Securing sensitive data stored in the cloud has become a growing priority as both individuals and organisations increasingly rely on cloud storage for personal and business use. With this shift, the risk of data breaches and unauthorised access to private information has also increased.
Here is our list of the best secure cloud file storage tools:
- N-able Cove Data Protection EDITOR’S CHOICE A file and system storage solution as part of a backup service that includes secure file storage space and all the tools to manage file transfers. Get started with a 30-day free trial.
- Files.com (FREE TRIAL) A secure file storage platform that includes collaboration and file distribution facilities. Start a 7-day free trial.
- ExaVault (FREE TOOL) An on-premises file storage and sharing tool that gives complete control and visibility into sensitive files and how they are accessed. Download the free tool.
- Acronis Cyber Protect Cloud (FREE TRIAL) This package of cloud-based security services is designed for use by managed service providers and includes cloud storage management options for backups. Start a 30-day free trial.
- Tresorit A cloud storage service that has strong encryption protection for files in transit and at rest and also offers file sharing utilities.
- Google Drive An easy-to-access cloud file storage system that can be used as working storage for current files under development thanks to its associated productivity suite.
- Citrix ShareFile A cloud storage platform with strong security features, watermarking, an eSignature function, and collaboration utilities.
- Accellion Kiteworks A content firewall that includes secure file storage and offers collaboration and file distribution facilities.
Secure cloud file storage tools are designed to address these risks through a combination of encryption, access controls, and broader data protection mechanisms. These features help safeguard files against cyber threats while also supporting compliance with relevant privacy and security regulations.
For organisations handling confidential data, such tools provide a controlled environment for storing, sharing, and managing files without compromising data integrity. They also enable administrators to define who can access specific files, ensuring that only authorised users are able to view or modify sensitive content. This level of control is particularly important when dealing with customer data, financial records, intellectual property, and other sensitive business information.
With a wide range of solutions available, selecting an appropriate secure cloud file storage tool can be challenging. Key considerations typically include encryption standards, access management capabilities, and integration with existing systems, all of which influence how well a solution aligns with organisational requirements.
This article reviews several leading secure cloud file storage options, focusing on the features that differentiate them and the ways they protect sensitive data. It also outlines how the right choice can help maintain file security, accessibility, and regulatory compliance.
Cloud Storage Tools
The types of tools that you need to look for depends on how you intend to use that storage space. If you want a system that aids team collaboration or file sharing, you can easily get a package of systems that include cloud storage – so you don’t need to worry about a separate contract for the storage space.
If your need for storage is primarily to support in-house functions on your premises, then you must watch over the performance of the connections between that storage provider’s servers and your site. You also need to be careful that your storage system and your connections are monitored against malicious actors.
The Best Secure Cloud File Storage Tools
So, there are two types of cloud storage tools to look out for – those that offer customized, function-driven storage space and those that monitor your cloud storage. In this review, we will look at both.
What key criteria did we consider important when looking for cloud file storage tools?
We reviewed the market for cloud file storage tools and analyzed the options based on the following criteria:
- Methods to secure both storage and transfer routes
- Collaboration and file sharing systems
- Storage performance monitoring
- Access rights controls
- File activity logging for data protection standards compliance
- A free trial or money-back guarantee for a risk-free assessment
- Value for money represented by a suitable price with respect to the usefulness of the tools provided
By examining different secure cloud storage options we drew up a shortlist of suitable systems.
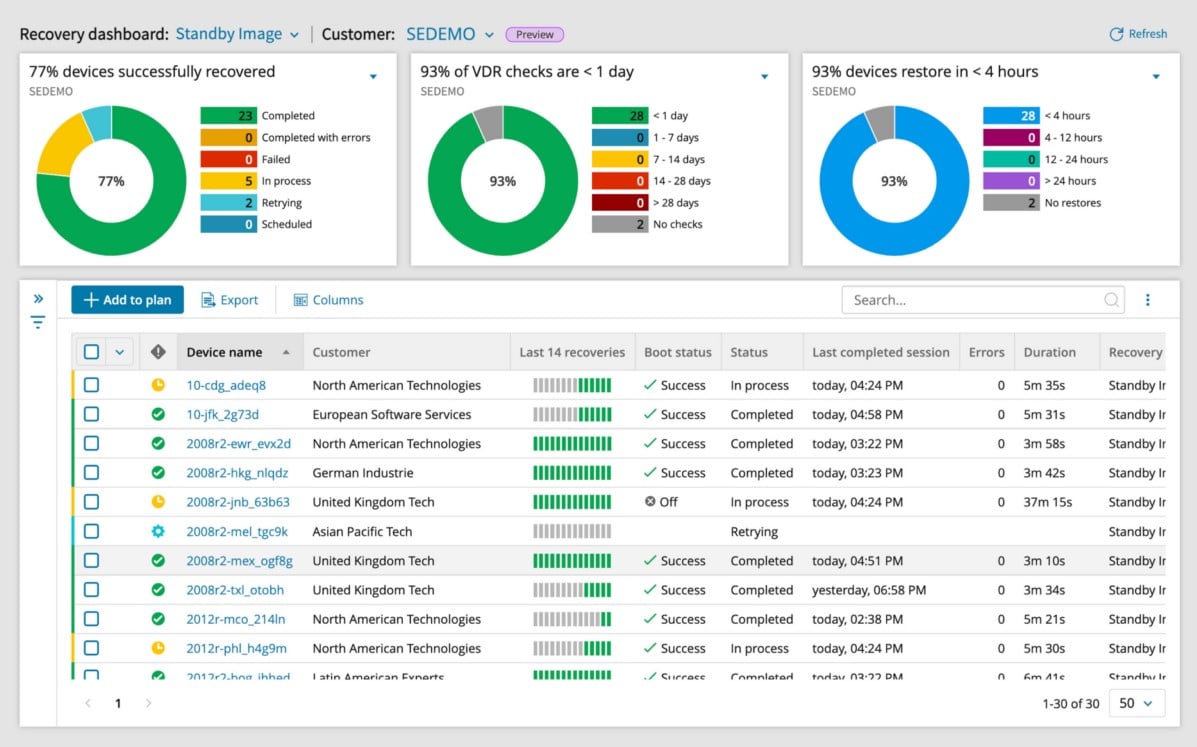
1. N-able Cove Data Protection (FREE TRIAL)
N-able Cove Data Protection is a secure cloud storage tool that is aimed at managed service providers. However, it could also be a useful service for the IT departments of large corporations. This system includes unlimited storage space on a private cloud set up and managed for you by N-Able.
Key Features:
- MSP-Focused: Designed specifically for managed service providers, offering targeted functionalities.
- Unlimited Cloud Storage: Provides endless storage capacity in a private cloud setup managed by N-able.
- Backup & Recovery: Equipped with tools for comprehensive backup and swift recovery of data.
- Encryption-Protected Files: Ensures data is safeguarded with robust encryption protocols.
- Microsoft 365 Integration: Offers seamless connectivity with Microsoft 365 for streamlined operations.
Why do we recommend it?
N-able Cove Data Protection is a backup service that keeps your files in the cloud so that they can be restored on demand. The N-able brand is primarily aimed at managed service providers, so the intention with this product is that MSPs will use the system to back up the data of their clients.
Think of this service as a managed cloud storage system with added tools to automate backup and restore functions plus secure file transfer utilities. The console for the system is also based in the cloud, so you don’t end up backing up your backup system.
The Backup service will back up the operating system as well as all software and services installed on each device. The system will back up virtualizations as well as physical servers. Any updates, changes, or additions you make to the contents of your servers get automatically replicated in the backup on the cloud. It will also back up all of your endpoints.
Microsoft Exchange Server, SharePoint, and MySQL databases can all be backed up, replicated, or migrated using the N-able service. It can also back up OneDrive cloud storage.
The operating systems that N-able Backup can manage are:
- Windows 7, 8, 8.1, and 10
- Windows Server 2008 R2, 2011, 2012, 2012 R2, 2016, and 2019
- macOS 10.10 to 10.16
- CentOS 5, 6, and 7
- Debian 5, 6, 7, and 8
- OpenSUSE 11 and 12
As this system is aimed at MSPs, it is multi-tenanted, so you will be able to back up the systems of your clients without the danger of their data or systems becoming mingled on the cloud server – each sub-account is kept securely separate.
N-able backs up the backups of its clients, so there is no risk of loss. The service is implemented in a string of data centers around the globe, so it is suitable for multinational organizations that need fast recovery services from relatively close storage locations.
Data transfers are accelerated by compression. Security for transfers is provided by uncrackable AES encryption with a 256-bit key. The storage area on the cloud servers is protected by the same encryption system. N-able technicians aren’t able to decrypt data, so confidentiality is assured.
The backup service offers options on how files are to be extracted in wither direction. It is possible to include version control, allowing copies of the same time to be stored over time and enabling rollback to earlier versions. It is possible to restore or replicate a complete device onto bare metal. Physical-to-physical and virtual-to-virtual options are also available.
Who is it recommended for?
This tool is designed for use by managed service providers, enabling them to back up and recover the data of their clients. However, there is nothing to stop IT departments from using this platform for their own data. The tool covers cloud Microsoft 365 accounts as well as on-premises data.
Pros:
- Versatile OS Coverage: Capable of backing up devices across Windows, Linux, and macOS platforms, providing wide-ranging compatibility.
- Enhanced Data Security: Guarantees secure file transmission with high-level encryption, ensuring data integrity.
- Swift Data Recovery: Facilitates rapid data restoration from cloud storage locations close to the user, minimizing downtime.
- Managed SaaS Solution: A fully managed software-as-a-service package, easing the burden of backup system maintenance.
- Multi-tenant System: Supports a multi-tenant architecture, ideal for MSPs looking to offer services to multiple clients without data mingling.
Cons:
- Dependence on Technicians: Relies significantly on N-able technicians for backup management, potentially limiting direct control for some users.
Backups will be run periodically, incrementally, in the background without human intervention. Restore actions are initiated on demand. N-able Cove Data Protection is offered on a 30-day free trial.
EDITOR'S CHOICE
N-able Cove Data Protection is our top pick for a secure cloud storage tool because it includes unlimited cloud storage space, which is encrypted by AES 256-bit encryption. The package includes all of the tools you need to make full use of the storage space, including secure file transfer management. The backup routines in this package are automated and restore functions can be performed on-demand through a browser-based console.
Download: Get a 30-day free trial
Official Site: n-able.com/products/cove-data-protection/trial
OS: Cloud-based
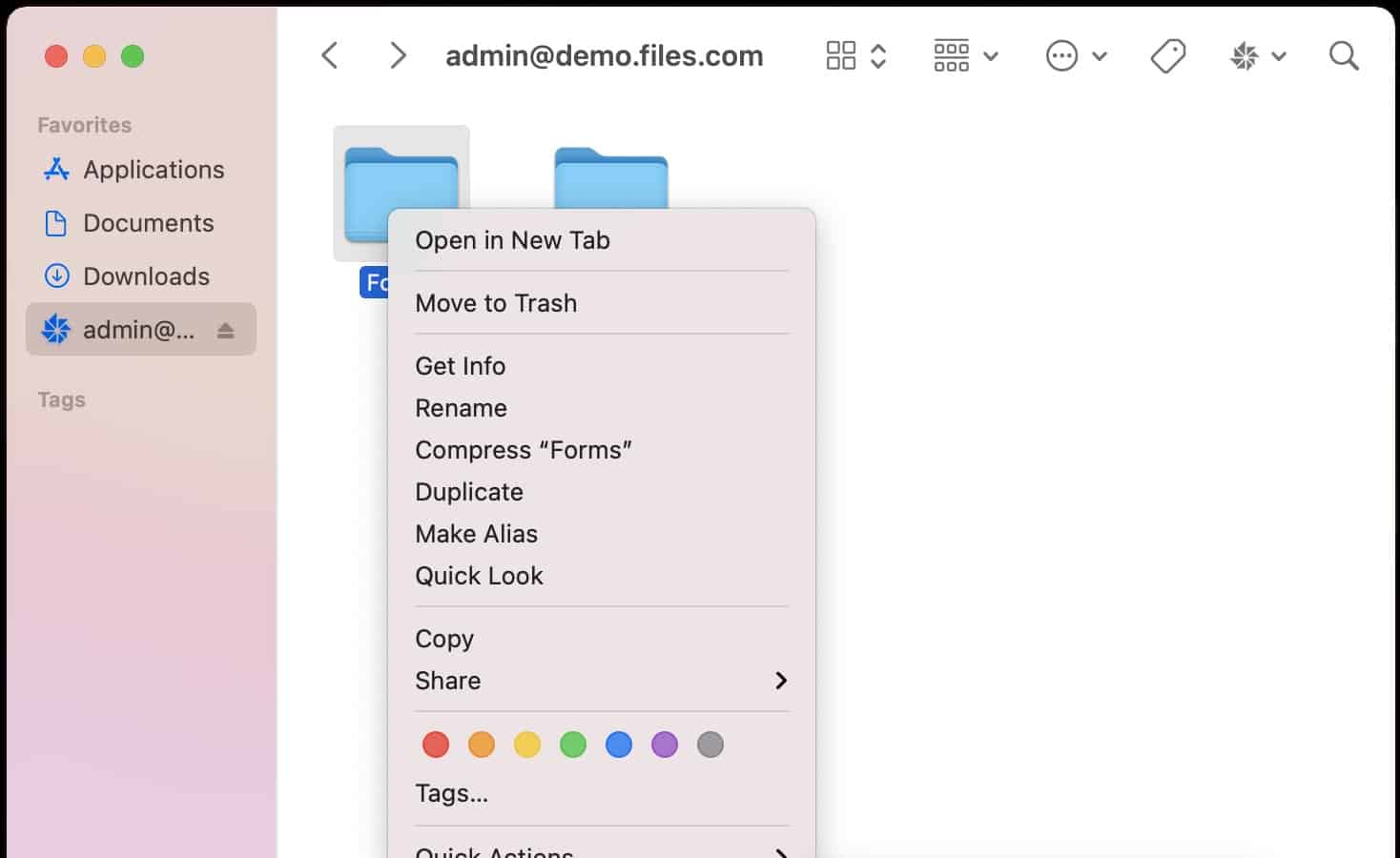
2. Files.com (FREE TRIAL)
Files.com offers a range of file management services that are based on its secure cloud storage platform. The system is available in three editions that include 1, 5, or 10 TB of storage space. That cloud storage is protected by encryption, using a 256-bit key AES cipher. File transfers to the storage platform performed by FTPS and are protected by Transport Layer Security with a 2048-bit key RSA cipher.
Key Features:
- Collaborative File Sharing: Streamlines sharing and collaboration on files with internal and external users.
- Encrypted Storage: Provides secure cloud storage with AES 256-bit encryption for file protection.
- Link-Based Invitations: Enables sharing through link invitations, enhancing security and convenience.
- Microsoft 365 Integration: Facilitates seamless integration with Microsoft 365 for efficient workflow.
Why do we recommend it?
Files.com is a cloud platform that offers companies accounts that let them create subaccounts for each employee. Files held in each user account can be shared by granting access both to other internal users and to outsiders. PErmisison levels possible are to view, comment, or edit.
The Files.com system is an interesting offer for businesses that are looking for a secure file distribution service or a collaboration suite for teams. The tools that are included in the Files.com bundle make this a flexible and multipurpose proposition.
Integrations with Microsoft 365 offer the opportunity to keep all files on the cloud server and let employees create and store their documents, spreadsheets, and presentations on the cloud service rather than on local computers. This configuration also allows for collaboration over document development, including version control, editing facilities, comments, and rollback options.
A secure forwarding utility in Files.com improves file tracking and enables more secure sharing of files. Under this system, the user uploads a file to the Files.com secure storage and then adds access permissions. This is performed by identifying allowed users by email address. The system generates an invitation email to that recipient. There is a link to the document in its cloud storage location within the email. This removes the need to send many copies of a file to different people. Permissions can be revoked at any time by the file owner or the administrator.
Who is it recommended for?
This package is suitable for any business. The platform includes integrations that make setting up Files.com as the default storage location. These connectors are available for systems such as Microsoft 365. The package can also be used to sync or back up local workstation drives.
Pros:
- Centralized File Management: Serves as a primary file location, simplifying file access and management for corporate users.
- Private User Directories: Allocates individual directories for each user, ensuring privacy and organization.
- Editable Access Invitations: Offers controlled access to files, with permissions for viewing or editing by invite.
- Version Rollback: Features rollback functionality to revert to previous file versions, safeguarding against accidental changes.
Cons:
- Lacks Built-In Productivity Tools: While it excels in file sharing and security, it does not come with its own suite of productivity applications.
Files.com is a subscription service with a rate per user per month. The actual amount of storage space allocated to the account is determined by the chosen plan. The administrator account is able to set up and manage user accounts. It is also possible to create private file spaces and shared folders. Files.com is offered on a 7-day free trial.
3. ExaVault (FREE TOOL)
ExaVault is a self-hosted platform that allows businesses to centralize user file activities through their own servers. It supports protocols such as SFTP and FTPS for secure file sharing when needed. It is also possible to use this storage space as the default location for users to save files, though the provisioning must be handled by the user.
Key Features:
- Easy Sharing: With a single click, users can share files and folders.
- Flexible Permissions: Limits access to files through user and group permissions.
- Activity Notifications: Sends notifications in real time to manage file activities.
Why do we recommend it?
One of the biggest aspects of ExaVault is that it allows you to keep your files and folders within your infrastructure. As a result, you have better control over your file storage, sharing, and access controls, all of which can reduce the chances of data theft and attacks.
At the same time, file sharing is simple and easy. With a single click, users can share files with colleagues and external stakeholders. Administrators can control sharing permissions, as they can mandate an email or password to access the shared file.
Another important feature is access controls. Administrators have granular control over who has access to what files and can implement it through fine-grained user and group access permissions. This feature prevents unauthorized access to sensitive data.
Who is it recommended for?
It is recommended for large enterprises that need to securely store all files while encouraging simple sharing. It is also well-suited for organizations that operate in regulated industries, as they have to meet stringent requirements.
Pros:
- Compliance-Ready: Suitable for businesses needing to adhere to PCI DSS, HIPAA, or GDPR standards.
- Accountable User Management: Provides individual user accounts with comprehensive access controls for enhanced accountability.
- Intuitive Interface: Comes with an intuitive user interface for easy sharing.
Cons:
- Advanced Features: Some advanced features are available only in the premium service plan.
You can download the on-premises ExaVault Appliance for free. However, if you need advanced services and more business seats, opt for the Premium Service, which is priced starting at $99/month.
4. Acronis Cyber Protect Cloud (FREE TRIAL)
Acronis Cyber Protect Cloud is a package of security services that is designed for use by managed service providers (MSPs) when managing the systems of their clients. The many modules included in this SaaS platform can be accessed individually per MSP client, so the managed service provider can sell on these services as a menu of options.
Key Features:
- Comprehensive Backup Solutions: Offers an extensive range of backup services tailored to various needs.
- MSP-Friendly Architecture: Designed with a multi-tenant structure, ideal for managed service providers.
- Flexible Storage Options: Provides a variety of backup location choices, catering to different preferences.
Why do we recommend it?
Acronis Cyber Protect Cloud is one of a menu of Cyber Protect variants that cater to different audiences. The Cloud edition is designed for use by large businesses. While it will back up cloud accounts, the main focus of the system is the protection of endpoints on sites.
Acronis gives you a choice of cloud storage options. Whichever options you choose, you can manage how your client’s data is stored through the Backup and Recovery system that is integrated into Acronis Cyber Protect Cloud. You can organize backups to be written to your client’s site, to your own servers on your site, to your own cloud servers, to a cloud platform, such as AWS, Azure, or GCP, or to the Acronis Cloud system.
You can direct backups to multiple platforms on different cycles and also chose whether to implement full disk backup, application-specific backup procedures, or a file-level backup. The system also includes methods for syncing the files of clients’ users and implementing a file sharing system through whichever cloud storage system you like – private, third-party platform, or Acronis Cloud.
The Acronis Cyber Protect Cloud system isn’t just a backup and recovery service. The package also includes endpoint management tools, such as a software inventory service with license and patch management features.
There are extensive endpoint and data protection services in the Cyber Protect Cloud package. These include AI-based threat detection, data loss prevention, and data access tracking, plus antimalware systems.
The antimalware systems in Acronis Cyber Protect Cloud offer protection on endpoints and for backups at the point of transfer. Data recovery processes also scan for infected files before restoring systems. Malware protection extends to email systems and there is also a URL scanning system that relies on blacklisting and HTML scanning.
Who is it recommended for?
This package is ideal for companies that manage a lot of endpoints. It isn’t just a backup service because it also includes an antivirus scanner. This combination of protection is especially important for combatting ransomware attacks. Acronis offers cloud server space for backups and you can also choose your own location.
Pros:
- Versatile Storage Choices: Allows backups to be stored on client sites, MSP servers, various cloud platforms, or Acronis Cloud, offering unparalleled flexibility.
- Integrated Management Software: Comes equipped with software that simplifies the backup and recovery process, ensuring data integrity and availability.
- Endpoint & Email Security: Features robust protection mechanisms for endpoints and email systems, safeguarding against malware and other threats.
Cons:
- Beyond Simple Storage: While offering excellent protection and backup options, it’s more complex than a basic cloud storage solution, encompassing broader cybersecurity measures.
As a SaaS platform, there is no software to be installed on your site other than an agent program per client system. The Acronis system integrates into third-party RMM and PSA packages. You can assess Acronis Cyber Protect Cloud with a 30-day free trial.
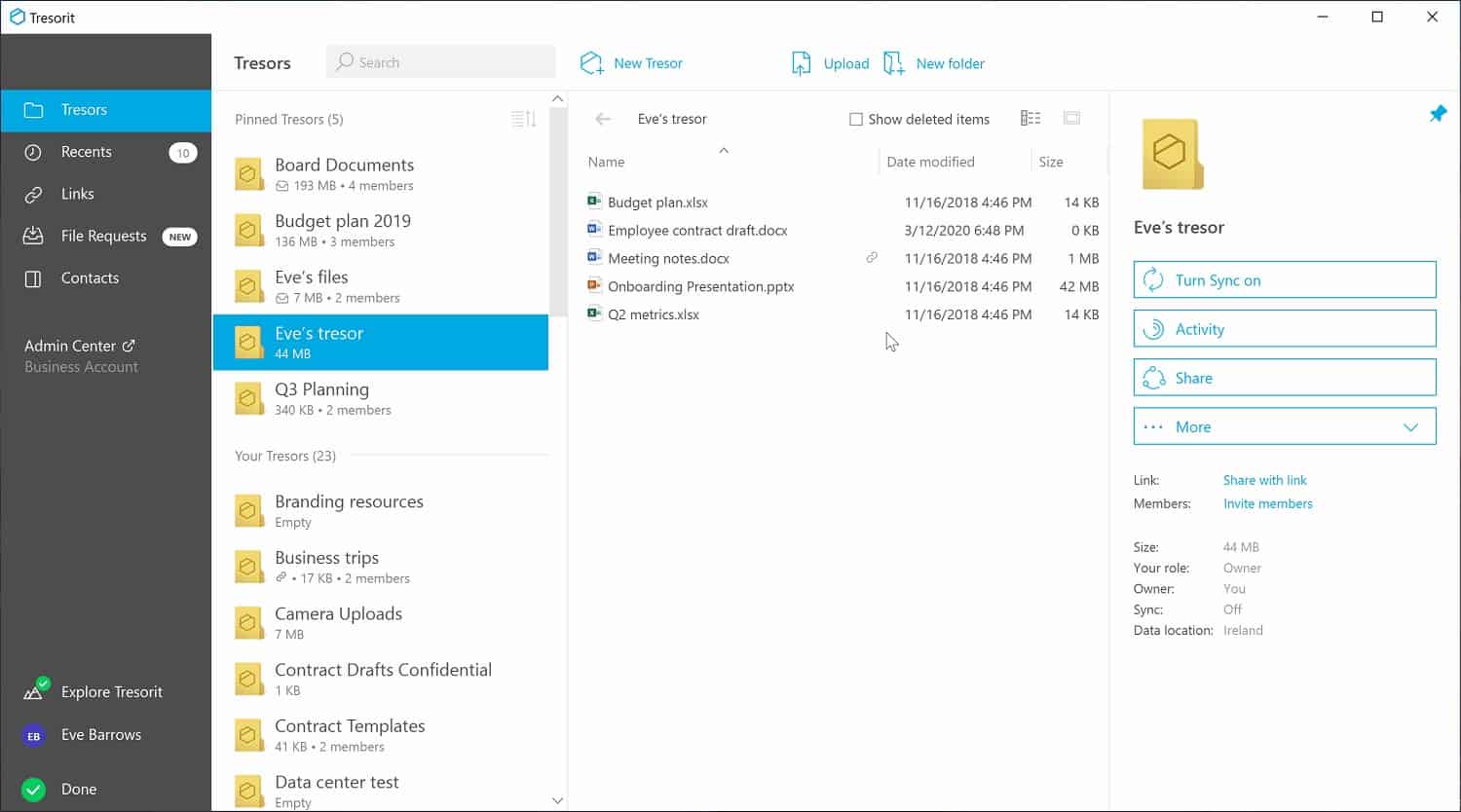
5. Tresorit
Tresorit offers a file storage system that begins its security on the devices of users. Each user in the business can have an individual account and a secure file storage space needs to be marked out on that user’s device. This is called a “tresor” and it is protected with encryption. The tresor is synched with Tresorit file space. So, the user can decide which files will get uploaded just by moving those files into the local tresor. Files are encrypted with 256-bit key AES encryption on the local disk. Transfers are protected by 4096-bit RSA encryption.
Key Features:
- Secure Cloud Storage: Delivers encrypted cloud storage for safe file keeping.
- Personal User Spaces: Offers individual accounts with encrypted local storage areas, or “tresors”.
- Advanced Encryption: Utilizes AES 256-bit encryption for on-device storage and 4096-bit RSA encryption for file transfers.
Why do we recommend it?
Tresorit is another corporate cloud drive service and it is similar to Files.com and ExaVault. The system can be used to mediate file transfers or to completely eliminate the need for them. The core function of the system for file sharing is to authorize colleagues by username and outsiders by email address.
When a file is on the Tresorit server, the owner can grant access to others by entering the recipient’s email address in the file permissions feature of Tresorit. This removes the need to email out copies of files. The encryption key for file protection is regenerated every time the list of allowed accessors is changed. So, it is possible to revoke the file access to individuals. Both the file owner and the system administrator get notified when any changes are made to the file. The notification gets written to an administration log file.
Tresorit can also be used to reduce the security risk of email attachments. The Tresorit system scans all emails, removes attachments, uploads them, and places a link to that file in the email. The recipient is then able to view the file on the Tresorit server. Access to files in Tresorit servers is performed through any standard browser with the HTTPS protocol, which is protected by Transport Layer Security (TLS).
Who is it recommended for?
Tresorit is reasonably priced and it will appeal to businesses of all sizes. Rapidly growing businesses will be particularly interested in the system because of its per user pricing. All of the plans are GDPR compliant and the top plan will provide a BAA for HIPAA and PCI DSS compliance.
Pros:
- High-Level Encryption: Employs AES-256 for local encryption and RSA-4096 for transfer security, providing top-tier data protection.
- Flexible Access Control: Allows precise control over who can access files, enhancing security and collaboration.
- Sync & Backup: Supports syncing and backup capabilities, ensuring data is both secure and readily available.
Cons:
- Additional Costs for Certain Services: Some features may incur extra charges, potentially increasing the overall cost for users.
There are three editions of the Tresorit subscription service. The Business Standard plan includes 1TB of space and Business Plus includes 2 TB. The Enterprise plan is a tailored service. The Tresorit system is available on a 14-day free trial.
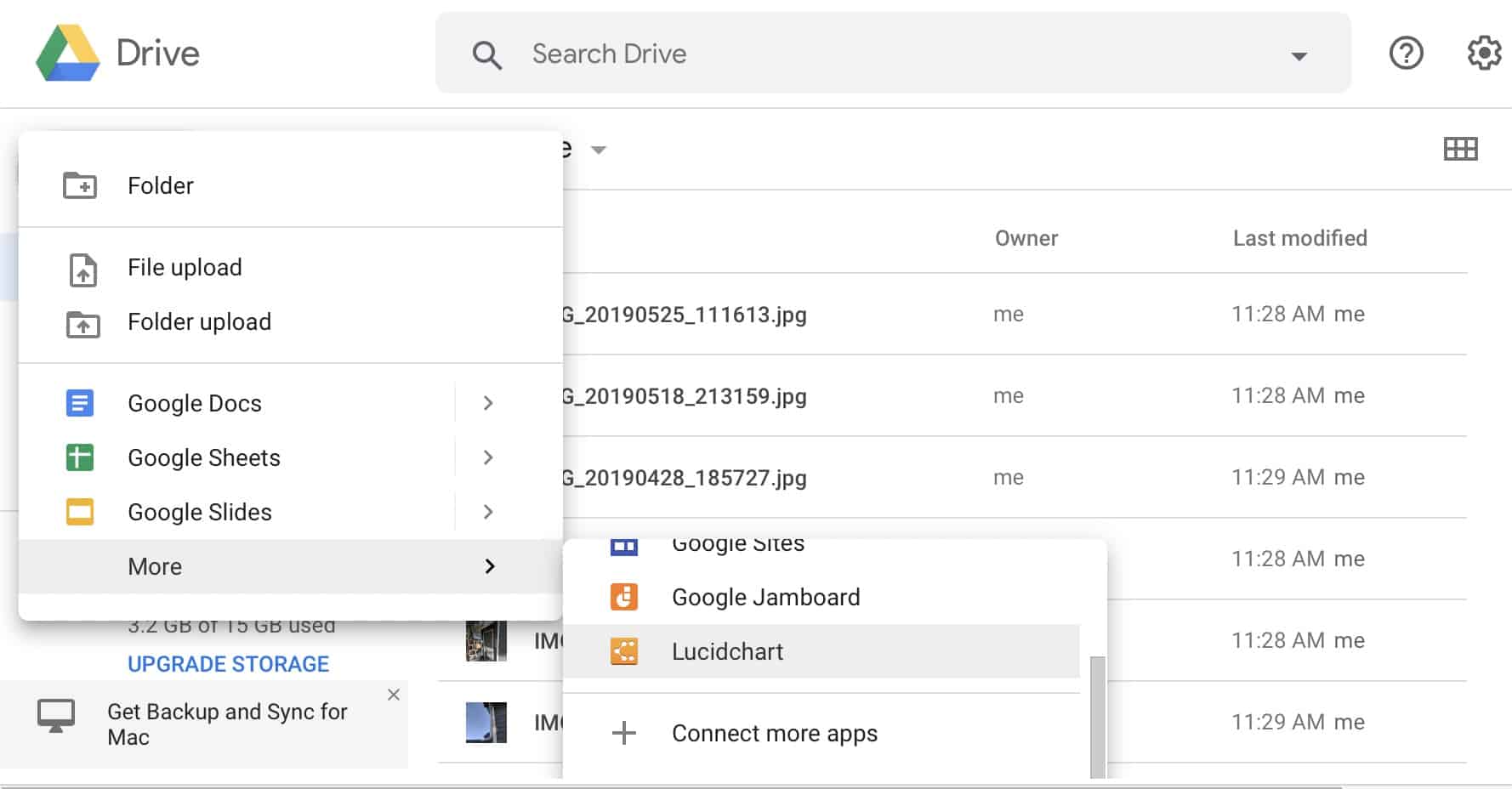
6. Google Drive
Google Drive is very easy to access and starting up a subscription is a straightforward process. Anyone can get a Google Drive account for free – accounts are identified by a Gmail address. Each free account gets 15 GB of storage space. These free accounts are available to business users as well as private individuals. However, there is no group administration control with that configuration. You need to get a Teams or Enterprise account for that.
Key Features:
- Integrated Cloud Storage: Offers cloud-based file storage accessible through a Gmail account.
- Organized Directories: Features a structured directory system for efficient file management.
- Comprehensive Productivity Suite: Includes a built-in suite of productivity tools for document creation and collaboration.
Why do we recommend it?
Google Drive is a widely-used cloud storage service that is free for individual use. The Business plans are not freed and they provide administration accounts to control user accounts. Attractions include commenting and version rollbacks. The Google Drive service is bundled in with the Google Workspace productivity suite.
Google Drive is able to identify sensitive data, such as Personally Identifiable Information (PII). The system scans files for this level of data and blocks access to those files by anyone outside the organization. Files spaces are protected by 256-bit key AES encryption.
Google Drive is integrated into the Google Workspace package. Whether you sign up for Google Workspace or Google Drive you get the same package. This is because Google workspace is a collection of productivity tools plus the Google Drive cloud storage space. Google Drive users get access to the productivity suite for free. Google Workspace is what used to be called Google G-Suite.
The file editors in the Workspace package enable documents, spreadsheets, and presentations to be created and altered. File owners invite others to share access to a file. Any changes to a document create a backup of the original version and all previous versions are available for rollback. The user who made changes is identified. Users can make comments on files and create action points for others.
Another option that file owners have is to grant read-only access. This is a great way to distribute documents without having to mail out copies. It also ensures that the original version is protected and recipients can’t make their own alterations.
Who is it recommended for?
This system is particularly useful for businesses that operate virtual offices and don’t run their own services on their own servers. The combination of the cloud storage space and productivity tools provides all the systems that office workers need and they can be accessed from any device anywhere.
Pros:
- Collaboration-Ready: Facilitates seamless collaboration with features for commenting, editing, and version control, making teamwork effortless.
- Access Control: Provides robust permission settings for shared files, ensuring file security and controlled access.
- User-Friendly Uploads: Enables easy uploading of files and directories through a straightforward menu, enhancing usability.
Cons:
- Sync and Backup Complexity: The process for syncing and backing up data can be intricate, potentially complicating user experience.
Google Workspace is such a useful suite of tools that many organizations provide this cloud productivity suite to their employees instead of on-device software. This strategy makes the cloud server the default storage location for all business files.
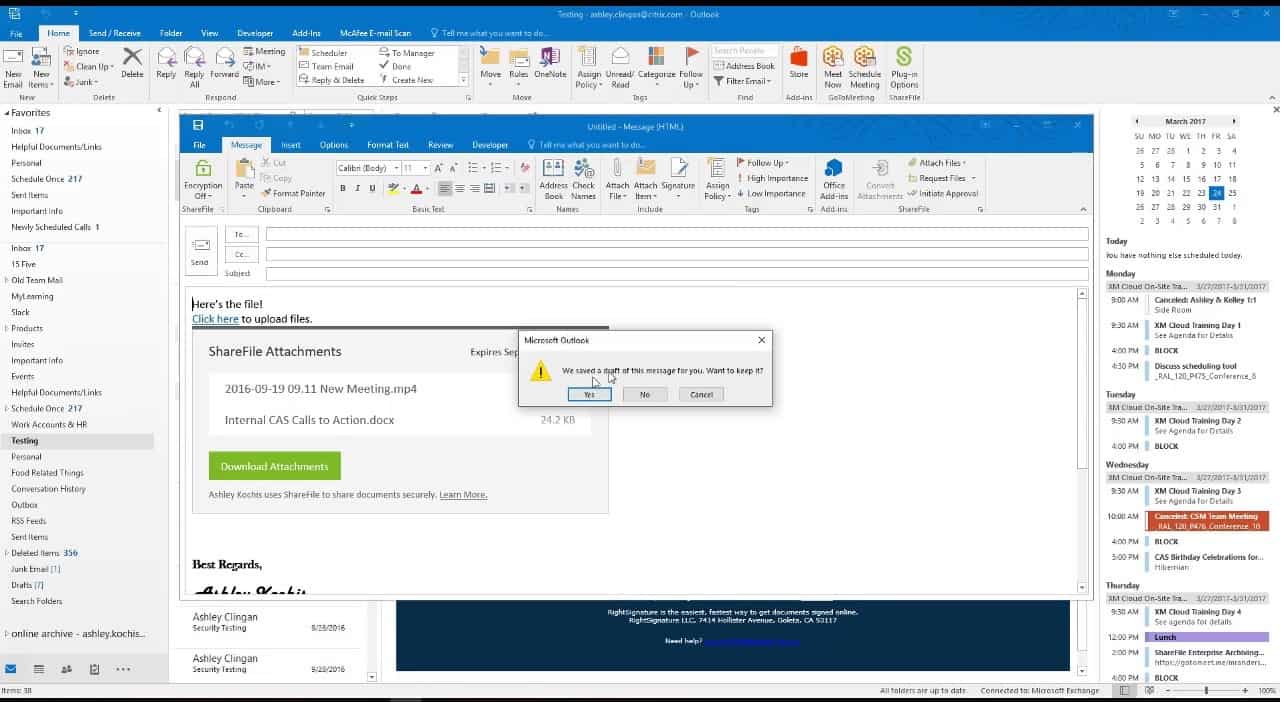
7. Citrix ShareFile
The ShareFile platform from Citrix is a secure cloud file storage service that has added tools to support file sharing and collaboration. This system includes unlimited storage space and so could be used for a company-wide data store, without the need to use on-site storage servers or retain files on local endpoints.
Key Features:
- Cloud-Based Sharing: Offers a platform designed for secure cloud file sharing.
- Sync and Backup Capabilities: Ensures files are regularly synced and backed up for data integrity.
- Seamless Microsoft 365 Integration: Enhances productivity with integration into Microsoft 365 for collaborative work.
Why do we recommend it?
Citrix ShareFile is another rival to the Files.com and ExaVault services. The tool offers a plug-in for Outlook that will strip out attachments, upload them to the cloud drive and insert an access link instead. Users can invite others to view or edit a file in their account space.
This system can be used for syncing and backup but its main purpose is to offer secure file sharing. Files are encrypted individually before uploading. The protection system uses a 256-bit AES cipher. The upload to the Citrix ShareFile server is protected by FTPS, which uses Transport Layer Security (TLS). Each file remains encrypted while on the ShareFile server. Files of up to 100 GB in size can be uploaded.
The higher plans of ShareFile include integration with Microsoft 365, Outlook, and Gmail. This provides a cloud collaboration file for documents, spreadsheets, and presentations, which can be jointly authored with version control and rollback facilities. Email attachments can be automatically removed and uploaded with a link for read-only access to the original file placed in the email instead.
The secure link mechanism is also used for file distribution. Other features offered in the ShareFile service include an eSignature system, watermarking, and automated approval workflows.
Who is it recommended for?
The package is a little more expensive than those competing systems, so you should examine the extra features of the service to judge whether it provides the extra services that you need. The base package of each plan is priced for a five member team. Per-user rates kick in above that number.
Pros:
- Versatile Storage and Sharing: Acts as a comprehensive storage, backup, and file-forwarding service with unlimited storage space.
- Individual User Accounts: Supports user-specific accounts for detailed file ownership and activity monitoring.
- Secure Link-Based Sharing: Allows file sharing through secure link invitations, ensuring safe and controlled access.
Cons:
- Mobile App Access: While providing convenience, access through mobile apps may present additional security considerations.
Citrix ShareFile is available for a 30-day free trial.
8. Accellion Kiteworks
Accellion Kiteworks is termed a “content firewall”. This is a cloud platform that offers a range of data protection services, which includes a secure file transfer system. One thing that isn’t automatically included in the cloud storage space – is optional. This is a package of tools for securing cloud file storage rather than an actual cloud file storage system with tools. You can decide which cloud storage system to use and Accellion makes its own servers available as a candidate service.
Key Features:
- Enhanced Cloud Security: Focuses on securing cloud storage and file transfers.
- Flexible Storage Options: Offers optional cloud storage space, allowing users to choose or integrate their preferred storage solutions.
- Protected File Transfers: Ensures secure file sharing and transfers with robust encryption.
Why do we recommend it?
Accellion Kiteworks offers a security system for file movements and shared access. The cloud platform includes an encryption add-on to make emails secure. The system also includes a managed file transfer (MFT) service and cloud storage for file sharing. The mechanism for sharing is by invitation.
Accellion watches over file transfers to and from your chosen cloud file storage and protects them with 256-bit AES encryption. If you choose the Accellion file storage as well, that cloud system is also protected by the same encryption.
Kiteworks can be integrated with Office 365 and Outlook. This interfaces all file-saving functions to protect the transfer of data. The service can also protect file attachments by loading them up to the secure cloud file storage and substituting a link for access.
The Kiteworks system logs all actions on files. Accellion Kiteworks has ISO 27001 certification and is validated to FIPS 140-2 Level 1. These processes and accreditations make Kiteworks a suitable tool for businesses that are following the HIPAA or PCI DSS standards.
Who is it recommended for?
This system has an appeal to businesses that need to show compliance with data protection standards because it has mechanisms to easily include the platform in the coverage of your existing SIEM and DLP packages, which will provide compliance reporting. It also integrates with Microsoft 365 as its default storage space.
Pros:
- Security-Centric Approach: Designed to secure cloud platforms, emphasizing strong AES 256-bit encryption for data protection.
- Compliance-Friendly: Tailored to assist businesses in meeting HIPAA and PCI DSS compliance, thanks to its comprehensive logging and certification.
- Versatile Integration: Easily integrates with Microsoft 365 and other systems, making it adaptable for various business environments.
Cons:
- Additional Cost for Storage: While offering significant security enhancements, the provision of storage space comes as an optional add-on, potentially increasing overall costs.
Deployment options include the SaaS system, managed by Accellion, a software package for installation on a private cloud system, or a bundle to install on your own onsite servers. You can get a demo to assess the system.