
- Unlimited devices
- Has servers in around 100 countries
- Works in the UAE and China
- Access Netflix, Hulu, and BBC iPlayer
- Keeps no logs whatsoever
Cons:
- More CAPTCHAs on mobile
- Occasional slow server
Our score:
BEST VPN SERVICE ON A BUDGET: Surfshark is a great budget VPN and an all-around strong performer. Allows unlimited simultaneous connections so you can protect the whole family with one account. 30-day money-back guarantee.
Check out our video review of Surfshark:
Read our full Surfshark review.
3. IPVanish
Website:
www.IPVanish.com
Money-back guarantee: 30 DAYS

Apps Available:
IPVanish makes it as easy as possible to access streaming apps like Netflix, Amazon Prime Video, or Hulu while traveling. The company is based in the US but owns and operates over 2,000 servers in around 60 countries. Its new Threat Protection feature even takes care of ads automatically to save you from having to wait around. Best of all, there’s a no-logs policy which has been verified by third-party auditors.

Best VPN for multiple devices
Most VPNs limit you to five or so connections. IPVanish is different. It’s one of the few VPNs that lets you connect every device you own simultaneously. We’re not just talking about the most common operating systems either; there are apps for Amazon Fire Stick, Android TV, and Apple TV as well as many other platforms. Manual configuration instructions are available in the help section of IPVanish’s website in case you want to secure Linux systems, Smart TVs, or routers.
Fast and functional
This service isn’t just great for streaming. Users can torrent as much as they like, regain access to geo-blocked websites, and switch regions to play games with friends in other countries, all without fear of throttling. It’s quick too, with average download speeds in excess of 300 Mbps. For context, that’s fast enough to watch 4K video on a dozen devices simultaneously!
Strong security, no matter what
IPVanish has been working hard to improve its security offering lately. One of its main goals seems to be offering a similar level of privacy, no matter which device you’re using. For instance, it’s now possible to take advantage of a kill switch and tracker-blocking on systems most other VPNs overlook, such as Amazon Fire TV sticks. There’s also a traffic scrambling feature that obfuscates traffic so your internet provider can’t tell that you’re using a VPN (though this only works with OpenVPN connections at the moment).
Pricing
- 2-year plan (with three months free) $59.13 ($2.19 per month)
- 1-year plan (with three months free) $41.85 ($2.70 per month)
- 1-month plan $10.99
Pros:
- First-class streaming ability
- Real focus on security and privacy
- Great for Kodi, Firestick, Apple TV, and more
- Unlimited simultaneous connections
Cons:
- Based in the USA, a Five Eyes country
Our score:
PERFECT FOR TV: IPVanish has what it takes to help you stream your favorite shows securely. Offers multi-platform support, a strong set of privacy tools, and 24/7 support over live chat. Long-term plans come with a 30-day money-back guarantee.
Read our full IPVanish review.
4. ExpressVPN
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.ExpressVPN.com
Money-back guarantee: 30 DAYS
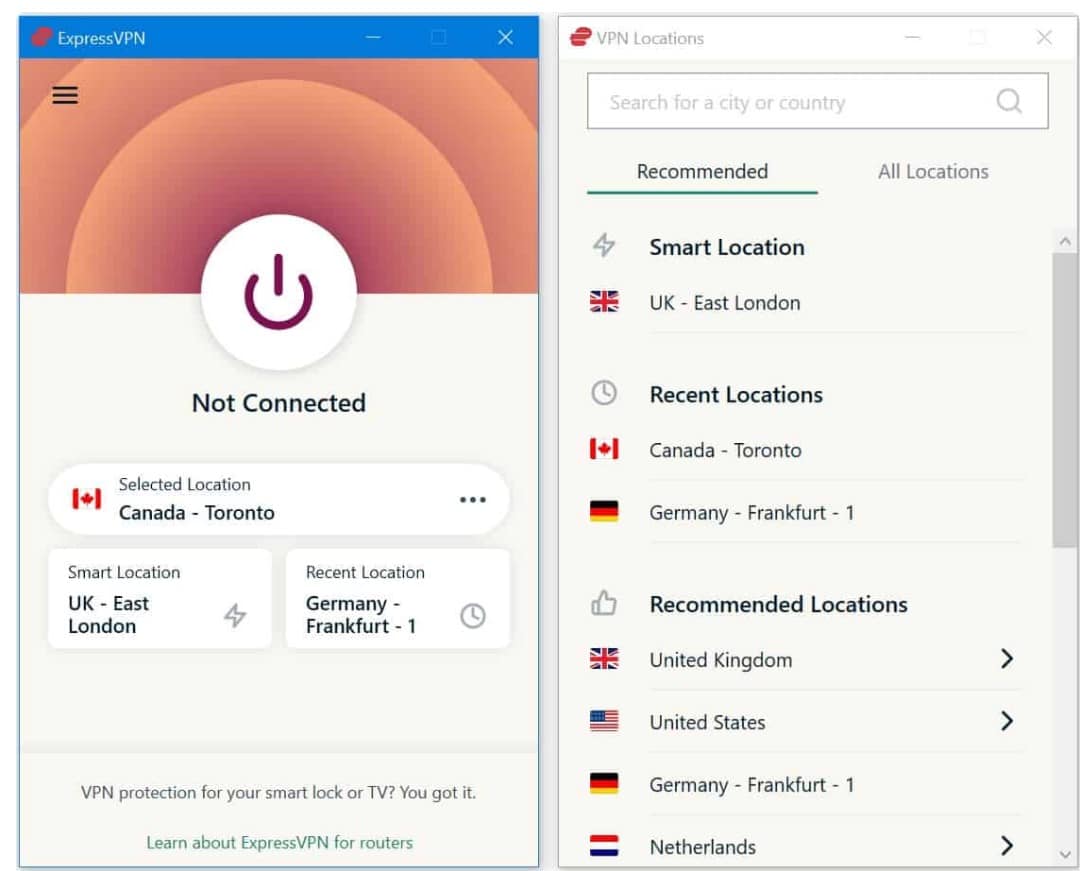
ExpressVPN stands out for having far more server locations than most other VPNs. Currently, it operates servers in 94 countries and, in our tests. Boasts average speeds of over 175 Mbps. This makes it not only one of the best VPN services in 2025 but one of the fastest. In other words, it’s an ideal choice for anyone hoping to stream live TV from back home while on vacation.
The apps for mobile devices, both iOS and Android, feel slick, and it’s a breeze to connect to servers all over the world.
Best VPN for China
China’s government blocks most foreign VPNs outright, but ExpressVPN works flawlessly on the mainland. You don’t even have to tweak any settings or activate a stealth mode, and there’s a separate version of the site that’s still accessible in China (though you’ll have to ask the support staff for the URL before you arrive).
Server choice
If you’re looking for a server in Laos, Bhutan, or Macau, ExpressVPN is one of your only options. Naturally, it has servers in higher-traffic locations too, and all of these run entirely in RAM, with no data left on hard drives after a reboot. This makes the server software more difficult to tamper with and doesn’t leave any remnant user data behind.
So why does this matter? Well, having more servers means there’s likely one nearby, which is important for torrenting since closer servers tend to be faster. Additionally, lots of supported countries mean a wider range of geo-restricted content is within your grasp. For instance, we’ve tested ExpressVPN with platforms like Netflix, ITV Hub, Stan, Crave, and Hulu and had no problems streaming, even while traveling.
Secure and trustworthy
ExpressVPN protects your privacy with 256-bit encryption, leak protection, a kill switch, and a no-logs policy. It also boasts its own Lightway protocol, which can keep your data secure even while switching from wifi to mobile data. These security tools are available in every version of the app, as well as in ExpressVPN’s custom router firmware.
One of the best things about this service is that it’s been independently audited to prove that it’s as secure as it claims. Users who wish to stay anonymous can pay with cryptocurrency and sign up through a dark web .onion site. If you need help with this (or just have a quick question you’d like answered), live chat is available around the clock.
Pricing
- 1-year plan $99.95 ($6.67 per month).
- 6-month plan $59.95 ($9.99 per month)
- 1-month plan $12.95
Pros:
- Strong security and keeps no identifying logs
- Fast speeds
- Unblocks Netflix, Hulu, Prime Video, etc
- 24/7 live chat support
- Works in China
Cons:
- Slightly more expensive than others on this list
- Streaming servers aren’t labeled
Our score:
BEST VPN IF YOU NEED SPEED: ExpressVPN excels on every front, whether you’re an advanced power user or a novice just getting started. 30-day money-back guarantee
You can watch our in-depth video review of ExpressVPN below…
Read our full ExpressVPN review.
5. CyberGhost
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.Cyberghost.com
Money-back guarantee: 45 DAYS
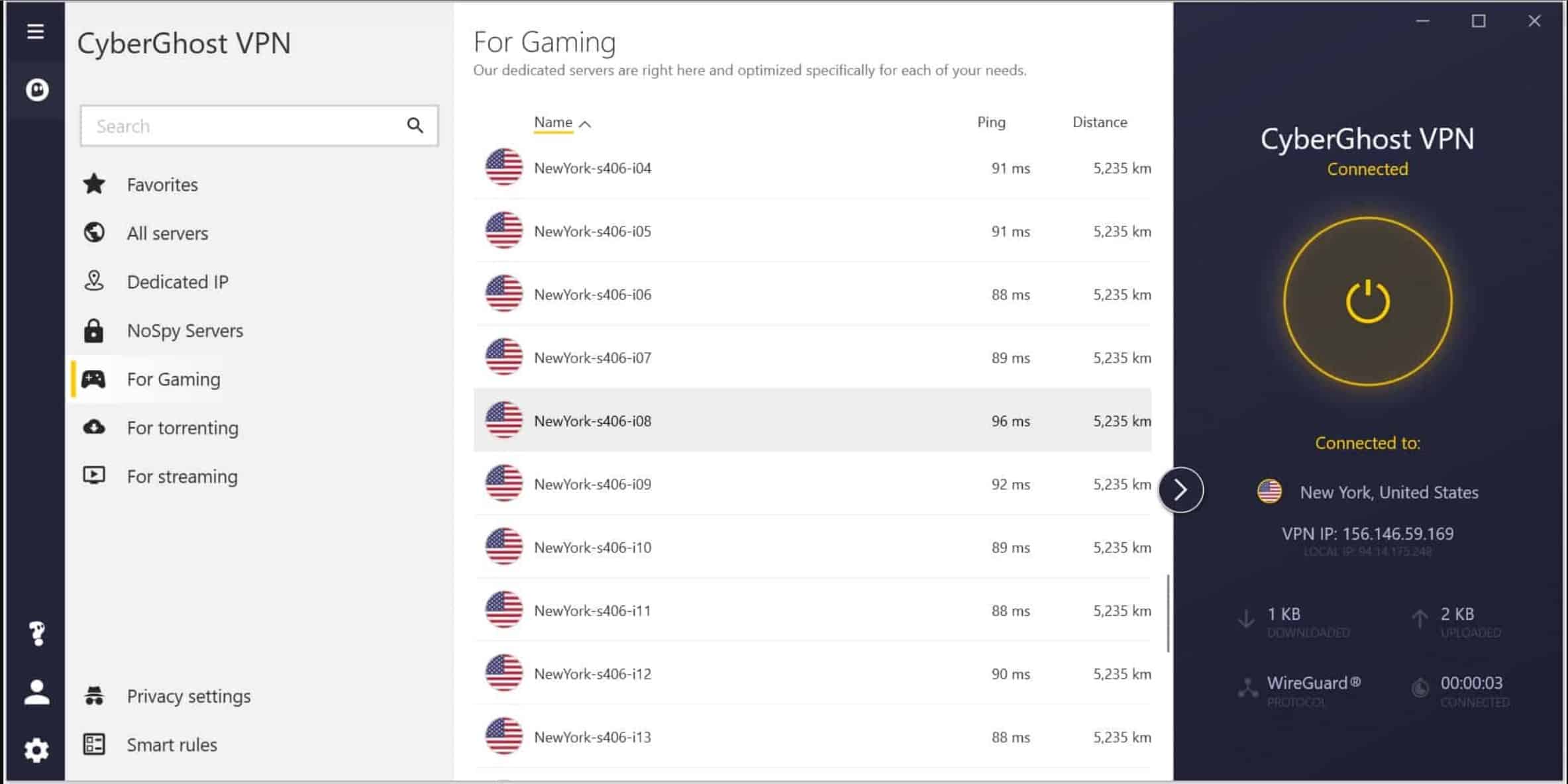
CyberGhost checks off every box when it comes to security and privacy. Not only that, but it’s newcomer-friendly, extremely fast, and incredibly versatile, and that’s why we think it’s probably the best VPN if you’re new to all this and want something that ‘just works’. With more than 9,000 servers in 90+ countries, you should have no trouble getting a speedy, low-latency connection wherever you are in the world. You can even connect up to seven devices at a time.
Task-specific servers
Usually, you’ll have to try several servers to find one that meets your needs. CyberGhost removes all of the guesswork by outright stating which of its servers is best for torrenting, browsing securely, or accessing a particular streaming service (like Netflix, Hulu, or BBC iPlayer, among many others). It also offers a Smart DNS service that can help you access US and UK-only apps on games consoles or other devices without full VPN support.
No-fuss security
CyberGhost boasts a zero-logs policy and promises not to record your online activities, IP address, or other identifying information. Its apps are available for all major operating systems and include a wealth of security tools, including 256-bit encryption, a kill switch, leak protection, and the ability to connect via a random port (which might help you use networks that otherwise block VPN traffic).
That’s not all: CyberGhost also offers perfect forward secrecy, meaning even if your current session’s encryption key is compromised, it can’t be used to decrypt past or future sessions. It recently added WireGuard support too, which is easier for security experts to audit, meaning there’s less chance of an unpatched vulnerability being abused to reveal your activities.
Industry-leading performance
This VPN is currently the fastest on the market, with an average download speed of over 500 Mbps. That’s fast enough for several users to stream Netflix, torrent, and video call at the same time with no noticeable issues. There are no monthly bandwidth or speed limits, so once you’ve signed up, you never have to browse unprotected again.
Pricing
- 3-year plan $89.31 ($2.29 per month) + 3 months free
- 2-year plan $78 ($3.25 per month)
- 1-year plan $51.48 ($4.29 per month)
- Monthly plan $12.99
Pros:
- Fast, streaming-optimized servers
- Connect up to seven devices simultaneously
- Kill switch on all apps and keeps no logs
- Apps are great for beginners
-
45-day money-back guarantee
Cons:
- Doesn’t reliably work in China or UAE
- Lack of advanced configuration options for power users
Our score:
BEST VPN FOR BEGINNERS: In addition to all of CyberGhost’s great features, speed, and security, it also comes with a 45-day money-back guarantee, longer than any other provider on this list.
Watch our full video review of Cyberghost VPN on YouTube:
Read our full CyberGhost review.
6. PrivateVPN
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.PrivateVPN.com
Money-back guarantee: 30 DAYS
PrivateVPN has a relatively small network compared to others on this list, but that hasn’t stopped it from offering a highly-competitive service. In fact, there are several areas in which this VPN is nearly untouchable, from privacy to streaming ability. On top of this, it comes with a generous 10-connection limit – twice what some other providers allow.
Privacy anywhere
PrivateVPN owns and hosts its entire network, as well as acting as its own internet service provider. In other words, no third parties ever have access to user traffic. What’s more, every connection is protected by powerful encryption, a kill switch, and leak prevention.
As you might expect, this VPN follows a zero-logs policy to keep your activities private at all times. Better still, it has a toggleable stealth mode that lets you browse safely, even in places like China, where online surveillance is rife. For even greater anonymity, you can choose to pay in Bitcoin.
Great for TV
We test a lot of VPNs here but haven’t seen many that are as well-suited to streaming as this one. PrivateVPN has no issues accessing services that cause its rivals trouble, so whether you’d like to watch Netflix as you travel or catch up on the latest Prime Video shows, you’re in good hands. Our tests showed that this VPN was fast enough for uninterrupted 4K streaming (though your base connection has a part to play here), and most importantly, these speeds are pretty consistent.
Novice-friendly but customizable
PrivateVPN has two modes (simple and advanced) that let you decide how many options you’d like to see. Further, with apps for MacOS, Windows, Android, and iOS, it can be quickly and easily installed on most devices (though manual setup is needed for Linux systems and routers).
If you’d like to dig a little deeper, users can specify which apps to halt traffic from when the connection drops, change the level of encryption or connect to a server specially optimized for torrenting. Live chat is available almost 24/7 in case you need any help.
Pricing
- 3-year plan $72.00 ($2.00 per month)
- 3-month plan $17.99 ($6.00 per month)
- 1-month plan $8.99
Pros:
- Fast speeds
- Great at accessing Netflix, Hulu, etc from abroad
- Strong security
- Works in China
Cons:
- Small server network
- Live chat not quite 24/7
Our score:
SMALL VPN, BIG PERFORMANCE: PrivateVPN is an up-and-coming provider that performs on a level we normally expect from serious veterans. Comes with a 30-day money-back guarantee.
Read our full PrivateVPN review.
7. Hotspot Shield
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.Hotspotshield.com
Money-back guarantee: 45 DAYS
Editor's Note: Hotspot Shield is owned by Point Wild, Comparitech's parent company.
Hotspot Shield is a solid option for people who want a VPN that just works. It’s quick, easy to use, and versatile, with tasks like streaming and torrenting as simple as they could possibly be. Up to five simultaneous connections are permitted, and there are no bandwidth or speed limits on paid plans.
Servers for any task
Users have plenty of server choices, with around 2,000 to choose from across 80+ countries globally. All of these are suitable for torrenting, and there are even some that are optimized for gaming. Likewise, Hotspot Shield has servers designed to securely access a huge range of British and American streaming services. We’ve tested these with BBC iPlayer, Hulu, and HBO Max, among others, and haven’t had any problems.
Anonymity abroad
It’s hard to overstate how important digital privacy is, and this is even more true if you’re traveling. Luckily, Hotspot Shield provides 256-bit encryption, protection against DNS, IPv6, and WebRTC leaks, and a kill switch, plus a no-logs policy, meaning your activities are hidden from anyone who might be watching.
This service also has its own protocol, Catapult Hydra, which hides the most common indicators that you’re using a VPN. This is helpful if you’re somewhere like China, where VPN traffic is blocked by default. An added bonus is that Hydra has proven significantly faster than OpenVPN, both over short and long distances.
Stress-free setup
Hotspot Shield has its own Windows, Android, iOS, MacOS, and Linux apps. These are streamlined and well-organized, but if you’d rather install the service on your router, support staff can walk you through it (just get in touch using the 24/7 live chat service).
Pricing
- 3-year plan $107.64 ($2.99 per month)
- 1-year plan $95.99 ($6.99 per month)
- 1-month plan $10.99
Pros:
- Good speeds
- Works in China
- Unblocks most streaming services
Cons:
- Only Windows app has a kill switch
- Leaks IPv6 and WebRTC
Our score:
BEST FREE VPN:Hotspot Shield is a solid VPN with both free and paid plans. The latter comes with a 45-day money-back guarantee.
Read our full Hotspot Shield review.
8. Private Internet Access
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
- FireTV
Website: www.PrivateInternetAccess.com
Money-back guarantee: 30 DAYS
Private Internet Access, not to be confused with PrivateVPN, is a veteran player in the VPN space with a sterling reputation when it comes to protecting its users’ privacy. It boasts lightweight, highly customizable apps that let you adjust encryption and network settings. PIA keeps no logs and can handle most day-to-day tasks without any issues.
P2P-friendly
This VPN has several features that make it ideal for torrenting. First off, there are servers in over 80 countries, so no matter where you are, there’s likely one nearby. The desktop apps have port forwarding options built in, and the split tunneling feature lets you encrypt P2P traffic while allowing specific apps to pass through unencrypted.
Flexible security
PIA has a vast array of security and privacy tools, including a kill switch, leak protection, and an ad-blocker. Users can customize their encryption level, the ports used, and DNS settings, and even add a proxy if they’d like. There’s also a snooze function that disconnects the VPN for a few minutes, which is an unusual but interesting addition. PIA doesn’t keep any logs either, so there’s no need to worry about your activities being traced back to you.
Very easy to use
This provider has apps for all major operating systems, so getting started is easy. You’ll have to follow manual setup instructions to get it running on routers, but support is on-hand over live chat should you need it. Unlimited devices can be connected at once.
Pricing
- 2-year plan $56.94 ($2.19 per month) + 2 free months
- 6-month plan $45 ($7.50 per month)
- 1-month plan $11.99
Pros:
- Strong, customizable security
- No logs
- Unlimited simultaneous connections allowed
Cons:
- Doesn’t reliably work in China
- Doesn’t unblock some major streaming services
Our score:
TORRENT SAFELY:Private Internet Access is a lightweight, customizeable VPN with strong security. It comes with a 30-day money-back guarantee.
Read our full Private Internet Access review.
9. VyprVPN
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.VyprVPN.com
Money-back guarantee: 30 DAYS
VyprVPN is a Switzerland-based provider with strong privacy and security standards. The company owns, rather than rents, its servers and maintains a no-logs policy. It’s long been a favorite of ex-pats in China who want to access Western news, social media, and streaming services.
Stream TV anywhere
It’s rare to find a VPN that can access more than a handful of streaming sites. However, our team had no issues using major platforms like Netflix, Amazon Prime Video, BBC iPlayer, or Disney+ while connected. VyprVPN has no rules against torrenting either and refuses to limit your speeds or bandwidth in any way. Customer support is available 24/7 over live chat.
Protection for any device
This VPN permits five simultaneous connections. If that’s not enough, you can manually install it on supported routers. There are apps for all major operating systems, including a command line-based interface for Linux. VyprVPN even natively supports Apple’s new M1 chips.
Proven no-logs policy
VyprVPN is one of the few providers to have undergone an independent audit proving that it keeps no logs. Its other security tools include 256-bit AES encryption, leak protection, a kill switch, and a feature that’ll connect you automatically whenever you use an unsecured network.
This service also offers its own protocol, named Chameleon. This scrambles your data in an attempt to hide the fact that you’re using a VPN (which helps in places like the UAE or China). Alternatively, you can connect via WireGuard, IKEv2, or OpenVPN.
Pricing
- 12-month plan $100.00 ($8.33 per month)
- 1-month plan $15.00
Pros:
- Privately owned servers and data centers
- No logs
- Works with Netflix
Cons:
- Average speeds
- Smaller server network
- No Linux app
Our score:
PRIVATE NETWORK:VyprVPN ensures speed and security through its self-owned servers and data centers. It comes with a 30-day money-back guarantee.
Read our full VyprVPN review.
10. Windscribe
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
- FireTV
Website: www.windscribe.com
Money-back guarantee: 3 DAYS
Windscribe is a Canada-based VPN provider with free and paid plans. The free version gets you 10GB of data per month and access to servers in 11 countries. The paid version offers 60 countries and unlimited data. Whether you’re a free or paid user, Windscribe won’t record any identifying logs and keeps your data safe with strong encryption.
Free browsing forever
Finding a decent free VPN, let alone one with a high monthly data cap is extremely rare. Windscribe raises the bar even higher by being one of the few providers to work reliably in China – something plenty of paid services fail to do. If you’re looking for a little more bandwidth, you can increase the limit to 15GB by tweeting about the company. You will have to do this every month (but this can be automated with the right tools).
Steady speeds
This isn’t the fastest VPN on the market. That said, our latest testing revealed an average download speed of around 55 Mbps, so you should still be able to stream, torrent, and video call without too much trouble.
We were particularly impressed by the server offering. Windscribe is one of the few providers to offer free servers in locations other than the US, and its paid plan is the only one we’ve seen with servers in Ghana. If you’re looking to access services from less in-demand countries, this VPN is well worth a try.
Exemplary security offering
Windscribe’s settings menu is a bit cluttered, but it does offer a huge amount of control over your connection. There’s automatic wifi protection, split tunneling, LAN traffic blocking, and a whitelist feature built-in, plus users can set up a proxy gateway to route traffic from devices without full VPN support.
As you might expect, Windscribe uses 256-bit encryption, DNS and IPv6 leak protection, and a kill switch. It doesn’t log any personally identifiable data and can even block ads automatically. Users can turn on the stealth protocol to browse freely in places with strict online blocking or switch to WireGuard for faster speeds everywhere else.
Pricing
- Basic plan: Free
- 1-year plan $49.00 ($4.08 per month)
- 1-month plan $9.00
Note: Additional cost for static IPs priced between $24.00 to $96.00 per year.
Pros:
- Works with Netflix and some other streaming sites
- Strong encryption
- Works in China
Cons:
- Doesn’t unblock some popular streaming services like BBC iPlayer
- Limited mobile app
- No 24/7 support
Our score:
UNBLOCK FOR FREE:Windscribe can unblock many streaming services on both free and paid plans. The latter comes with a 30-day money-back guarantee.
Read our full Windscribe review.
Why do I need a VPN?
Connecting to a VPN, or virtual private network, achieves s few things:
Encrypts your internet traffic
A VPN will encrypt all of your device’s internet traffic and tunnel it to a VPN server in a location of your choosing. This offers several benefits focusing on unblocking restricted content and improving your online privacy.
- Regaining access to the web in autocratic countries like China
- Accessing geographically restricted apps, websites, and Netflix content from different countries, Hulu, Amazon Prime Video, Disney+ and BBC iPlayer
- Preventing ISPs from snooping on your Internet activity
- Securing open Wi-Fi connections
- Anonymous torrenting and Kodi streaming
Let’s dig into these benefits one by one…
Regain access to the web
Depending on where you live, your access to the web might be restricted by the Government, your ISP or network admins. Nationwide censorship is especially prevalent in autocracies, such as those found in Asia and the Middle East.
VPN use is almost commonplace in countries like China, Iran, and the UAE where it’s one of the only reliable ways to gain access to a free internet. Although, these are far from the only regions that frequently restrict internet access, with more Western countries starting to cherry-pick sites and apps to block.
VPNs can also un-censor the web in government or corporate settings, such as offices and schools, where firewalls and blacklists prevent staff and students from accessing restricted content.
Unblock region-locked content
Worldwide content distribution is regulated through licensing deals, and this applies to movies, TV shows, video games music, and any other types of content. Netflix, for example, might stream a show in the US that is not allowed to be streamed in the UK. In another example, entire streaming services might not be available in certain territories such as Hulu and HBO Now, which as only available in the US.
This results in an extremely confusing and fragmented offering of content country-to-country, leading many to turn to VPNs to gain access to a titles that might be blocked in their region.
When connected to a VPN server you are assigned a new IP address which is then used by websites and apps to determine your current location. So, in essence, you can “spoof” your real location and appear anywhere in the world to gain access to the content you want without leaving your home.
Note that while unblocking a region-locked streaming service is not illegal, you might be breaking the streaming company’s terms of service, although that’s rarely enforced.
Some companies have taken action against VPN users by blocking connections from known VPN servers. Only a handful of VPNs still work with Netflix and Hulu, for example.
As more and more events are live-streamed online, regional blackouts are another problem VPNs can help with. A blackout occurs when a live event is unwatchable online because a local alternative has purchased exclusive broadcasting rights. This is often the case with sports, to the outrage of fans who can’t stream the games they want to see most–those played by their favorite local teams. By connecting to a VPN server outside of the blackout region, however, blackouts can be bypassed.
See also
Stop ISP snooping
Everything you do online is visible to your internet service providers (ISPs). If your ISP wishes, they could monitor every page you visit, everything you purchase, every message you send, every video you watch, and every file that you download. And unfortunately, it is not uncommon for ISPs to collect this information and sell it onto third parties.
As you’d expect, the level of typical ISP monitoring varies from country to country. For example, in the US, ISPs can now sell this data without restrictions to third parties without your consent. The have also been known to collude with law enforcement and intelligence agencies to spy on citizens, even if they are not under suspicion.
A VPN can help nullify all of this online monitoring through the use of encryption. A VPN will encrypt all your traffic before it leaves your device so that no one can see what you are accessing, buying or downloading online.
Secure Wi-Fi connections
Not all Wi-Fi connections are secure. If you connect to Wi-Fi in a public place, such as a café, hotel or airport, you’re opening yourself up to potential online threats. Hackers often take advantage of public Wi-Fi networks to exploit vulnerabilities and capture traffic sent by users over the internet. This allows the hack to monitor and log anything you do online, including passwords.
Not only can hackers view your data, they can modify it. In a man-in-the-middle attack, a hacker can intercept data and change it for nefarious purposes. This could be used to direct you to malware-infested websites or change the contents of messages before they are received, for example.
A VPN can help add a layer of security to public Wi-Fi networks by encrypting all of your traffic before sending it over the public network. This means that even if someone is monitoring you, they wouldn’t be able to break the encryption to see what you’re doing.
Anonymous torrenting and streaming
If you want to download files or stream from P2P torrenting sites, a VPN is a necessity. Torrenting and streaming from such as sites can land you in hot water with your network admin, ISP, law enforcement and your government and can even land you some jail time, depending on where you live.
Torrenting on sites like Acestreams can also pose a security risk for your device by disclosing your UP to anyone else who is downloading/uploading the same content as you. With this information you can become the victim of hacking or copyright trolls looking to extort money from you.
Using a VPN will help mask your real IP so it is never disclosed to anyone on a P2P site. Also, because most reputable VPN providers don’t keep logs of who does what when this isn’t a problem. And since all your traffic is encrypted, ISPs can only see that data is being downloaded, but not what that data contains or where it is coming from.
Why you need a VPN service: A few statistics
If you’re still not convinced about the benefits of a VPN, we’ve included some recent statistics that make for interesting reading.
Whether they’re used for privacy, streaming, or bypassing censorship, VPNs are catching on worldwide. Here are some key statistics showing how the VPN trend is shaping up:
- The shift to remote work, spurred by the pandemic, increased VPN usage by 27.1 percent in 2020
- 31 percent of internet users worldwide have used a VPN as of 2022, according to Surfshark
- The Middle East and Africa have the highest rate of VPN use at 35 percent
- 22 percent of VPN users use their VPN to unblock streaming services
- 51 percent of users connect to VPNs so they can enjoy better privacy
- VPNs are banned or restricted in 10 countries
- The VPN market is expected to be worth $133 billion by 2032
See our full list of VPN statistics
Methodology: How do we test the best VPNs?
Comparitech evaluates VPNs using a series of empirical tests as well as first-hand experience in day-to-day activities like streaming, web browsing, and torrenting. Our research analyzes each VPN’s speed, security, and usability, among other factors.
Comparitech VPN reviewers assess the best VPNs on the following criteria:
Privacy
The best VPNs have watertight no-logs policies that are based in countries without data retention laws or invasive government surveillance and accept anonymous signups and payment methods.
Ideally, VPNs should not store any identifying logs, including logs of your online activity, IP address, or connection timestamps.
Example of a simple VPN logging policy.
We’ve analyzed 140 VPN logging policies as part of our research in order to find the best VPNs you can trust.
Security
VPNs must meet a minimum set of criteria for VPN protocols, encryption, and leak prevention, among other factors.
We evaluate each VPN’s encryption on a number of factors, including encryption strength, authentication protocol, key length, perfect forward secrecy, and leak prevention.
Even with those protections in place, many VPNs still leak data. Every VPN we review is tested for IPv6, DNS, and WebRTC leaks.
Example of a WebRTC IPv6 leak in our tests. Note that NordVPN has since patched this leak.
The VPN must use a secure protocol, such as Wireguard, OpenVPN, or IKEv2. Kill switches that halt internet traffic when the VPN disconnects are also welcome.
Speed
We test every VPN’s speed when connected to a range of servers around the world. The faster, the better!
We publish average global download speed test results for most VPNs we review. Each result in the graph below is the average of nine tests: three times per day staggered at least four hours apart and across three locations. Our test machine is in the United States, from where we test connections to VPN servers in North America (nearest), Europe, and Asia.
Speed is measured on a minimum 1 Gbps connection using the Ookla Speedtest.net desktop app, using the fastest available, secure protocol for each VPN.
In addition to those tests, we also try out bandwidth-intensive day-to-day activities like 4K streaming, video conferencing, and competitive online games.
Access to region-locked streaming services
Most streaming services are region-locked, meaning they can only be accessed from a specific country. We test each VPN’s access to major streaming services like Netflix, Hulu, Prime Video, Disney+, HBO Max, and BBC iPlayer. This ensures our readers can choose a VPN that allows them to access their favorite streaming services while traveling abroad.
Our tests pit each VPN against both the desktop website and mobile app of each streaming service to find out if the VPN can unblock them from overseas. In the case of Netflix, we also test access to several international libraries.
Sometimes we also test VPN access to live events and sports.
Censorship
We prefer VPNs that can bypass web censorship in countries like China. Because of China’s advanced Golden Shield Project, a.k.a. The Great Firewall, much of the web is censored. Authorities also block access to most VPN services, so China is usually a good bellwether for whether a VPN works in other countries that censor the web, such as the UAE and Russia.
If the VPN can bypass censorship and detection in China, it can work anywhere.
Servers
We assess the number of locations available, whether servers are physical or virtual, and the use of virtual locations.
VPNs typically have servers in somewhere between 20 to 100 countries. The total number of servers isn’t strictly important, as performance is more determined by server capacity and the number of active users.
Some VPNs use virtual locations, which entails a VPN server with an IP address from one country that’s physically located in another country. The practice might be good or bad, depending on how it’s used.
Customer support
We contact each VPN’s customer support as a normal user would to find out how quickly support responds and how knowledgeable they are. We test live chat, support tickets, and email support systems for each review.
Apps
Support for more simultaneous connections and more types of devices is always welcome. Most VPNs make apps for Windows, MacOS, iOS, and Android.
Less common are apps for Linux and Wi-Fi routers.
We use and test at least one desktop and one mobile app for each VPN review, taking into account design, features, and responsiveness.
Most VPNs put a limit on how many devices you can connect at one time. The standard is five, but many go higher, and a couple even allow unlimited simultaneous connections.
Check out this overview of our VPN testing process for more details.
How does a VPN work?
VPNs use a variety of authentication measures, encryption, and protocols, but here’s a broad overview of how a VPN works when visiting a website:
- Your device (a smartphone, laptop, or PC) requests a connection to a VPN server. The user might choose this server from a list in their VPN app.
- An encrypted connection is set up between the VPN server and your device. By default, all of the internet traffic going to and from the client is now encrypted and routed through the VPN server.
- When the user visits a website, web app, or service, the client encrypts the request and then sends it to the VPN server.
- The VPN server receives the request, decrypts it, and sends it to the website.
- In response, the website sends the web page back to the VPN server.
- The VPN server encrypts the page and sends it to the client.
- The client decrypts the page and views it in their web browser.
Note that encryption is only in place between the client and the VPN server. The VPN does not encrypt data between the second party (website) and the VPN server.
VPN privacy limitations
A VPN can greatly improve your online privacy and security, but it’s just one of a few tools in your arsenal.
A VPN protects you from:
- ISP snooping on your online activity
- Man-in-the-middle attacks, such as on unsecured Wi-Fi
- Location tracking (based on IP address, not GPS or other location services)
- Being identified and tracked by your IP address
Even the best VPNs do not protect you from:
- Tracking cookies
- Browser fingerprinting
- Location tracking using GPS or other location services
- Revealing your identity when you log into a website, app, or service
With that in mind, you can combine a solid VPN with a few free tools and features to maximize your online privacy. These might include:
- Incognito or in-private browsing modes
- Ad and tracker-blocking browser plugins
- Tor browser
- Signing up with fake personal information
- End-to-end encrypted services, such as chat apps and online backup
- Disabling location services or using a GPS spoofing app
How to hide or change your IP address with a VPN
Every device on the internet has an IP address. IP addresses are all unique, so if someone knows your IP address, they could reasonably identify your device and location. Using a VPN changes your IP address to one that belongs to the VPN company.
Best VPNs of 2025: FAQs
What's the best VPN right now?
The best VPN for one person might not always be the best for another. VPNs have different uses and some are better at one thing than they are at others. Our testing found NordVPN to be the best all-round VPN, looking at all of the criteria. The other VPNs listed in this article are all strong performers and you honestly won’t go far wrong if you choose any of the VPNs mentioned above.
Is using a VPN legal?
Using a VPN is 100 percent legal in almost every country, with a small handful of exceptions such as Iran and possibly the United Arab Emirates. Even though many countries censor the web, accessing censored content through a VPN does not constitute breaking the law.
Note, however, that what you do while connected to a VPN is a completely different matter. If you use a VPN to do something that is illegal in your country, such as pirating copyrighted material or accessing online gambling sites, those are activities are still illegal. A VPN can hide such activity from your internet service provider and authorities, but we advise against doing anything illegal and expecting the VPN to shield you.
In some countries, even though there are no laws against using a VPN, it may be illegal to operate a VPN. This is the case in China, where a recent regulatory notice made it illegal for VPN providers to operate in the country without a license. Other countries, have implemented mandatory data retention laws that require VPN providers to log the activity of their users. This defeats the privacy purpose of a VPN, so be wary of VPNs that operate servers or are incorporated in these countries. Be sure to read privacy policies before signing up.
What is the best free VPN in 2025?
Be wary of most free VPNs. Of course, everyone’s favorite price is “free”, but you usually end up paying with something else.
Running a VPN is expensive so you need to ask yourself: “Why is this company offering its product for free? What are they getting in return?”.
It’s common practice for free VPNs to monitor and record user activity, insert tracking libraries and persistent cookies to gather data for advertisers, and even inject advertisements into your web browser. Free VPNs can also contain malware that will infect your system. A 2017 report (PDF) published by a group of researchers from several institutions including UC Berkeley and CSIRO showed that 38 percent of the Android VPN apps on Google Play contained malware or malvertising, 84 percent leaked users’ web traffic, and 18 percent didn’t encrypt data at all.
Many free VPNs lack sufficient encryption to keep your online activities private from third parties. Worse yet, they might well keep logs of your online activity and identity, which can be sold to third parties and/or used to target you with ads. That pretty much defeats the privacy-preserving purpose of a VPN.
Free VPNs tend to offer fewer servers and are much slower than paid counterparts. Their servers get quickly congested with users. Most set strict data caps or bandwidth limits. They are not well suited to unblocking streaming sites.
In short, we recommend choosing one of the products from our best VPN list and making the most of their free trials and money-back guarantees to ensure you;re happy before commiting long term. If you need a free VPN and don’t mind limited features, we recommend:
- Hotspot Shield
- Windscribe
- ProtonVPN
Can I use a VPN to access streaming sites like Netflix from abroad?
Yes, but not every VPN will work. Check out our list of the best VPNs for Netflix to find the ones that do.
With a VPN you can change your IP address, which is how most websites and apps determine your location. For example, if you live in the UK and would like to access the US Netflix catalog, you can select a US-based server, this will give you a US IP address an allow you to browse freely as though you were there. Similarly, you can do so if you live in a country where Netflix is not yet available, although you will still need to purchase a subscription.
In early 2016, Netflix started blocking many VPNs, but most of the VPNs we recommend still work.
Will a VPN slow down my internet speed?
Yes, but it might not even be enough to notice.
Some VPNs are faster than others, but assuming you can max out your available bandwidth, expect your download speeds to slow down about 10 percent.
There are other factors to consider with slow internet speeds, such as your CPU speed, the distance to the VPN server, and congestion on the network.
If you are having ongoing issues with speed and your underlying connection is fast, get in touch with the provider for support.
Will a VPN work in China?
It will depend on the VPN provider that you choose. China is a tricky country for VPNs so check out our list of the best VPNs for China, for an up-to-date list of those that currently work. Those VPNs will allow you to access western social media, news sites, and streaming services, among others.
Some VPN providers have been blocked or banned, including both their servers, their websites, and the app stores where users can download VPN apps. This makes it difficult to access the means to download the software. If you travelling to China and would like to use a VPN while there, we recommend downloading it before you leave.
How do I set up a VPN?
All of the providers we recommend on our site make their own VPN apps. Getting set up is a simple matter of downloading and installing the app, inputting your username and password, and hitting the Connect button. Configurations for all of the servers come built in, so selecting a location is as easy as browsing through a list.
Some VPNs do not make apps, however, and require manual configuration. Many operating systems have built-in VPN settings, but setting up a VPN this way is much more tedious and doesn’t offer the additional security benefits that come with good VPN apps. We recommend avoiding these, especially if you’re new to VPNs.
What should I look for when choosing a VPN?
There is no one-size-fits-all best VPN for everyone, but neither are all VPNs created equal. Finding the VPN that best suits you depends on a variety of factors and how you intend to use it. Here are some things you should consider when looking for a VPN:
- How much speed and data do I need?
- Is it important that I hide my identity and online activity?
- How much do I want to pay?
- What, if any, streaming services do I need to unblock?
- Do I need to bypass censorship in places like China and UAE?
- What devices do I need to run the VPN on? How many devices in total?
- Are you a novice? Consider getting a VPN with good customer support.