A protocol analyzer provides details of the information inside the headers of data packets as they move around a network. The detection task is also known as “packet sniffing”.
The details in a packet header include the source and destination address of the traveling message and part of this address is the port number.
By listing the port numbers on packets, a protocol analyzer can provide application-specific details of network activity.
Here is our list of the best protocol analyzer tools:
- SolarWinds Network Packet Analyzer with NPM EDITOR’S CHOICE This network device monitor extracts status information and also uses deep packet inspection to examine traffic performance per protocol. Runs on Windows Server. Start a 30-day free trial.
- ManageEngine NetFlow Analyzer (FREE TRIAL) This package of traffic monitoring systems includes a packet statistics feature that logs the port numbers in TCP headers and records traffic statistics by protocol. Installs on Windows Server, Linux, and AWS. Start a 30-day free trial.
- Site24x7 Network Traffic Monitoring (FREE TRIAL) This cloud-based package uses flow protocols to collect traffic data from network devices to implement protocol analysis and other traffic management investigations. Start a 30-day free trial.
- Paessler PRTG (FREE TRIAL) This is a bundle of monitoring tools for networks, servers, and applications and it includes a packet sniffer that has a protocol analyzer in its user interface. Runs on Windows Server. Start a 30-day free trial.
- Wireshark This is the leading protocol analyzer and one of the oldest. If you take a course on network analysis or cybersecurity, you will use Wireshark in the lab. Available for Windows, macOS, and Linux.
- Snort This traffic analysis tool is known mainly as an intrusion detection system but it includes a protocol analyzer. Available for Linux, Unix, and Windows.
- Splunk this data analyzer is widely used for searching through data and it can be fed a pcap file to make it a protocol analyzer. Available for Windows, Linux, Unix, and macOS.
- Omnipeek Network Protocol Analyzer A live traffic analyzer that can also be used to perform searches through historic data analysis. Runs on Windows.
You can read more about each of these options in the following sections.
Port numbers and protocols
In network parlance, a “port” isn’t a physical receptor on the side of a device; it is a logical identifier that creates an address. The concept of logical ports is part of the suite of TCP/IP protocols and it is found at the Transport Layer of the stack. Ports are identified as being used for TCP or UDP, while many are used for both.
A global organization, called the Internet Assigned Numbers Authority (IANA), maintains a list of assigned port numbers. Numbers are allocated to specific applications, which are also called protocols.
The purpose of the IANA list is to provide a universal list of protocol identifiers. The assignments don’t belong to any individual business. This means that no one gets an advantage over control of port numbers. The value of this universality is that software developers working independently can create compatible systems that can send and receive data without having to reach agreements with all of the other software developers in the world.
Anyone can get access to the list of assigned port numbers. IANA maintains a list of ports but it isn’t very well presented. You can get a better table of port numbers at other websites, such as the Wikipedia page on port numbers.
The full range of port numbers is subdivided into sections:
- Well-known ports: 0 – 1023
- Registered ports: 1024 – 49151
- Ephemeral ports: 49152 – 65535
The difference between these ranges is that the well-known ports are the oldest allocations and represent long-standing protocols, such as the File Transfer Protocol (FTP) and the Simple Mail Transfer Protocol (SNMP).
While well-known ports are almost all used for open-source standards, the registered ports are assigned to services that companies might have developed. However, open-source protocols are also assigned numbers in this range because there are no spare numbers left in the well-known ports range.
Ephemeral ports are deliberately unregistered and IANA won’t assign numbers in this range. Non-official lists of port numbers will include usage guidance for port numbers in this range where the regular use of one of these port numbers has been coded into a piece of widely-used software.
One of the main uses of ephemeral ports is to allow concurrent connection management. In this scenario, a software package might signal to a correspondent that the connection should continue on another port, thus freeing up the well-known port for connections from other clients.
Packet capture and protocol analyzers
Protocol analyzers need data to analyze. This data is a stream of packets that are collected from a network. The protocol analysis task is not the same as packet capture – they are two separate functions. A protocol analyzer doesn’t just operate on live data because packets can be read in from files for analysis.
The best protocol analyzers include an integrated packet capture system. However, that packet capture process probably isn’t built into the protocol analyzer. The most widely used system for packet capture is pcap and this is implemented for Unix and Unix-like operating systems, including Linux and macOS, through libpcap. Windows users need WinPcap. These systems are free to use.
The best protocol analyzer tools
Protocol analysis based on packet captures is one of the oldest network troubleshooting techniques around. There are many long-running protocol analyzers available that are free to use. Although these systems are free and old, many of them are still leading the industry because they have been adopted by large network system providers and funded, while still being kept free to use.
Our methodology for selecting protocol analyzer tools:
We examined the market for protocol analyzers and assessed the available options based on the following criteria:
- An integrated packet capture tool, such as libpcap and WinPcap
- Options to laugh packet capture from the analyzer
- Filters for packet capture and display
- Color coding for different protocols
- An indication of conversations or related streams
- A free tool or a free trial for a paid tool so that assessment can take place without payment
- Value for money that is provided by a paid tool that is worth its price or a free tool that works well
With these criteria in mind, we identified free and paid protocol analyzers, looking as well for wider system monitoring packages that include a protocol analyzer as an extra service.
1. SolarWinds Network Packet Analyzer with NPM (FREE TRIAL)
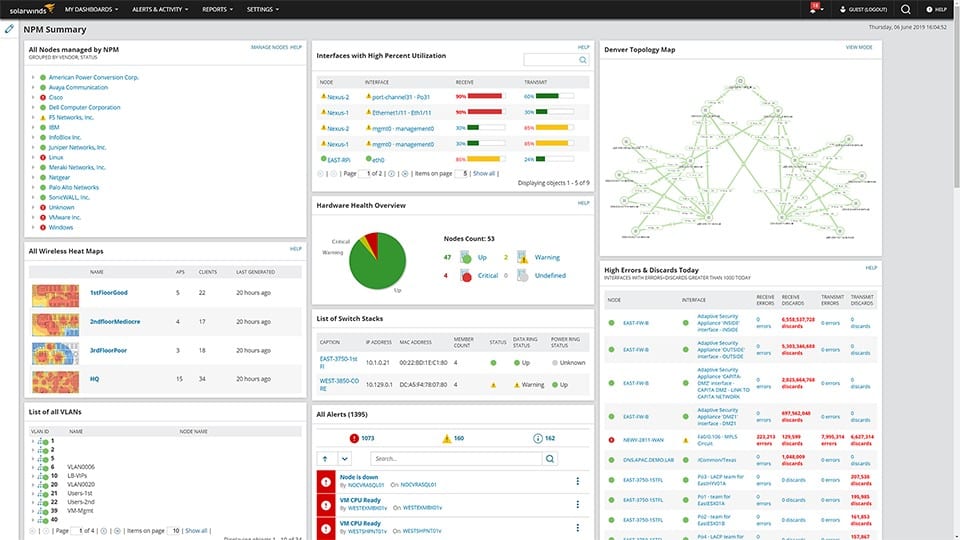
SolarWinds Network Packet Analyzer is a module of the Network Performance Monitor (NPM), a leading network monitoring system with many utilities. One of the tools in the SolarWinds package is the Deep Packet Inspection service. This enables you to slice all network performance metrics by application. The applications referred to by SolarWinds are protocols and this is derived by looking at the port numbers in passing packets.
Key Features:
- Traffic Statistics per Application: Protocol analysis
- Categorizes Traffic by Usage: Identifies data movements
- Summarizes Packets per Endpoint: Both source and destination
- VoIP Measurements: QoS statistics
- Traffic Throughput Rates: Spot network slowdowns
Distinct feature
A big advantage that this solution has over the other tools in this list is that it isn’t a standalone protocol analyzer; it is part of a much bigger set of network monitoring tools that includes an autodiscovery service, a network inventory creator, and a network topology mapper.
Why do we recommend it?
SolarWinds Network Performance Monitor is well known as a status tracking tool to acth over network device health. However, the package also includes a packet analyzer, which reads the headers of packets and derives information on destination and source ports. That makes the tool a protocol analyzer that lets you measure traffic per application as it passes through your network.
The user interface for the Network Performance Monitor is very sophisticated and presents a lot of graphical representations of traffic data as well as lists. The screens are well laid out and make data interpretation easy. The tool doesn’t include a data viewer for manual traffic analysis.
Who is it recommended for?
The Network Performance Monitor provides automated monitoring for large networks. The larger the network, the more valuable the service. The protocol analyzer is an extra feature of the package that supports manual traffic analysis. However, this analysis can be automated as well by setting up throughput thresholds that will trigger alerts.
Pros:
- Easy to Use: Well-presented data screens
- Automated Monitoring: Alerts for unusual traffic patterns
- User Activity Tracking: Categorization of traffic for business or personal use
- Security Monitoring: Records unusual spikes in traffic
- Packet Analyzer: Removes the need to switch to Wireshark
Cons:
- Only Available for Windows Server: No SaaS option and no software for Linux
The software for SolarWinds Network Performance Monitor installs on Windows Server and you can assess the system with a 30-day free trial.
EDITOR'S CHOICE
SolarWinds Network Packet Analyzer is our top pick for a protocol analyzer because the package provides many other functions as well as its deep packet inspection utility, so you get much more than just a protocol analyzer with this system. The tool is able to present traffic speed information per protocol. It will also discover all devices on a network and document them with an inventory and a network topology map. The package performs constant polling of network devices with the Simple Network Management Protocol. This enables it to present live status reports for every device on the network.
Download: Download a 30-day FREE Trial
Official Site: https://www.solarwinds.com/registration/network-performance-monitor/
OS: Windows Server
For even more network traffic troubleshooting power, you can add traffic statistics to your network analysis efforts if you also use the NetFlow Traffic Analyzer. This communicates with switches and routers to extract traffic statistics using NetFlow, IPFIX, sFlow, J-Flow, and other flow protocols. The service will also help you to implement traffic shaping measures to improve network performance. You can buy the Network Performance Monitor and the NetFlow Traffic Analyzer together in the Network Bandwidth Analyzer Pack. Start with a 30-day free trial.
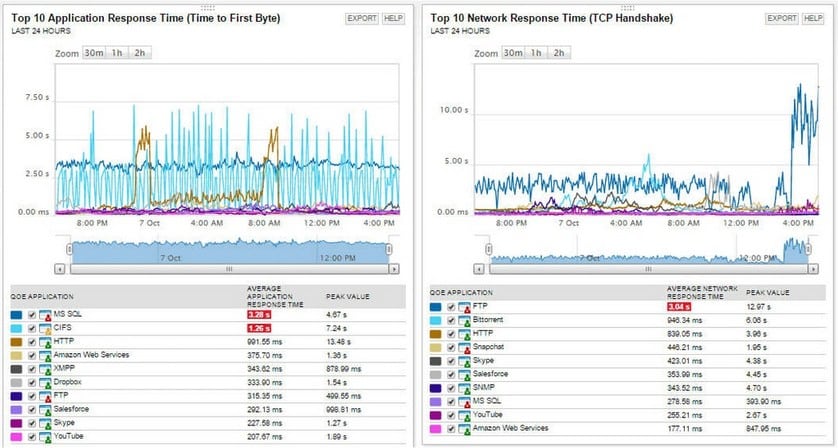
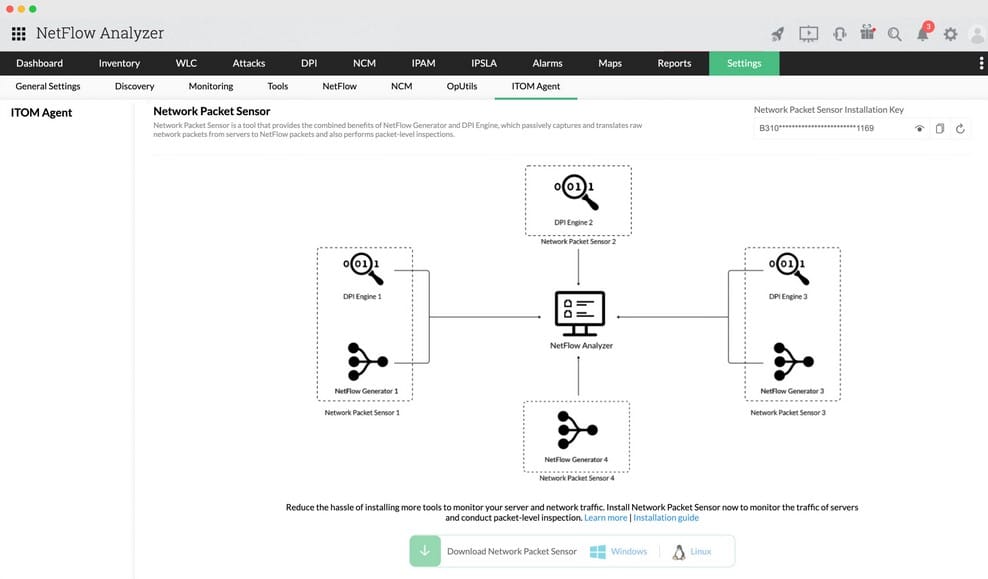
2. ManageEngine NetFlow Analyzer (FREE TRIAL)
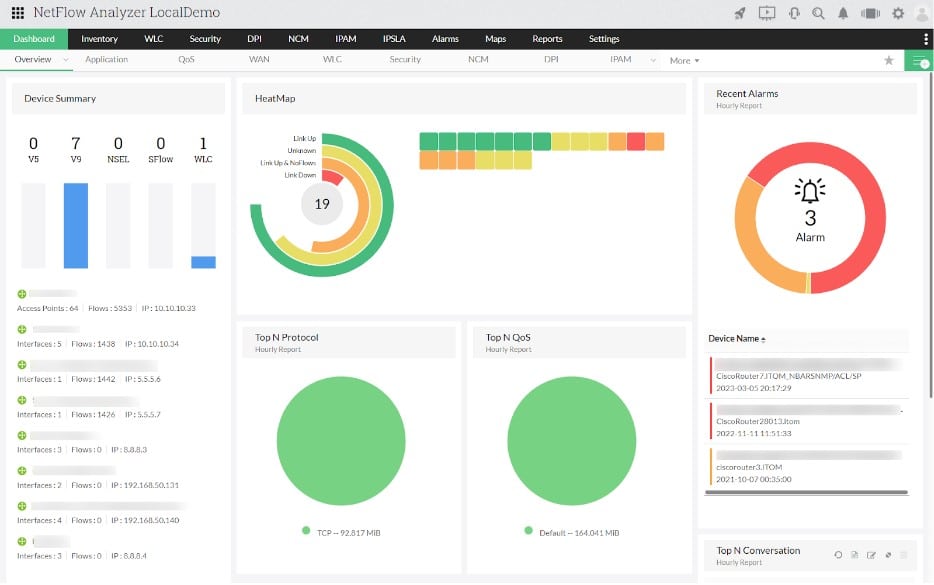
ManageEngine NetFlow Analyzer is a protocol analyzer that analyzes the packet headers as it traverses through the network and generates traffic information of protocols. It contains a configurable dashboard that shows the top protocols, applications, and devices of the network.
Key Features:
- Application Mapping: Discovers dependencies
- Top Talkers Traffic Insights: Endpoints and remote locations
- Network Forensics: Security analysis
- Cloud Hosting Option on AWS: Also available for Windows Server and Linux
Why do we recommend it?
ManageEngine NetFlow Analyzer provides a number of options for protocol analysis. A packet sniffer in the package can be set up to just count and discard packets, giving you a protocol analyzer without building up large files. The package also uses flow protocols, such as NetFlow, sFlow, and IPFIX, which can query switches for traffic data per protocol.
The ManageEngine system exploits the statistics-gathering functions of network devices. It doesn’t need to separately capture packets because the routers and switches on your network automatically record data about the packages that they process. So, the NetFlow Analyzer just downloads that data from the devices. This is a very efficient strategy.
Who is it recommended for?
ManageEngine offers a Free edition of the NetFlow Analyzer but it is limited to monitoring only two interfaces. This is not going to be enough any but the smallest businesses. So, small businesses would probably look for a free protocol analyzer rather than opt for the NetFlow Analyzer.
Pros:
- Flow Protocols: NetFlow, IPFIX, sFlow, J-Flow, AppStream, and NetStream
- Traffic Statistics Overviews: Also drill down, segmented stats
- Time-Series Throughput Graphs: Can be customized
- Protocol Analysis: Uses Network-based Application Recognition (NBAR)
Cons:
- Not a SaaS Package: You have to arrange hosting separately
ManageEngine NetFlow Analyzer is available in different editions: Free, Professional, Standard, and Enterprise. The Free edition is suitable for small businesses to help collect data from two interfaces. With the Standard edition small-medium businesses can leverage basic bandwidth monitoring capabilities, especially if it does not require raw data reports or add-ons. The Professional Edition can be used by businesses that would like to monitor their network having as least as 10 interfaces or a single LAN. For larger enterprises that have distributed networks, the enterprise edition will be the best match, as it can offer better scalability. You can get a 30-day free trial of the Professional edition.
3. Site24x7 Network Traffic Monitoring (FREE TRIAL)
Site24x7 Network Traffic Monitoring implements protocol analysis and other traffic data segmentation by collecting throughput statistics from network switches and routers. This tool uses flow protocols to source traffic statistics. This information is posted in the console of Site24x7 for manual analysis.
Key Features:
- Flow Protocols: NetFlow, IPFIX, sFlow, J-Flow, cFlow, AppFlow, and NetStream
- Live Traffic Monitoring: Also historical analysis for capacity planning
- Path Testing: Across the network or over the internet
Why do we recommend it?
Site24x7 Network Traffic Monitoring is delivered from a cloud platform of system monitoring and management tools. This service collects the data that switches and routers accumulate. This information illuminates the capacity of each switch interface and so each link on the network and how much of that capacity is being used.
The Site24x7 is able to communicate with network devices that are provided by different manufacturers. This is possible because the package includes all of the flow protocols that different suppliers use. So, the tool will gather data with the NetFlow, IPFIX, sFlow, J-Flow, cFlow, AppFlow, and NetStream protocols. This data is then centralized in the Site24x7 dashboard and displayed live. It is also stored for later analysis. 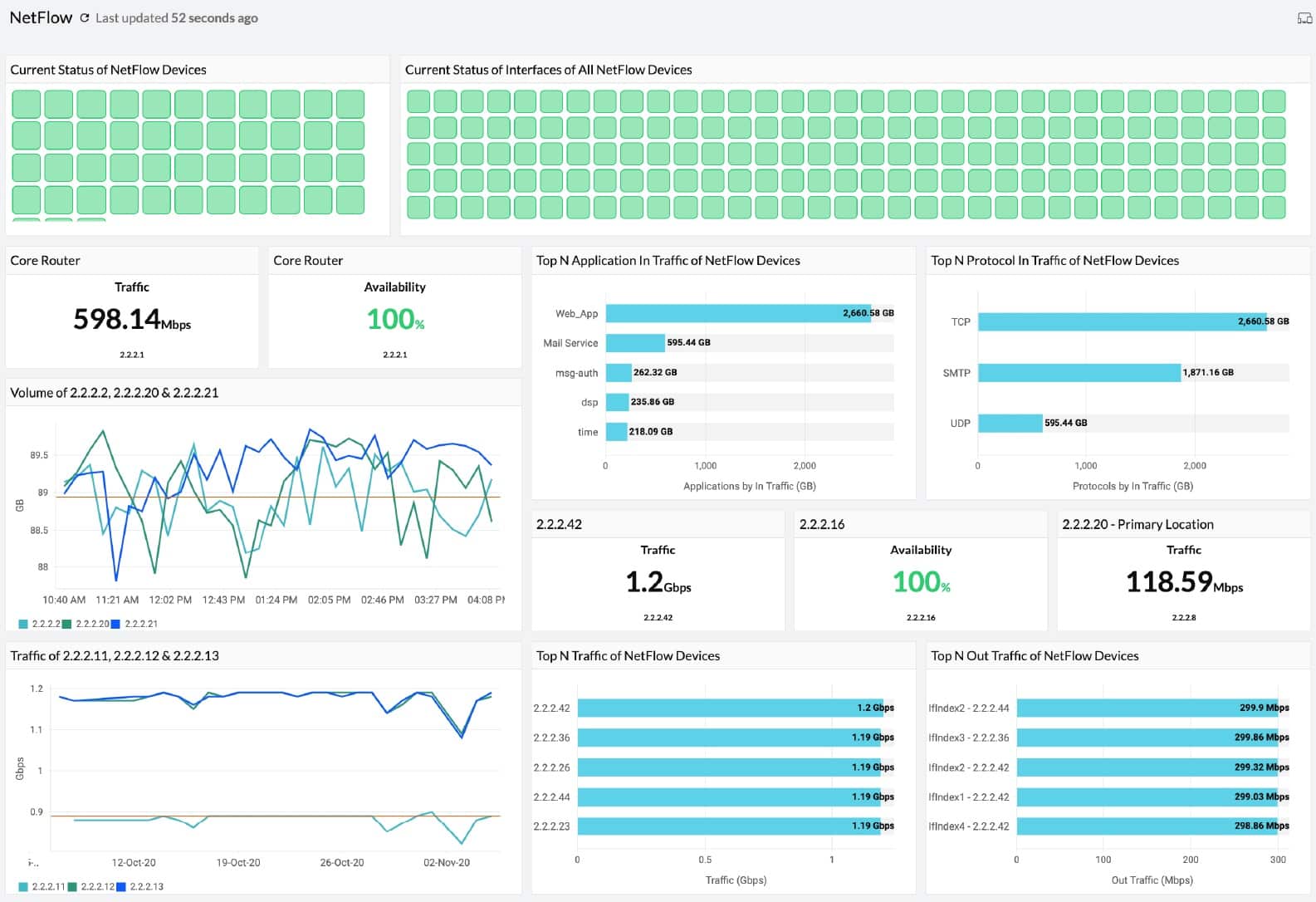
Who is it recommended for?
This package is suitable for any size of business. The system includes a series of performance expectations that trigger alerts when crossed. For example, alerts will tell you if traffic throughput drops or reaches a point at which network devices will be overwhelmed. These alerts are forwarded to technicians by email, SMS, or Slack post.
Pros:
- Alerts for Traffic Anomalies: Surges, bottlenecks, and drops
- Top Talker Analysis: Per protocol, source, and destination
- A Cloud-Based System: Can monitor multiple networks
Cons:
- No On-Premises Version: Only available as a SaaS platform
Site24x7 is a cloud platform with many system monitoring and management tools. The network monitoring system includes network testing tools, which can help track down internet connections that aren’t working. The platform also provides network device status tracking. Network monitoring is bundled in with many other tools as plans. There are many plans available, including one for managed service providers. You can investigate the Site24x7 platform with a 30-day free trial.
4. Paessler PRTG (FREE TRIAL)

Paessler PRTG provides a choice of monitoring systems for networks, servers, and applications. The bundle includes a large number of monitors, which are called sensors. The price you pay for the system depends on how many sensors you want to turn on and then you choose which to activate.
Key Features:
- Choice of Packet Analysis Techniques: Flow protocols or packet sniffing
- Traffic Generator Rankings: Top talkers reports
- Includes Other Network Monitors: Implements monitoring with the Simple Network Monitoring Protocol (SNMP)
Why do we recommend it?
Paessler PRTG includes a packet sniffer, which only records data from headers rather than storing packets. This is the classic protocol analyzer strategy and you can get port activity reports along with other analyses, such as top talkers. PRTG is a software package for Windows Server and a SaaS platform.
The PRTG sensor list includes a number that can be used for packet sniffing and protocol analysis. The straightforward packet sniffer will capture packets and display statistics about them. The screen or this sensor includes a ranking for top traffic generators per application, per device, and per conversation.
Other traffic analysis options come from bandwidth analysis systems, such as IPFIX, NetFlow, J-Flow, and SNMP. You can also switch to network performance screens to see whether any of the switches and routers on your network is experiencing problems.

Who is it recommended for?
PRTG is permanently free to use if you only activate 100 sensors. So, it is possible for small businesses to use this package as a protocol analyzer without ever having to pay and still being able to use some other tools in the package. Big businesses can go right up to a multi-site implementation.
Pros:
- Flow Protocols: NetFlow, IPFIX, J-Flow, and sFlow
- Displays Traffic per Protocol: Protocol analysis
- Link Analysis: Also path testing
Cons:
- No Tools for Manual Protocol Analysis: Export data for analysis in another tool
Paessler PRTG installs on Windows Server and you can use it for free forever if you only activate 100 sensors. You can get a 30-day free trial of the system with all sensors activated.
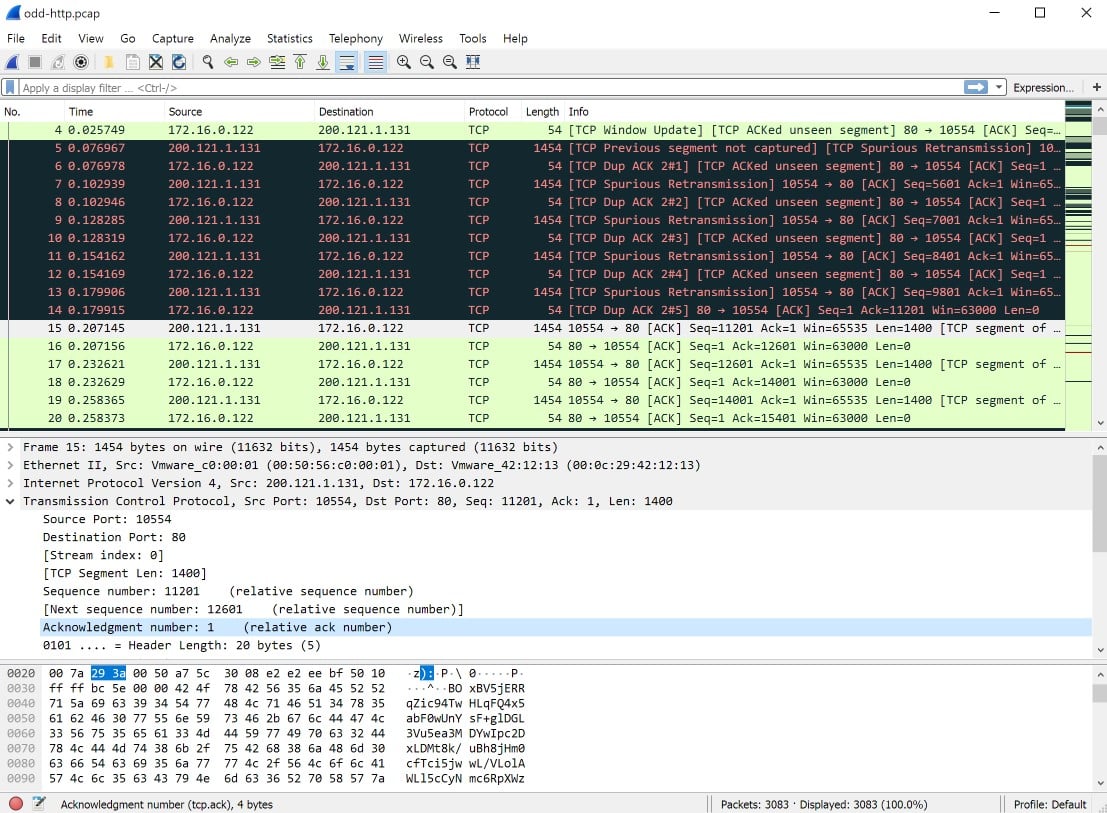
5. Wireshark
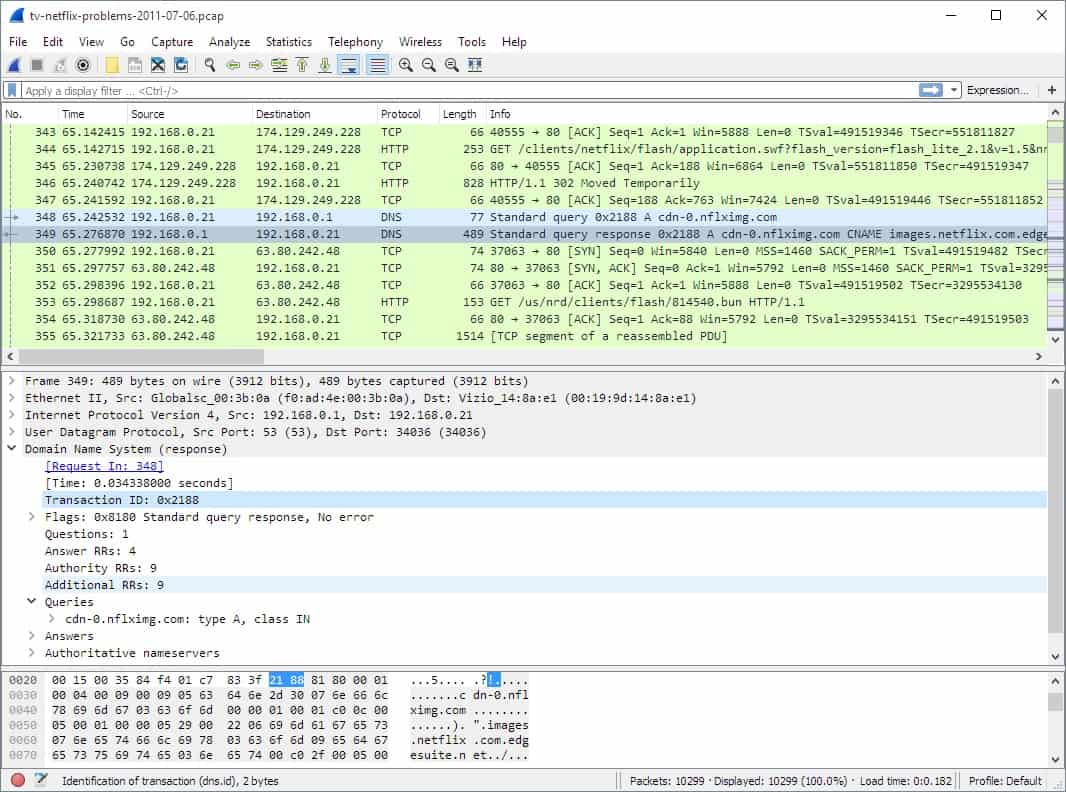
Wireshark ticks all of the boxes to be a great protocol analyzer: it integrates a packet capture system, it color codes protocols and it gives a range of quick options to filter packets through a right-click menu. What makes Wireshark even better is that it is free to use.
Key Features:
- Easy to Install and Use: Available for Windows, macOS, and Linux
- Start and Stop Packet Capture: Uses WinPcap and libpcap
- Query Language: Both for packet capture and packet display filtering
Why do we recommend it?
Wireshark is a widely used packet analysis tool that is free and is used on courses in network management and cybersecurity. So, it is likely that you are already familiar with this package and know how to use it. Wireshark has its own querying and filtering language, which can be applied to packet capture and to packet analysis.
The Wireshark system doesn’t have its own packet capture routines, but it works seamlessly with WinPcap and libpcap. The installer for Wireshark downloads and installs the right pcap version for you while it installs its own software. You start and stop packet capture with a button within the Wireshark interface.
Who is it recommended for?
This is a very powerful tool that can help you with a range of investigations, not just protocol analysis. Wireshark is free to use, which makes it accessible to all sizes of businesses. The software for the package will run on Windows, macOS, and Linux.
Pros:
- Industry-Recognized Tool: Network and cybersecurity professionals need to understand this tool
- Command-Line Version: This is called Tshark
- Free to Use: There is no paid version
Cons:
- The Query Language is Very Complicated: It is a proprietary command set that you will not encounter anywhere else
Wireshark has its own query language with long lists of commands and data definitions. The big problem with the system is that the query language is very complicated – it takes training and a lot of time to be able to use it. Filters can be applied to packet capture that greatly reduce the volume of packets that are brought into the viewer. The user gets the option of whether to save captured packets.
6. Snort
Snort is a well-known intrusion detection system. However, the package is a data analyzer and can be applied to several different applications, such as packet-level scanning and protocol analysis.
Key Features:
- Intrusion Prevention System: Seeks out suspicious packets
- Packet Display and Searching: Possible in a data viewer within the console
- Automated Rules: Make your own or buy a pack
Why do we recommend it?
Snort is a free tool that is owned by Cisco Systems but is independently run. The main purpose of the system is to detect intrusion but it implements protocol analysis as part of that aim. The system is very flexible and its main mechanism is to detect patterns in traffic, which involves packet sniffing.
Snort has a packet sniffing mode which is based on the pcap system. You don’t need to run libpcap or WinPcap separately because Snort can integrate with those tools to read packets directly from the network.
Snort’s key strength is its automated searches which are implemented by rules. You can acquire rules yourself or write them yourself. With these rules, you can create your own alert conditions and let Snort operate as a live network performance monitor.
Who is it recommended for?
Snort is a useful tool for any network manager and it can be used to implement cybersecurity protection. The vital element of this package is its rule sets. You can get these free from the community or pay for a megapack from Snort.
Pros:
- Automated Searches: Identifies suspicious activity
- Customizable Filtering and Detection Rules: Set up your own detection rules to scan automatically
- Customizable Alerts: Decide what events will provoke a notification
Cons:
- Takes Time to Learn: The detection rules are central to the operation of the IPS
Snort is available for many Linux distros, BSD Unix, and Windows. The system is free to use but it becomes more powerful with a set of rules. You can get community-created rules for free and more powerful business-centered rule packs for a subscription.
7. Splunk

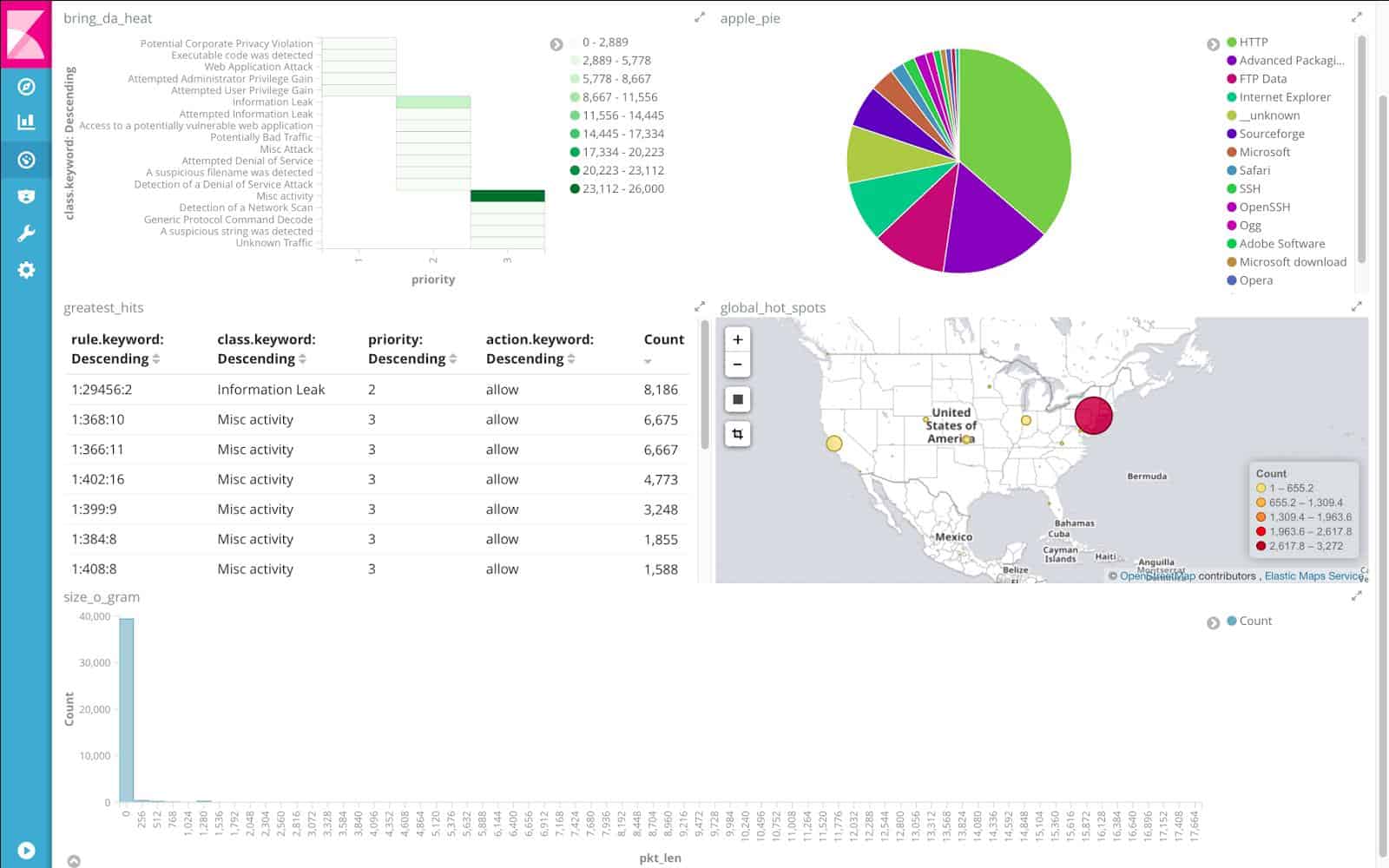
Splunk is a data analysis tool and it is available in both on-premises and SaaS versions. Although you can use Splunk to create any data search, creating your own analysis applications from it, the tool has become more successful through the production of pre-written tools, especially Splunk Enterprise Security. This security package is a SIEM and it also offers a live port and protocol activity monitor.
Key Features:
- Data Analysis Tools: Pre-written SIEM and monitoring packages available
- Adaptable to Custom Applications: Construct your own data analyzer
- Analyzes Any Data: Also useful for examining marketing and financial data
Why do we recommend it?
Splunk used to be free, but it isn’t anymore. The tool is basically a data flow processor and it is particularly useful for analyzing log files. It isn’t a protocol analyzer out of the box. However, you can feed a packet header stream into it to get traffic data compiled per protocol.
It is possible to use Splunk to look at packet data and identify protocol activity through a free plug-in. The community of users of Spunk includes an app marketplace, called Splunkbase. There is a package available on that forum called PCAP Analyzer for Splunk. This service is free to use and it provides a connector to read pcap files and a set of searches that place data in its own Splunk screens – there is a protocol analysis feature in this tool.
Who is it recommended for?
Splunk has expanded its platform rapidly to the point where it has been completely transformed from the original free data analyzer. The platform offers a monitoring package and a security system. Either of these could be adapted to provide protocol analysis. However, this function would be a side benefit.
Pros:
- Flexible Tool: Adaptable for a range of customized applications
- Free Plug-in for Packet Analysis: This is based on pcap
- Protocol Analyzer: Collates traffic data by port number
Cons:
- Runs off PCAP Files Rather than an Integrated Packet Sniffer: Packet capture files can get really big
Splunk Enterprise installs on Windows, Windows Server, Linux, Unix, and macOS, or you can access Splunk Cloud through any standard Web browser. Both systems are available for a free trial – 14 days for Spunk Cloud and 60 days for Splunk Enterprise.
8. Omnipeek Network Protocol Analyzer

If you just want a pure protocol analyzer without lots of peripheral capabilities, then the Omnipeek Network Protocol Analyzer from LiveAction is probably your best bet. As the name suggests, this tool is all about tracking traffic by protocol and it does it very well.
Key Features:
- Focused on Protocol Analysis: A software package for Windows
- Live Traffic Throughput: Captures packets
- Graphical Data Representations: Click through to packet details
Why do we recommend it?
LiveAction Omnipeek Network Protocol Analyzer is a pocket capture tool, so you can implement your own analysis on packet headers as well as using the pre-written protocol analysis service. The interface produces time-series graphs of protocol traffic and will also record statistics for historical analysis.
When you use Wireshark, you start with a screen full of packet contents and then filter out data so you get through the mass of available data to something of workable size. With Omnipeek, it’s the other way around because it starts with an overview and lets you click your way through to slices of data until you end up right down at the packets. This is a much more manageable way to approach traffic data because you only need to go down to a level of detail that explains the problems that your network is experiencing.
If your technical skills are not that great and you don’t want to have to learn a whole programming language to get something meaningful to appear on the screen, then you will like the Omnipeek Protocol Analyzer a lot.
Who is it recommended for?
LiveAction doesn’t publish its price list but you should know that it is way out of reach of small businesses. It is more expensive than the Network Performance Monitor, which provides a lot more network monitoring capabilities. Large businesses would be interested in the Omnipeek system as an addition to regular network monitoring systems.
Pros:
- Easy-to-Read Screens: Needs no training
- Displays Live Traffic Data: Can also store statistics
- Gets Packets from Wired and Wireless Networks: Can isolate media traffic
Cons:
- Doesn’t Do Much Else other than Protocol Analysis: Isn’t a full analysis tool
Omnipeek Protocol Analyzer is an on-premises software package that installs on Windows Server. The tool can gather packets itself, so you don’t need to set up a separate PCAP service and feed it files. The system can analyze wireless networks as well as LANs. Examine the capabilities of Omnipeek Protocol Analyzer with a 30-day free trial.