Data breaches and cyber threats are becoming increasingly common. Safeguarding sensitive information has become more critical than ever. One of the most effective ways to protect confidential data is by using encrypted file sharing services. These platforms ensure that files shared over the internet are encrypted both during transit and at rest, making it nearly impossible for unauthorized users to access the content.
Whether you’re sharing business documents, personal files, or confidential contracts, encrypted file-sharing services offer peace of mind, knowing that your data remains secure. As businesses and individuals increasingly rely on cloud storage and collaboration tools, choosing the right encrypted file-sharing service is essential for maintaining privacy and security.
A wide variety of encrypted file sharing services are available, each offering different features, security protocols, and user experiences. Some services focus on advanced encryption techniques, while others offer features such as password protection, two-factor authentication, and file expiration dates to further enhance security. These services provide an essential layer of protection in an era where data privacy is a growing concern.
Here is our list of the best encrypted file-sharing services:
- Files.com EDITOR’S CHOICE A cloud platform for file management that enables encrypted transfers, secure storage, collaboration, and link sharing.
- ExaVault (FREE TRIAL) A subscription service that provides storage space and a user account structure that enables users to secure files and grant access to others for collaboration.
- Citrix ShareFile This cloud platform includes encryption for file transfers, storage, and link sharing and can also run process automation.
- SolarWinds Serv-U Managed File Transfer Server This file server system protects uploads and creates a secure file distribution service through links for access to files on the server. It runs on Windows Server and Linux.
- Sharetru A secure file server platform, based in the cloud that implements encryption on all aspects of file sharing.
- Tresorit A cloud platform that manages secure file distribution and collaboration and includes encrypted storage space.
This guide reviews some of the best encrypted file-sharing services available today. We’ll highlight the key features, encryption standards, pricing, and performance of top platforms, helping you choose the right service to meet your security needs.
Whether you’re an individual looking to safeguard personal files or a business looking to securely share sensitive documents with clients or employees, this guide will help you identify the most reliable, secure, and feature-rich encrypted file-sharing services. Ultimately, the right service can ensure that your shared files remain confidential, protected, and compliant with privacy regulations.
Encryption for file-sharing systems
There are three points of vulnerability for files in file sharing systems. Those are when the file is in transit, when the file is at rest, and when the file is opened for viewing through a Web browser. So, there are two types of encryption to examine where considering encrypted file sharing systems.
There are well-established protocols for file transmissions. The oldest protocol available for moving files is called the File Transfer Protocol (FTP). However, this system is not encrypted and not secure. The most commonly used secure protocols used for file transmission are the SSH File Transfer Protocol, which is also known as the Secure File Transfer Protocol (SFTP), and the File Transfer Protocol Secure (FTPS).
The security built into SFTP is called Secure Shell. This is actually a protocol for secure remote access but it has a file transmission protocol built into it, which applies encryption, which is established by SSH to the file transmission packets that occur within an SSH session. The file transfer system doesn’t require a remote terminal session to actually be opened.
FTPS uses the same authentication and encryption services employed for HTTPS. The HTTPS system is the method that makes Web page transmissions secure enough that bank account and credit card details can be passed over the Internet without fear of data theft. That protection system is called Transport Layer Security (TLS).
There are many encryption systems that can be used to protect files on a server. The strongest is probably the Advanced Encryption System (AES). This cipher is considered to be uncrackable in its strongest form, which involves an encryption key that is 256 bits long. Even the weaker 128-bit key would take years to crack by permutation and trial and error, which is called a “brute force attack.” So, AES with a 128-bit key is also, effectively, uncrackable.
Many encrypted file sharing services strengthen security by holding all files on a server and not allowing them to be moved. Instead of sending a file to a recipient, the system sends that person a link to the file’s location on the server. The recipient then views the contents of the file through a Web browser rather than copying it over. Displaying a file in a browser requires that the file’s contents be sent to that browser. This creates a point of vulnerability because snoopers could intercept the transmission. To enforce security, these transmissions are protected by HTTPS, which uses the TLS protection system.
The Best Encrypted File Sharing Services
The requirement to keep information flowing in order to support the business while restricting access to certain data is a difficult mix of priorities. Encrypting files ensures that only authorized personnel and external stakeholders can see the data. Encryption ensures confidentiality because it means that possession of the file is not enough, you also need to be able to decrypt it before the contents are meaningful.
So, encryption goes a long way towards fulfilling the requirement of protecting information from theft. However, that shifts the focus of security measures from access to the file to access to the encryption system.
Effective data encryption is difficult to manage. Therefore, using a file management package that has encryption key control built into it is the most efficient solution available. These systems can tie in with your existing access rights management systems to make secure file sharing even more manageable.
What should you look for in encrypted file sharing services?
We reviewed the encrypted file sharing services market analyzed options based on the following criteria:
- A security management system that implements secure encryption that is bundled into the file sharing service
- The secure distribution of encryption and decryption keys
- A service that optionally can integrate with existing access rights management systems
- Secure file transfer mechanisms
- Storage security
- A free trial or demo version for a risk-free assessment
- A good mix of functions at a fair price that represents value for money.
An encrypted file sharing service needs to allow easy access to files by authorized users while blocking out others. It is also necessary to ensure that those who are allowed access only appropriately use the information those files contain.
The control over appropriate use has to be implemented through company policy and secure working practices. However, the encrypted file sharing service needs to contribute to those practices. This is achieved by logging all actions and putting in place processes that support data disclosure tracing. We took all of these factors into consideration when researching the market for secure file management tools.
1. Files.com (FREE TRIAL)
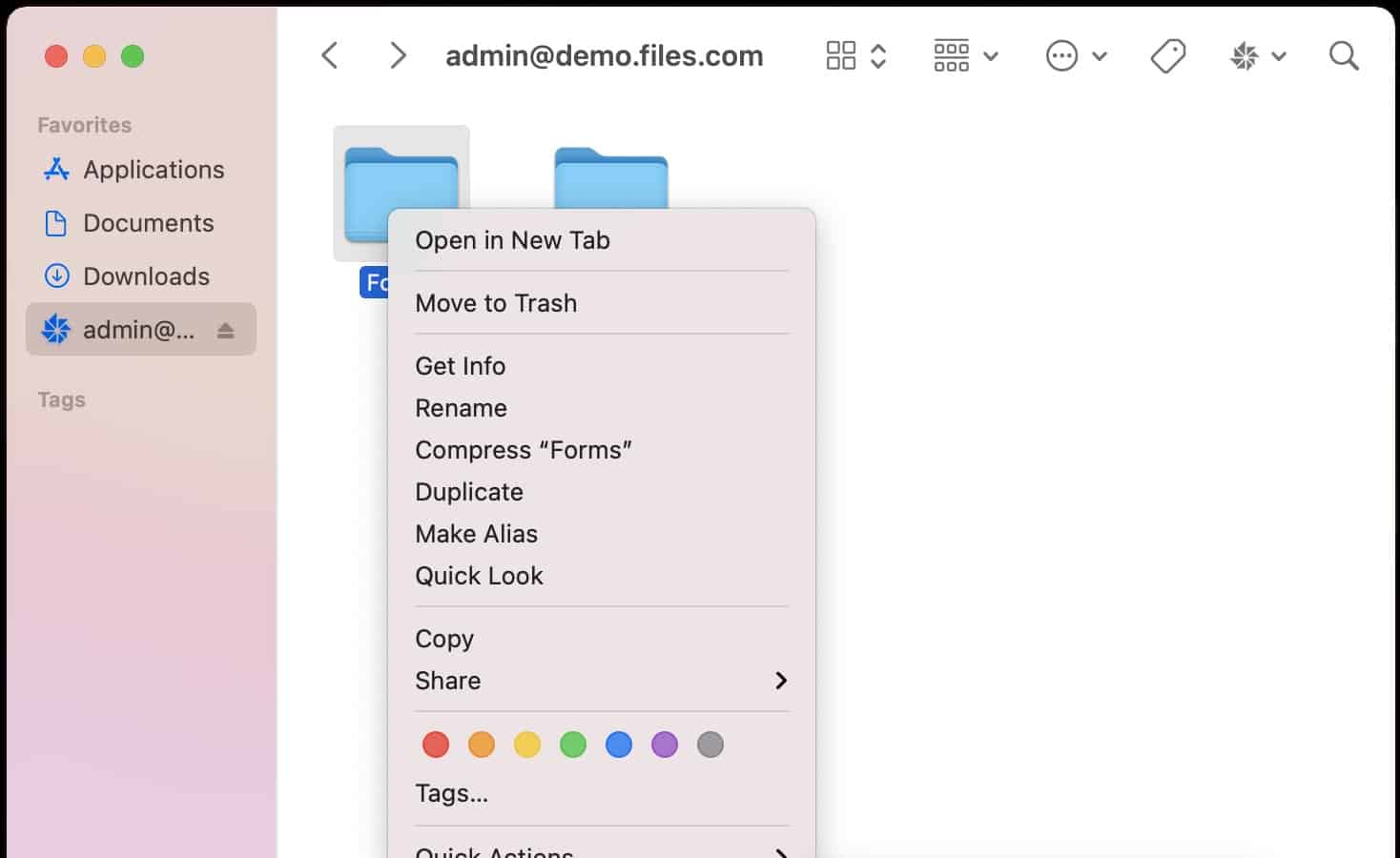
Files.com is a cloud platform that provides a file server function for its customers. Each account on the Files.com system gets a secure area of storage space on the server to hold files. There is an administrator account to start off the customer’s experience of the service. The administrator is able to set up individual accounts for the business’s users. The passwords for those accounts are kept confidential in an encrypted password vault and even the account administrator is unable to read them.
Key Features:
- Cloud Platform: Includes an administration console
- Storage Included: Can be subdivided to create user filespaces
- Secure File Transfer Protocols: SFTP and AS2
- Empowers Users to Control Access: Can grant file access to others and revoke it
Why do we recommend it?
Files.com is a cloud drive that can facilitate file transfers and collaboration. The architecture of the platform enables file owners to permit others to access, copy, or edit files. This function reduces the need to transfer files. For example, email attachments can be eliminated, with an access invitation mailed instead.
All file transfers are protected by FTPS, which includes Transport Layer Security (TLS). This involves encrypting all file transfers with an RSA cipher that has a 2048-bit key. Viewing access to files is conducted by a Web browser using HTTPS. This is also protected by TLS with a 2048-bit RSA cipher. The server space offered by Files.com is hosted by AWS. It is the AWS S3 service, which is encrypted storage space. Amazon S3 uses the Advanced Encryption Standard (AES) with a 256-bit key.
The main usage for Files.com is to centralize file storage and provide. The administrator can set up shared folders or private folders for each user. The users upload their files to the central store and then grant access to others with their system username or by email address. Access to individual files can also be granted to outsiders by email address.
The file distribution service operates through the permissions granting screen for files. The Files.com system emails out a link to each person who has been granted access. Those recipients then view the file through a browser connection that is protected by HTTPS. The file itself does not move and is not duplicated. The service uses a similar system to secure email attachments. When a user attaches a file to an email, Files.com uploads that file to its storage area and places a link to that location in the email.
Who is it recommended for?
This system has many uses. It can be used as the primary storage location for a business’s files. It can also be used for syncing and backup. The tool can facilitate the mass mailout of a single file upload, reducing the load on your network.
Pros:
- Protection for File Transfers: Uses 2048-bit RSA encryption
- Protection for the File Storage Area: Implements 256-bit AES encryption
- Administrators Can Create Shared Folders: Useful for projects
- Audit Trails: Proof of delivery
Cons:
- Encryption Protection for File Transfers isn’t the Best Available: 4095-bit RSA is stronger
You can assess Files.com on a 7-day free trial.
EDITOR'S CHOICE
Files.com is our top pick for an encrypted file sharing service because it offers a secure, user-friendly platform designed to protect sensitive data while providing seamless file access and collaboration. One of its standout features is end-to-end encryption, ensuring that all files are securely encrypted both in transit and at rest. This guarantees that only authorized users can access the files, providing peace of mind for businesses handling confidential information. Files.com also excels in granular access controls, allowing administrators to define who can view, edit, or share specific files or folders. This level of control ensures that sensitive data is protected from unauthorized access while still enabling collaboration across teams. The service supports multi-factor authentication (MFA), adding an extra layer of security to protect accounts from unauthorized login attempts. In addition to its reliable security features, Files.com offers easy integration with a wide range of popular applications, including Google Workspace, Microsoft 365, and Slack, making it simple to incorporate into existing workflows. The platform’s audit logs and real-time activity monitoring provide full visibility over file access and usage, helping businesses maintain compliance and security.
Download: Get a 7-day FREE Trial
Official Site: https://signup.files.com/signup/
OS: Cloud based
2. ExaVault (FREE TRIAL)
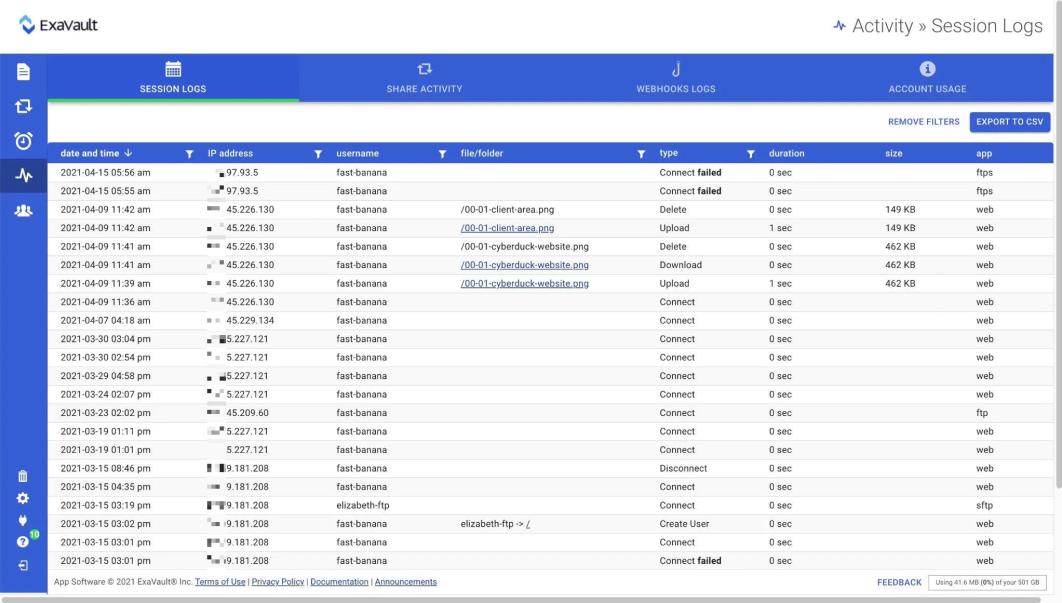
ExaVault is a cloud package that is designed to provide secure file transfers and cloud storage space. The system includes a secure file server that can interact with clients through SFTP and FTPS. The system uses 2048-bit public key encryption to protect transfers and also provides encryption protection for data at rest on the ExaVault servers.
Key Features:
- A Cloud Platform: Low maintenance
- Storage Included: Allocate space to each user
- Compliance Management: Good for GDPR
Why do we recommend it?
ExaVault is a rival to the Files.com system. It provides file space that can be allocated to individual user accounts. It can mediate file transfers or replace them through access invite links. The system can also be used as the primary storage server or for syncing and backup.
ExaVaul can be used to distribute files, removing the need to send files to external destinations. The service can also be used for internal file sharing as well because file owners grant access to others within the business.
All of the access to the cloud storage space that is included in an ExaVault system is controlled by user account credentials. The administrator can also choose to impose multi-factor authentication. Once a user has an access to the file storage space, collaboration is facilitated through uploading and by them granting access to others. Those access rights can be time-limited and they can also be revoked.
Who is it recommended for?
This cloud service offers a large file space to each user – 1TB minimum. This makes the platform a good choice for businesses that generate a large number of files or many large files. Files can be created on the platform or uploaded there. The file space is fully encrypted for security.
Pros:
- Protection for File Transfers: Protected by 2048-bit RSA encryption
- User Authentication: Multi-factor authentication
- User Invites Others to Access a Document: Controls the permission level
Cons:
- File Security: Doesn’t state the encryption cipher used to protect files at rest
All actions performed on files are logged for compliance auditing. The physical security processes carried out by ExaVault make this service compliant with the requirements of GDPR. You can assess ExaVault by accessing a 30-day free trial.
3. Citrix ShareFile
Citrix ShareFile is a cloud platform that offers a number of methods for encrypted file sharing. The service revolves around secure storage space allocated to each client’s account. This file space is unlimited and is protected by 256-bit AES encryption. The administrator of the account can set up password-protected accounts for each of the business’s staff.
Key Features:
- Secure Transfers: FTPS for file movements
- Transfer Large Files: Handles files up to 100 GB in size
- SaaS Management: Integration with Microsoft 365
Why do we recommend it?
Citrix ShareFile is a similar tool to the Files.com and ExaVault systems. This service’s remarkable feature is that it can handle file transfers of up to 100 GB in size. The service is hosted on the Web and accounts are accessed through a standard Web browser.
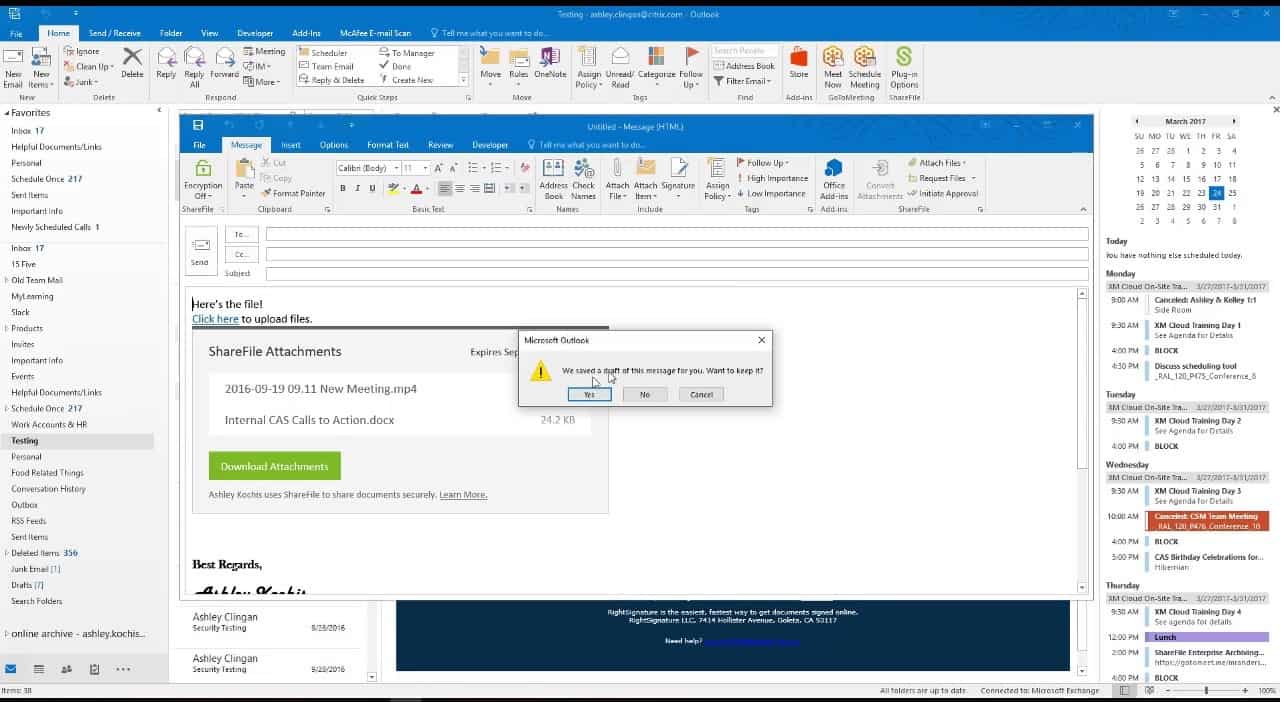
Uploads to the ShareFile server are all encrypted individually with a 256-bit AES cipher and then protected in transit by TLS that creates an FTPS connection. The system can transfer files up to 100 GB in size. Once on the server, the files do not move. Instead, users mail out links for secure access. These permissions can be revoked by the file owner or the administrator at any time.
ShareFile integrates with Office 365. This allows groups of users to collaborate on the composition of documents and store them securely. ShareFile also integrates with email applications. It removes any attachments, uploads them to the client’s file space, and inserts a link to the file into the email. Access through a browser to files on the server is protected by HTTPS.
Who is it recommended for?
The capability to move large files makes the Ctirix system suitable for media businesses and other companies that generate very large files for manufacturing designs or structural plans and calculations. Collaboration features, such as commenting and editing capabilities make it a good service for document creation.
Pros:
- Secure File Storage Drive: Protected by AES-256 encryption
- End-to-End Encryption: File encryption is applied before uploading and then maintained on the cloud platform
- Activity Logging: Identifies the user account involved in each action
Cons:
- Access by Mobile Apps: Could be a security weakness
All actions on files are logged with a timestamp and the identity of the user involved. You can a 30-day free trial of Citrix ShareFile.
4. SolarWinds Serv-U Managed File Transfer Server
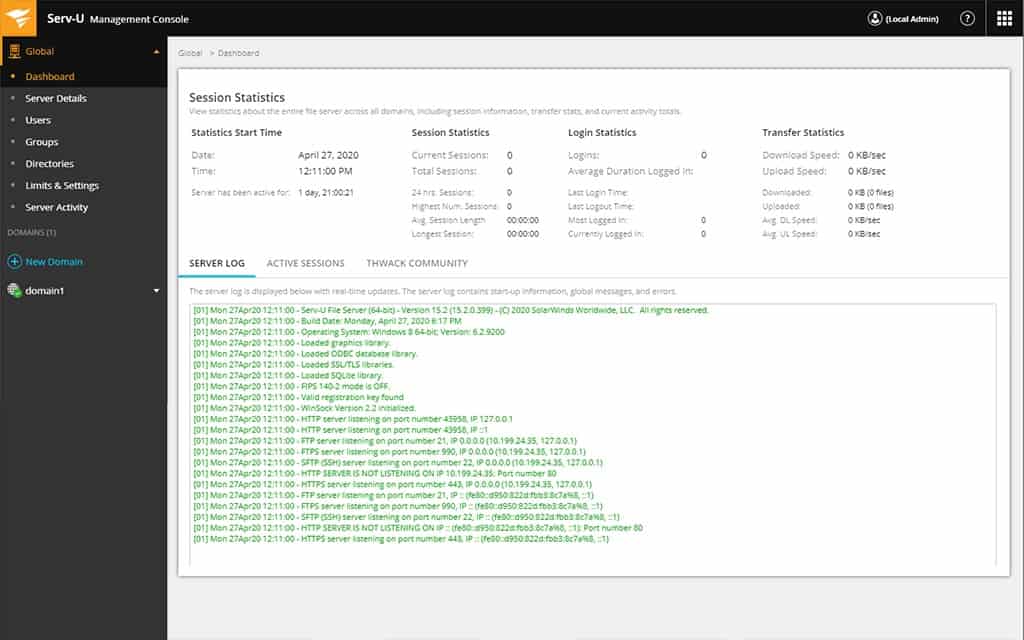
Serv-U Managed File Transfer Server is a software package that creates a secure file server for your organization. The system creates a central store of files that can be safely distributed or accessed by teams from their central location. The software is able to manage SAN and NAS file server configurations.
Key Features:
- Self-Hosted: Installs on Windows Server and Linux
- Can Manage File Transfers to and from File Servers: Good for SAN and NAS
- Encrypted Transfers: FTPS, SFTP, and HTTPS
- Protection for Files: Access controls, encryption, and activity logging
- Integrates with Active Directory: User your enterprise user accounts for Serv-u access
Why do we recommend it?
SolarWinds Serv-U Managed File Transfer Server has a number of uses. The service and be used to transfer files within a network and also to download files from cloud services, such as SaaS platforms. The MFT system allows transfer actions to be integrated into scripts, which can implement file processing actions.
The security measures built into the Serv-U Managed File Transfer Server are suitable for use by businesses that need to comply with PCI DSS, HIPAA, FISMA, or SOX. These measures are a combination of access control, encryption, and activity logging.
File transfers to the file server are protected by SFTP or FTPS, which include encryption. The overhead of encryption doesn’t place performance limits on the service – files can be up to 3 GB in size. The service is also able to hand the volumes of traffic that are generated by syncing.
The Managed File Transfer Server doesn’t impose encryption on files stored on the server. However, as this is an in-house system, physical access controls to the server and account access processes make up for that shortfall. Corporate users need accounts to access files on the server. However, this access control can be integrated with the user management services of your existing Active Directory or LDAP systems.
File sharing is implemented through secure link mailing. All users can be authorized via their email addresses. The owner of the file can specify the level of access that a recipient gets and that access can be easily revoked by the file owner or the system administrator. Users access files through any browser or through a special mobile app. This imposes HTTPS encryption on the connection.
Files can be uploaded through any secure file transfer client. The Serv-U site includes a downloadable secure FTP client. This client is able to use SFTP and FTPS security, imposing encryption on all file transfers to the Serv-U server in your data center.
Who is it recommended for?
This system is a little expensive, so it wouldn’t appeal to small businesses. Its capabilities extend to supporting the creation and management of a private file server within a network. Thus, you could use it to centralize the storage of data within the organization. This makes the protection of sensitive data easier.
Pros:
- Compliance Reporting: For PCI DSS, HIPAA, FISMA, and SOX
- User File Access Tracking: Activity logging attributable to the user account
- Link Invitation for File Sharing: Removes the need to send files
- File Transfer Package: Provides the software for both server and client
- Web-Based Client: Enables remote actions
Cons:
- Not a SaaS Package: A software package for Windows Server and Linux
Serv-U Managed File Transfer Server is available for Windows Server and Linux and it is offered on a 14-day free trial.
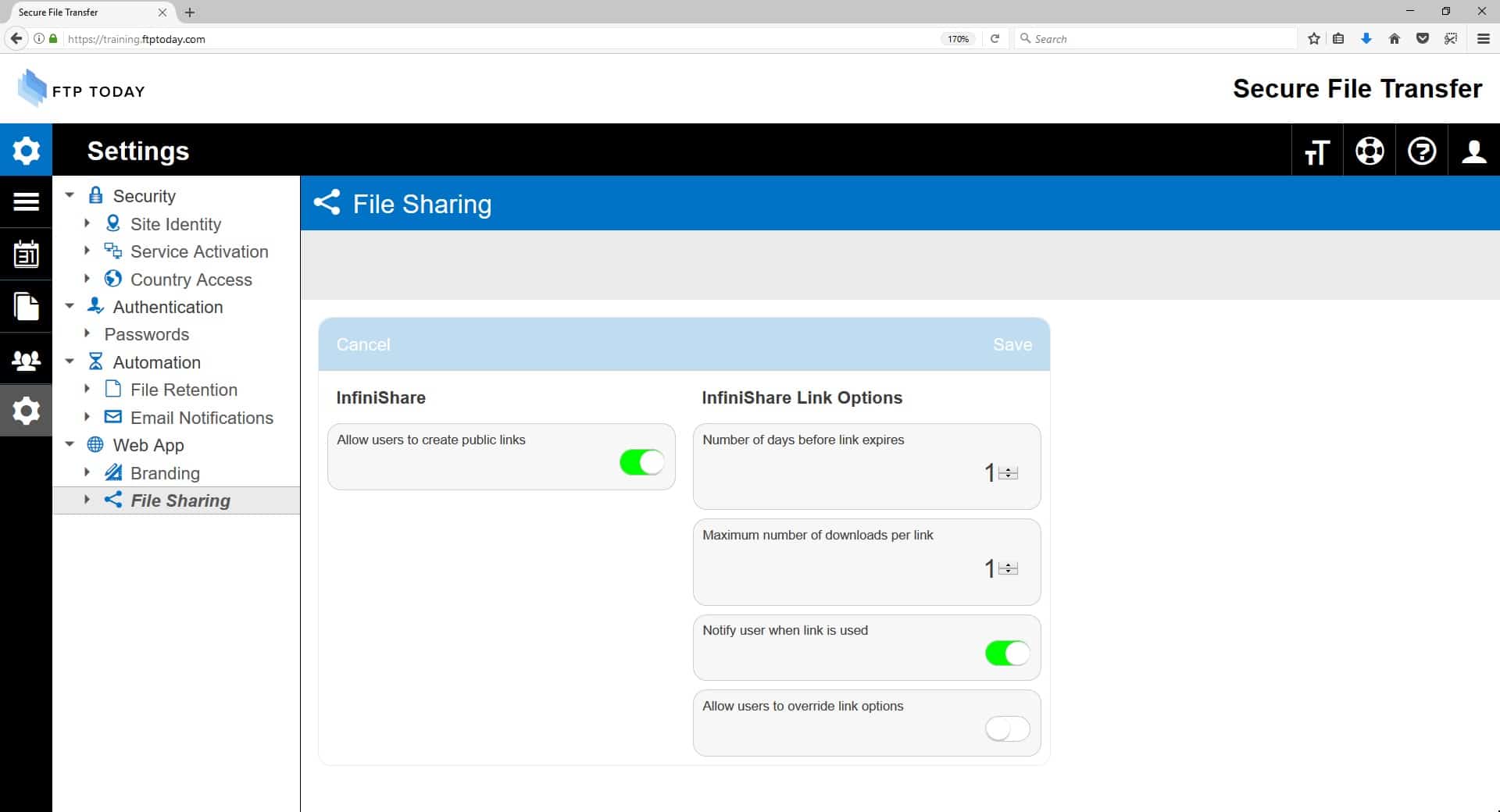
5. Sharetru
Sharetru is a hosted secure file transfer sharing system that includes cloud storage that is protected by 128-bit AES encryption. Transfers are conducted by FTPS, using TLS with a 2048-bit RSA encryption cipher.
Key Features:
- Secure Storage Space: With security monitoring
- Secure File Transfers: FTPS for file movements
- Compliance Management: Suitable for GDPR
Why do we recommend it?
Sharetru is another cloud drive service with a secure FTP feature. Users can send files or just invite others to access the file in situ on the Sharetru server. Editing and commenting features allow the collaborative creation of documents. Colleagues are invited by username and outsiders are identified by their email addresses.
Sharetru protects all of its servers with security software and that adds extra protection to all of its customer accounts. Each account has a separate operating system and the service is protected by firewalls and an Intrusion Detection System (IDS).
Access to files is facilitated via a link and through a browser protected by HTTPS.
As well as securing files in transit and on the server, Sharetru offers administrators a range of tools to protect data. It is possible to suspend user accounts immediately and revoke access to files. The system offers geofencing, which prevents authorized users from accessing files if they are physically located outside an allowed area. This is particularly useful for implementing GDPR. It is also possible o block access from specific domains or IP addresses.
Who is it recommended for?
The plans for Sharetru provide packages for a minimum of 10 users. The package is useful for businesses that operate virtual offices and don’t want to manage their own servers. SaaS productivity suites can be set up to store files direct to the Sharetru server, bypassing the need for local storage.
Pros:
- Intrusion Prevention System: Automatically applied to the cloud storage space
- Data Protection: Files in storage are protected by 128-bit AES encryption
- Data Movement Protection: File movements are protected by 2048-bit RSA encryption
Cons:
- Encryption Not the Strongest Available: AES-256 and RSA-4096 would offer stronger protection
Explore the Sharetru system by accessing a demo or sign up for the 14-day free trial.
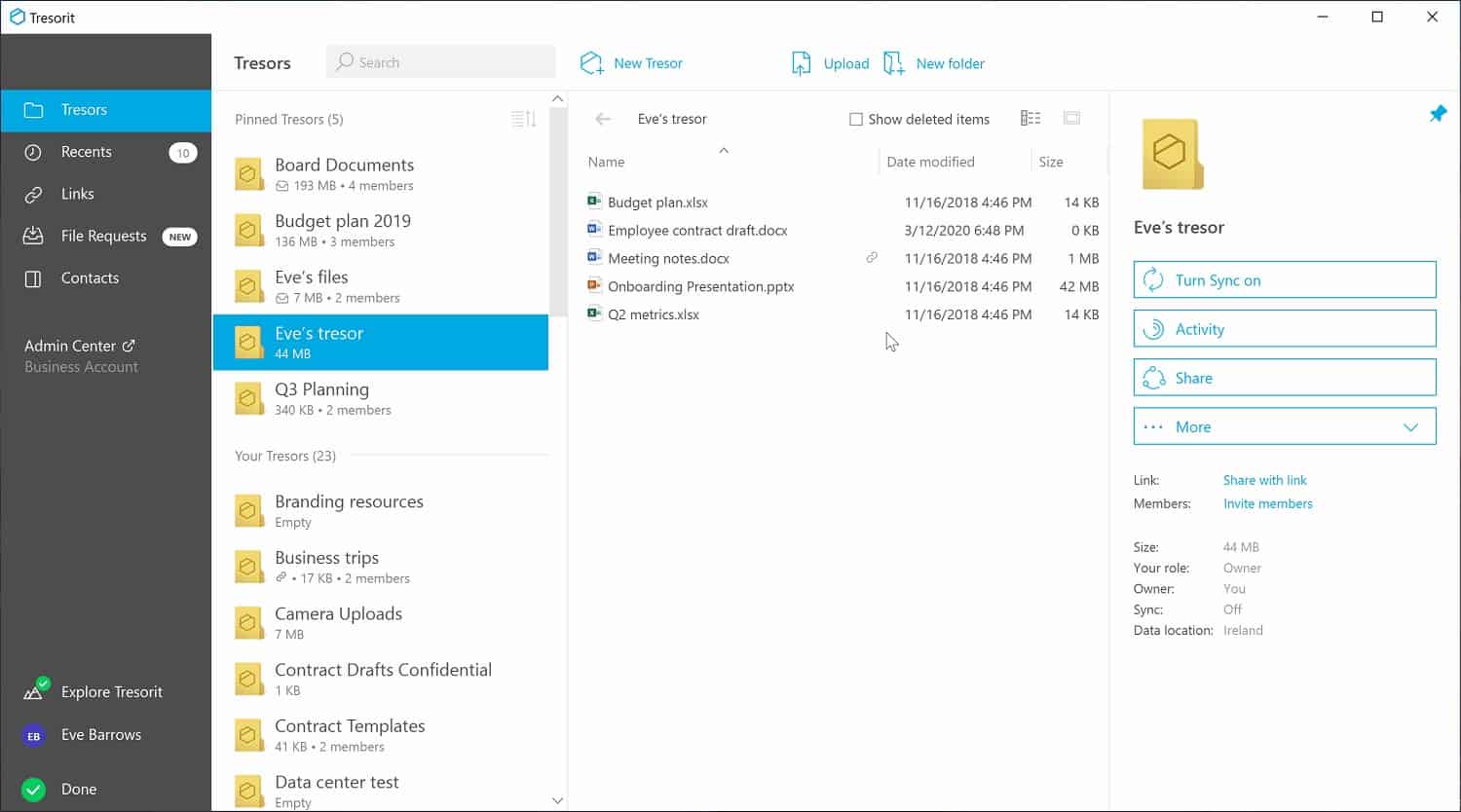
6. Tresorit
Tresorit is a file server platform based in the cloud. The service is based on cloud storage space with three editions. The Business Standard users get 1TB of space and Business Plus users get 2 TB. The highest plan, called Enterprise is a tailored plan. Whichever plan you choose, that space is encrypted for protection and access requires login credentials that include multifactor authentication.
Key Features:
- Secure System: Uses very strong encryption
- Create Files Spaces for Users: User-owned directories
- Backup Local Files: Can be used for synching
Why do we recommend it?
Tresorit is another system that provides a corporate cloud drive. You can share files by transferring them with a secure FTP system or by just letting others access the file on the server. The user can decide on the permission level that others will get and shared directories for projects are also possible.
Each file stored on the Tresorit server is encrypted individually, each with a different key, so a user can’t get access to any file without specific permission. That encryption takes place before the file is uploaded and uses a 256-bit AES cipher. The file’s encryption gets regenerated with a different key every time the file is changed or when the group of users permitted to access it changes.
Users are invited to access a file through a list of email addresses of permitted accessors. Each directory is called a tresor. It is a sync file that exists both on the owner’s device and on the Tresorit server. A tresor is encrypted by 4096-bit RSA public key encryption in both local and remote locations.
Permission can be graded to allow or block editing and access rights can easily be revoked both by the file owner and by the system administrator. Users grant access to colleagues and outsiders through their email addresses. The system tracks the status of files and, if any changes are made by anyone other than the owner, a message is generated to notify the owner and also write an entry into a log file.
The same processes that protect uploaded files are also applied to email attachments. Those get uploaded to the Tresorit server and then referenced by a secure link that gets written into the email. Uploading and file viewing are protected by TLS.
Who is it recommended for?
Tresorit is a good collaboration service for team-driven document development. Business plan changes are levied at a subscription rate per user per month, which makes this a particularly good choice for growing businesses. The minimum team size for a Tresorit account is three members.
Pros:
- Unbreakable Protection: 256-bit AES for storage and 4098-bit RSA for transfers
- Accountability: Individual user accounts to aid security controls and identify the origin of file actions
- Scans Emails: Removes attachments and replaces them with links
Cons:
- Email Protection isn’t a Core Module: Costs extra
You can assess the Tresorit system on a 14-day free trial.