Steganography is an ancient practice that involves hiding messages and data. From its humble origins that involved physically hiding communications and using invisible inks, it has now moved into the digital realm, allowing people to slip critical information into seemingly mundane files.
It may not be as popular as its older brother cryptography, but steganography still has important applications. So let’s jump in and discuss what steganography is, the history behind it, how it differs from cryptography, its major use cases, and how it can be detected.
What is steganography?
To put it simply, steganography is the study and practice of concealing information. It can be done either physically or digitally, with techniques ranging from blinking in Morse code to hiding data in .mp3 files.
The history of steganography
The first written case of steganography is found in Histories by Herodotus. He writes that it happened during the Ionian Revolt, an uprising of some Greek cities against Persian rule at around 500 BC. Histiaeus, the ruler of Miletus was away from his city, acting as an adviser to the Persian king.
He wanted to go back to Miletus, which was under the control of his son-in-law, Aristagoras, so he planned to stage a revolt in Ionia as a pretext for his return. This is where the steganography comes in: He shaved the head of one of his slaves and tattooed a message on his scalp.
Histiaeus then waited for the slave’s hair to grow back and hide the message, then sent him to Aristagoras with instructions to shave the slave’s head once more and read the message. The concealed text told him to rise up against the Persian rule, which kicked-off the uprising against their conquerors.
Herodotus tells another story about steganography that occurred several years later, when the Spartan king Demaratus sent a seemingly blank wax tablet back to Sparta. Hidden beneath the wax was a message that warned the Spartans of Xerxes’ planned invasion.
Herodotus is known for his tall tales, so we can’t be sure of how truthful these stories are, but they’re the earliest records of steganography we have.
It wasn’t long before more sophisticated forms of steganography were recorded. In the 4th century BC, Aeneas Tacticus made mention of a hole punching technique. Philo of Byzantium was the first to discuss invisible inks, writing about them in the third century BC. His recipe used gall nuts to write text and a copper sulfate solution to reveal it.
The term steganography was first used in a book called Steganographia by Johannes Trithemius. The word combined the Greek steganos, which means concealed, with graphein, which means writing.
Steganographia was a clever book that was purportedly about magic and the occult, but used cryptography and steganography to hide its real subject matter, which centered around cryptography and steganography.
Steganographia was followed up by Polygraphia, which was first published after Trithemius’ death in 1518. This was a more straightforward book about steganography and its practice.
Another key development in steganography came in 1605, when Francis Bacon devised Bacon’s cipher. This technique used two different typefaces to code a secret message into a seemingly innocent text.
Microdots were first developed in the latter half of the 19th century, but they weren’t used heavily for steganography until World War I. They involve shrinking a message or image down to the size of a dot, which allows people to communicate and pass on information without their adversaries knowing.
There have been a wide range of other steganographic developments and techniques over the years. Steganography continues to be practiced to this day, with low tech versions often used by prison gangs, and digital methods harnessed to hide data in pictures, sound files and other media.
Steganography vs cryptography
Steganography is focused on hiding the presence of information, while cryptography is more concerned with making sure that information can’t be accessed. When steganography is used properly, no one – apart from the intended recipients – should be able to tell that there is any hidden communication taking place. This makes it a useful technique for situations where obvious contact is unsafe.
In contrast, cryptography tends to be used in situations where the participants aren’t concerned if anyone finds out that they are communicating, but they need the message itself to be hidden and inaccessible to third parties.
Let’s go through some examples to understand the differences. If you were a political activist who’s been imprisoned and you need to communicate with your organization, the logistics can be challenging. The authorities may monitor everything going in and out of your cell, so you would probably have to hide any communication that takes place.
In this kind of situation, steganography would be a good choice. It may be challenging with the resources you have at hand, but you could write a plain-sounding letter with a hidden message concealed with different font types or other steganographic techniques.
Alternatively, let’s say you’re a diplomat discussing secret details with your home country. It’s normal for diplomats to talk with officials from their own nation so the communications themselves don’t raise any suspicions. However, since the content of the conversation is top secret, the diplomat may want to use cryptography and talk over an encrypted line.
If spies or attackers try to intercept the conversation, they will only have access to the ciphertext, and not what the two parties are actually saying.
Let’s flip things over to examine the differences even further. If the political activist used cryptography to communicate with their organization, the authorities would most likely have intercepted it.
The officials would see the ciphertext and know that the activist was trying to send encoded messages, then they would most likely stop its delivery and interrogate the activist about it. This could end very badly, in beatings, torture, or even the activist’s death. That’s why steganography would be more suitable in such a scenario.
Conversely, diplomats are often monitored by their host countries. If a diplomat tried to send steganographically concealed messages back home, they could be intercepted, analyzed and the content may be uncovered. In this situation, cryptography is more suitable, because although interceptors will know communication is taking place, they won’t be able to find out what it concerns.
See also: Beginner’s guide to cryptography
Combining steganography & cryptography
While these two processes are often performed separately, cybersecurity analysts can also be combined together to gain the advantages that come from both fields. If you wanted to hide the fact that communication was taking place, but also protect the message in case it was discovered, you could first encrypt it and then conceal it with steganography.
As an example, let’s say you want to hide the message “I’m going home” with a simple Caesar cipher and invisible ink. Using the cipher, you could shift each character to the one that follows it in the alphabet, giving you a ciphertext of:
J’n hpjoh ipnf
Now that you have your cipher text, you can write it down on your piece of paper with lemon juice or whatever kind of invisible ink you have at hand. As long as your recipient knows where the message will be, how to reveal it (heat, in this case) and how to decrypt it, they will be able to access the covert communication.
If anyone intercepts the message but can’t detect the invisible ink, then they will not know that any communication has taken place. If they do know that a message is there but can’t crack the code, then the message itself will still be secure, but the interceptor will know that something has been sent. They won’t be able to access the contents of the message unless they can crack the code.
If you wanted to increase the security of the communications, you could use more sophisticated encryption and steganography methods, such as AES and bit plane complexity segmentation (BPCS), respectively.
The uses of steganography
Steganography has a number of surprising applications, aside from the obvious one of hiding data and messages. Hackers use it to conceal malicious code in malware attacks. Printers use steganography as well, hiding imperceptible yellow dots that identify which printer created a document and at what time. Steganographic techniques are also frequently used in watermarking and fingerprinting to prove ownership and copyright.
The limitations of steganography
Steganography is a useful practice, but it does have a number of limitations. There are two key factors that are often in competition – the first is how obvious and easy the hidden data is to detect (whether by human perception or other forms of analysis), while the second is how much data can be hidden in a given file or piece of communication.
The higher the percentage of data someone tries to conceal, the easier it is to spot. How much data you can safely include in a given file will depend on the steganographic technique, risk level, and amount of scrutiny expected.
If data is hidden in images, it’s still quite hard for the human eye to detect anomalies when 20 percent of the data has been replaced, assuming the information has been well hidden. At lower percentages, the image will look essentially the same. As more data is packed in, the quality starts to deteriorate and you may even be able to see elements of the hidden picture.
If you’re having trouble getting your head around what it looks like, check out the examples starting at page three, and then again from page 12 in this paper written by John Ortiz for Black Hat.
If we use 20 percent as a benchmark, then it’s best to have a file that’s at least five times the size of the data you want to conceal. With this technique at a low risk level, you would want a five gigabyte image file for each gigabyte that you want to hide.
This makes steganography relatively inefficient. If your goal is to keep data secure and confidential, rather than to obscure the fact that communication is taking place, cryptography is generally a better option.
On top of the efficiency problem, the recipient also needs to know where and how information has been hidden so that they can access it. This generally means that you will need access to a secure channel so that you can discuss these details without any attackers intercepting them. Because secure channels are often difficult to come by, particularly in situations that require steganography in the first place, this can be a difficult problem to surmount.
Finally, when trying to keep information hidden, it’s important to consider Kerckhoffs’ principle:
“A cryptosystem should be secure even if everything about the system, except the key, is public knowledge.”
The central point is that it is unwise to use a system where the only protection is the enemy’s lack of awareness – they may stumble upon or deduce that there is hidden data, then figure out ways to extract it.
It depends on the situation, but if keeping information secure and inaccessible to unauthorized parties is of the utmost importance, then data should be encrypted with a private key before steganographic techniques are applied.
The different types of steganography
There are too many types of steganography to cover each one, so we will stick to the more commonly used and interesting forms, giving examples of how they are used.
Physical steganography
Steganography was developed well before computers, so there are a range of non-digital steganography techniques that we can use to hide information.
Invisible ink
Throughout history, invisible ink has been one of the most common steganographic practices. It works under the principle that a message can be written without leaving any visible marks, only to be revealed later after a certain treatment is applied.
A wide range of substances can be used as invisible inks. Some of these include lemon juice, cola, wine, vinegar, milk, and soapy water, all of which can be made visible by heat. Laundry detergents, sunscreen, soap and saliva are also invisible inks, but they are revealed by ultraviolet light instead.
There are also a number of combinations where the first ingredient is used to write and the second causes a chemical reaction that makes the image visible. These include starch and iodine, iron sulfate and sodium carbonate, vinegar and red cabbage water, phenolphthalein and ammonia fumes, as well as salt and silver nitrate.
Invisible ink can only be relied on when adversaries don’t suspect that it’s been used. If messages are already being screened, it may not be the best technique, because it’s relatively easy to uncover the messages. Likewise, if the writing process leaves behind any signs, such as a different texture, scratch marks or an altered sheen, the invisible ink might be detected by the enemy.
Invisible ink was a critical part of George Washington’s communication process as he worked to overthrow the British. He created a spy group in 1778, and messages would frequently be sent between the members. They would often write a legitimate shopping list with an invisible ink message hidden underneath, just in case the note was intercepted.
They used an ink developed by Dr. James Jay. Washington often referred to it as ‘medicine’ in his letters as a cover. The letters were also frequently written in code, just in case the British came across one of the messages. Combining steganography with encryption added another layer of protection.
Null ciphers
Null ciphers hide their real messages amid seemingly normal text, using a range of different techniques. Common examples include creating a mundane text, where every nth word, or even letter, is part of the secret message.
For example, if we use a null cipher where every fifth word is our real message, we can take a message like:
I don’t want any dogs because they stink and are not known for being great.
And find the hidden text:
“dogs are great”
Alternatively, we can code something into the first letter of every third word:
If you hate being so anxious, buy a puppy, or a pony, it’ll help you.
Contains a secret message of:
“happy”
You can create and use null ciphers according to just about any scheme you can think of, as long as your recipient knows the technique. However, creating hidden messages in a way that doesn’t raise suspicion can be a very laborious and time-consuming process, so null ciphers aren’t the most efficient means of communicating in secret.
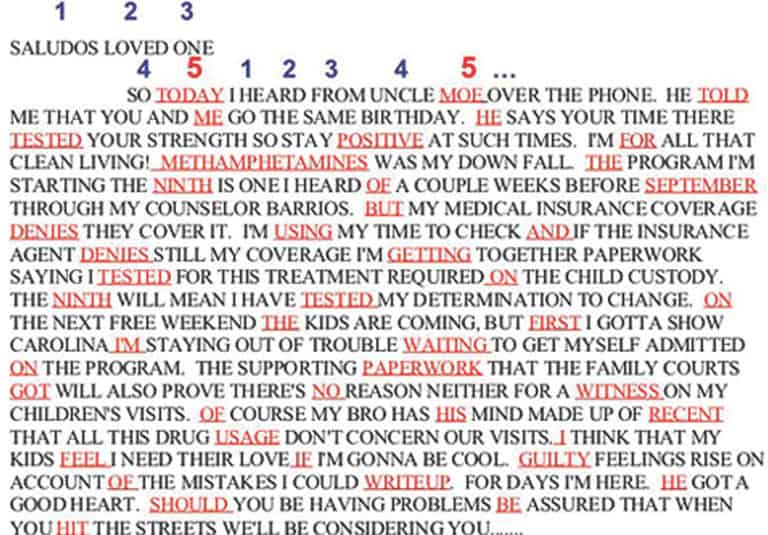
The FBI released this sample of a null cipher they intercepted from a prisoner:
The entire text makes the sender seem like he has a pretty turbulent family life, but on the surface the writer isn’t advocating anything criminal. When you read every fifth word, which the FBI has thankfully highlighted for us, it becomes much more sinister.
It closes with “IF GUILTY OF WRITEUP, HE SHOULD BE HIT.” In other words, Moe should be murdered if he is convicted. Fortunately for Moe, this prisoner’s steganography wasn’t good enough and the message was decoded by the FBI.
Bacon’s cipher
Another early steganography scheme was Bacon’s cipher, invented by the philosopher and politician, Francis Bacon, in the seventeenth century. It was an interesting development, because it hides the secret message in the format of the text rather than its content.
Bacon’s cipher is a steganographic technique rather than a cryptographic one because the message is hidden by seemingly normal text, rather than appearing as a jumble of ciphertext in plain sight.
Look at the image below as an example:
The Baconian Bilateral Cipher by New York Public Library licensed under CC0.
As you can see, in this example are two different font styles for both lower and upper case letters. To hide a message using Bacon’s cipher, an innocent message is written using a combination of the two different styles. The secret message is formed by blocks of five letters. The particular arrangement of the fonts in each group of five letters represents a single letter of the hidden message.
It may be difficult to see in the image, but the poem in the top left corner “Have more than thou showest, speak lest than thou knoweth…” actually contains a secret message. To uncover the text hidden by Bacon’s cipher, the poem must first be broken into blocks of five letters:
Havem
oreth
antho
ushow
estSp, etc.
The next step is to compare the font style of each letter and decide whether it fits into the first group, “a”, or the second one, “b”. The upper and lower case letters of our first group, Havem”, are each written in font “a”. According to the key (which is in tiny print at the bottom left), “aaaaa” translates to the letter “A”.
If we follow the same process with the second group of five letters, “oreth”, the first is written in style “a”, the second, style “b”, the third, “style “a”, the fourth, style “b”, and the final, style “a”. A run of “ababa” translates to an “L” according to the code.
If we translate the entire poem in this way, it reveals “ALL THAT GLISTERS IS NOT GOLD”. As you can see, it’s a relatively novel process for hiding messages. If an adversary isn’t aware of Bacon’s cipher, it’s quite simple to slip a secret message past them.
Bacon’s cipher is really just a simple binary system, and it’s not restricted to font types. You could hide a message with an a/b system by varying the spacing, the size of the letters, writing them a little above or below the line, or with other subtle manipulations.
A different encoding method could be used as well, making it even more difficult for your enemies to uncover the hidden text. Instead of having “aaaaa” represent “A”, you could have “aababababbabaaaa” or some other string stand in for “A” instead. Obviously, this is longer and far less efficient, and you will also have to make sure that your recipient knows about the new encoding method.
Bacon’s cipher has been adopted to hide information numerous times over the years. In recent times, the notorious white supremacist gang, the Aryan Brotherhood, used it to encode lists of gang members and order hits on its enemies.
Microdots
If you want to hide messages or other information, one of the best techniques is to make it invisible, or at least as close as possible. This is the school of thought behind microdots. They were first developed in the late 19th century and improved upon during the 20th.
Photographic techniques can shrink down images or text to a tiny fraction of the original size. By 1925, a method developed by Emanuel Goldberg was so sophisticated that a regular printed page could be shrunk down to one hundredth of a square millimeter.
Microdots allowed people to hide large amounts of information without any obvious trace. Spies could hide them on their person, send them through the mail, or keep information stored on them. Unless an adversary is already suspicious, microdots are almost impossible to detect, due to their tiny nature.
They were used heavily throughout World War I, World War II and the Cold War. One key incident involved the Serbian triple agent Duško Popov. He was a wealthy man who had infiltrated the German military intelligence service, the Abwehr.
The Nazis fed him information and, following the British raid on Italy’s Taranto naval base, they inferred that the Japanese were interested in how the attack took place. His handlers sent him a message via a microdot, instructing him to go to the US and report back on Pearl Harbor’s defenses for the Japanese.
While Popov was in the US, he warned US officials of the enemy’s interest in Pearl Harbor, although it seems that this information never made it to the military. This lapse led to the US being blindsided by the Pearl Harbor attack.
There isn’t much information regarding if and how microdots are used at the moment, although this is to be expected considering their clandestine nature. Due to the proliferation of digital communications and other techniques, it’s unlikely that microdots are still so heavily used, although there could be niche applications.
Printer steganography
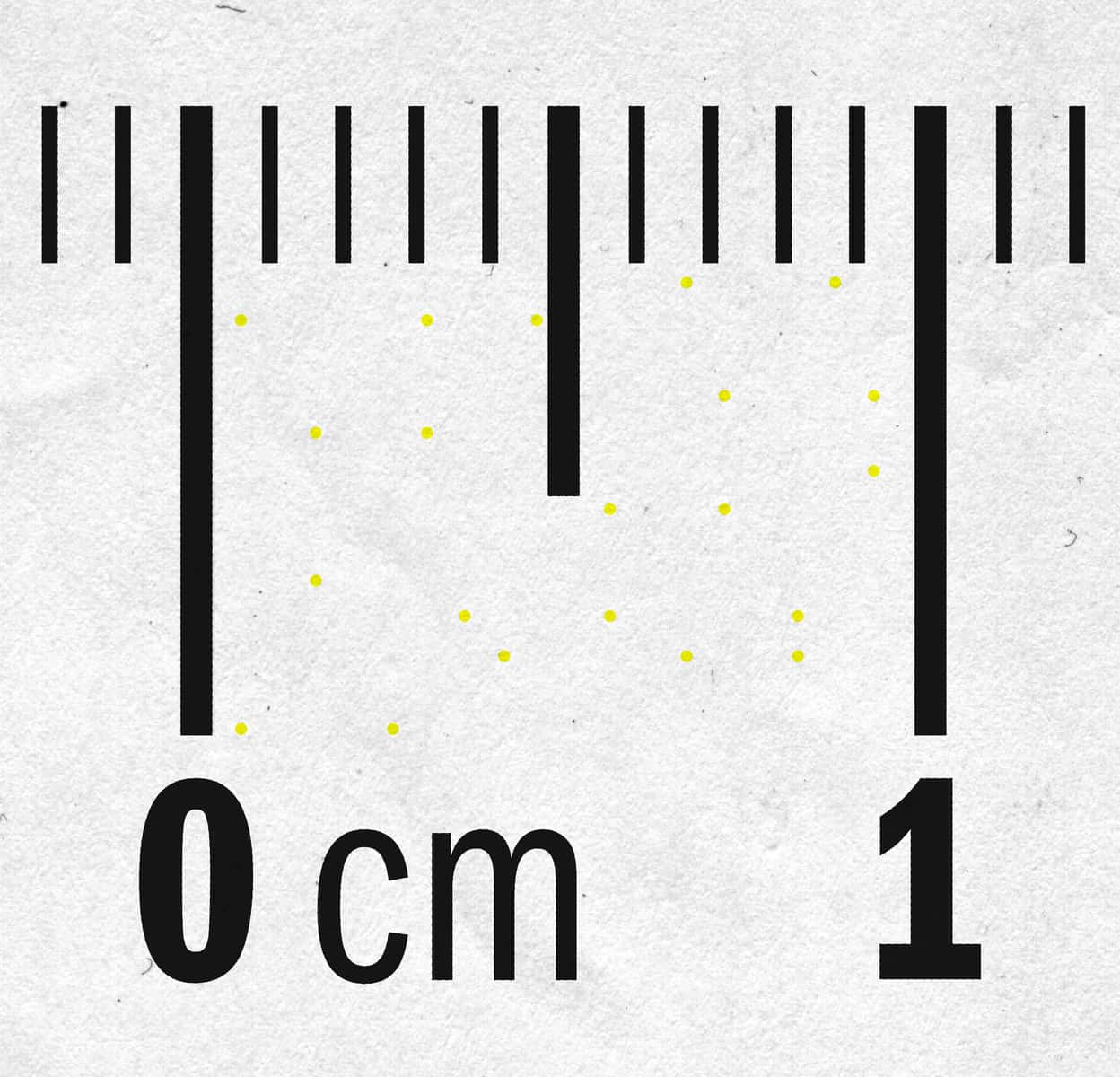
An example of the code left behind by printers. Printer Steganography by Parhamr licensed under CC0.
Since the 1980s, various printer manufacturers have programmed their machines to print out a series of almost imperceptible yellow dots on every single page. Each dot is only a tenth of a millimeter in size, and their arrangement is coded to display the printer’s serial number, as well as its date and time.
This information is repeated again and again across the page, so that the information can be recovered even if only a fraction of a page is found, or if the printed code is damaged due to printer error, moisture, or other problems.
This steganographic practice is ostensibly used to crack down on currency counterfeiters – if authorities seize the notes, they can figure out which machine they was printed by. It’s assumed that the dots are also used to track down the perpetrators of other crimes, with some speculating that the NSA whistleblower Reality Winner would have been caught using this method, had she not made other mistakes.
The secret dots weren’t made public until 2004, when an article revealed that Dutch authorities were using the codes to try and track down a gang that was counterfeiting train tickets.
There are a number of different coding schemes. Most big printer brands have been confirmed to use at least one of them. At this stage, researchers from the EFF aren’t sure if every printer model secretly hides some kind of information that can be used to trace when and where a document was printed. Because of this, it’s considered safest to assume that every printer does leaves a trace.
In 2018, researchers from the University of Dresden released a program that adds extra yellow dots, scrambling the code. This prevents anyone from being able to trace when and where a document was printed. The software was developed to help whistleblowers and other activists retain their anonymity.
The software has some limitations, including that it must be used with a printer that’s programmed with the same yellow dot encoding technique. Because there are a range of other identification codes in use, there is still a chance that a person’s printer leaves other markings on the page which can be used to identify them.
Digital steganography
Like just about everything else in our lives, steganography has made its way into the digital realm. It’s possible to hide information in different file types, in a range of online venues, and even in places you’d never suspect, such as by varying the timing between data packets being sent over a network protocol.
Media files are some of the most popular places to hide information, because their large size means that more secret data can be stuffed inside them without raising suspicion. There are three separate ways that information can be hidden in files:
- By adding it to the file, such as in unused header space.
- By substituting part of the information within the file. One of the most common ways to do this is by altering the Least Significant Bit (LSB). In sound files, audio files and other files, the last bits of information in a byte aren’t necessarily as important as the beginning ones. For example, 10010010 might be a shade of blue. If we only change the last two bits to 10010001, it could be a shade of blue that’s almost exactly the same. This means we can hide our secret data in the last two bits of every single pixel in a picture, without noticeably changing the image. If we change the first bits, it would alter it significantly.
- By creating a new seemingly benign file, which is actually just a cover for the steganographic text.
Video steganography
Videos are relatively large files, so they can hide more data than most alternatives. Some of the most common techniques include a variety of different schemes for substituting the least significant bits (polynomial equations, hash-based, etc.). Alternatively, data can also be embedded into each frame, or filtering and masking data can be used as well. There are a range of video steganography programs available online.
One of the most interesting cases of video steganography was uncovered when the German authorities arrested a suspected al-Qaeda member in 2011. Officers searched the man and found a flash drive as well as memory cards in his underwear. Among the other files was a pornographic video called Kick Ass.
Because he was suspected of being involved in terrorism, the authorities investigated the video further to discover that steganographic techniques had been used to hide more than one hundred al-Qaeda documents. These included terrorist training manuals and plots for future attacks.
As un-Islamic as having pornography may seem, it’s actually quite a clever scheme. When the authorities find encrypted files, their suspicions are often raised, wondering why the file was encrypted in the first place.
If they were to compel a suspect to hand over their key and discovered that the target had encrypted children’s TV shows, it would seem fishy. The authorities would know something is up and be more likely to inspect the data further and discover the hidden information.
Because pornography is generally taboo, particularly for Muslims, the authorities might view the content, then just wave the person off as a sexual deviant filled with shame, rather than inspecting the data further. Fortunately for the world, the German officials weren’t tricked.
Picture steganography
Data can be hidden in pictures with a variety of techniques. These include:
- Least significant bit – We discussed this earlier under the Digital steganography section.
- Bit plane complexity segmentation (BPCS) – This technique replaces complex data with hidden information in a way that isn’t perceptible to the human eye.
- High capacity hiding in JPEGs – This is essentially an adaptation of least significant bit that compensates for the compression involved in JPEG files.
In 2010 a Russian spy ring was busted by US authorities. As part of their communications process, they would encrypt data, use steganography to hide it in pictures, then post them on public websites. The communication technique was discovered after the suspect’s homes were raided and some of their computers were found to contain steganography software.
Steganography has also been used to steal intellectual property. In 2018 a GE engineer conspired with a business partner based in China to steal company secrets related to steam and gas turbines. At first, he just copied files to a flash drive. He was caught, and the company blocked USB ports and banned flash drives from being used.
Remarkably, he wasn’t fired, and was given another opportunity to steal files. He took data from 40 Matlab and Excel files, used steganography to hide it in a picture of a sunset, then emailed it to himself, before forwarding it on to his business partner. He was caught by GE, then charged with six counts of economic espionage.
In a worrying trend, steganography is also becoming more common among hackers. Security researchers from Trend Micro analyzed the efforts of a Twitter account that posted malicious memes in October 2018.
Once the malware was running on a device, it downloaded the memes from the Twitter account, then extracted a malicious command hidden inside them. It took a screenshot of the infected computer, and sent the information back to the attacker after it collected the control server details from Pastebin.
Audio steganography
Audio steganography also comes with a range of different methods. As with all kinds of steganography, it’s important for the techniques to be robust, to be able to carry a reasonable portion of hidden data, and for any changes to be as imperceptible as possible. Some of the most common techniques include:
- Least significant bit coding – Just like the other types of least significant bit that we mentioned, it’s possible to alter less important parts of the audio data without making any obvious differences to the way a file sounds.
- Echo hiding – Data can also be masked in an echo.
- Tone insertion – Since it’s hard to detect lower energy tones when they are near those that are much more powerful, these lower energy tones can be used to conceal data.
A Polish researcher used audio steganography in an interesting project. He took the song Rhythm is a Dancer by Snap! and then modified the tempo. When a beat was slowed down, it represented a dash in Morse code, and when a beat was sped up, it signified a dot. He used this system to spell out “steganography is a dancer!”
He then played the song to a mix of professional musicians and laymen. With a one percent tempo discrepancy, no one noticed that anything was amiss. It was only at around two percent that the professional musicians knew that something was up, and around three percent for everyone else.
His results show that it’s quite easy to hide information in dance songs without anyone noticing. Despite this, his method isn’t a particularly efficient way of communicating, because it only transmitted three words over a whole song.
Text
When it comes to text, there are many different ways to hide information. However, because text files are generally quite small, they aren’t particularly useful for sending large amounts of data. One simple technique involves opening Microsoft Word, typing out your secret message, then changing the text color to white.
Over the white background of your word processor, it’ll look like nothing’s there. You can then save it and send it to your co-conspirator, making sure that you instruct them over a secure channel on how to access the information.
Otherwise, they might be perplexed at why you keep sending them blank documents. This isn’t a very secure method, because anyone who intercepts the messages will become suspicious about why you are always sending blank documents. All they have to do is select the text and your plot is foiled.
spammimic offers another steganographic technique to communicate in secret. The website’s tool allows you to encode a message so that it looks like spam. Because we are so used to ignoring spam, a message like this could easily fly under the radar and allow you to communicate without being detected. The usefulness of the software is debatable, but at the very least, it shows that messages can be hidden in a wide range of ways – you just have to think outside the box.
Hiding data in plain site
The internet is incomprehensibly large, containing a wealth of strange and nonsensical information. This leaves a lot of opportunities to hide secret messages in public without raising any suspicions.
As long as two people aren’t already being closely monitored, they can easily post their communications to each other on popular or obscure websites without being caught. They just have to make sure that their actual intentions aren’t clear to any onlookers.
Just think of all of the absurd comments you have come across on forums or social media, and the thousands of blog posts that made absolutely no sense. We tend to either brush them off or read them for our own amusement, but never consider that there could be something more to them than lunacy.
The Intercept claims that even the NSA has been in on the practice, using its official Twitter account to communicate with Russian spies. In a clandestine operation, the Intercept reports that some of the participants leaked the details of NSA Tweets to Russian operatives before they were posted. According to the report, this acted as confirmation that they were in fact representatives of the NSA, and not just scammers.
Detecting steganography
Steganography can be incredibly difficult to detect, especially when there is no reason to be suspicious. In the online world, so much information passes before our eyes, that we simply can’t spare the time or effort to scrutinize every anomaly, let alone the things that appear legitimate.
This is what makes it so hard to talk about good steganography. All of the examples we’ve talked about have been failures, because they are now public knowledge. Techniques are actively being researched and the technology is improving, but its very nature makes it impossible to detect successful steganography in the wild.
There may also be a variety of techniques developed outside of the public sphere, by intelligence agencies, terrorist networks and criminals gangs. We really can’t know unless we come across examples of them.
Despite this, a lot of analytical tools we can be applied when we suspect that steganography is being used to hide messages. However, the right tool depends on which techniques concealed the data in the first place.
Detecting physical steganography
When it comes to invisible ink, the detection methods depend on what kind of invisible ink was used. If it has been done poorly, there may be scratch marks on the paper, a change in its texture, or a differing reflection where the writing has been hidden.
If a message is suspected to contain invisible ink, you can first inspect it visually and smell it for any irregularities. The next step is to pass it under an ultraviolet light, which shows several types of invisible ink. The message can then be exposed to heat, which may reveal other kinds of ink. If you still haven’t found the message, exposing it to iodine fumes may do the trick.
If none of these techniques work, you can’t prove that there is no message there – just that there is unlikely to be one. Your adversary may be using a sophisticated invisible ink solution that you are unaware of.
Null ciphers can often be detected by anomalies in the text. They sometimes use strange turns of phrase as the creator tries to mold their secret message into the cover text. However, if the null cipher is done well and you have no reason to scrutinize it heavily, it can be simple for people to slip hidden messages past you.
Likewise, Bacon’s cipher can be detected by looking for anomalies. In suspicious text, interceptors should examine the fonts, spacing, sizing and many other factors. Once again, if it’s done well, it can be hard to tell if a secret message is present.
The tiny size of microdots makes them almost impossible to detect, unless the interceptor is already wary. On the other hand, because we know that printers leave codes on every single page, it’s pretty easy to detect them.
One method involves taking a high quality scan of the page, then zooming in on some of the white space. If you invert the colors, it should make the yellow dots more apparent. Once you have done that, you can use this tool from the University of Dresden to try and decode the dots.
Detecting digital steganography
Digital steganography can also be incredibly difficult to uncover. Unless you are already suspicious, or the steganography has been done poorly, you are unlikely to inspect someone’s files in any serious way.
One of the biggest clues is when steganographic software is discovered on someone’s computer, or if they have a history of visiting steganography-related sites. This is a good indicator that they may be hiding files with steganography, and can even give clues as to how they are doing it.
If the original version of a file is available, detecting steganographic modifications is relatively straightforward. You can take the hash of the original file and compare it to the suspicious file. If they are different, then the file has been altered and it may include hidden data.
If the above method is not possible, steganography can also be detected through statistical analysis. While our eyes and ears can’t generally detect hidden information in pictures and audio, the secret data can often be easily discovered by looking for statistical anomalies and inconsistencies.
Detecting steganography is only part of the process. If steganography is suspected, and the investigator feels almost certain that it contains hidden information, they still might not be able to uncover the data. They may not have the right steganographic tools, could be unable to figure out the algorithm, or the data may have been encrypted beforehand.
If steganography is detected by an interceptor, this may or may not mean failure for the communicators. It depends on their initial reason for sending the message. If it was absolutely critical that the communication remain unnoticed, then the detection would compromise their plan. In other cases, the communicators may be safe as long as the data itself can’t be accessed by the adversary.
Is steganography safe for hiding messages?
Steganography can be useful, but it needs it to be applied in the right situations – when you want to hide the fact that communication is taking place. When used properly, you can send secret messages from right under the nose of your enemies.
In many circumstances, steganography is completely unnecessary. If it doesn’t matter whether third parties discover that you are communicating, but the details of the communication must remain secret, you should use cryptography instead.
Steganography can be inefficient and time consuming, and it still requires you to have a secure channel where you can communicate which steganographic technique is being used, and where the data is hidden.
Encryption is much simpler and far more data can be encoded in the same space. With techniques such as public-key encryption, you can even communicate without a secure channel.
When steganography is used by itself, it’s security through obscurity, which can lead to the secret message being revealed. If you want to hide a message from adversaries, but also protect it in case it is discovered, it’s best to combine steganography with cryptography. This combination gives you the advantages of both techniques and can protect you and your data from being compromised.
In the future, however, this doubling-up of techniques is unlikely to be necessary. In 2023, a group of researchers discovered a steganography algorithm that didn’t subtly change the distribution of the innocuous content. This made it impossible to discover that anything had been hidden. The researchers used a technique involving minimum entropy coupling, which – as reported by SciTech Daily — can “join two distributions of data together such that their mutual information is maximized, but the individual distributions are preserved.” The algorithm, which the researchers say will provide “perfectly secure” digital communication.