
On March 31, the Chinese government pushed out an update to the Great Firewall blackholing hundreds of VPN servers with the goal of stifling internet freedom and privacy. Its system of high-tech spying is pervasive; when you’re online in China, someone is always watching. VPNs have never been more important to expats and citizens, and they’re being systematically detected and shut down by the government in really advanced and upsetting ways.
Large scale testing of VPNs in China is challenging, not least because someone caught inside the country running these tests would be at the mercy of Chinese authorities. China represents one of the biggest markets for VPN use, but there is a lack of reliable information on which VPNs actually work behind the Great Firewall.
This article goes in to a lot of technical detail. If you just want a quick overview of which VPN to use, head over to our best VPN for China round-up.
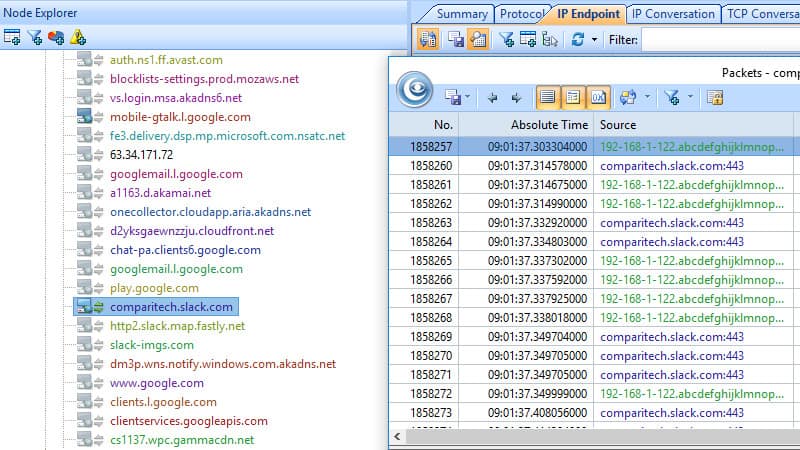
To mitigate the ethical issues of employing a tester within China, Comparitech rented a server in Shenzhen and commissioned me to test 59 VPN providers after the latest government purge. I checked each app to make sure I could connect to banned websites and get around regional content bans.
In order to supplement our technical testing, we also brought our specialist on internet privacy in China and Comparitech.com editor, Paul Bischoff. Paul, who lived in China as a journalist for several years, summed up the situation in China like this, “As the world’s most advanced surveillance state, the Chinese government does not like online anonymity or privacy. Any part of the internet beyond Chinese authorities’ control that allows private communication or the spread of information by users is blocked by the Great Firewall.”
“Likewise, any popular online content that disparages China or the Communist Party is promptly censored. VPN services, which can bypass these restrictions, are largely blocked as well, but a handful have the resources and knowledge to give users reliable access to the free and open internet.”
Internet privacy in China
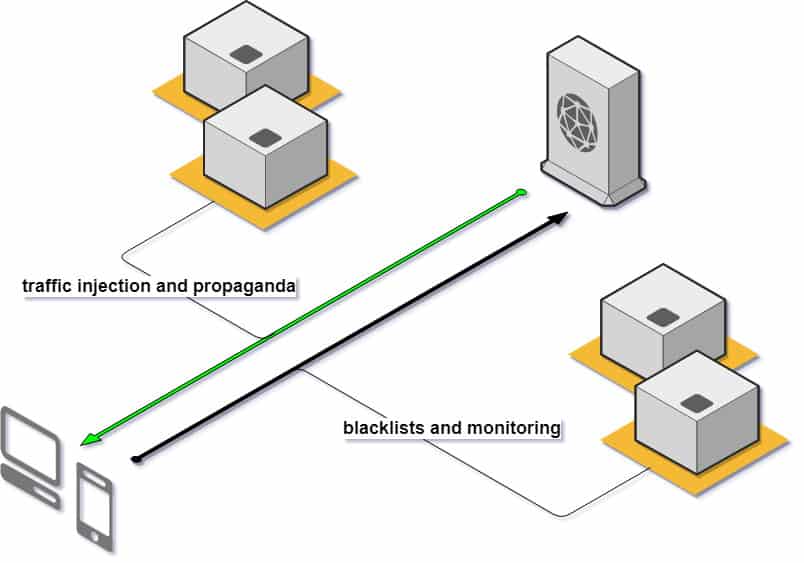
Every bit of internet traffic going in or out of China is wiretapped. Seven backbone connections serve the country, and each connection is being monitored, logged, checked, and double-checked by farms full of servers for snooping in the name of the Party.
What they’ve built is a nationwide stateful firewall– a big, powerful tool for keeping track of each and every session created by each and every device across the entire country.
It’s tracking you, and it’s smart enough to know whether you’re having counter-revolutionary thoughts and shut them down on the fly. Entire sections of the web are blackholed. Censorship is so pervasive that people familiar with the Great Firewall often make a distinction between “Chinese internet”—a walled garden of state-monitored website, apps, and services—and “rest-of-world (RoW) internet”.
There is no such thing as internet privacy or freedom in China unless you take steps to protect yourself.
Comparitech VPN testing in China
“VPNs remain the primary means of bypassing the Great Firewall and accessing censored content on the web. However, not all VPNs are equal, and a distinct few can reliably get through. The demand for these VPNs is high”, according to Paul.
In order to be perfectly fair about things, I developed an automated testing suite with UiPath and added all 60 VPN providers. I confirmed they all connected in America and ran through my automated tests a final time. Then I copied everything to Shenzhen and got started.

Each provider connects, opens a command prompt, and the test logs ping results to Facebook, Twitter, Twitch, Reddit, Instagram, and Wikipedia. It logs two DNS lookups, hopefully returning American servers for YouTube and Netflix. UiPath takes a final screenshot, then disconnects before starting on the next provider.
What I ended up with was detailed connection data on 60 VPN providers within China, using their Windows apps and preferred high-security settings. The test pits every provider’s recommended configuration against China’s best defenses.
The best VPN providers for China
After testing, I found pretty mixed results. Most VPN providers can’t beat the Great Firewall; their existing servers have been blackholed and their connections aren’t secure enough to avoid Chinese state detection of new servers. Standard OpenVPN connections, and even dedicated L2TP over IPSec servers, are being detected and shut down.
Every VPN provider marked Up in China connected successfully in at least 6 of the 7 rounds of testing I ran, each time to a different gateway.
| Name | Status | Notes |
|---|---|---|
| AirVPN | DOWN | |
| AnonymousVPN | DOWN | |
| Astrill | UP | |
| Avast Secureline VPN | DOWN | |
| Avira Phantom | DOWN | |
| Betternet | DOWN | |
| BlackVPN | DOWN | |
| BTGuard | DOWN | |
| Buffered | DOWN | Buffered has previously been reported as up, but I could not get a connection after the March 31 update |
| BulletVPN | DOWN | |
| CactusVPN | DOWN | |
| CyberGhost | DOWN | |
| EarthVPN | DOWN | |
| Express | UP | |
| F-Secure Freedom | DOWN | |
| FrootVPN | DOWN | |
| Goose | DOWN | |
| Hide.me | DOWN | |
| HideMyAss | DOWN | Freedom mode tested |
| Hotspot Shield | UP | |
| ibVPN | UP | |
| IPVanish | DOWN | |
| Ironsocket | DOWN | |
| Ivacy | UP | |
| Kaspersky Secure Connection | DOWN | |
| Keenow | DOWN | |
| Le VPN | DOWN | |
| LiquidVPN | DOWN | |
| McAfee Safe Connect | DOWN | |
| Mullvad | DOWN | |
| NordVPN | UP | Up using an obfuscated server |
| Norton WiFi Privacy | DOWN | |
| OneVPN | DOWN | |
| PandaPow | DOWN | |
| Perfect Privacy | DOWN | |
| Private Internet Access | UP | Up and running despite some initial issues with DNS |
| Private Tunnel | DOWN | |
| PrivateVPN | DOWN | |
| ProtonVPN | UP | Up but many individual servers are down |
| ProXPN | DOWN | |
| PureVPN | UP | Works in both standard and Internet Freedom mode, IF mode recommended |
| SaferVPN | UP | |
| SlickVPN | DOWN | |
| Speedify | DOWN | |
| StrongVPN | DOWN | |
| SurfEasy | DOWN | |
| SurfShark | UP | NoBorders mode is required to connect in China, double-check it's turned on |
| TigerVPN | DOWN | |
| TorGuard | UP | |
| TunnelBear | UP | |
| Unotelly | DOWN | |
| VPNBook | DOWN | |
| VPN Tunnel | DOWN | |
| VPN Unlimited | DOWN | |
| VPNArea | DOWN | |
| Vypr | DOWN | |
| Windscribe | UP | Most servers are accessible in China |
| WorldVPN | DOWN | |
| Zenmate | DOWN |
The VPN providers who fared best all used additional encryption over and above what OpenVPN traditionally offers. More than one provider made use of the OpenVPN scramble extension that obfuscates packet headers in order to avoid detection by automated network defense systems.
When you’re shopping for a VPN in China, that extra layer of security isn’t really optional. It’s the key to a reliable connection that will beat Party wiretapping.
Why did so many fail?
A lot of VPN providers failed, and there are a handful of reasons why. All of them boil down to a provider being detected by Chinese anti-privacy measures at the firewall, then blackholed by an established system of government censorship.
Most VPN servers are blackholed
China’s first line of defense is, and always will be, blackholing sites and services via border gateway protocol. BGP was designed to allow routers to communicate efficiently and tell other routers which resources are and aren’t available.
Changes made in China’s biggest state-run routers propagate automatically via BGP, which puts the Chinese internet authority in every ISP in the country. The state enforces their blacklist by using the technology exactly as intended, just with the worst possible motivation. Sites disappear across the entire country when China updates their routers.
Most VPN providers have at least one or two servers blackholed. VPNArea, Keenow, CactusVPN, and many others who failed have all of their servers blackholed; you just can’t connect in China.
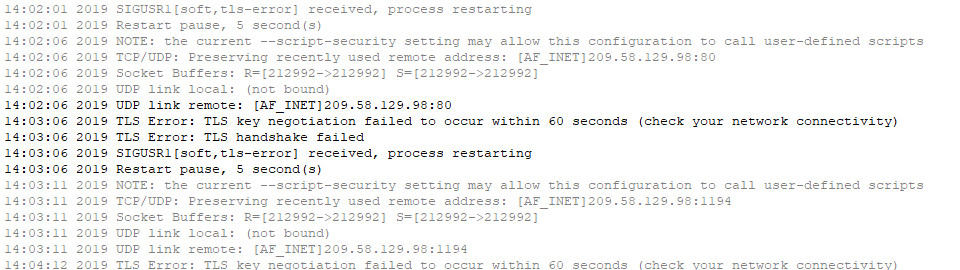
OpenVPN is under attack
OpenVPN is the most popular protocol for establishing private networks, in China and everywhere else. The government can’t shut it down completely because of its utility in enterprise networks. But they’re getting smarter and faster at finding unauthorized OpenVPN traffic.
When I asked Paul about China’s efforts against OpenVPN, he said, “In my experience, you can set up an OpenVPN server outside of China and connect to it for a few hours if you’re lucky, but it inevitably gets blocked within a day or two.”
Proton is a great example of a strong VPN provider that just hasn’t been able to keep up with China’s evolving defenses. They use outdated methods like routing OpenVPN traffic through port 443, intended to disguise OpenVPN as HTTPS traffic, which have proven ineffective against an adapting China.
L2TP over IPSec is pretty well cracked
The Chinese government has had OpenVPN servers in its sights for years, but for a long time using L2TP over IPSec in place of OpenVPN worked pretty well. That’s no longer the case; I saw firsthand as the Great Firewall intercepted two of my L2TP over IPSec connections and shut them down with TCP RST floods.
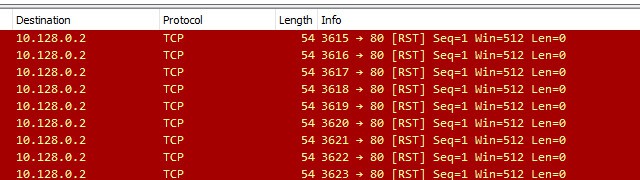
The March 31 update proves to me L2TP over IPSec is no longer secure enough to get past the Great Firewall. Its strength and weakness both is a reliance on modular, external encryption for security. Some modules provide weaker encryption than others and seem to be cracked.
Depending on each vendor’s configuration, L2TP over IPSec may be a long-term solution for VPN access in China, but it varies a lot case-by-case.
It’s only a matter of time for ShadowSOCKS
ShadowSOCKS is a VPN-like service designed in China to circumvent the state’s control of the internet. Some providers recommend using it instead of a VPN, because the government has not yet put resources into widespread detection and shutdown of ShadowSOCKS servers.
Unfortunately, Chinese internet policy over the past decade leads me to believe it’s only a matter of time until ShadowSOCKS is on the chopping block. Evading detection by the GFW is critical; even though the protocol was designed to defeat exactly the sort of DPI China uses to identify and blackhole servers, it was designed in 2012.
There is a bright spot for ShadowSOCKS, though. There are already modules that can scramble its traffic similar to how the most successful VPN providers in China do today.
Limitations
Our tests were performed on a Windows Server instance and not a consumer desktop. We only ran tests from a single server, so these results represent a specific internet service provider and geographic region. Other internet service providers and other regions may have more or less strict censorship in place.
Testing VPNs in China is a moving target. VPN services and the internet itself is subject to availability. A VPN provider that works in the country today may not work tomorrow. Share your experiences in the comments.
VPNs can still bypass censorship and maintain privacy in China
In order to take basic steps to protect yourself online in China, you need a VPN. But the government is getting better and better at detecting them. We saw VPNs that succeeded at our testing use next-generation obfuscation to hide their servers from the internet censors’ blackhole.
High encryption isn’t enough; the packet headers themselves need to be protected against China’s stateful firewall and DPI systems. Unless more VPN providers do a better job of hiding themselves, they’ll find themselves unable to compete in the country.
“Not only has the Great Firewall gotten better at detecting VPNs in use, China has also taken steps to block VPN websites and app store listings for VPNs. Domestic VPN providers that offer access to the outside world have been shut down. It’s never been more difficult to use a VPN in China than it is today,” Bischoff says.







PrivateVPN was working on 2 May 2019 when I was in China, but only with stealth mode turned on.
I’ve successfully used Witopia for almost 3 years. Any comments on that one?
Sorry Tom, it didn’t make it into this round of testing but I’ve made a note. Thanks for the heads up!
I’m surprised that you’ve “downed” Strong as I’ve been using it successfully in China for about two years now and I’m soon to renew that subscription. True, there were some difficulties last year, but it was overcome. Anyway, good article still.
Hi John, thanks for reading. You’re right that Strong VPN was a borderline case, and they actually incorporate some really useful technology to evade detection. But ultimately I wasn’t able to connect successfully often enough to report them online.
We did have some pretty high standards here. I wanted 6 or 7 successful connections out of 7 attempts, each to a different gateway, to report a VPN provider online. That means you can really count on the providers we reported up. But it also means failing some contenders like Strong VPN.
Well, this article is one of the best I’ve seen this year, everything is on the plate, good job! Tried NordVPN and ExpressVPN myself, both up and working, just as mentioned
Thanks for the VPN tests. I hope you can take a look into Shadowsocks-libev, ShadowsocksR, V2Ray, Tor, and Wireguards next time if you like. Maybe even give a tutorial on how to set them up yourself.
What about SSH tunnels? Are they blocked too?
This. But not a SOCKS SSH tunnel to my own server–what about tunning OpenVPN through SSH for one of the VPN providers listed above?
For example, you listed AirVPN as “DOWN” without any notes, but AirVPN allows you to (a) setup an ssh tunnel to their servers and then connect to their openvpn server _through_ that ssh connection. Did you give that a try with AirVPN or any of the other service providers?
Similarly, AirVPN allows you to (b) run an stunnel to establish a normal TLS connection to their server over 443, then connect to their openvpn server _through_ that ssh connection as well. Did you have a chance to test tunneling the openvpn connection through an stunnel connection to the vpn providers from within China?
Hi Michael these are great questions!! I can tell you have a super solid grasp of ways to hack around and play with these connections and turn maybe a borderline provider into a reliable one.
But here’s the thing, you’re being blackholed at the router. At every router in fact, but your in-country ISP gateway is probably the relevant one here. You don’t have an exit to tunnel to because AirVPNs servers aren’t valid destinations in the routing table. SSH, SOCKS, Wireguard, there’s a million solutions and none of them work because the remote gateway is unreachable through every means. It’s not just DNS, the IP address doesn’t exist until you’re encrypted and having your traffic routed by someone sane.
If you’ve ever been left hanging for a high five, you ain’t seen nothing until you tried to initiate a handshake from Shenzhen
That’s why it’s so important to hide your remote gateway! It’s why my favorite provider who I didn’t name maintains an entirely separate list of servers that have only ever passed obfuscated traffic. Keeps them off of blacklists, and being blacklisted in China is the only thing that really matters. Because once you’re on, you don’t get off, and your servers become completely inaccessible from within the country.
Hey Aaron, thanks for the response.
I haven’t been to China, but I assumed that these VPN providers would churn their entry IPs constantly out of necessity of staying off blacklists. Is this not common practice for VPN providers? Do you know of VPN providers that explicitly & constantly migrate their service to different IP addresses by design at some interval to avoid blacklisting?
One solution would be to use “entry” IPs on disposable VPS boxes that merely pass the traffic back to dedicated openvpn servers. Even if the dedicated servers are blocked, it doesn’t matter; the connection is initiated from the disposable VPS box’s IP. This sort of idea was experimented by cryptostorm’s now-deprecated voodoo network as described here:
* https://github.com/cryptostorm/voodoo.network
Do you know of any VPN providers that employ some sort of ephemeral entry VPS nodes / IP Addresses (which could hop around in aws or gcp to make blocking them in China cause economic damage to their country–as we saw happen to Russia when they tried to block Telegram in April 2018)
Hey, thanks for reading. I’ve got a companion piece to this coming up where I tear into the GFW more and look at non-VPN services and some of their countermeasures. Short answer is SSH tunnels are functional, but unless you’ve spent some time looking at your encryption I don’t think you can necessarily count on it.
SSH is arguably even more infrastructure-critical than VPNs, so getting it in and out of data centers is not a problem. But I can guarantee that some State network appliance is doing its best to dig into packet headers and snoop as hard as it can at the data stream.
Outside of data centers, it really depends on the ISP. It’s common for ISPs and employers to introduce additional levels of monitoring and firewalling at the gateway, long before your traffic hits the GFW.