Coming to grips with network performance management in an extensive network requires constant vigilance.
Poor performance can emerge unexpectedly at any time. Network monitoring platforms like Log analysis tools allow you to spot performance issues before they arise.
Here is our list of the best log analysis tools:
- ManageEngine EventLog Analyzer (FREE TRIAL) Comprehensive event monitor for Windows Server and Linux. Start a 30-day free trial.
- FirstWave opEvents (FREE TRIAL) This centralized log and event manager reduces the impact of network faults and failures using proactive event management.
- ManageEngine Log360 (FREE TRIAL) A log management system that supplies log analysis tools and a SIEM with a threat intelligence feed. Runs on Windows Server.
- Paessler PRTG Network Monitor (FREE TRIAL) Network, server, and application monitor that includes Windows Event Log and Syslog receivers.
- Site24x7 Log Management (FREE TRIAL) This tool is provided on a platform of system monitoring and management services and it will collect Syslog messages and Windows Events.
- Datadog Log Analysis and Troubleshooting This cloud-based log server tracks throughput metrics as it processes and consolidates incoming messages. A data viewer in the system dashboard enables log files to be loaded and analyzed. An optional storage space package is also available.
- Splunk Widely used log monitor with real-time alerts that is available for Windows, Mac OS, and Linux.
- SolarWinds Security Event Manager Automated protection measures are built into this log monitor for Windows Server.
- XpoLog Online log monitor that exploits AI to detect errors and intruders.
- Mezmo A cloud-based log collector and consolidator that provides a log analysis and routing utility.
Why do I need a log analyzer?
Every single device or application connected to your network creates log files. Network administrators use these log files to view performance data. These tools are useful because they provide access to the data that the user wouldn’t otherwise have. A log analyzer collects data from a device’s log files and translates it into a data format that’s easy to read.
On a log analysis tool, this ranges from a graph display performance data to smaller dials. Reading performance data in a centralized format like this is much easier than reading through log files directly as text files.
The best log analysis tools
Our methodology for selecting log analysis tools
We reviewed the market for log analysis software and assessed the options based on the following criteria:
- Statistics derived from the arrival rate of log messages and their sources
- A filtering and sorting tool to identify specific sources and events
- A correlation system that enables log messages generated in different formats to be analyzed together
- A system of highlighting to make patterns of activity easier to identify visually
- A charting service that can interpret raw data
- A free trial for an assessment period or a money-back guarantee
- A good list of tools in one package that provides value for money
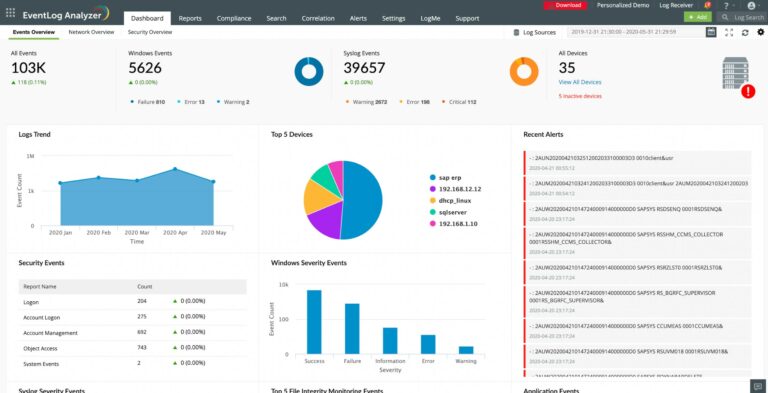
1. ManageEngine EventLog Analyzer (FREE TRIAL)
Tested on: Windows, Windows Server, and Linux, including as SaaS platform
ManageEngine EventLog Analyzer is a log analysis tool with a streamlined user experience. ManageEngine EventLog Analyzer collects logs from database platforms, web servers, routers, switches, hypervisors, vulnerability scanners, Linux systems, Unix systems, firewalls, and Endpoint Security Solutions.
Key Features:
- Collects Logs from Different Sources: The package can process messages from more than 750 sources
- Consolidates and Processes Logs: Converts messages into a standard format and can also select and tag fields
- Shows Logs in a Data Viewer: The viewer includes analysis tools
Why do we recommend it?
ManageEngine EventLog Analyzer provides a log server and consolidator as well as automated security analysis. You can also access log messages to perform your own analysis and your saved queries can be set up to run automatically. This package also provides file integrity monitoring and compliance auditing.
To help you to navigate log data, ManageEngine EventLog Analyzer uses an alerts system. Alerts are customizable and alert you in real-time via email or SMS if the program detects something that needs your attention. Alerts are categorized as high, medium, or low priority to help you to respond appropriately to notifications.
The software is regulatory compliant for a number of policies including HIPAA, PCI DSS, ISO 27001, GLBA, SOX, FISMA, and more. Compliance reports help to ensure that you have all the documentation needed to keep your organization clear of red tape. For example, HIPAA compliance reports the handling of objects, successful user logons/logoffs, and system logs to ensure there is a clear record of user activity.
EventLog Analyzer prepares live data for analysis by converting incoming log messages from all sources into a common format. This enables all of the messages from different sources to be analyzed together in the data viewer of the package. It is possible to set up a series of response rules, which effectively gives you a customized SIEM. The tool provides a parser as well as an analyzer and these two tools together provide a powerful service for log analysis. You can also set up the system to automatically generate alerts and channel them into your Service Desk system as tickets.
Who is it recommended for?
This service is a SIEM with added log management features. It can be set up to automatically raise alerts if it detects security anomalies and you can also create your own trigger conditions. The log management system provides compliance auditing and you can also get reporting for compliance with HIPAA, PCI DSS, ISO 27001, GLBA, SOX, and FISMA.
Pros:
- Downloadable Software: For Windows Server and Linux
- Includes Automated Searches: You can also set up your own searches to run automatically
- Fee Edition: Limited to collecting logs from five sources
Cons:
- No Cloud Version: Only available for on-premises hosting
ManageEngine EventLog Analyzer is available for Windows and Linux in 32-bit and 64-bit. There are two versions of the program that you can download: the Free and Premium editions. There is also a 30-day free trial which gives you a period for evaluation.
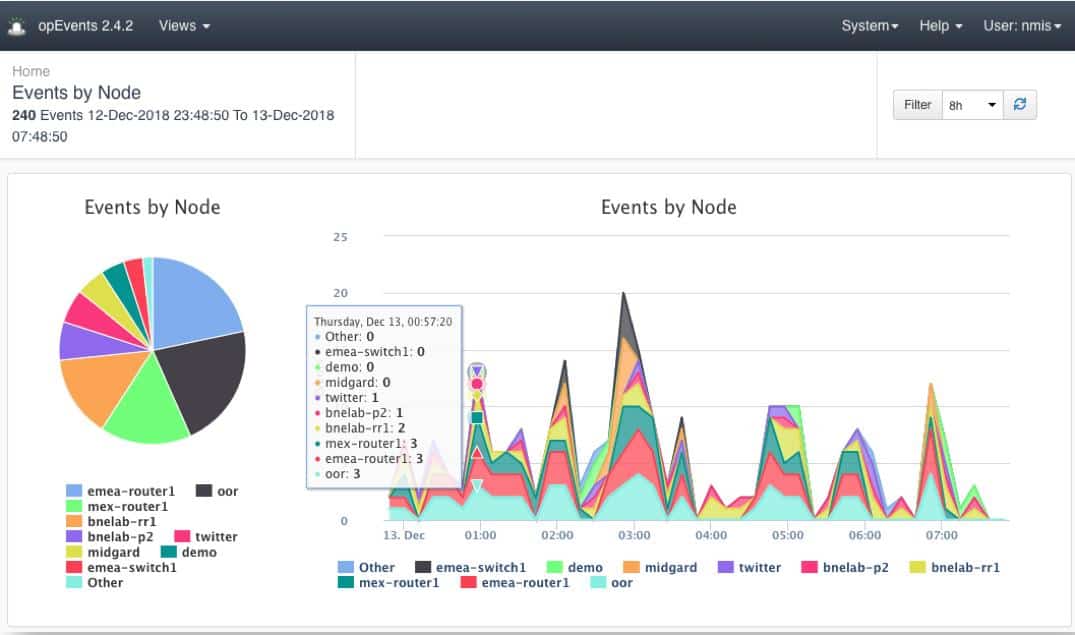
2. FirstWave opEvents (FREE TRIAL)
FirstWave opEvents is an automated log and event manager that is particularly useful for event automation and remediation. opEvents offers complete management of logs from NMIS (FirstWave’s Open-Source Network Management System), applications, active directory, devices, cloud infrastructure or any custom location that is required.
Key Features:
- Collects and Consolidates Logs: Converts logs from different protocols into a common format
- Log Analysis: Search through arriving log messages manually
- Automate Log Analysis: Set up queries to run automatically
Why do we recommend it?
FirstWave opEvents is a network monitoring system that derives its performance analysis by mining log data. As it requires logs for source data, this package also provides a log server and consolidator. The system is great for compliance management because it records problem-resolution measures as well as managing logs.
The opEvents dashboard includes utilities to analyze log records both as they arrive at the log consolidator and as records loaded in from log file storage. The analyzer includes utilities to sort, search, and filter records and it also allows you to set notification rules based on operational hours, organizational hierarchy and prioritize the events you need to see.
opEvents will parse any records and present them in a friendly format, it will also filter and normalize all the events while grouping events to help weather an event storm and focus on the real issue.
You can quickly drill down into the event that displays node data, any remediation that has taken place and presents actions that can be customized to the device/alert. Operators can annotate and close down issues through the dashboard, if linked with a ticket desk it can also close tickets from the same screen. The console also provides attractive graphical data visualizations.
Who is it recommended for?
opEvents is an on-premises system for Linux but it will run over a hypervisor if you only have Windows. The free version will manage 20 devices, which is a reasonable size for small businesses. This log manager is intended for use alongside the NMIS network monitoring system from FirstWave.
Pros:
- Multiplatform Logs: Collects logs from all operating systems, software packages, and cloud platforms
- Route Alerts: Create alerts and conditions that route notifications to different specialists
- Trigger Automation: Set up playbooks to run on the discovery of a specific event revealed through automated log analysis
Cons:
- Only Available for Linux: You could get it to run on a Windows computer over a hypervisor
FirstWave opEvents runs on Linux. However, it is possible to run it over a hypervisor on Windows Server. They offer a 20 device license free for life and higher node counts can be purchased. You can evaluate opEvents on a 30-day free trial.
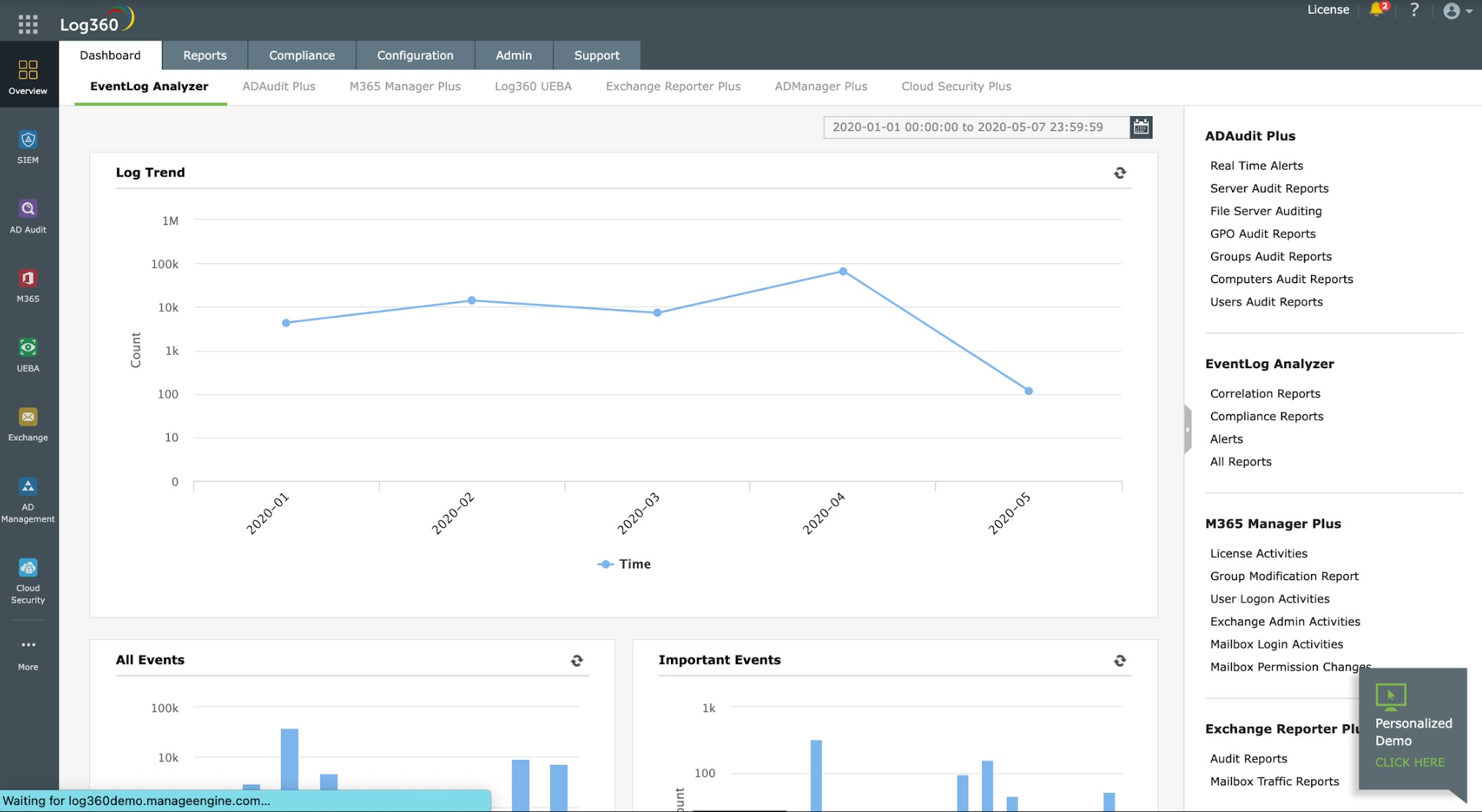
3. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 is a SIEM that includes a log management system to compile a source of data to mine. The service is created by on-premises software with a central log server and distributed agents. The ManageEngine system includes a library of agents for different operating systems. These include Windows, Linux, and cloud platforms, such as AWS and Azure.
Key Features:
- Megapack: Includes many ManageEngine modules, including EventLog Analyzer
- A SIEM Service: Automated threat hunting
- Log Management: Collects, consolidates, and stores log messages
Why do we recommend it?
ManageEngine Log360 is a super bundle that includes ADAudit Plus for Active Directory auditing; EventLog Analyzer, which is a log manager and SIEM (see above), M365 Manager Plus for Microsoft 365 management; Exchange Reporter Plus for reporting on Microsoft Exchange Server; Log360 UEBA, which tracks user activity and events per device; DataSecurity Plus for sensitive data protection; ADManager Plus for Active Directory management; and Cloud Security Plus for public cloud log management.
The agents send log messages to the log server, where they are converted into a unified format. Arriving logs are shown in the data viewer of the console. This includes log analysis tools. Logs are also stored to file and any log file can be opened for analysis in the data viewer. The SIEM uses prewritten search rules that are influenced by a threat intelligence feed. The system also includes compliance reporting for HIPAA, PCI DSS, FISMA, SOX, GDPR, and GLBA.
Who is it recommended for?
This is a large package and you might not need all of the elements. The full package is only available for Windows Server and there is no free plan but EventLog Analyzer by itself has a Free edition and is also offered as a SaaS package. So, check whether some of the elements are more suitable for your requirements before opting for Log360.
Pros:
- Manual Analysis: Arriving log messages are displayed in a data viewer that has analysis tools
- Compliance Reporting: For HIPAA, PCI DSS, FISMA, SOX, GDPR, and GLBA
- User and Entity Behavior Analytics: Spots activity anomalies that could represent an insider threat or an account takeover
Cons:
- Only Available for Windows Server: There is no cloud version
As well as collecting log messages from operating systems, Log360 is able to interface with more than 700 third-party software packages to extract activity information. The central server installs on Windows Server. You can assess ManageEngine Log360 with a 30-day free trial.
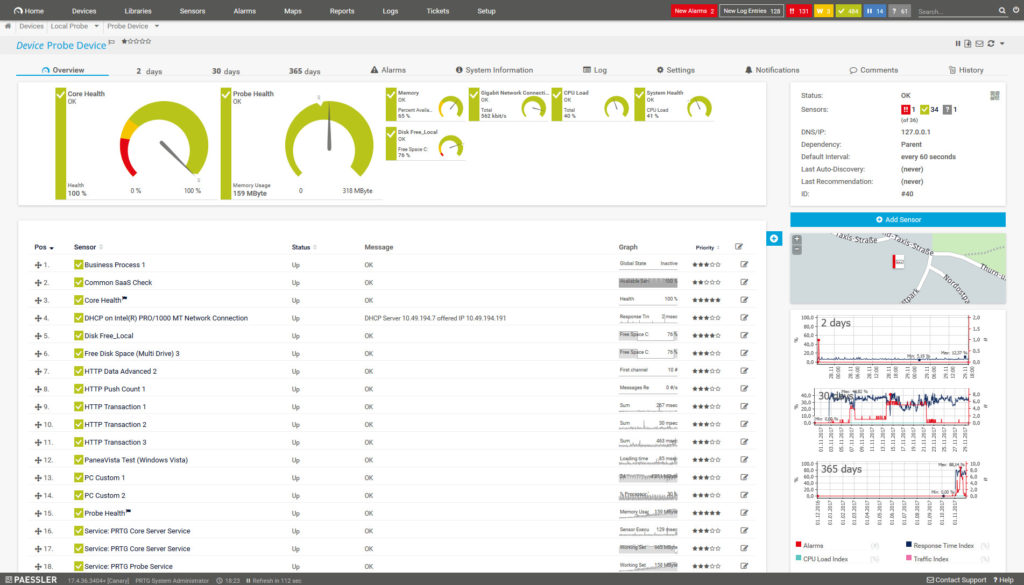
4. Paessler PRTG Network Monitor (FREE TRIAL)
Paessler PRTG Network Monitor is a network traffic monitoring platform that includes a Windows Event Log Sensor and a Syslog Receiver Sensor. The Windows Event Log Sensor monitors Windows system and application log files and displays the rate of log messages. The Syslog Receiver Sensor records the number of syslog files per second sent by devices in the network and filters them. Filters are customizable so you can determine what activity will trigger an alarm.
Key Features:
- A Flexible Monitoring Package: PRTG provides monitoring for networks, servers, and software
- Syslog Receiver: The PRTG package includes a server that receives and analyzes Syslog messages
- Event Log Processing: The bundle includes two modules for Event log processing and analysis
Why do we recommend it?
Paessler PRTG Network Monitoring is a modular package that you can customize by deciding which components to turn on. The Windows Event Log Sensors and the Syslog Receiver Sensor record statistics about the generation of log messages and can compile compliance reports on that data.
The notifications system offered by PRTG Network Monitor is highly customizable. You can determine whether you want to receive notifications via email, SMS, or push notifications. The range of alerts options means that you can receive updates on network performance from PRTG Network Monitor on almost any device.
Who is it recommended for?
Paessler PRTG is a very useful package for monitoring networks, servers, and applications. It doesn’t collect log messages, so it isn’t a good choice for log management. You would have to buy a separate package to be able to collect and store log messages or analyze their contents.
Pros:
- Log Filter: Filter messages by severity
- Log Analysis: Set up searches to trigger alerts
- Generates Throughput Statistics: Set up counters for the throughput of different types of messages and display them in the dashboard
Cons:
- Not an Automated Analyzer: This package doesn’t consolidate log messages and it doesn’t provide automated searches
PRTG Network Monitor is available as a free or paid product. The free version supports up to 100 sensors, after which you will have to transfer to a paid plan. The paid versions start at $1,799 (£1,506) for 500 sensors. There is also a 30-day free trial.
5. Site24x7 Log Management (FREE TRIAL)
Site24x7 Log Management provides an administrative function and also an opportunity to extend your analytical capabilities. The Site24x7 platform is hosted in the cloud and it requires a collector on each site to gather log messages. The system will collect all of the major log formats, including Syslog and Windows Events.
Key Features:
- Cloud-Based System: Part of a package of system monitoring tools
- Collects and Consolidates Logs: Receives messages from on-premises and cloud sources and standardizes them
- File or Forward Logs: Also possible to file AND forward log messages
Why do we recommend it?
Every device, operating system, and piece of software in your IT system generates log messages that record events, milestones, and problems. These messages need to be collected because they were all written for a reason. They tell a story and you just have to assemble the information into meaningful system activity guides with the data analyzer on the Site24x7 Log Management dashboard.
The Log Management tool receives log messages and converts them into a standard format before storing them. You can get a view of all messages as they arrive and assemble searches on them to create your own early warning system. The package allows searches to be saved and launched automatically, creating customized alerts.
The dashboard for the Log Management service shows metrics about the frequency of log message arrival and their sources. This in itself provides useful system performance monitoring information because a sudden spike in log message generation from one source could indicate a problem has developed.
Who is it recommended for?
The log manager provides the bare bones of a do-it-yourself SIEM. However, you can use the tool as a forwarder to send logs into a pre-written SIEM tool if you don’t have the time or expertise to assemble your own. The data in log messages provide a pool of information that can prove useful for ad-hoc investigations.
Pros:
- Data Viewer for Analysis: View arriving log messages and apply sort, filter, and group functions
- Historical Analysis: Read log files into the viewer for analysis
- Automated Searches: Set up your queries to run automatically on arriving messages
Cons:
- No On-Premises Option: Site24x7 was created as the cloud version of ManageEngine
Site24x7 is a cloud platform of many system monitoring and management tools and you can’t pay for each of them individually. Instead, you choose a plan that includes multiple services. So, you would get monitoring tools in with your Log Management subscription. You can get a look at the full Site24x7 platform by accessing a 30-day free trial.
6. Datadog Log Analysis and Troubleshooting
Tested on: Cloud SaaS
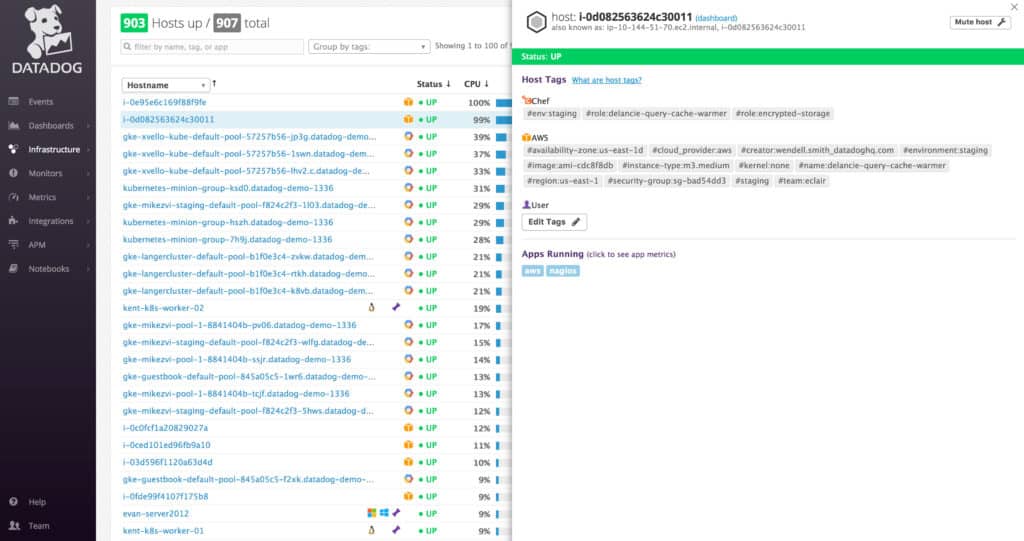
Datadog is another accessible log analysis tool. With Datadog you can record and search through log data from a wide variety of devices and applications. Datadog’s visualization displays log data in the form of graphs so you can see how network performance has changed over time.
Key Features:
- Cloud-Based Service: A SaaS package
- Log Message Collection: Gathers logs from many different sources
- Consolidates Messages: Converts different types of messages to a single format
- Options to Parse Logs: Can split log messages
- Log Forwarding: Send log messages to other packers or file them
Why do we recommend it?
Datadog Log Management is provided in two modules that offer log processing for analysis and filings and another system to manage log files into archive with an option to bring them back for usage. The analytical tools in these packages provide throughput statistics and utilities to analyze message contents.
All displays are top-notch and can be read with a glimpse. However, you can create unique log analytics dashboards by drag-and-drop if you require further customization. Log data can be viewed in real-time and historically. Once Datadog has recorded log data you can use filters to determine what information is listed.

To keep log data from being compromised, Datadog uses centralized data storage so that no data is left on the server. The main benefit of centralized data storage is that your data is protected in the event of an outage.
There are also smart alerts that use machine learning to detect anomalous log patterns and errors. Alerts can be sent through tools like Slack and PagerDuty so that your staff knows the moment there is an issue. You can also set your own alerts with Boolean logic to make sure that you don’t miss anything.
A data viewer in the system dashboard enables log files to be loaded and analyzed. An optional storage space package is also available.
Who is it recommended for?
As it is a cloud-based platform, Datadog is convenient for use by any business anywhere. It can centralize log management for multiple sites and even provide one point of storage for multinationals. The throughput-based pricing of these two packages makes the system affordable for all sizes of businesses.
Pros:
- Log Analysis: Set up automated scans for performance or security monitoring
- Manual Analysis: A data viewer with analysis tools
- Live Tail: Get logs displayed in the data viewer as they arrive
- Log File Management: Get logs stored in directories with meaningful rotation
- Historical Analysis: Read log files into the data viewer
Cons:
- Storage for a Fee: Cloud storage space isn’t included in the Ingest plan but is available for an extra charge
The log collection and analysis functions of Datadog Log Management are provided by a module called Ingest at a price of $0.10 (£0.084P) per GB per month. This service requires you to provide your own storage location. You can choose to store your logs on the Datadog server by using the Retain or Refresh service. This provides options over archiving and is priced at different rates according to the retention period selected. You can opt for 3, 7, 15, or 30 days and there is custom pricing for more than 30 days. The 7-day retention offer costs $1.27 (£1.06) per million leg events per month. You can start with a 14-day free trial.
7. Splunk
Splunk is one of the most widely-used log management platforms on this list. Splunk monitors log and machine data in real-time. Splunk’s versatility allows it to take log data from practically any device or application in your network. When using the program you can use the search bar to look through real-time and historical data. There are also search suggestions to help you find the information you need more easily.
Key Features:
- Data Analyzer: Provides analysis tools to process any type of data
- Log Feed: Provides interfaces to read in log messages and process them
- Pre-Written SIEM: Splunk offers a SIEM package that has pre-written log analysis queries
Why do we recommend it?
Splunk can be used to process any type of data and it can easily be set up to process log messages. You need to create a separate log server because Splunk isn’t specifically made to consolidate logs – just analyze data. However, if you buy the Splunk Enterprise Security package, you will have an off-the-shelf log manager and SIEM system.
To make sure that you don’t miss anything important, Splunk has real-time alerts. Alerts can be sent by email or RSS. Alerts have configurable thresholds and trigger conditions so you can determine what activity will generate a notification. The supporting information included with alerts helps you to reduce your event resolution time.
Splunk is available on Windows, Mac OS, and Linux. There are three versions of Splunk available: Splunk Enterprise, Splunk Cloud, and Splunk Free. Splunk Enterprise supports unlimited users and an unlimited amount of data per day on premises. Splunk Cloud is a cloud service that supports unlimited users and unlimited data as well.
Who is it recommended for?
You need some technical expertise in order to channel log messages into Splunk. This will require a third-party log processor because Splunk is purely an analytical tool. There isn’t a free version of Splunk anymore, so this option won’t appeal to companies that are on a tight budget. This solution is suitable for mid-sized and large organizations.
Pros:
- Cloud or On-Premises: There are two versions of Splunk that provide equal services
- SOAR Option: Opt for a Splunk option that coordinates security activity between third-party security systems that is partially based on log analysis
- Log Management: Splunk will convert log messages from different sources into a standard format and store them
Cons:
- Free Version Deprecated: Splunk used to offer a very good free edition, but that has gone
To view the price of these two versions you will have to contact the sales team directly. Splunk Free is available free of charge and supports one user with up to 500 MB of data per day. You can download the free trial version of Splunk
8. SolarWinds Security Event Manager
Tested on: Windows Server, Cloud (Hypervisor, AWS and MS Azure)
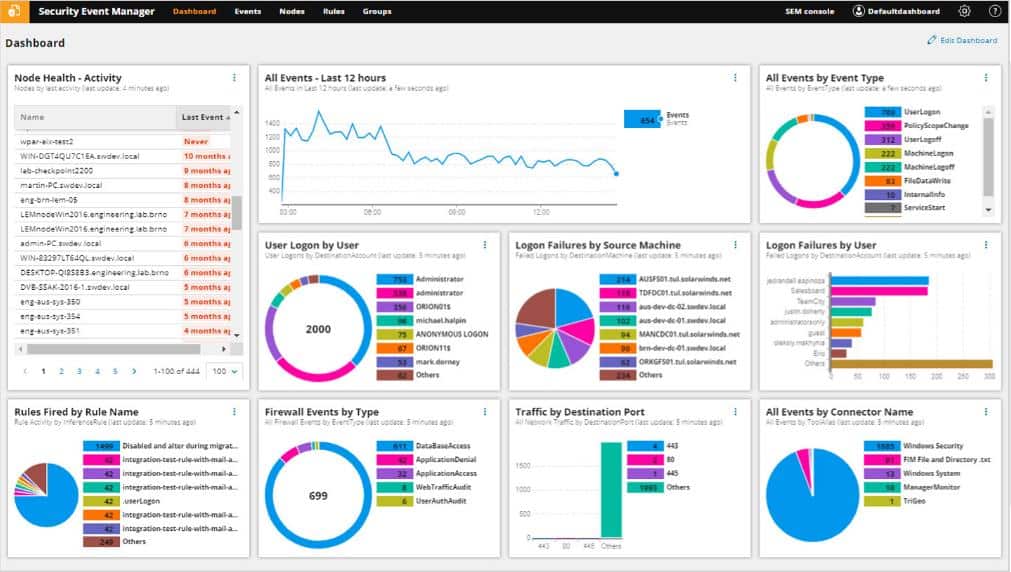
SolarWinds Security Event Manager is a log analysis tool for Windows that provides a centralized log monitoring experience. The platform offers event-time detection to aid the user in detecting threats quickly. Data processed by SolarWinds Security Event Manager is encrypted at rest and in transit so that it can’t be read by unauthorized entities.
Key Features:
- Log collection: Includes a log server that takes all formats of logs
- Log Message Standardization: Converts logs into a unified format
- Log File Management: Stores log messages
- Automated Threat Detection: Provides a SIEM service
Why do we recommend it?
SolarWinds Security Event Manager provides automated log analysis to form a SIEM tool. This security service requires efficient log collection and management and so those functions are also provided in the SolarWinds package. The total bundle also includes opportunities to perform manual analysis on live or historical logs.
The responsiveness offered by SolarWinds Security Event Manager is its biggest asset. Once threats are detected the tool can automatically respond to block IPs, close applications, change access privileges, disable accounts, block USB devices, and more. Being able to respond to threats like this helps to minimize the risk of damage or downtime.
For further data analysis, log findings (normalized logs or specific log files) can be forwarded to other members of your team or turned into reports. The reporting offered by SolarWinds Security Event Manager is compliant with HIPAA, PCI DSS, SOX, DISA, and STIG. The range of report capabilities makes this program ideal for larger organizations that need a program with a high level of compliance requirements.

Who is it recommended for?
This is an on-premises package that is particularly efficient at collecting logs from one site. However, it can be set up to collect logs from other sites and cloud platforms. Analysis functions report on log frequency, which can be categorized by source or severity. This is a high-priced package that is suitable for large organizations.
Pros:
- Live Log Viewing: Displays logs in a data viewer as they arrive
- Analysis Tools: Search, sort, filter, and group functions in the data viewer
- Customized Automated Searches: Set up your own queries to run automatically
Cons:
- Available for Windows Server: Not available for macOS or Linux
Overall, SolarWinds Security Event Manager is an excellent choice based on its threat response capabilities and regulatory compliance. The tool starts at $4,665 (£3,591). There is also a 30-day free trial version you can download here.
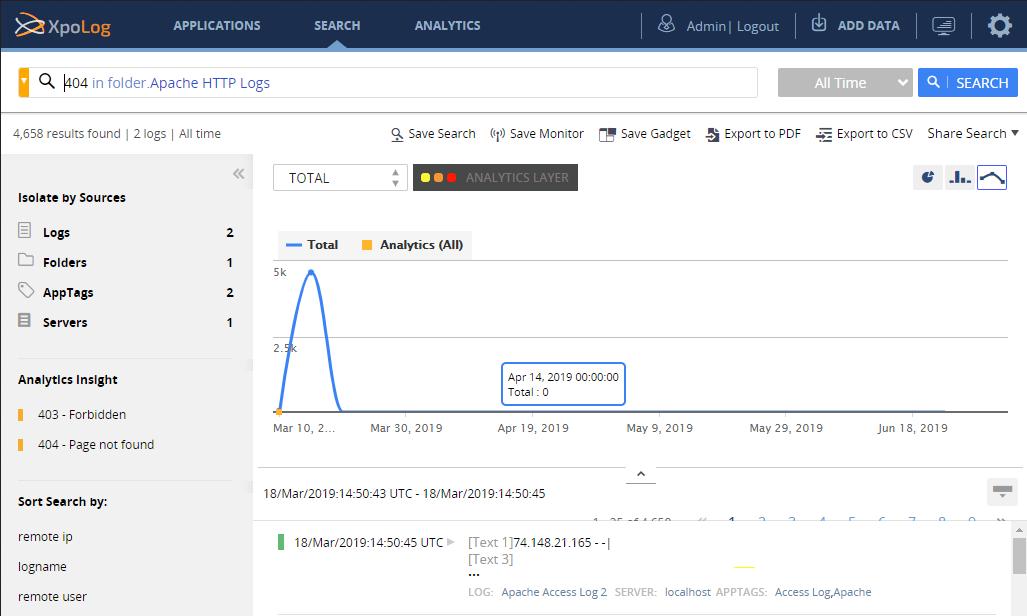
9. XpoLog
XpoLog a fully automated, open log management tool that can also be used end to end, a log monitoring platform that can collect and analyze logs from devices across a network. XpoLog monitors logs in real-time to discover performance issues and create alerts. Users can define rules for alerting and implement their own filtering rules.
Key Features:
- Log Manager: With a Free edition for small businesses
- Automated Analysis: The package includes a library of performance and security searches
- Manual Analysis: Read logs into a viewer and apply analysis tools
Why do we recommend it?
XpoLog isn’t a well-known brand like all of the providers above. However, this log management and analysis package is a very attractive system and offers a very good deal while still providing excellent service. XpoLog provides automated analysis that uses AI to organize performance alerts and also tools for manual data analysis.
One of the features that makes XpoLog stand out is its AI-powered error detection. The AI can discover errors, security risks, and distinguish log patterns that indicate poor performance. Error detection serves to automate log management and ensures you don’t miss any problematic activity. However, if you want to take a closer look, you can use the automated log search feature to view machine intelligence when you run a manual search.
Who is it recommended for?
XpoLog is available for Windows, Linux, and, AWS. The lowest plan, Basic, is free to use and offers 1 GB of data throughput per day. The system is very easy to set up because its dashboard provides a list of systems that you can extract logs from and clicking on one gets the integration installed.
Pros:
- Log Statistics: Calculate and display statistics on log message generation
- Log Cloud Storage: Choose a plan with cloud storage for log files
- Third-Party Collectors: Set up third-party log processors, such as Syslogd and Logstash to get records into the XpoLog system
Cons:
- Alerts: You need to set up alerts for security or performance issues to get full value out of this package
The price of XpoLog depends on the number of users, retention, and volume of data you require. The Basic version is free and supports 1GB a day with unlimited data and five days of data retention. The XpoLog 7 Pro Version is available for $39 (£30.03), $334 (£257) and $534 (£411) per month for 1GB, 5GB, and 8GB per day with unlimited users and unlimited retention. You can download the free trial version of XpoLog.
10. Mezmo
Mezmo is a log management software platform that can monitor log data in real-time. This tool is cloud-based and is configured in less than two minutes to collect logs from AWS, Heroku, Elastic, Docker, and other vendors. The tool instantly aggregates logs from applications and servers across your network with the bandwidth to handle one million log events per second.
Key Features:
- Free Edition: Doesn’t include cloud storage
- Collect and Process Logs: This package receives, consolidates, and files log messages
- Log Alerts: Activate alerts for throughput anomalies, such as surges and absences
Why do we recommend it?
Mezmo is a cloud-based log server that provides a range of functions that can be performed on log messages as they arrive. The tool’s log analyzer performs parsing, and reformatting, through a query and search tool. The system doesn’t perform any content analysis other than log management functions.
One of the interesting things about Mezmo is that the agent and the CLI interface are open-source. In effect this allows you to customize your log management experience. However, if you don’t want to do that, the standard user interface has more than enough features to help you monitor system logs effectively.
Mezmo is a must have for organizations that need a cloud-based and scalable log management solution.
Who is it recommended for?
Mezmo is useful if you have complicated requirements for log routing. You can store the original messages and duplicate them to feed in selected data from different formats of messages into different processors. It will standardize or alter log message formats and send them to different places.
Pros:
- Log Sources: Receives logs from cloud services as well as on-premises systems
- Automated Log Analysis: Access a library of queries or write your own and set them up to run automatically
- Ad Hoc Searches: Access log messages in a data viewer and run searches
Cons:
- Community Edition Difficult to Find: Mezmo requires that all users go through the free trial for the paid version first
The first paid version is called Birch and starts at $1.50 (£1.15) per GB for seven days retention and five users. Maple starts at $2 (1.54) for 14 days retention and 10 users. Finally, the Oak version starts at $3 (£2.31) for 30 days retention and with support for up to 25 users. You can download the free trial.
Choosing a Log Analysis Tool
Though there are many exceptional log analysis tools on this list, ManageEngine EventLog Analyzer, Datadog and Splunk stand out as the most complete log management solutions. Each tool is easy to use with enough depth of features to aid with incident discovery and response in any environment.
Log Analysis FAQs
What is event log correlation?
Event log correlation examines logs from many sources on the IT system and looks for similarities. This leads to the compilation of a report on a possible security breach as indicated by a series of events, which might seem harmless individually.
What is server log analysis?
Server log analysis involves collecting and consolidating log records from all reporting tools resident on a specific server. This process identifies issues, problems, or performance metrics. This is particularly practiced for web servers to gain performance insights.
Which tool can be used to collect logs from a client network?
Look for any log management tool that is designed for managed service providers when you want a system to connect logs from a client network.