In today’s digital world, cyber threats evolve faster than ever. Back in the day, companies only needed basic tools and strategic planning to keep intruders out of their systems. But today, with the rise of network complexity, where everything is connected through the internet, outmaneuvering cybercriminals is a challenge.
Protecting your digital infrastructure is no longer an option. To survive and stay ahead of competitors, organizations must invest in Security Operations Center (SOC) tools for real-time visibility, control, and response to cybersecurity incidents.
What is SOC?
SOC stands for security operations center, a centralized hub that performs continuous surveillance of the IT infrastructure. Earlier, SOC looked more like a room filled with large screens and a team of security experts. But, today things have changed, or say, upgraded. Now, even one person is enough to handle the intensity of modern threats. The advanced tools and technology support provided by the security team can help counter the growing complexity of cyberattacks. A SIEM tool is among the most basic technologies that make up a SOC’s core.
But what has resulted in such a high demand for these tools? What are the pain points that are pushing businesses to invest in SOC tools at a rapid pace?
Be it small or large enterprises, IT experts are finding it hard to protect their sensitive data, transactions, and systems. Some other key pain points that are driving the growing demand for SOC tools are:
- Your team is flooded with alerts every day, but most of them are false positives, making it difficult for the security team to figure out real threats in time.
- Your business has invested in several security tools, but none of them collaborate or talk to each other, leading to visibility gaps and slow response.
- Your logs and data are too scattered across different systems, resulting in more time to investigate a security incident.
- You are expected to meet strict compliance requirements but pulling manual audit reports is time-consuming.
- Cyber threats are getting more advanced, but your team is already busy handling identified threats and can’t keep up with the volume or complexity.
- You know attacks are happening outside your working hours, but without round-the-clock monitoring, managing threats is challenging.
By investing in the right SOC tool, businesses can overcome these challenges and better monitor everything happening across systems. With these tools in practice, security analysts or cybersecurity professionals will be able to detect, analyze, and respond to threats in real-time. But, there are multiple tools available in the market, making it harder for buyers to compare and choose the right one.
To ease the process, our team of experts has researched and reviewed some of the best SOC software tools. Investing in any of these tools will not only enable your team members to secure data and systems from threats but also respond to threats in real time and stay ahead of cybercriminals.
Our goal is to help you find SOC software that keeps your business protected from threats and stops attacks before they cause damage.
Here is our list of the best SOC software tools:
- ManageEngine Log360 EDITOR’S CHOICE This large bundle of services includes a SIEM, a threat intelligence feed, UEBA, file integrity monitoring, AD auditing, log management, compliance reporting, and a SOAR service. Runs on Windows Server. Start a 30-day free trial.
- LogRhythm SIEM (formerly LogRhythm XDR Stack, now part of Exabeam) A combination of four layers of security that ranges from endpoint protection through to automated threat response. They are offered as a cloud service, as an appliance, or as on-premises software.
- Rapid7 Insight Platform A bundle of cloud-based automated security services with on-site agents, including threat detection and automatic response.
- Heimdal Threat Hunting and Action Center This SaaS platform provides coordinated threat protection across all the endpoints of an enterprise with hybrid cloud/local threat detection.
- Trend Vision One – Security Operations (formerly XDR) A package of coordinating cybersecurity tools that include a SIEM, email security, and threat response. This is a cloud-based system.
- Exabeam New-Scale SIEM A cloud-native next-generation SIEM that includes threat intelligence and automated threat response.
If you need to know more, explore our vendor highlight section just below, or skip to our detailed vendor reviews.
Best SOC software tools highlights
Top Feature
Unifies logs alerts dashboards and threat intelligence to strengthen SOC posture
Price
Negotiated pricing
Target Market
Small to mid size enterprises looking for a security solution that is easy to manage and helps audit security events and mitigate attacks in real time
Free Trial Length
30-day free trialAdditional Benefits:
Features:
Top Feature
Leverages AI behavior analytics and automates incident response workflows
Price
Negotiated pricing - No pricing information, demo and quote available
Target Market
SMBs and enterprises needing enterprise grade SIEM with advanced analytics, integrated XDR, automated workflows, and faster response
Free Trial Length
Demo available
Read more ▼
Top Feature
Eliminates asset inventory blind spots and prioritizes risk remediation
Price
InsightIDR starts at $5.89 per asset per month
Target Market
Organizations focused on discovering, prioritizing, and managing vulnerabilities and attack surfaces
Free Trial Length
Free trial available, demo available upon request, duration not disclosed by the vendor
Read more ▼
Top Feature
Tracks users and endpoints, hunts anomalies, prioritizes high risk actions, triggers response
Price
Instant online price estimate available, final pricing negotiated with a sales representative
Target Market
Security teams needing proactive threat hunting with one click remediation and visual analytics
Free Trial Length
14-day free trial available, demo available upon request
Read more ▼
Top Feature
Unifies XDR Agentic SIEM and Agentic SOAR, correlates signals across email endpoint server cloud and network to track complex attacks and speed detection and response
Price
Negotiated pricing
Target Market
Enterprises and SOC teams looking for extended detection across endpoint server email network and cloud, with automated correlation
Free Trial Length
30-day free trial, live demo available upon request
Read more ▼
Top Feature
Scalable AI powered modular platform integrating SIEM UEBA SOAR insider threat tracking and compliance
Price
Negotiated pricing
Target Market
Organizations of any size seeking a modern SIEM enriched with UEBA SOAR and AI automation
Free Trial Length
Demo available upon request, duration not disclosed by the vendor
Read more ▼
A Security Operations Center (SOC) is a dedicated facility or team within an organization responsible for continuously monitoring, detecting, analyzing, and responding to cybersecurity threats and incidents. The primary goal of a SOC is to safeguard an organization’s digital infrastructure, assets, and sensitive data by proactively managing and mitigating security risks. SOC teams use a combination of people, processes, and technologies to ensure rapid detection of security threats and efficient incident response.
The core tasks of a SOC include:
- Threat Monitoring: Continuously monitoring network traffic, endpoints, servers, and systems for suspicious activities or potential security breaches.
- Incident Detection: Identifying and analyzing security incidents, such as malware attacks, unauthorized access, or data breaches.
- Incident Response: Coordinating the response to security incidents, including containment, investigation, and remediation.
- Threat Intelligence: Collecting and analyzing threat intelligence to stay ahead of emerging cyber threats.
- Vulnerability Management: Identifying and addressing system vulnerabilities that could be exploited by attackers.
- Reporting and Compliance: Ensuring compliance with industry standards and regulations by generating security reports and maintaining audit trails.
While larger organizations typically operate an in-house SOC, outsourcing is also a viable option for many businesses, especially smaller or mid-sized ones that lack the resources for a full-scale internal team. Managed Security Service Providers (MSSPs) offer outsourced SOC services, providing round-the-clock monitoring and incident management at a lower cost. Outsourcing a SOC can offer expert-level security management without the need for maintaining an in-house team, making it an attractive option for many organizations.
SOC tools
The type of tools you need for your SOC depends on the size of your operations. The core systems a SOC needs are security monitoring systems. If you have a team working in the SOC, you will also need team management systems and incident management tools. If you run a small enterprise and leave security monitoring to automated software, then you should look for detection and response systems tied up in one bundle.
This is a long list of tasks. However, there are cybersecurity software bundles available that provide all of these services. A good indicator of a competent SOC package is the term “XDR.” This stands for “extended detection and response.” An XDR package could be bundled around an endpoint detection and response (EDR) system, which itself is an advancement on the original antimalware systems that formed the mainstay of IT security systems back in the day. Other XDR packages start around SIEM tools. SIEM has the added advantage of providing log management, which is essential for businesses working to a data privacy standard, such as PCI DSS or HIPAA.
Key points to consider before purchasing a SOC Software Tool
Continuous monitoring and protection of your system and data has become a necessity with the rise of cybercrime. Investing in the right SOC software tool can help strengthen security posture. But, how to find one? Choosing from a variety of tools in the market offering similar features makes it challenging to compare and determine which one aligns best with your security goals and business needs. Hence, we have listed a few pointers that will ease the evaluation process for buyers:
- Threat Detection and Incident Response: One of the key features of SOC software tools is its ability to detect threats in real-time. The tool must be capable enough to analyze security events, trace risk issues, and send immediate alerts to security teams on discovering anomalies. Further, it must have an automated response mechanism that instantly blocks malicious activities from exploiting systems. Thus, helping organizations to reduce downtime and minimize security risks.
- Efficient Log Collection and Smart Correlation: SOC performs major analysis on the logs collected by the system for detecting threats and incident analysis. It is important to check if your selected SOC software tool can collect log data from different sources, i.e., cloud applications, network devices, firewalls, etc. A tool with log correlation capability allows security teams to identify security weaknesses or threats in real-time. It further helps find patterns and insider threats within the system.
- Seamless Integration with Your Security Tools: Most companies use different sets of security tools to stay protected and secure. For example, some companies invest in cloud security tools, endpoint protection tools, etc. Now, when you decide to invest in another security tool, i.e., SOC software tool, make sure it supports integration with other security solutions. Compatibility with other existing tools allows team members to monitor threats from a single console.
- Scalability: A lot of security data is generated by organizations on a daily basis. Hence, choose a SOC software that can grow with your organizational needs, i.e., it is capable of handling more logs and data in the future without compromising on speed. Scalable SOC tools help security teams keep up with threats as the business grows.
- Advanced Threat Detection with AI and Intelligence Feeds: Threat intelligence integration is another key aspect that security teams must look for in the tool selection process. This feature enables team members to collect real-time threat feeds that help them stay updated about fake IP addresses, known attack patterns, and emerging threats. With AI and machine learning techniques, the tool will further make it easier to analyze historical data, spot unusual behavior or patterns, and reduce false positives.
- Automated Compliance Reporting: To keep data safe, following GDPR, HIPAA, and PCI DSS strict cybersecurity regulations is mandatory. Security software used in a Security Operations Center (SOC) should help businesses follow these rules. The software allows team members to automatically create reports that show the company is meeting security requirements. In fact, by using this software, businesses don’t have to do all the checking and reporting by hand—it helps them stay compliant with less effort.
- Pricing and Licensing: Each tool has a different pricing structure and feature availability. Make sure to compare each tool and its total cost before finalizing a product. Some platforms or vendors even offer free trial sessions to test the product and ensure it meets your business needs.
- Support and Documentation: Having the essential features is not only what a buyer must focus on. Instead, it is important to check the support services offered and user community resources. Access to detailed documentation and active community after the post-purchase acts as a great deal.
To dive deeper into how we incorporate these into our research and review methodology, skip to our detailed methodology section.
The best SOC software tools
If you want to combine your security monitoring requirements with general system management, you are into SecOps territory. You should get a security package that will monitor everything without much human intervention. You need the system to issue an alert when problems are detected. Knowing that you will be notified tells you that everything is going OK if you don’t receive any notifications. Automated responses also take a lot of responsibility off your shoulders.
Getting a SOC software package saves you time in trialing many different systems for each security monitoring function and works out cheaper.
We have analyzed multiple tools in the market and shortlisted the best ones that can be a great asset for your business. Check our reviewed and recommended SOC software tools. The tool insights shared by our expert team will make it easier to compare and determine the right tool.
1. ManageEngine Log360 (FREE TRIAL)
Best for: Small to mid-size enterprises looking for a security solution that is easy to manage and helps audit security events and mitigate attacks in real-time must invest in this tool.
Price: On-premises Log360 uses an online calculator with instant quotes at the ManageEngine Store. Pricing scales by number of log sources, domain controllers, file servers, endpoints, and cloud accounts, and the page notes flexible pricing beyond prescribed slabs. Large environments are directed to sales for a custom quote. A 30-day free trial, an online demo, and a personalized web demo are available.

ManageEngine Log360 includes a lot of security monitoring and threat response services. The core of the threat detection service in this package is a SIEM tool. This is paired with its own log manager, which collects data from all endpoints plus third-party applications. The system also has a threat intelligence feed, which provides a blacklist of IP addresses and domains known to be used by attackers.
ManageEngine Log360’s Key Features:
- Comprehensive SIEM Solution: Includes log management and threat detection.
- File Integrity Monitoring: Keeps track of important system files for security.
- Activity Logging: Provides detailed records of system and user activities.
Unique buying proposition
It is an all-in-one security platform that tracks 750+ log sources and combats threats in real-time. Further, the tool supports integration with ServiceDesk Plus and other ticketing tools.
Feature-in-focus: Unifies logs alerts dashboards and threat intelligence to strengthen SOC posture
Log360 consolidates logs, alerts, dashboards, and threat intelligence into one customizable space. What really stands out to users is its ability to address SOC challenges and maintain network security posture.
Why do we recommend it?
ManageEngine Log360 examines user accounts and identifies misuse. Tools in this system include Active Directory auditing scanners that identify unauthorized changes and also assess weak account security, such as open-ended password validity or abandoned accounts. The system is able to track the activity of each user account and generate a baseline of regular activity.
The service also watches all behavior on endpoints and uses that for baselining. The system performs anomaly detection so any deviations from normal behavior raises an alarm. The tool will log unusual activity, particularly in relation to files because the system includes a file integrity monitor.
The package collects activity reports and logs from cloud platforms. Access to cloud services and the usage of cloud packages are governed by a cloud access security broker (CASB). A security orchestration, automation, and response (SOAR) module ties together all of the units in the bundle plus third-party security systems so that responses to detected threats are automatic and coordinated.

Who is it recommended for?
This package makes it onto our list because it is recommended for use by a Security Operations Center. It would also be a good choice for a managed security service provider (MSSP). This is a big bundle of tools that needs a team to manage. It isn’t suitable for small businesses.
Pros:
- Extensive Log Management: Covers a wide range of log sources and types.
- Integrated Threat Intelligence Feed: Enhances security awareness and response.
Cons:
- Complex Setup: May require significant time and resources to fully deploy.
ManageEngine Log360 provides compliance reporting for PCI DSS, GDPR, FISMA, HIPAA, SOX, and GLBA. The software package for the bundle runs on Windows Server and you can access it with a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Log360 is our top pick for a SOC software tool because it provides a comprehensive SIEM service that is designed to help security teams monitor, detect, and respond to threats in real time. It integrates capabilities like log management, user behavior analytics, and event correlation, making it a strong candidate for use in Security Operations Centers (SOCs). One of its core strengths is centralized log management, allowing SOC analysts to collect and analyze logs from diverse sources such as servers, applications, firewalls, and cloud services. This aids in threat detection and compliance reporting. Log360’s real-time event correlation feature is particularly effective in detecting anomalies by linking disparate security events and generating actionable alerts. The tool also offers robust user behavior analytics (UBA), which helps identify insider threats or compromised accounts by monitoring deviations from normal user activity. Furthermore, its automated threat detection and response capabilities, including workflows for security incidents, enhance the SOC’s efficiency in mitigating potential breaches.
Download: Get a 30-day free trial
Official Site: https://www.manageengine.com/log-management/download.html
OS: Windows Server
2. LogRhythm SIEM (formerly LogRhythm XDR Stack, now part of Exabeam)
Best for: SMB or large enterprises who are looking for a comprehensive security solution that offers powerful detections, automated workflow, and faster response must invest their time, money, and energy into this tool. Larger enterprises needing enterprise-grade SIEM with advanced analytics and integrated XDR might also find it useful.
Price: No information related to the pricing structure is available on the portal, but buyers have the option to get a demo session or submit quote requests to the sales team.

LogRhythm SIEM (formerly LogRhythm XDR Stack, now part of Exabeam) is a SaaS package that is built around a SIEM. As the processing module of the SIEM is based in the cloud, the system needs onsite elements to gather log data and upload it. This configuration leads to the concept of a stack.
LogRhythm SIEM Key Features:
- Modular Security Platform: Offers customizable security components.
- Behavior Analytics: Employs advanced analytics for threat detection.
- Integrated SIEM: Provides comprehensive security event management.
Unique buying proposition
A fully integrated platform combining SIEM, file integrity monitoring, and machine learning–based behavioral analytics. The platform helps translate complicated data into language that is useful for security.
Feature-in-focus: Leverages AI behavior analytics and automates incident response workflows
For users looking to detect hidden threats, having AI and advanced behavior analytics features is particularly important. Further, the platform supports 100s SmartResponse™ plugins that automate incident handling.
Why do we recommend it?
LogRhythm SIEM is a cloud-based SIEM. It installs agents on monitored systems, which collect log files and upload them to the threat-hunting module. Automated responses are implemented through SOAR, allowing the tool to interact with third-party products such as firewalls and access rights managers to block malicious activity.
SIEM systems combine log file analysis with live network monitoring. The strategy aims to spot anomalous behavior either in network traffic or on endpoints. The endpoint agent that gathers logs and uploads them to the LogRhythm server is called UserXDR, and the network monitor is called Network XDR.
The SIEM is divided into a log consolidator, called AnalytiX, and a threat detection system called DetectX. The DetectX system uses AI-based UEBA and a threat intelligence feed to identify a possible intrusion. That threat intelligence is collated from shared experiences of other LogRhythm XDR clients. The threat response is provided by RespondX, which uses SOAR to interact with other services, such as Active Directory and firewalls, to shut down hacker activity.

Who is it recommended for?
LogRhythm SIEM is an almost entirely cloud-based system. The package has almost no footprint on local systems – unlike Falcon, which has the Prevent module that can operate autonomously. The LogRhythm SIEM system could be disabled by malware that disconnects a target computer from the internet.
Pros:
- Cloud and On-Premises Flexibility: Supports various deployment options.
- Advanced Threat Detection: Utilizes modern technologies for security insights.
Cons:
- Requires External Security Tools Integration: Additional effort needed for complete protection.
LogRhythm SIEM is available as IaaS (Infrastructure as a Service) on the cloud, as on-premises software for Windows Server, or as a network appliance. In any of these options, the package offered by LogRhythm will provide you with all of the SOC tools you need to keep your system secure.
3. Rapid7 Insight Platform
Best for: Organizations focused on discovering, prioritizing, and managing vulnerabilities and attack surfaces must give this tool a try.
Price: InsightIDR starts at $5.89 per asset per month; buyers can request a demo on the official site. A free trial is also available.

Rapid7 Insight provides a bundle of security systems that supply a complete set of SOC tools. The core of this package is a SIEM system called InsightIDR, which is delivered from the cloud. IDR stands for Incident Detection and Response. The system requires agents to be installed on-site to gather log messages and upload them to the Rapid7 server.
Rapid7 Insight Platform’s Key Features:
- Cloud-Based SIEM: Streamlines security event management.
- Automated Detection and Response: Enhances overall security posture.
- Integrated Security Services: Offers a range of complementary security tools.
Unique buying proposition
From a buyer’s standpoint, Rapid7 Insight Platform is a perfect option for businesses as it offers internal and external attack surface visibility with vulnerability data. Allowing businesses to get a complete 360° view of risk.
Feature-in-focus: Eliminates asset inventory blind spots and prioritizes risk remediation
During our hands-on testing, we found that the Rapid7 Insight Platform helps find and eliminate blind spots from both internal and external asset inventories. It even enriches intelligence to prioritize remediation efforts efficiently.
Why do we recommend it?
Rapid7 Insight is almost identical to LogRhythm SIEM in that local agents upload log files for threat hunting in the cloud and responses are implemented by SOAR. Both systems also use user and entity behavior analytics to spot anomalous behavior and detect zero-day attacks.

InsightIDR collects log messages and consolidates them into a standard format. It then applies UEBA to register normal patterns of behavior on the monitored system. Deviations from this norm raise alerts and trigger closer scrutiny of a user account, a device, or traffic from a particular IP address. The system also uses a database of known hacker attack strategies called Attack Behavior Analytics (ABA).
The attack response mechanism in the InsightIDR system is called Insight Connect. This uses SOAR methods to coordinate mitigation actions, such as blocking an IP address or suspending a user account.
Who is it recommended for?
Potential buyers of Rapid7 Insight should also consider Falcon Insight and LogRhythm SIEM as three very similar products. Of these three, Falcon is probably a stronger candidate because it can continue to operate on endpoints that are cut off from the local network and the internet.
Pros:
- User-Friendly Interface: Simplifies security monitoring and management.
- Flexible Deployment Options: Adapts to different organizational needs.
Cons:
- Potentially Overwhelming for Small Teams: Extensive features may require dedicated resources.
The Insight platform also includes InsightVM, a vulnerability manager that scans all devices on a network and its endpoints, looking for weaknesses that hackers exploit. If you use cloud services, you would also subscribe to DivvyCloud, which protects cloud-based assets. Another SOC tool that could be of interest to you is Insight AppSec, which monitors DevOps environments.
4. Heimdal Threat Hunting and Action Center
Best for: Security teams needing proactive threat hunting with one-click remediation and visual analytics might find it a suitable option.
Price: Buyers can get an instant online price estimate (final pricing is negotiated with a sales representative); a 14-day free trial is available, and a demo can be requested.

Heimdal Threat Hunting and Action Center operates from a cloud server but installs agents on monitored endpoints. These agents are available for Windows, macOS, and Linux.
Heimdal Threat Hunting and Action Center’s Key Features:
- Anomaly Detection: Identifies unusual patterns indicating potential threats.
- Automated Responses: Quickly reacts to identified security issues.
- Security Consultancy Advice: Offers expert insights for security enhancement.
Unique buying proposition
In my professional opinion, Heimdal’s Extended Threat Protection engine is a unique buying proposition. It allows security teams to perform real-time monitoring, and threat hunting, respond to modern cyber threats, and offer instant action.
Feature-in-focus: Tracks users and endpoints hunts anomalies prioritizes high risk actions triggers response
The tool offers full visibility and allows team members to track user and endpoint activity, hunt anomalies, and take immediate action. Further, determine risk events in advance and rank high-risk actions, like advanced threats and suspicious user logins.
Why do we recommend it?
There are three layers to the Heimdal Threat Hunting and Action Center solution. The agent is the first of these – it uploads local event data to the cloud server for threat hunting. That cloud server is the second element and it sends response instructions to the endpoint agents when a threat is detected. The third element is the security consultancy team, who will advise you on ways to fine tune your automated security policies.
The cloud server standardizes all of the log messages that device agents send so that they are in a common format. It then performs its threat hunting on this standardized data. The package will indicate a threat with an alert and optionally send instructions to endpoint agents to block the threat.

The server identifies each user account, external source, and endpoint and records a pattern of regular activity in each dimension. If a user suddenly does something different or if an endpoint shows unusual activity, the Heimdal system registers a security event. This strategy is called user and entity behavior analytics (UEBA).
The Heimdal system is able to coordinate with third-party security tools such as access rights managers and firewalls. This interfacing is used both to gather event data and also to shut down threats.
Who is it recommended for?
Heimdal Threat Hunting and Action Center is a flexible package that is finalized through a consultation. The involvement of the Heimdal technicians can be increased according to the client’s requirements. Therefore if you have your own technicians on the payroll who have good system administration skills but weak cybersecurity knowledge, this plan would be a good fit.
Pros:
- Cross-Platform Agents: Compatible with Windows, macOS, and Linux.
- Cloud-Based Operations: Enhances accessibility and data management.
Cons:
- No On-Premises Server Option: May not suit organizations with specific on-premises requirements.
Heimdal Security provides a platform of tools and the Threat Hunting and Action Center is not the company’s only product. The typical way to identify your business’s exact requirements is to start with a consultation with Heimdal Security experts. You can access a free demo.
5. Trend Vision One – Security Operations (formerly XDR)
Best for: Enterprises and SOC teams looking for extended detection across multiple layers, including endpoint, server, email, network, and cloud, with automated correlation.
Price: Buyers can start a 30-day free trial, book a live demo, or request pricing via the official portal (no public price list).
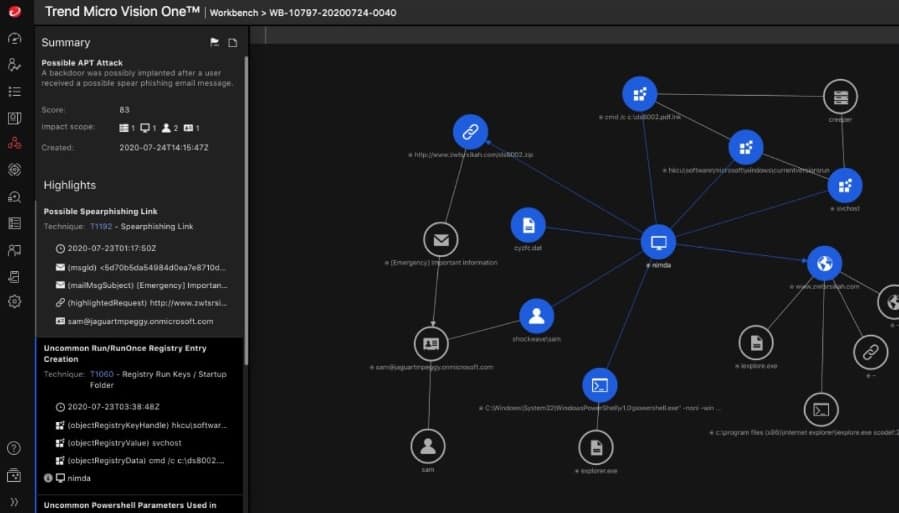
Trend Micro delivers a SecOps platform that unifies XDR, Agentic SIEM, and Agentic SOAR. The platform is cloud-delivered with on-site sensors and agents that collect telemetry and upload it. Those agents also execute response actions coordinated by SOAR. XDR for Cloud monitors and protects assets in your cloud accounts, including detections from cloud activity logs.
Trend Vision One – Security Operations Key Features:
- Unified XDR and SIEM capabilities: Provides thorough security event analysis.
- Hybrid Environment Support: Protects both on-premises and cloud assets.
- Customizable Detection Rules: Tailors security to specific organizational needs.
Unique buying proposition
Advanced users will appreciate that the tool correlates signals across email, endpoints, servers, cloud workloads, and networks to track complex, multi-layered attacks. Machine learning and an AI-powered SIEM help identify anomalous behavior and speed detection and response.
Feature-in-focus: Detects threats across endpoints servers networks and cloud for faster investigations
Combines deeper endpoint and server protection with cross-layer correlation to detect threats across devices, servers, networks, and cloud, enabling shorter detection time and faster root cause analysis.
Why do we recommend it?
Trend Micro Vision One correlates activity across email, endpoints, servers, networks, and cloud to surface complex attacks and speed investigations. It provides both user and device context in one console.
Whether operating on your site or in your cloud account, sensors and agents collect log messages and compile statistics on system activity. These information feeds are uploaded to Trend Micro and consolidated to provide a data source for the SIEM and XDR workflows.
The SIEM operates a threat detection system, which looks for indicators of compromise. A typical indicator would involve a sequence of suspicious events. So, one action doesn’t automatically trigger an alert. Instead, the SIEM will pay extra attention to the activities of the user account involved in that action to see whether a follow-on action occurs that is expected from a hacker attack. If enough related actions occur that match a known chain of attack, the system triggers a response.

The threat response is communicated from the SIEM to the monitoring modules, which then either perform their actions or communicate with an access rights manager and firewalls to block hacker activity.
Who is it recommended for?
As already observed, Trend Micro Vision One is a good choice for enterprises and SOC teams needing unified detection and response across email, endpoint, server, network, and cloud. This includes hybrid environments and cloud workloads, which benefit from correlated telemetry and coordinated response.
Pros:
- Cross-layer coverage: Correlates data across email, endpoint, server, cloud, and network for stronger detection.
- Comprehensive Cloud Protection: Safeguards cloud-based assets effectively.
Cons:
- No public pricing: Buyers must contact sales.
Trend Micro’s SOC support system is available in two formats. The first is Trend Vision One Security Operations, a cloud-delivered SecOps platform. The system is also available as a managed service, Managed Detection and Response (MDR), which provides 24×7 monitoring and incident response by Trend’s team.
6. Exabeam New-Scale SIEM
Best for: Organizations of any size seeking a modern SIEM enriched with UEBA, SOAR, and AI automation might find Exabeam New-Scale SIEM an ideal choice.
Price: The tool offers no public pricing information. Instead, buyers can request a demo or contact sales on the official page.

Exabeam offers a Security Operations platform that is built around a cloud-native SIEM (New-Scale SIEM). As with other SOC packages on this list that operate on the SIEM model, this bundle includes off-site processing with onsite data gathering via Cloud Collectors and Site Collectors. The Exabeam system processes log messages, so it is also a log management and analytics layer (Data Lake) that helps data privacy standard compliance reporting by laying down an audit trail. Data retention and archive options are available (for example, Cloud Archive and long-term storage).
Exabeam New-Scale SIEM Key Features:
- Cloud-native SIEM Solution: Offers a centralized approach to security.
- Compliance Reporting: Assists in meeting various regulatory standards.
- Log Management: Keeps detailed records for analysis and reporting.
Unique buying proposition
It is a scalable Security Operations platform that is AI-powered and modular, integrating SIEM, UEBA (behavior analytics), SOAR (Incident Responder playbooks), insider threat tracking, and compliance.
Feature-in-focus: Automates investigations with Stateful User Tracking and Smart Timelines
Exabeam Nova is a built-in AI assistant that automates routine investigations. It helps SOC analysts concentrate on actual threats by creating stateful user sessions and automatically building Smart Timelines.
Why do we recommend it?
Exabeam describes its solution as a SIEM. However, it is very similar to the XDR products on this list. This demonstrates the blurred line in the definition of these two categories of cybersecurity services. Like CrowdStrike, Rapid7, and LogRhythm, the package ingests telemetry via Cloud Collectors and Site Collectors and integrations with third-party tools, and uploads data to a cloud-delivered platform for detection and investigation. The Exabeam also deploys UEBA in Advanced Analytics, including Stateful User Tracking and Smart Timelines, for fine-tuned baselining.
All of the information that the Cloud Collectors and Site Collectors upload to the Exabeam server is called the Exabeam Data Lake. The Data Lake provides the source material for the Exabeam Advanced Analytics module. This is the threat hunting element of the SIEM. It deploys UEBA (including Stateful User Tracking and timelines) to watch for abnormal behavior. The Exabeam Data Lake is also available for manual examination through Data Lake Search and New-Scale SIEM search in the Exabeam console. This allows you to sort, group, and filter records for your assessments.

The console for Exabeam can be accessed through any standard browser and centralizes reporting, dashboarding, and case management. It displays live statistics and indicators as new log messages arrive, with dashboards and reports you can customize. The console includes Incident Responder playbooks and actions that allow you to specify the degree of response automation you are comfortable with. It is possible to set specific events to trigger automated responses while others generate notifications to give you the option of dealing with those situations manually, using triggers or running actions on demand.
The Exabeam Incident Responder implements automated responses. Fine-tuning the actions of the Incident Responder gives you control over your own business’s SOC strategy. The system works with playbooks. Several pre-written playbooks are built into the Exabeam service, but you can create your own or decide which of those provided playbooks to activate. A playbook is a workflow that links triggers and actions. Typically, a response involves SOAR workflows that integrate with third-party tools to block hacker activity.
Who is it recommended for?
Businesses that are interested in a cloud-native SIEM and behavioral analytics platform should consider Exabeam alongside LogRhythm, Rapid7, and CrowdStrike for the protection of office networks from attack and to root out advanced persistent threats.
Pros:
- Advanced UEBA: Utilizes behavior analytics for sophisticated threat detection.
- Log Archiving: Manages large volumes of log data effectively.
Cons:
- May Require Extensive Customization: To fully leverage all features.
Exabeam offers a demo upon request.
Our methodology for choosing SOC Software Tools
Investing in the SOC (Security Operations Center) software tool has become essential for businesses to stay protected and secure in the evolving world of threats and cyberattacks. But how can one decide which one is the right tool when thousands of software guaranteeing similar benefits are available in the market?
Selecting the right security tool in such a case can be challenging. Hence, we have listed some key pointers that will help ease the tool evaluation process and help businesses or buyers to make informed decisions.
1. All-in-One Security Coverage
It is essential to verify that your selected SOC tool does not focus solely on one security aspect. Instead, it provides an automated system that covers all critical areas. Whether it is threat detection, prevention, or response, the tool comes with all the capabilities. Further, include log management, vulnerability scanning, and endpoint security to reduce dependency on multiple vendors.
2. Real-Time Alerts and Notifications
Businesses can prevent damage with real-time updates or alerts on suspicious activities. SOC tools are one of those options that guarantee the delivery of real-time alerts and notifications. This functionality within the tool further helps reduce the impact in case of a breach.
3. Network and Endpoint Protection
Another feature that buyers must look for in a SOC software tool is its ability to secure both network infrastructure and endpoint devices. Make sure the tool provides comprehensive protection across servers, desktops, mobile devices, and cloud environments. Further, eliminates any weak link in the security system.
4. Integrated Log Management for Compliance
Compliance with standards such as PCI-DSS, ISO 27001, and HIPAA requires detailed event logs. Strong log management features that facilitate auditing and guarantee your company complies with legal standards without adding complexity should be included in SOC software.
5. Vulnerability Scanning and System Hardening
Vulnerability scanning and system hardening are essential components of effective SOC solutions. Your overall security posture is strengthened by seeing possible vulnerabilities before they are exploited and implementing recommended security configurations.
6. Free Trial or Demo Availability
It is essential to verify the tool’s usefulness and compatibility with your environment before investing. Teams can confidently assess the performance and functionality of SOC software without having to commit to payment if it provides a free trial or demo setup. So, look for this key feature in your selected tool.
7. Consolidated Security Suite
Choose a SOC platform that provides a valuable set of integrated tools rather than piecing together multiple products. This cohesive strategy minimizes the total cost of ownership, improves feature coordination, and reduces complexity.
8. Support and documentation
Investing in a tool with little or no experience can put you in trouble. However, most companies provide assistance and comprehensive documentation to help you in difficult times post-purchase. Make sure you are choosing software that offers appropriate support services.
Broader B2B Software Selection Methodology
Apart from focussing on the benefits and features a tool/product can offer, our professional team also covers other areas to evaluate a product. For instance, when selecting a B2B software for our readers, we even share insights collected about the company behind the product. It is important to check the support services offered by each platform as it will play an important role in the future post-purchase.
So, every time our team reviews a software or product, it makes sure that the following points are given attention.
- Check whether the price of the product is suitable and offers proper value in return to solve real business problems.
- Evaluate the product or software scalability. Measuring this criterion gives an idea that the product has the potential to scale in case of business expansion or growth.
- User feedback and testimonials related to the software, services, and company are taken into consideration to measure overall satisfaction level.
- Check how responsive and active the support staff is on receiving concerns or suggestions from the buyer or user.
- Review the limitations and advanced features that come with each product.
Just a quick reminder that not each product review covers all areas. Our team highlights only the relevant and insightful updates with the buyer. For more information on the evaluation process by the Comparitech team, we recommend visiting the B2B software methodology page.
Why Trust Us?
For years, Comparitech has been trusted as one of the best sources for high-quality product reviews and software tools. In fact, to make it easier for buyers to choose one tool from a thousand options available, our team of cybersecurity experts and software testing professionals have been sharing their practical experiences and vendor insights.
Our experts do not limit their research to evaluating products based on features and functionalities. Instead, follow well-defined evaluation criteria and customer feedback to deliver accurate, unbiased insights. We understand that a great user experience extends beyond product performance, so we also assess post-purchase customer support. By rating vendors based on the quality of their service, we provide a holistic view that reinforces our role as a trusted, all-in-one resource for expert software guidance.
SOC software tools FAQs
What is a SOC tool?
A Security Operations Center requires tools that collect system activity intelligence, search for malicious activity, and provide automated responses or advice for manual intervention. The types of security packages that achieve these goals include SIEMs, vulnerability managers, intrusion detection systems, and compliance reporting services.
Is SOC same as Siem?
A Security Operations Center (SOC) is an IT asset protection service that should be built into the tasks performed by your IT department. This service requires the collection and examination of system data to identify threats and a SIEM tool performs these actions. Therefore, a SOC isn’t the same as a SIEM, but it needs a SIEM.
Can you have a SOC without a SIEM?
A Security Operations Center (SOC) needs to gather system activity data and search it for signs of intrusion or malware movements. These actions are exactly the services performed by a SIEM. Therefore, a SOC can exist without a SIEM but it will need a suite of replacement tools to perform those data gathering and searching functions.









