Data protection software is designed to safeguard sensitive organisational information from loss, theft, corruption, and unauthorised access. It plays a central role in maintaining the confidentiality, integrity, and availability of data across on-premises systems, cloud environments, and mobile devices. These solutions typically combine multiple functions such as encryption, backup, disaster recovery, and access control into a unified framework that helps organisations manage risk more effectively.
Here is our list of the best data protection software packages:
- Fortra Digital Guardian EDITOR’S CHOICE This SaaS package is able to protect data held on endpoints running Windows, macOS, and Linux. The system can also operate its security measures to guard data stored on cloud platforms. Access a free demo.
- ThreatLocker (FREE TRIAL) An advanced storage control and access solution that protects your data from unauthorized access and malicious actors by allowing you to control data access through granular policies. Its intuitive interface and searchable logs are also helpful. Start a 30-day free trial.
- Files.com (FREE TRIAL) A secure file transfer and storage system that supports the implementation of a centralized data control strategy and allows users to decide on the permission levels that others get when accessing files. This service removes the need to mail out many copies of a file, thus retaining control. Try it with a 7-day free trial.
- N-able Cove Data Protection (FREE TRIAL) A data security system that prepares for unexpected data loss by managing backups of all data to provided cloud storage space. This is a cloud-based service. Start a 30-day free trial.
- ManageEngine RecoveryManager Plus (FREE TRIAL) This package provides backup services for Active Directory, Azure AD, Microsoft 365, Exchange Server, SharePoint, OneDrive, and Google Workspace. Runs on Windows Server. Get a 30-day free trial.
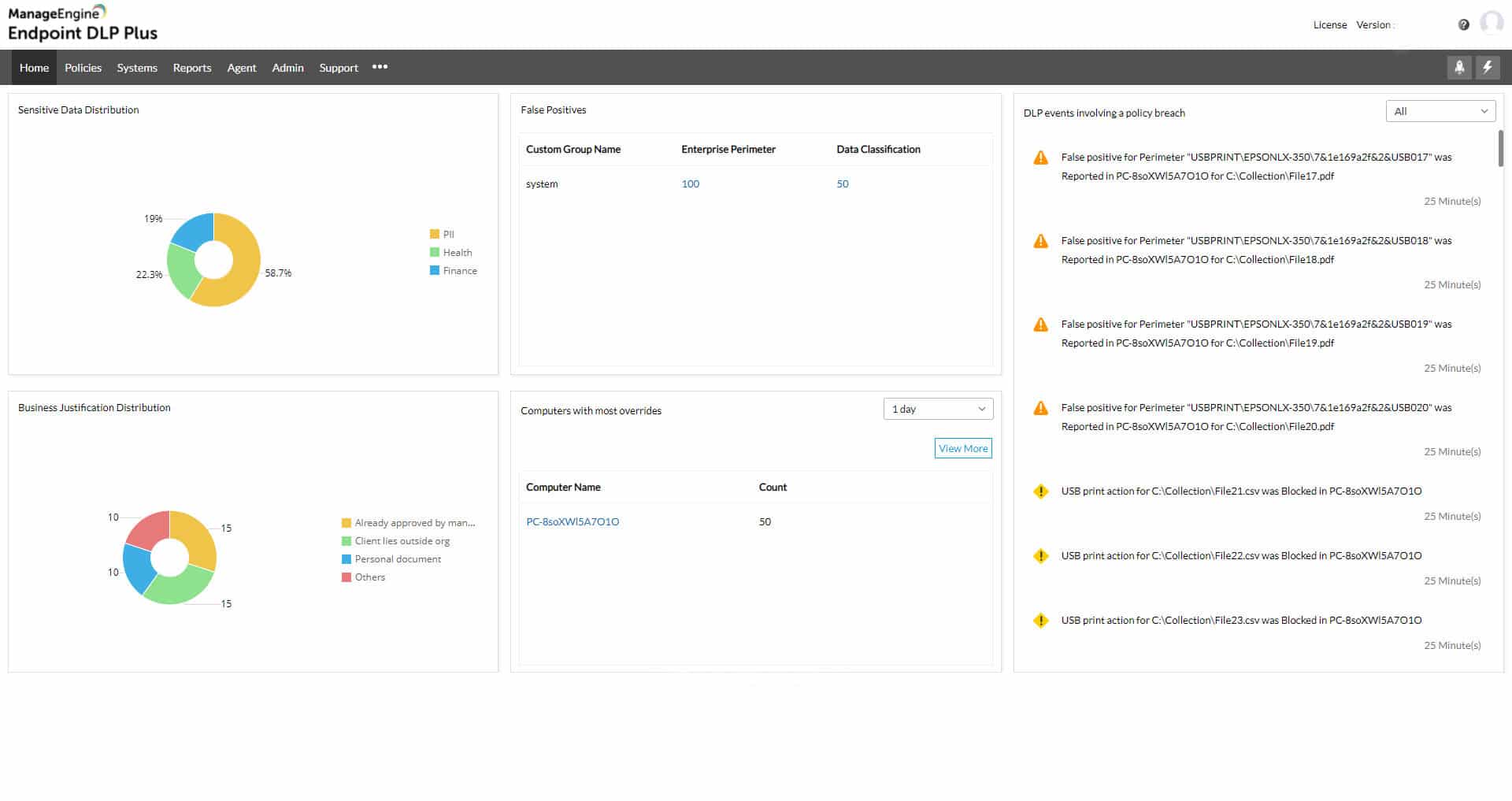
- ManageEngine Endpoint DLP Plus (FREE TRIAL) This package discovers and manages sensitive data, providing granular access for those who need it. Runs on Windows Server. Download a 30-day free trial.
- Trellix Helix A cloud-based threat management system that includes log file monitoring and protection.
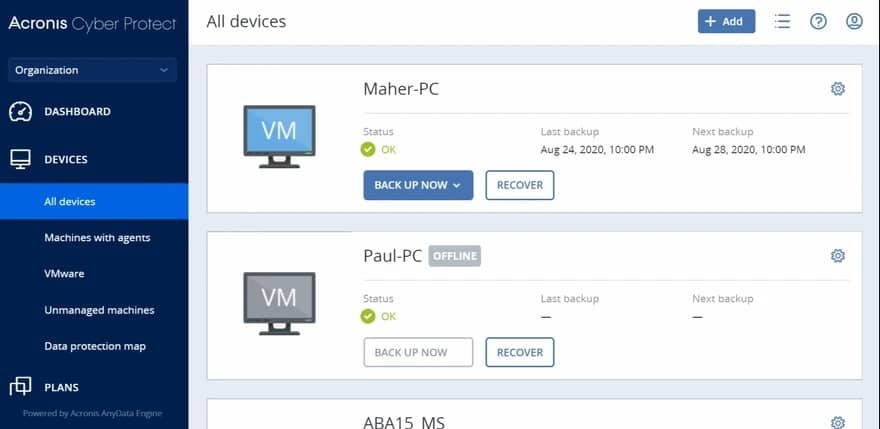
- Acronis Cyber Protect A package that includes backups, vulnerability scanning, and data loss prevention. Runs as a virtual appliance.
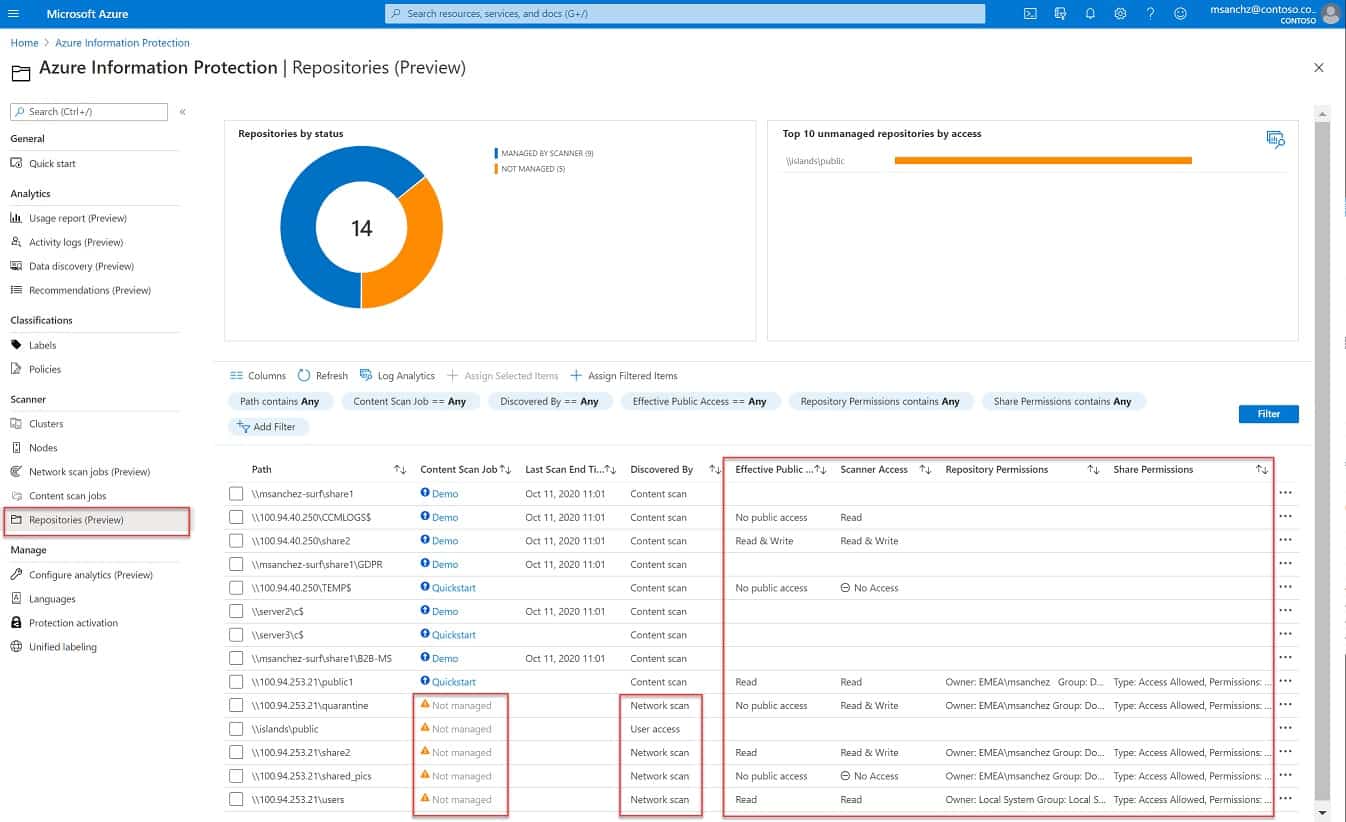
- Azure Information Protection This service from the well-known cloud platform tracks your sensitive data no matter where it is – it doesn’t have to be on an Azure server.
With cyberattacks, data breaches, and regulatory requirements becoming increasingly common, choosing appropriate data protection tools has become a critical decision for modern businesses. Strong encryption is essential to ensure data remains protected both in transit and at rest, while backup and disaster recovery capabilities help restore systems after incidents such as hardware failure, ransomware attacks, or accidental deletion. Some solutions also offer continuous data protection (CDP), enabling near real-time backups that reduce the risk of data loss.
Scalability is another key factor, as organisations generate and store increasing volumes of data over time. Effective data protection software should be able to expand alongside business growth without degrading performance or weakening security. Integration with related systems such as identity management platforms or security information and event management (SIEM) tools can further strengthen visibility and control across the environment.
Compliance requirements also heavily influence tool selection. Many industries must adhere to regulations such as GDPR, HIPAA, or PCI DSS, which define strict rules around how data is stored, accessed, and protected. Good data protection software supports compliance through audit logs, secure handling of sensitive information, and ongoing updates aligned with regulatory changes.
Ultimately, selecting the right solution helps organisations reduce exposure to risk, prevent data loss, and maintain operational continuity. It requires careful evaluation of security features, scalability, and compliance support to ensure the chosen platform aligns with business needs.
The information you hold on associated companies needs to be protected because it is probably covered by some contractual obligation. For example, a supplier may have given you a tailored price list, which they wouldn’t want their competitors or other customers to know about. Similarly, your sales team has probably stored the special deals that it has agreed to win the business of a new customer and they wouldn’t want their existing clients to know about that. Other important internal business data that needs to be protected are the salaries paid to employees and intellectual property.
The reference data in your system that pertains to individuals is covered by legislation and you could face fines if that information gets disclosed. Those individuals whose information is leaked also have the right to sue your company. Laws also govern how you use that data, which is called Personally Identifiable Information (PII), and even where you store it.
Data protection priorities
When conducting data protection, you need to consider three areas of concern:
- Data loss
- Data disclosure
- Data misuse
Ensuring that you put in place software to prevent these three types of events will give you a data protection strategy.
Data loss
Within the IT industry “data loss” usually means data theft. In this guide, we use the term to mean accidental or environmental events that cause data to be no longer accessible. So, a server being ruined by a burst pipe or an IT technician accidentally wiping a disk would be two examples of this. In other words, the data is lost and cannot be recovered.
It should be assumed that the only reason you hold each piece of information is that your business needs it to operate. Imagine if all of your system’s customer accounts suddenly got wiped or if you lost all of the work in progress that your company’s consultants and engineers have stored while working on client accounts.
The consequences of the actual unrecoverable loss of data would be catastrophic. While the loss of all data of a particular type would be disastrous, so would even the loss of part of the data. This type of data protection forms part of company continuity procedures and relies on backup and recovery systems.
Data disclosure
Data disclosure refers to non-authorized access to data. This might be through theft or through sharing. In the case of data sharing by authorized users, this could be accidental or intentional. Intentional data disclosure could be driven by resentment against the company, as a power play by rival employees, or as a whistleblowing act.
Protecting data from disclosure is carried out through data loss prevention systems and threat detection.
Data misuse
Data misuse is usually intentional. For example, a company might use contact information for clients of one division to launch a promotion campaign for the launch of a new division. Data is held for a purpose and must not be spread around to benefit unrelated activities. Holding incorrect data is classified as data misuse because it incorrectly labels a customer. These types of events can be prevented through data governance and data protection compliance packages.
As incorrect information is classified as misuse, unauthorized alteration to records is another form of misuse that needs to be guarded against. Changes that render stored information incorrect can be performed accidentally or intentionally by employees, by company management to cover up a misdemeanor or improve a financial or by an intruder to cover up activity or to slur a rival. This type of data misuse can be guarded against by file integrity monitoring (FIM) systems.
The best data protection software
When looking for the best data protection software, we are aiming for packages that can cover as many of the damaging events that can impact data integrity. Data protection standards, such as PCI DSS and HIPAA understand that some data disclosure events are unavoidable. However, in these cases, the standards expect that companies should spot the data disclosure, loss, or damage with speed and notify all of those affected by the event as quickly as possible. The data attacks should also be reported to the relevant authorities as quickly as possible, while remediation attempts to recover data or prevent a similar attack from happening are also expected.
What should you look for in a data protection system?
We reviewed the market for data protection software and analyzed the options based on the following criteria:
- An off-site system or virtual appliance that is systemically protected from events on the network
- A data persistence service that enables backups to be managed and changes to be rolled back
- A method to identify sensitive data and implement graded protection measures
- Integrated vulnerability and risk management
- Action logging for compliance auditing
- A demo or a free trial for a no-cost assessment
- Value for money offered by bundles that discount each function when compared to the cost of buying them individually
As well as following those guidelines, we looked for tools that would cover as many aspects of data protection as possible and specialized systems that are geared towards achieving excellence in specific aspects of data protection.
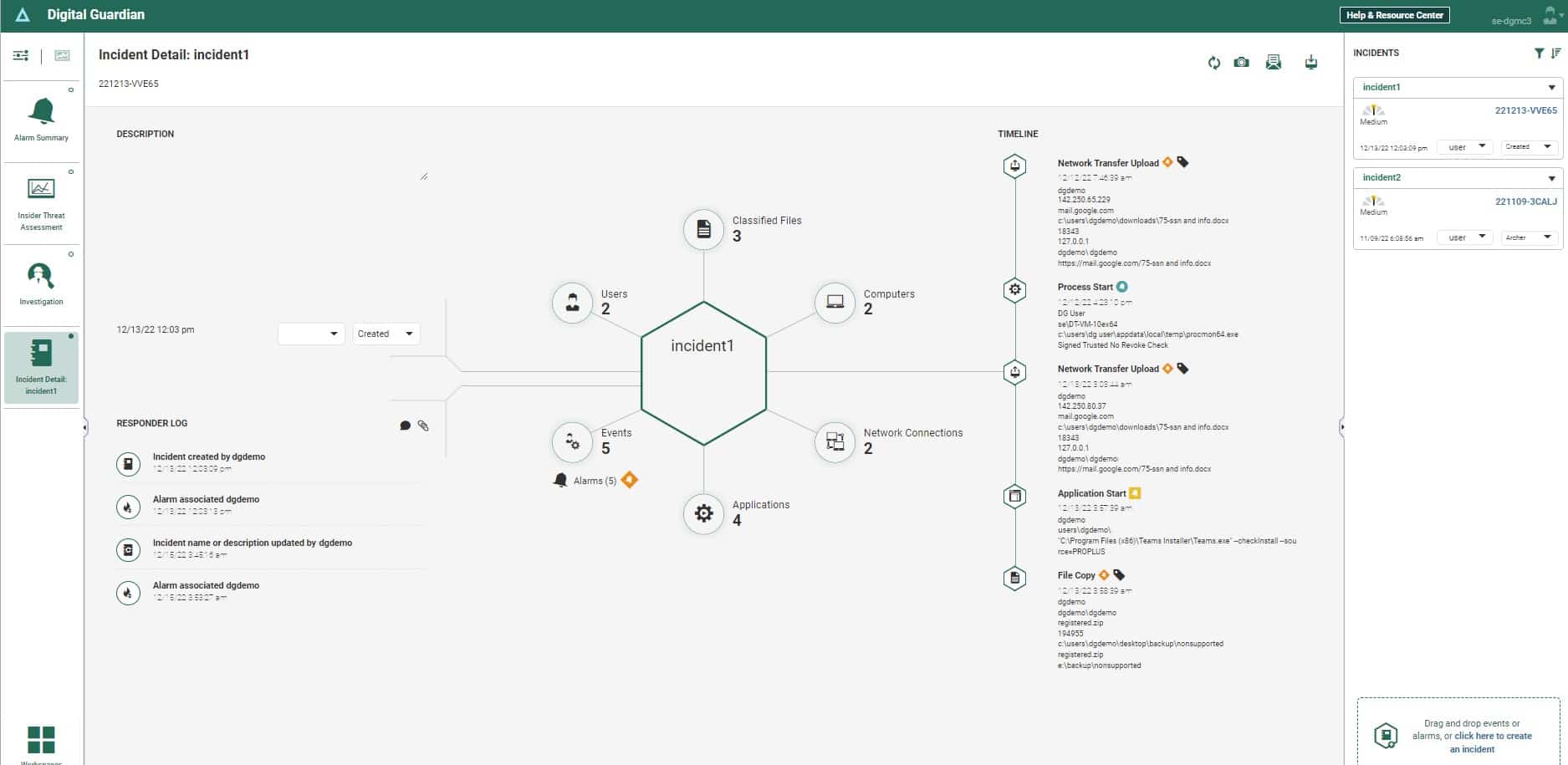
1. Fortra Digital Guardian (GET DEMO)
Fortra Digital Guardian is a cloud-based data loss prevention package that guards data held on premises and in the cloud. The system includes a data discovery and classification service and it will automatically adapt to the definitions of sensitive data given by specific data protection standards.
Key Features:
- On-Premises Protection: Secures data stored on local servers.
- Cloud Data Protection: Guards data in Google Workspace and Microsoft 365.
- Multi-Platform Support: Scans Windows, macOS, and Linux endpoints.
- Cloud Platform Security: Protects data on AWS, GCP, and Azure.
- Sensitive Data Classification: Automatically discovers and classifies sensitive information.
Why do we recommend it?
Fortra Digital Guardian is a SaaS package that runs on the AWS platform. You don’t need to make space on one of your servers to host the system and you don’t need to worry about software maintenance. The tool will protect data on your own endpoints, on cloud platforms, and held within SaaS packages.
This system will protect both personally identifiable information (PII) and intellectual property (IP). The system uses context awareness to identify data fields that could be spread through a document but collectively signify PII while individually seeming innocuous.
The Digital Guardian system relies on Active Directory for access rights controls but it doesn’t provide auditing for that ARM, so you need to tune up the access controls in AD in order to get the best security service from the package.
The Digital Guardian system is adaptable to many data protection standards, including HIPAA, GDPR, and PCI DSS. Digital Guardian offers a managed service for companies that don’t have their own cybersecurity experts on the payroll.
Who is it recommended for?
This is a good option for businesses that follow HIPAA, PCI DSS, GDPR, and other mandatory data protection standards. The cloud base of the package means that it isn’t limited to monitoring one site and can easily manage security for hybrid systems. The Managed DLP will appeal to businesses that don’t have their own technicians.
Pros:
- Monitors Data Movement: Tracks and encrypts data transfers to ensure security.
- Access Control Integration: Enforces access rights based on Active Directory.
- Comprehensive Data Protection: Safeguards PII, intellectual property, and trade secrets.
- Cloud Service Control: Regulates file sharing on cloud platforms.
- Detailed Activity Logging: Provides extensive logs of user activities for security audits.
Cons:
- Pricing Inquiry Required: Must contact the vendor for pricing details.
Digital Guardian has a strong performance history, which makes it stable and reliable. Fortra doesn’t publish a price list or offer a free trial. However, you can examine the system by accessing a free demo.
EDITOR'S CHOICE
Fortra Digital Guardian is our top pick for data protection software because this is a leading DLP system that has been heavily tested and proven through use by an extensive client list. This system protects data on cloud systems as well as on premises, making it ideal for hybrid environments. Companies without their own cybersecurity teams will be drawn to the managed service option.
Download: Get FREE Demo
Official Site: https://www.digitalguardian.com/demo
OS: Cloud-based
2. ThreatLocker (FREE TRIAL)
ThreatLocker is a data protection software that prevents unauthorized access through granular policies. With this tool, administrators can have complete control and visibility into what data can be accessed, copied, shared, or accessed by every user.
Key Features:
- Centralized Logging: Records every activity, including read, write, access, copy, etc., in a single place for in-depth visibility.
- Customizable Filters: The logs can be searched using custom and granular filters. These filters can also be saved for repeated use.
- Granular Access: Enables administrators to streamline access for every request, instead of just blocking or revoking permissions.
- Learning Mode: Comes with a test mode for testing the policies to understand their impact before implementing them in the live environment.
Why do we recommend it?
We recommend it because it provides the visibility that you need without compromising on user experience. When a user requests access, the administrators are immediately notified, and the permissions are granted or rejected – all within a few seconds. Such quick workflows ensure there are no business disruptions or wait times. Similarly, every activity is logged in centralized locations, and these log files can be searched using multiple filters.
Furthermore, administrators can restrict users from accessing certain locations or file types, reducing the chances for them to view or copy restricted data. Similarly, policies can be used to restrict users from using certain applications, and this can come in handy to prevent unauthorized users from running executable files.
Who is it recommended for?
It is highly recommended for organizations of all sizes that want to safeguard their data from unauthorized users or applications.. It also helps those organizations that have to meet strict compliance records, as the log files come in handy to prove security.
Pros:
- Automated Alerts: Sends alerts automatically when certain events occur.
- Extensive Policies: Supports both broad and granular policies.
- Zero Trust: Takes a zero-trust approach to security.
- Test Mode: Comes with a test mode for testing the policies.
Cons:
- Learning curve: Some users may face a learning curve.
ThreatLocker is known for its stability and excellent customer support. Though it does not publicly list the price, you can watch a demo, request information, or try it by registering for a 30-day free trial.
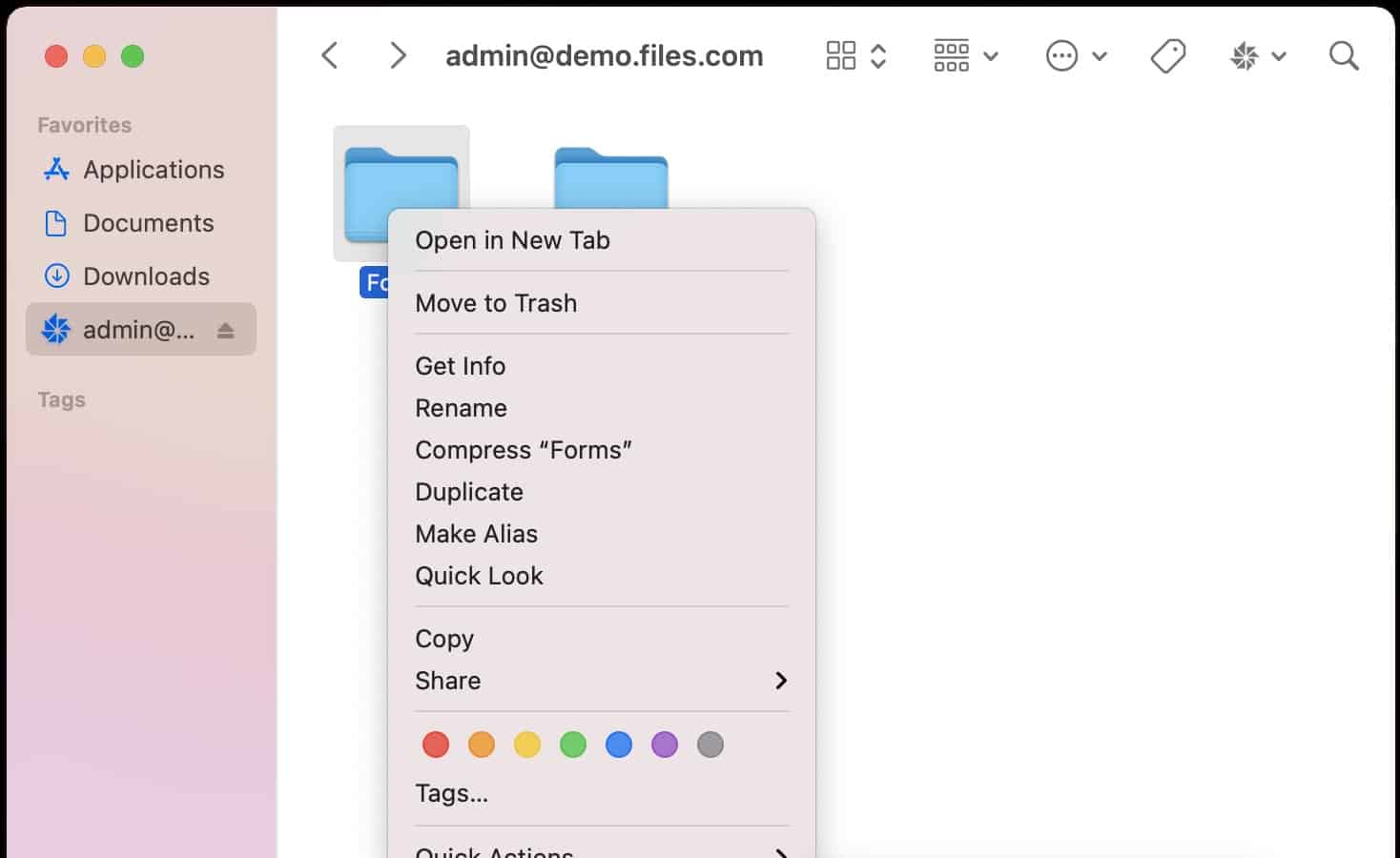
3. Files.com (FREE TRIAL)
Files.com is a cloud service that operates as a secure file store and transfer manager. You can improve data protection by centralizing all file storage in one place on this cloud storage system. Uploads to the service are protected by encryption as files at rest on the server.
Key Features:
- User Access Controls: Manage who can access files with user-specific permissions.
- Cloud Platform: Centralized, secure cloud-based file storage and management.
- Invitation-Based Access: Share files via invitation links, enhancing security.
- Permission Levels: Assign different access rights to users based on their roles.
- Microsoft 365 Integration: Seamlessly integrates with Microsoft 365 for enhanced collaboration.
Why do we recommend it?
Files.com protects data in motion and at rest with AES-256 encryption. That is the strongest encryption system around and it is used by the banking industry and the US military. The Files/com system is a data-sharing platform that can be used for collaboration over the creation of files through an integration with Microsoft 365. It is a secure storage space that can be used for business continuity in case of an environmental disaster on your site and it is also a good choice as a hub for distributed teams. Store files for distribution and mail out invite links for in-place access rather than by sending attachments.
Files.com gives you several data management strategies. You can institute a working practice that requires all files to be created and saved on the cloud platform. This service integrates with Microsoft 365, so by removing endpoint software, you get better control over where files are saved. Each user gets an individual account, which enables all actions on files to be tracked. There is also an administrator account for each plan, which has several file-tracking services built into it.
When all files are on the Files.com server, users can distribute or share files by sending out a link to the file on the server. Permissions can be restricted to read-only, controlling the number of copies that are issued for each file and tightening data protection.
Who is it recommended for?
The Files.com system is recommended for any size or type of business. Small businesses cut costs by removing the need to buy a files server and large businesses get unlimited, extendable storage space that is secure and can link together distributed teams.
Pros:
- Space-Saving Storage: Eliminates the need for physical file servers, saving space.
- Efficient File Management: Handles large files effectively.
- Reduced File Duplication: Keeps a single version of files to minimize unnecessary copies.
- External Viewer Access: Allows external parties to view files securely without downloading.
- Link-Based Sharing: Replaces email attachments with secure links for file access.
Cons:
- Limited Trial Period: The free trial lasts only seven days.
You can assess Files.com on a 7-day free trial.
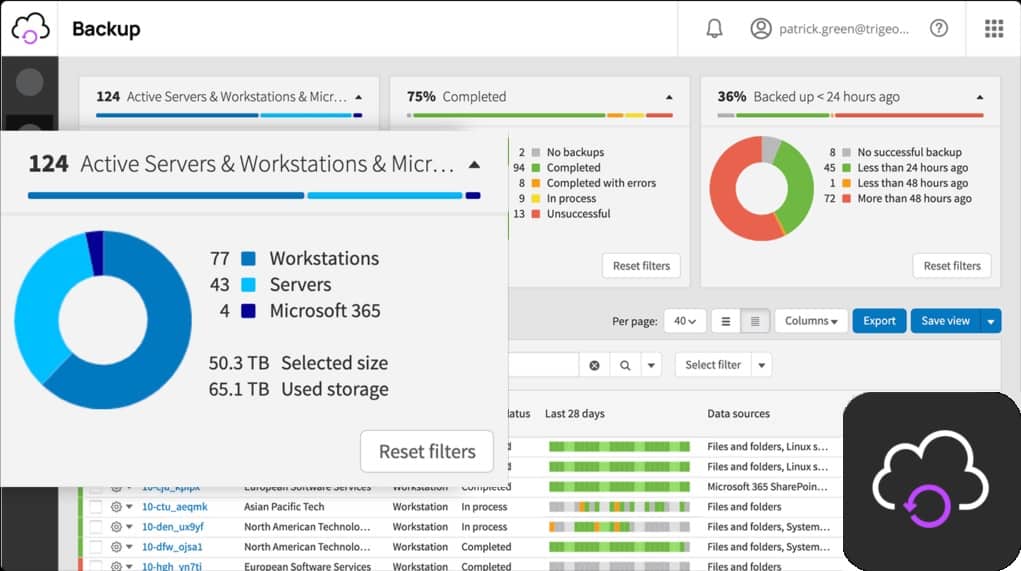
4. N-able Cove Data Protection (FREE TRIAL)
N-able offers a range of services that support Managed Service Providers (MSPs). However, these tools can also be useful for in-house IT departments, especially those that manage multiple sites. The N-able Cove Data Protection system is based in the cloud, so it can automate the backup services of any site anywhere. Backups created by this system can be used for migration or replication as well as for restoring lost data to the same location.
Key Features:
- Cloud-Based: Manages backups and recovery through a cloud platform.
- MSP-Focused Design: Tailored for managed service providers but useful for in-house IT departments.
- File Backup: Provides comprehensive file backup services.
- Secure Storage: Ensures data safety with strong encryption.
Why do we recommend it?
N-able Cove Data Protection is a backup and recovery system that is designed for use by managed service providers (MSPs). The service is one of the tools offered on the N-able platform, which are all meant for use by MSPs. The central package on that platform is a remote monitoring and management (RMM) bundle and Cove Data Protection enables MSPs to add data protection to their regular work of system administration. Backup repositories are protected by AES-256 encryption.
Data needs to be uploaded to the N-able cloud servers for storage. However, this is not a security risk because transfers are protected with strong encryption. This involves the AES cipher with a 256-bit key, which is considered uncrackable. Data is compressed for transmission, which speeds up the storage process and also makes the restore phase quicker.
While on the N-able server, backups are also protected by 256-bit key AES encryption. N-able has data centers around the globe and will store your backups in a location closest to your site to make transfer paths shorter. Data held on the N-able servers is also mirrored on another server, so there is no risk that the backups that you save can be lost or damaged.
If your business is hit by environmental damage that renders your premises inoperable, N-able Cove Data Protection enables you to get up and running as soon as you have started up the alternative site that your business continuity plan designated. The backup system can populate your new servers with your old data, meaning that the business can continue to run with minimum disruption.
The N-able Cove Data Protection system can manage the contents of virtual servers as well as physical servers. Servers can be backed up down to the operating system – even including the OS. The service has special backup routines for Microsoft Exchange Server, Sharepoint, and MySQL. It is also possible to backup OneDrive with N-able Cove Data Protection. Updates can be versioned, creating timed archives, any one of which can be used in full or partially to restore files. This is an important function to recover from unauthorized file tampering, which might not be discovered before many backup cycles have occurred.
N-able Cove Data Protection includes all of the storage space you need to hold copies of your important data. The Backup system is automated and can cover data held on any site. The system creates efficiency by running constantly in the background, performing incremental backups and its off-site location means the processes of the Backup service won’t be impacted by any environmental damage or system hijacking that could be the cause of your data loss or tampering.
Who is it recommended for?
The audience for Cove Data Protection is MSPs and the package is more likely to appeal to existing users of the N-able RMM service. This system would also be good for large, multi-site businesses.
Pros:
- Inclusive Cloud Storage: Comes with ample cloud storage for backup needs.
- Strong Encryption: Uses AES-256 encryption for data in transit and at rest.
- Database Backup: Supports backups for SharePoint, MS Exchange Server, and SQL Server.
- Migration-Friendly: Allows backups to be used for data migration.
Cons:
- MSP Optimization: While usable by in-house IT departments, it’s optimized for MSPs.
N-able Cove Data Protection can operate restore actions to bare metal servers, physical-to-virtual, or virtual-to-virtual. The N-able Cove Data Protection system can be assessed on a 30-day free trial.
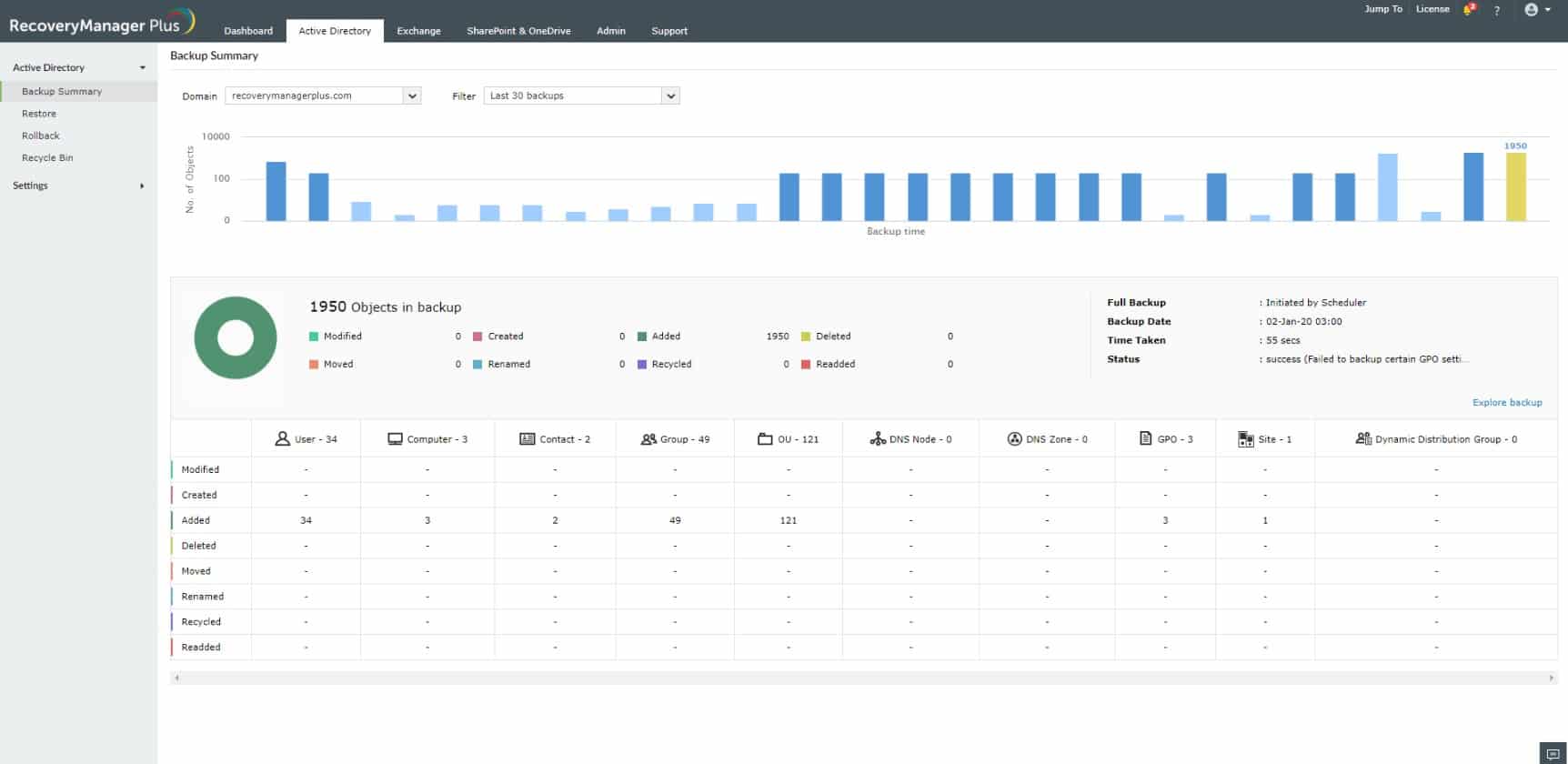
5. ManageEngine RecoveryManager Plus (FREE TRIAL)
ManageEngine RecoveryManager Plus is a software package that backs up the Microsoft systems that run on Windows Server or SaaS packages provided by Microsoft, such as Microsoft 365. It can also back up Google Workspace accounts. This tool is particularly important for backing up Active Directory and Azure AD.
Key Features:
- On-Premises Operation: Runs directly on your local servers.
- Comprehensive Backup: Backs up both on-site and cloud systems.
- Cloud Drive Backup: Secures data from cloud storage services.
- Free Edition: Available with limited capacity.
Why do we recommend it?
ManageEngine RecoveryManager Plus is an important purchase for any business that runs on Microsoft products. It is particularly essential for those companies that use Active Directory, either on Windows Server or on Azure, for their access rights management system. The service is also very good a backing up SaaS packages.
As well as copying over the data held on your cloud services, this system backs up settings for those cloud systems and for Active Directory in its many different forms. The service spots changes in your AD instances and copies over just those updates, which is a very efficient strategy that places minimum load on the network.
The backup and recovery system can operate while the Microsoft tools are still in use – you don’t have to kick users off to recover data This is particularly important in the case of Active Directory where a recovery could otherwise require all users to be booted off the system.
Local and cloud syncing presents a complication for backup systems because the same file can exist in several locations and copying over all instances wastes space. So, for example, if you are synching to OneDrive, you just back up the OneDrive system, which will automatically take care of local copies because the Microsoft service will update local versions once files are restored.
The movement and storage of data can present security risks. The ManageEngine system compresses data to save space and it also protects files with AES-256 encryption both at rest and in motion. This encryption cipher is impossible to crack and it is the system used by the US military and most of the world’s banking system.
The coverage of all AD types – on Windows Server, for Exchange, for SharePoint, etc., means replication and SSO systems are coordinated within the backup system. You won’t get your replication out-of-synch, so there is no worry about corruption or users getting shut out of some of their services due to uncoordinated data restoration in AD.
Who is it recommended for?
The ManageEngine system is a good choice for businesses that are all Microsoft and it also covers Google Workspace, so those companies that are heavily reliant on these cloud systems are the primary market for RecoveryManager Plus. Small businesses will be drawn to the package’s free edition because it covers all of the systems that the paid version backs up but with a few capacity restrictions.
Pros:
- Robust Encryption: Protects data with AES-256 encryption during transfer and storage.
- AD Coordination: Synchronizes all Active Directory instances for seamless backups.
- Minimal Impact: Lightweight backup and recovery processes that don’t disrupt operations.
- Data Compression: Reduces storage space needed for backups.
Cons:
- No Storage Provided: Requires users to arrange their own storage solutions.
- Windows-Only: Limited to running on Windows Server.
The ManageEngine gives you complete control over your backup storage strategy because that element is not included in the package – you need to arrange your own storage locations. There also isn’t any choice over which operating system the software runs on because it is only available for Windows Server. You can test the RecoveryManager Plus system with a 30-day free trial.
6. ManageEngine Endpoint DLP Plus (FREE TRIAL)
ManageEngine Endpoint DLP Plus is a large package of sensitive data management tools. The system starts with a discovery process – that service continues to discover new instances of sensitive data as they are created. The bundle provides access controls, activity monitoring, and data movement monitoring. It also includes compliance reporting.
Key Features:
- On-Premises Software: Operates directly on local servers.
- Data Discovery: Continuously finds and classifies sensitive data.
- Sensitive Data Protection: Implements robust methods to secure data.
- Access and Movement Controls: Monitors and regulates data access and transfers.
Why do we recommend it?
ManageEngine Endpoint DLP Plus is a sensitive data management package and it discovers and classifies personally identifiable information, personal health information, and intellectual property. The system provides automated tools to protect data from disclosure or tampering while allowing employees who need to use that data for business purposes to get access.
The data discovery process has to be focused on a specific type of data and the precise category that your implementation of Endpoint DLP Plus needs to find depends on your business sector and the data protection standards that you need to follow. For example, businesses that handle credit card data need to comply with PCI DSS.
The discovery process is made easier by a library of templates. So, the administrator setting up the package just chooses the appropriate template that implements a specific data protection standard. Data can be found in PDFs as well as text files and those formats require OCR scanning.
Classification sorts out which instances of data relate to a specific standard, while others could be flagged as potentially sensitive. The next step is to associate user groups or individual user accounts that need access to that data with each data type.
With that reference data in place, Endpoint DLP Plus works on implementing protection. One cutting-edge method for data protection that this package employs is to define trusted applications. This had a double benefit because not only does it enhance the value of access control for those applications but it completely blocks unauthorized software from getting to data. So, malware and ransomware are rendered useless.
The package also applies controls to data movement channels, such as emails, USB drives, and cloud uploads. The system allows some people to use some data transfer methods for some data. So, it doesn’t just block everything and people can still get on with their work.
Who is it recommended for?
This package is suitable for any company. It will be of greater interest to companies that handle PPI. However, you should also remember to protect trade secrets and intellectual property. ManageEngine offers a Free edition for SMBs. This will protect data on 25 endpoints. Larger companies get a paid edition of the package.
Pros:
- Insider Threat Detection: Tracks user activities to identify potential insider threats.
- User Credential Enforcement: Utilizes data containerization to enforce user access rights.
- Application Control: Blocks unauthorized applications from accessing sensitive data.
- USB Device Management: Regulates the use of USB drives to prevent data leaks.
Cons:
- No Cloud Version: Lacks a SaaS deployment option.
Endpoint DLP Plus runs on Windows Server and it has a Free edition that protects data on 25 endpoints. ManageEngine offers the unlimited paid plan, called the Professional edition, on a 30-day free trial. If you don’t buy at the end of that period, your installation switches over to the Free edition.
7. Trellix Helix
Trellix Helix is a next-generation SIEM service that includes a threat intelligence feed. This service is a good choice to protect your entire IT system and all data from theft or other malicious activity.
Key Features:
- Cloud-Based SIEM: Offers a cloud-hosted Security Information and Event Management system.
- Threat Detection: Identifies and mitigates various security threats.
- Behavior Analysis: Uses UEBA to spot anomalous behavior by authorized accounts.
Why do we recommend it?
Trellix Helix is a new name in cybersecurity but it has a very strong history in the field. This is FireEye, which has changed its name to Trellix, due to a series of splits, mergers, and takeovers. So, the company is still establishing its brand but Trelix already has a solid track record of service. You can protect your data with this SIEM system and be sure that its threat hunting is up to date, thanks to the high-quality threat intelligence feed that Trellix provides.
The service doesn’t just block intruders. It includes a system called User and Entity Behavior Analytics (UEBA) that can identify unusual activities performed by authorized accounts. This anomalous behavior may indicate a hijacked account or an insider threat. Account hijacking can be identified by illogical login activity, such as an account of a user being used in a different country. The system will track the activities of those suspicious accounts, particularly concerning data access.
You can set up your Helix system to perform by a specific data protection standard. The service operates with “playbooks” which are workflows that get triggered by a particular combination of events. It is also possible to create your playbooks. The service is hosted in the cloud and the dashboard is accessed through any standard Web browser. Those dashboard screens can also be customized.
Who is it recommended for?
Helix is hosted by Trellix on its cloud platform, so anyone can use this package, regardless of operating system. Small businesses will find this package a little too much, but mid-sized and large businesses need the comprehensive threat identification offered by Trellix. This is a general data protection service and doesn’t have sensitive data discovery or compliance reporting.
Pros:
- Baseline Activity Monitoring: Establishes normal activity baselines to detect deviations.
- Automated Intrusion Blocking: Implements workflows to automatically respond to threats.
- Compliance Auditing: Collects and stores log messages for compliance purposes.
Cons:
- No Price Transparency: Requires contact with the vendor for pricing information.
Integrations in the Helix package will exchange data and interact with other applications if you activate them. This makes it easier for the security system to extract activity reports from other services and also implement remediation through coordinating with other systems.
8. Acronis Cyber Protect
Acronis Cyber Protect is a bundle of security and data management services. It includes a backup system, a vulnerability scanner, and a threat-protection system.
Key Features:
- Backup System: Provides comprehensive data backup solutions.
- Vulnerability Scanner: Scans for system vulnerabilities to prevent threats.
- Threat Detection: Identifies and mitigates potential threats, including malware.
Why do we recommend it?
Acronis Cyber Protect is a very useful combination of malware protection and backup. It will even scan each file before it is uploaded into the backup repository to prevent your backups from getting infected. Thus, this is the perfect system for ransomware protection. The antimalware will spot the ransomware before it does too much damage. However, it is likely that a few files will be encrypted before you spot the infection. However, those files can be deleted and replaced from the backup, so you will never have to pay the ransom.
The backup service can also be used to replicate servers, enabling you to set up new hardware quickly if your premises get destroyed. This can protect servers running Windows Server and Linux. The backup service will operate on virtualizations as well as physical systems.
Backups can be made to other devices on-premises or to cloud storage systems. Acronis offers a cloud storage facility but this is not included in the price of the Cyber Protect system and the two systems are not glued together, so the choice of platform is up to you.
Who is it recommended for?
All businesses need antimalware and backup systems, so getting both of these vital data protection services in one package is a great acquisition time saver. Acronis offers Cyber Protect in many editions that are suitable for different sizes of enterprises from home offices to multinational organizations.
Pros:
- Ransomware Protection: Includes malware protection with ransomware detection.
- Pre-Scanned Cloud Backup: Scans files before uploading to cloud backups to prevent infections.
- Patch Management: Offers vulnerability scanning and patch management for enhanced security.
Cons:
- Additional Cloud Storage Cost: May require additional purchase for cloud storage space.
The controller for the system is based in the cloud and one agent on your site will manage all of the system and data protection services on the Cyber Protect bundle. Acronis offers this system on a 30-day free trial.
9. Azure Information Protection
Azure Information Protection will search all of your data stores and categorize files by sensitivity. This action can be applied to any site and also to cloud servers. The cloud data management capabilities are not restricted to Azure accounts – the data can be located on any cloud platform.
Key Features:
- Azure-Hosted: Operates on the Azure platform for seamless integration.
- Hybrid System Support: Effective for both on-premises and cloud-based data.
- Compliance Ready: Supports GDPR, PCI DSS, and HIPAA compliance.
Why do we recommend it?
Azure Information Protection is a bundle of data protection services that are delivered from the Azure platform. This is a Microsoft service, so it is well integrated into the Azure platform and is good at interacting with other Microsoft systems, such as Active Directory. However, it isn’t limited to operating on data held on the Azure system, so you can use it to protect your data anywhere – even on AWS.
The monitoring service operates continuously, catching new files as they get saved and including them in the grading and control service. The classification of data as sensitive relies on the settings you put into the system. This enables the service to tailor its protection services according to data standards, such as GDPR, PCI DSS, or HIPAA.
It is possible to block sensitive files from being copied or transferred. You can also prevent their contents from being printed and those files can also be prevented from attaching to emails.
Who is it recommended for?
Azure Information Protection has services that are suitable for many different data management scenarios. For example, it has data discovery and classification for standards compliance and can be tuned to PCI DSS, HIPAA, and GDPR. You also get copy tracking for document distribution through watermarking.
Pros:
- Sensitive Data Classification: Automatically identifies and categorizes sensitive files.
- Graded Access Rights: Implements access controls and transfer blocking for sensitive files.
- Active Directory Integration: Works well with Microsoft Active Directory for managing access.
Cons:
- Dependent on Active Directory: Less effective without Active Directory integration.
The Azure Information Protection service includes an encryption service to protect files on your server and in transit. You can link the Azure Information Protect service to your Active Directory implementation for access rights management.