In March 2016, Jigsaw featured the Billy the Puppet character from the horror movie Saw on its ransom demand page
Here are examples of the type of protection software that you will need to protect against Jigsaw and any other ransomware:
- ManageEngine Ransomware Protection Plus EDITOR’S CHOICE An all-in-one ransomware protection tool that safeguards your endpoints from Jigsaw ransomware. It can detect and neutralize different kinds of ransomware, regardless of whether they infect the memory, processes, or files. Start a 30-day free trial.
- CrowdStrike Falcon Insight This dual-level system provides a cloud-based controller and a fully independent endpoint protection unit. The endpoint unit is an antivirus and it also uploads activity reports to the central controller for further threat hunting.
- ManageEngine DataSecurity Plus This megapack includes file integrity monitoring, email scanning, endpoint activity tracking, and automated responses.
Although it struck fear into businesses worldwide, this terror turned out to be fallible because it was written in .NET, and its code could be read to work out how to decrypt files instead of paying the ransom.
Despite its security weakness, Jigsaw needs to be protected against. Although not currently on the rampage, Jigsaw has a habit of rising from the dead, so it could yet return and scare the life out of your network manager.
The name of Jigsaw
Jigsaw ransomware got its name from the iconic puzzle piece symbol used in its ransom note, which is a direct reference to the “Saw” movie franchise. The jigsaw puzzle piece resembles the logo of the antagonist, known as Jigsaw, from the popular horror series Saw. In the films, the character Jigsaw is known for setting up traps and games that force victims to make difficult choices, often involving life-threatening consequences.
This connection to the Saw movies is evident in the ransom notes generated by Jigsaw ransomware, which not only feature the puzzle piece but also include references to the films, often with threatening and disturbing messages designed to frighten the victim. For example, the ransomware might include images or messages inspired by the Saw franchise’s notorious, graphic scenes, heightening the psychological pressure on the victim to pay the ransom.
The use of this horror-themed imagery and the puzzle motif ultimately led to the name “Jigsaw” for the ransomware. It is also known by several other names, reflecting its various versions and its association with different malware families. Some of the other names it has been identified by include:
- Puzzel Ransomware – This name refers to the puzzle piece icon used in the ransomware’s ransom note, as well as its behavior of progressively “puzzling” over the victim’s files.
- Saw Ransomware – Named after the infamous horror movie franchise, this variation includes references to the Saw films in its ransom notes and its threatening tone.
- Zer0Cool Ransomware – A variant of Jigsaw ransomware that emerged later, adopting the “Zer0Cool” name from the popular hacking alias featured in the 1995 movie Hackers.
These alternate names highlight the evolution of Jigsaw ransomware, with each version adding new features or modifications to enhance its effectiveness or to evade detection. Despite the different names, they all share the same core functionality: encrypting files and demanding a ransom for their release.
In addition to the names already mentioned, Jigsaw ransomware has also been associated with another variant called BitcoinBlackmailer. BitcoinBlackmailer is a name that refers to a version of the ransomware that demands payment in Bitcoin for the decryption of the victim’s files. This variant, like other versions of Jigsaw, uses the same aggressive tactics, such as threatening to delete files progressively if the ransom is not paid within a specific time frame.
BitcoinBlackmailer gained attention for its use of Bitcoin as the preferred payment method, aligning with the trend of ransomware creators adopting cryptocurrency due to its anonymity. It also employed psychological tactics, including references to the Saw movie franchise and a threatening message aimed at pressuring victims into paying the ransom.
Despite the different names associated with Jigsaw ransomware, they all share the same underlying malware and ransom tactics, making them part of the same ransomware family.
What does Jigsaw ransomware do?
Jigsaw ransomware only attacks computers running the Windows operating system. Jigsaw gets onto a system through spam email. Variants of the ransomware can also be found in Adware and on porn site downloads. The attachment or download includes the installer for Jigsaw and will activate once the file is opened.
Jigsaw hides its existence by adopting the name firefox.exe or drpbx.exe. The code for the encrypting virus is located in %UserProfile%\AppData\Roaming\Frfx\firefox.exe, and it writes a launching command for itself in the Startup process list.
The ransomware encrypts all data files on the infected computer, plus its Master Boot Record. It uses AES encryption. It also ensures it starts up with the computer. Encryption starts immediately once the program has been installed. Fortunately, Jigsaw doesn’t move laterally around a network. It only encrypts files on the device onto which it has downloaded. The system does not encrypt executables.
The ransom screen appears once the encryption process has been completed. This includes a countdown for an hour; when that reaches zero, a file gets deleted. The screen consists of a button, which, when pressed, brings up a text file that lists all of the encrypted files.
The ransom for the decryption key is the Bitcoin equivalent of $150. To motivate the victim, Jigsaw deletes a file after one hour. It then performs a delete cycle every hour, deleting an increasing number of files with each action. If the payment isn’t made 72 hours after the initial message shows, the ransomware will wipe the whole computer.
Rebooting the computer is a bad idea because the ransomware will start up again and delete 1,000 files as a punishment. The ransom warning also states that 1,000 files will be deleted if the user attempts to terminate the malware’s running process. However, this turned out to be untrue, making it very easy to defeat the program.
Many cybersecurity analysts concluded that Jigsaw was the product of amateurs, perhaps overachieving teenagers, because it wasn’t very well planned. The ease with which researchers could spot the process and stop it showed that the hackers didn’t have much experience creating malware. This leads to the conclusion that the Jigsaw system was more of a dare than a threat.
Paying the ransom for Jigsaw ransomware
The ransom screen shows the identifier of a Bitcoin wallet. The victim is supposed to buy the demanded Bitcoin and allocate them to that wallet.
The screen also includes a button that the victim has to press once the payment has been made. The system then checks the account for the deposit and, if that is detected, it will update the program to decrypt all of the files and then delete all of the ransomware components, putting the computer back into its original state.
Variants of Jigsaw
There were many variants of Jigsaw, each indicated by a different ransom screen, a different extension used for encrypted files, and different methods of ingress. The amount of the ransom changed with each version as well. The first incarnation asked for $150, but the demands of subsequent variants ranged from $10 to $380. The original Jigsaw added the .fun extension and the developers initially used this name for the ransomware.
Newer versions of the Jigsaw malware were either adaptions to change the language of the demand screen, refinements of the code, changes to the ransomware screen layout, or differently named ransomware that was almost identical to the original Jigsaw.
Some variants used a contact email address as the encrypted file extension with several different addresses employed. This could imply that many of the variants were adapted by other individuals who had acquired the Jigsaw code.
Recovering from Jigsaw ransomware
Cybersecurity analysts discovered very quickly that the Jigsaw ransomware and all of its variants could be easily defeated. Although the ransom screen states that 1,000 files will be deleted if the user tries to stop the process, that isn’t the case.
Follow these steps to recover from Jigsaw for free:
- Open the Task Manager and kill two processes. These are Firefox and Dropbox. The variant you have might use either or both of these. If you don’t spot both, don’t worry. Just make sure that neither is running.
- Open the Startup tab in the Task Manager and disable the Firefox and/or Dropbox entries there.
- Download the CheckPoint Jigsaw Puzzle Solver by clicking here. Unpack the JPS.zip file.
- Go to the directory you unzipped into and right-click on the JPS.exe file—select Run as Administrator.
- Follow the instructions in the Jigsaw Puzzle Solver.
The Check Point utility tricks the Jigsaw program into thinking that the ransom has been paid, so it launches all of its remediation processes and decrypts all files. It will also clean up by removing all elements of the Jigsaw ransomware from the computer.
Two characteristics of Jigsaw make it easy to deal with. First of all, it only infects one computer at a time; it doesn’t replicate itself around the network. Secondly, it fires immediately after it has been installed on a computer, so you don’t have to worry that there might be copies lying dormant on any of your computers.
Protecting against Jigsaw ransomware
Jigsaw hasn’t emerged again for quite a while. However, the creators were never arrested, so they are still out there and could relaunch a campaign at any time. Although there is an easy solution available to reverse the encryption, these hackers rely on the fact that some people who are attacked will panic and pay the ransom as quickly as possible without looking for a free solution.
The hackers behind Jigsaw were never identified. It wasn’t even discovered which country they operate in. There is plenty of research published on the Web that explains the weaknesses of Jigsaw, and the hackers are more than likely to have read all of that analysis. They could be out there right now, hardening their ransomware to make it harder to defeat.
Jigsaw ransomware gets downloaded by the computer user. Therefore, essential protection against future attacks by this and any other ransomware is to educate the user community about downloading attachments on emails from unknown sources. It is also a good idea to place penalties for users to prevent them from downloading unauthorized software onto company computers.
You should also have intelligent cybersecurity software installed on all endpoints and invest in security monitoring software.
The best tools for defense against Jigsaw ransomware
As desktop computers are the most vulnerable to Jigsaw ransomware, you need to get an endpoint detection and response suite (EDR) package to protect all of your endpoints. If you are tied to a data privacy standard, such as HIPAA, PCI DSS, or GDPR, you should have security software to defend sensitive data from any attack.
EDR systems have evolved from the original antivirus systems. Whereas AVs checked for files or processes running on a computer in a known malware list, EDRs are more sophisticated. IT takes time for cybersecurity research labs to become aware of new malware, investigate it, and produce a solution. During that period, many computers could be infected by what are called “zero-day attacks.” Modern EDR systems don’t rely on a blacklist. Instead, they look for unusual behavior.
A sound EDR system shares information about attacks between clients. This cuts out the research labs by pooling experiences, so as soon as the implementation of an EDR spots a new virus on one client site, all of the other instances of that EDR operating in the world know about it.
Our methodology for selecting a Jigsaw ransomware protection system
We reviewed the market for cybersecurity packages that can defend against ransomware, such as Jigsaw, and tested the tools based on the following criteria:
- An endpoint activity scanner that works on Windows
- Protection against infected email attachments
- File integrity monitoring
- Data backup services
- An alerting mechanism that triggers on the detection of unusual activity
- A free edition or a free trial so a tool can be tested before buying it
- A fair price with respect to the services offered or a free system
1. ManageEngine Ransomware Protection Plus (FREE TRIAL)
ManageEngine Ransomware Protection Plus is an advanced tool that maximizes the security of your endpoints by detecting and neutralizing ransomware attacks before they impact your infrastructure. Its comprehensive approach, from detection to recovery, makes it a convenient cybersecurity tool.
Key Features:
- Improved security posture
- Safe backups
- One-click recovery
- Autonomous security
- Low false positive
Why do we recommend it?
We highly recommend ManageEngine Ransomware Protection Plus because its features cover every aspect of ransomware protection. Starting from its advanced detection capabilities to its one-click data restoration, the entire process is smooth and streamlined, and ensures minimal impact from the ransomware.
Its intuitive user interface provides complete visibility into the ransomware mitigation process. A highlight is that it works even when there is no Internet access, making it a good choice in situations where you can’t connect to the Internet. Also, it generates detailed reports that can help with understanding the root cause of the problem and the efforts taken to mitigate it.
Who is it for?
A good choice for MSPs and large organizations that need dedicated protection against ransomware attacks. It can be useful for organizations with a distributed environment spanning thousands of endpoints.
Pros:
- Complete mapping: It maps the entire ransomware lifecycle, from entry to recovery, for in-depth analysis.
- MITRE ATT&CK: Reports the ransomware attacks and strategies to the VirusTotal Community.
- Critical file protection: Prevents unauthorized processes from modifying the critical files and data.
- Device isolation: Identifies and isolates infected devices to prevent the ransomware from spreading.
Cons:
- Technical resources: Requires technical resources for configuration.
Register for a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Ransomware Protection Plus is the editor’s choice for protecting against the Jigsaw ransomware because of its proactive defense capabilities. With its advanced scanning, the ransomware can be detected and neutralized before it can create a big impact. Its recovery processes are also seamless, reducing downtime and data and productivity loss. Its use of the latest technologies is another reason why this tool is a clear choice to tackle emerging patterns in ransomware attacks.
Download: Start a 30-day FREE Trial
Official Site: https://www.manageengine.com/ransomware-protection/
OS: Windows
2. CrowdStrike Falcon Insight
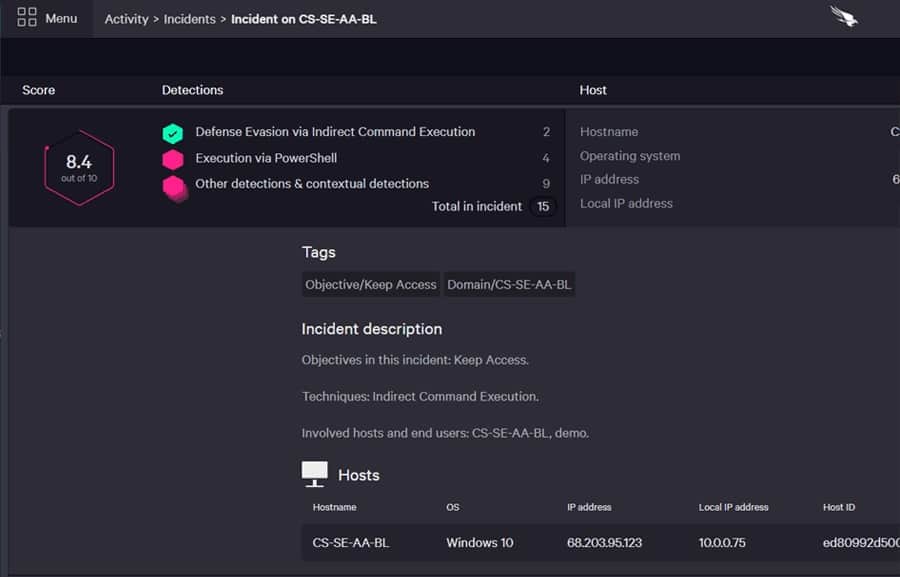
CrowdStrike Falcon Insight is a coordinated enterprise-wide EDR. It includes modules installed on all endpoints plus a cloud-based central controller. The endpoint agents are implementations of a standalone next-generation antivirus system marketed by CrowdStrike. This is called Falcon Prevent.
Key Features:
- On-device antimalware
- Centralized threat hunting
- Corporate threat intelligence
- Endpoint hardening
- Incident warnings
Why do we recommend it?
CrowdStrike Falcon Insight is a hybrid solution. The dual level of Falcon is its strength. While central, cloud-based systems can mine log files and discover company-wide threats, that process has a lead time. The local unit of this package can act much faster on the detection of ransomware activity.
The endpoint agents are fully autonomous and will continue to operate if the computer is cut off from the network and can’t get through to the Insight controller. Ordinarily, this module monitors the endpoint and uploads event data to the Insight cloud system for analysis. The cloud system also receives automated threat intelligence from the Insight user community.
The endpoint agent looks for abnormal activity and can implement immediate actions if it spots it. Instructions for responses also come down from the Insight system. The service can kill processes, delete files, isolate the device from the network, suspend user accounts, and block communication with suspicious IP addresses. All of these actions are suitable for dealing with Jigsaw.
The abilities of Falcon Insight provide protection against zero-day attacks as well as a list of known malware. The coordinating functions of the Insight cloud module mean that as soon as one endpoint is attacked, all other endpoint agents are put on alert.
Who is it recommended for?
The CrowdStrike Falcon suite is a high-end solution, so it would be a little too expensive for small businesses. The Falcon system is very easy to expand. The endpoint unit is called Falcon Prevent, which feeds data through to a cloud-based controller, which is also a SIEM. Just install Prevent to include another endpoint.
Pros:
- Excels in hybrid environments (Windows, Linux, Cloud, BYOD, etc)
- Intuitive admin console makes it easy to get started and is accessible in the cloud
- Can track and alert anomalous behavior over time, improves the longer it monitors the network
- Lightweight agents take up little system resources
Cons:
- Would benefit from a longer trial period
You can get a 15-day free trial of Falcon Prevent.
3. ManageEngine DataSecurity Plus
ManageEngine DataSecurity Plus is a system for protecting sensitive data. This package was designed to assist companies that have to comply with a data privacy standard, such as HIPAA, PCI DSS, and GDPR. Data protection systems have to ensure that data is not damaged or inaccurate and maintain its availability for appropriate use. Some malware attacks aim at stealing and then selling or publishing personally identifiable information (PII).
Key Features:
- Blocks ransomware encryption
- Protects sensitive data
- Isolates USB devices
- Scans emails
Why do we recommend it?
ManageEngine DataSecurity Plus is a very large package that is actually four modules in one. Each module addresses a different type of threat. The system is a software package for Windows Server and if you buy multiple units in the suit, they are all bundled into the same installer.
DataSecurity Plus locates and categorizes sensitive data and then protects it. The system implements file integrity monitoring, which alerts on unauthorized changes to files or unauthorized movement. The service monitors emails and USB devices to block downloads and prevent data disclosure.
The security service protects Windows systems, which are the targets for Jigsaw and most other ransomware. The package presents options to administrators to set up automated responses to detected attacks.
Who is it recommended for?
This package protects sensitive data, so you will be more likely to choose DataSecurity Plus if your system handles PII or PHI. There is a Free edition of this package but it doesn’t include the file integrity monitoring and file change notification features of the paid packages and you need those for ransomware protection.
Pros:
- Provides a detailed account of file access, allowing sysadmin to understand the context of the file change
- The platform can track access trends over time, allowing for better malicious behavior detection
- Supports built-in compliance reporting for popular standards such as HIPAA, PCI DSS, and FISMA
- Can integrate with numerous helpdesk solutions, notification platforms, and backup systems
Cons:
- Requires a sizable time investment to fully explore all the platforms features and tools
The software for ManageEngine DataSecurity Plus installs on Windows Server, and it is available for a 30-day free trial.
Jigsaw Ransomware FAQs
What does Jigsaw ransomware do?
Jigsaw ransomware implements file encryption. Although Encryption is often used to block unauthorized access, when an outsider encrypts your files, it prevents authorized access. To motivate victims to pay the ransom quickly, Jigsaw periodically deletes files. The best protection against Jigsaw lies in backing up your field regularly. With this process in place, you just need to kill and delete the Jigsaw program, remove the encrypted files, and replace them with the original files from the backup.
Who created the Jigsaw ransomware?
According to the U.S. Attorney’s Office for the Eastern District of New York, Jigsaw 2 was created by Moises Luis Zagala Gonzalez. The 55-year-old Venezuelan cardiologist was charged in May 2022 as the creator of a number of malware strains, which includes Jigsaw’s 2nd edition and Thanos ransomware.
What happens if you pay the ransomware?
It is a bad idea to pay the ransom for a ransomware attack. It is far better to prepare to defend your data from an attack by creating regular backups. Many ransomware strains don’t even have the mechanism to restore the damaged files.






Hey, Stephen Cooper.
Last year I was doing a ransomware project on my VM labs, to learn and educate my self.
It turns out that the VM was infected with JigSaw/BitcoinBlackmailer.
One of the things I do was to search internet and get some knowledge about it, and how to stop it.
Well in my opinion you wrote an excellent article, not only about what happened in the past and how things were done, but also about what could happen in the future and how to be ready in that case.
I really like the story while reading it. Thanks.