What are third-party apps? Any app not made by your device manufacturer or service provider falls into this category. While many are safe, downloading third-party apps from unverified sources can be risky. Knowing the differences can help you avoid potential issues.
Below, we’ll discuss the types of third-party apps (with examples) and what sets them apart from first-party ones. We’ll also discuss the dangers of installing apps from external marketplaces, how to manage app permissions for improved security, and answer some related FAQs.
What are third-party apps?
In contrast to first-party apps, any app that the phone manufacturer or service provider doesn’t specifically develop is considered a third-party app.
Safari is a first-party iOS app because Apple developed it, but Google Chrome is a third-party app. Conversely, Google’s products are first-party apps on Android, while Firefox and Instagram are third-party browsers and social media apps, respectively.
Types of third-party apps
Third-party apps come in four main types based on their source, purpose, and intended users.
Officially approved apps
These apps come from trusted sources that check for security and compatibility, whether the App Store, Google Play Store, or one of the many official stores of phone manufacturers. Apple, Google, or other companies that manage these stores check third-party apps for:
- Malware and other threats
- How user data is collected and used
- Compliance with store rules and standards
- Operating system compatibility
With so many apps out there, some shady ones will naturally slip through the cracks. For the most part, though, third-party apps obtained through official channels are safe.
Unverified apps from external sources
Getting an app listed on one of the stores mentioned above means following strict guidelines, which can take ages. Worse yet, your app may not even be approved, and you might have to start over.
As a result, many developers choose to publish their apps on unofficial marketplaces, like APKPure or F-Droid. These options aren’t necessarily harmful and can provide apps with niche uses you won’t find elsewhere.
That said, smaller stores lack the oversight of major platforms, making it easier for fake apps to slip through. These apps may contain ransomware, adware, or other malicious code. Be careful if you see a popular app sold for cheaper on a third-party store.
Internal-use company apps
Companies sometimes build custom software strictly for in-house use, such as tracking inventory, organizing schedules, and more. Naturally, you won’t find most of these kinds of apps on a public store.
Since setup is limited to company devices, it’s considered safe to use. Its focus on specific tasks also makes it harder for attackers to exploit weaknesses while limiting potential issues like user mistakes, misconfigurations, or conflicts with other tools.
Add-ons or third-party integrations
Some third-party apps don’t need to be installed, as they integrate directly with others. They act as add-ons, allowing new actions within the main app—whether it’s sharing Spotify playlists with your Facebook/Google account, linking Microsoft Teams with Outlook for scheduling, or connecting Slack to Dropbox or Google Drive for file management.
Unsurprisingly, these third-party add-ons need to follow strict guidelines to access user data, ensure compatibility, prevent unauthorized data sharing, comply with legal and regulatory requirements, and so on.
Dangers of third-party apps
We briefly touched on some of the dangers of third-party apps earlier, but there are more to watch out for. Read on for the details.
Data leaks and identity theft
Downloading apps from third-party websites puts you at risk of having your data exposed. Unverified apps might collect and misuse this data without your consent, whether it’s your phone number, email, payment data, or other sensitive device information.
Besides the obvious threat of having your accounts stolen, fraudsters can use your data to commit identity theft, potentially opening up accounts in your name or making unauthorized transactions.
Related: Is identity theft insurance worth it?
This can lead to financial losses and long-term damage to your credit. Since unofficial stores lack the rigorous screening processes of official platforms, you should spruce up your security settings and think twice about where you get your third-party apps.
Malware infections
As mentioned before, any app you get from external sources may contain malicious code designed to steal your data, bombard you with intrusive ads, or even lock your device until you pay a hefty ransom.
Prevention is the name of the game here. Read user reviews for any app you download in case there’s something shady going on behind the scenes. It’s also worth installing reliable antivirus software to stay safe against any hidden dangers.
Related: Malware vs viruses
Exploiting system vulnerabilities
Some apps exploit security flaws in an operating system or other software to gain unauthorized access. This could allow attackers to bypass security features, install malware, or steal sensitive data without your knowledge.
Keep your device and apps updated to cover your bases, and check your app permissions regularly to limit unnecessary access.
Permissions abuse
Many apps request access to things like your contacts, microphone, or location. While some need these permissions to work, others ask for way more than necessary. A malicious app could secretly record audio, track your movements, or collect private data without your knowledge.
Fortunately, it’s easy to manage app permissions on your mobile devices. Here’s how to do so on Android and iOS.
How to change app permissions on Android
- Open your Android Settings.
- Scroll down and press Apps (or Apps & notifications).
- Choose which app you want to check.
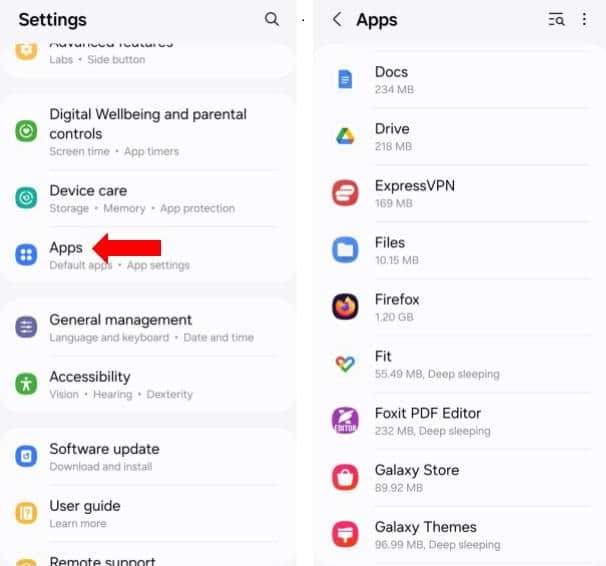
- Tap Permissions to find out what the app can access.
- Select any of the permissions, and you can enable or disable them as needed.

- You can also tap See all apps with this permission to quickly go through all other apps that can access your camera, location, and so on.
How to change app permissions on iPhone and iPad
- Go to Settings.
- Scroll down and tap on Apps.
- Select the third-party app you want to review.
- You’ll find a list of permissions (such as microphone, camera, or location).

- Toggle off anything unnecessary to improve your security.
Are third-party apps illegal?
Third-party apps are not illegal, but some may violate a service’s terms. For example, downloading apps from unofficial sources can pose security risks. Apps that modify or exploit other services, like Snapchat savers, may also result in bans but aren’t necessarily illegal.
That said, some third-party apps can aid illegal activities, such as sharing pirated content (e.g., torrent clients), compromising user privacy, or bypassing paywalls. Using them could lead to account bans or even legal trouble.
What are third-party apps? FAQs
What are some examples of third-party apps?
Some examples of third-party apps include photo editors, VPNs, social media tools, and messaging apps not made by your phone manufacturer or service provider, such as WhatsApp or Spotify. These apps function independently but may integrate with first-party services.
How do I know which apps are third-party?
You can tell an app is third-party if it’s not developed by your device manufacturer, operating system provider, or service provider. For example, on an iPhone, Safari is first-party, while Chrome is third-party. App store listings usually show the developer’s name.
What are third-party apps for Snapchat?
Third-party apps for Snapchat are tools that interact with Snapchat’s features, like apps that save snaps or offer extra filters. Examples include Snapchat++, Phantom, and SnapTools. Using these can violate Snapchat’s terms of service and may result in a ban, so it’s best to stick to official features or apps that use Snap Kit.
What are third-party apps on iPhone?
On an iPhone, third-party apps are any apps not made by Apple. While Safari, Messages, and FaceTime are first-party, apps like Chrome, WhatsApp, and Instagram are third-party. You can install third-party apps from the App Store, but Apple restricts sideloading (installing apps from outside the App Store) for security purposes.
What are third-party apps on Android?
On Android, third-party apps are apps not made by Google or your phone’s manufacturer, such as Firefox or Spotify. Unlike iPhones, Android allows sideloading, meaning you can install third-party apps from outside the Play Store if you enable it.
How do I remove third-party access from my Google account?
You can remove third-party access from your Google account through the settings. Click the button near your profile icon (the dotted square) and go to Account > Security > Your connections to third-party apps & services. You can click on any entry and check what data the provider has about you, or use Delete all connections to remove access.

