We hear a lot of talk about electronic and internet voting as ways to improve our election processes, but few people understand the underlying techniques that keep these systems safe.
Cryptography is one of the fundamental fields involved in securing both electronic and internet voting. Despite its usefulness, the technical aspects and mathematics of cryptography can’t keep voting systems secure by themselves. Security also requires the right organization, processes, and implementations.
To answer our question of whether or not cryptography can be used to secure electronic and internet voting systems, we first need an understanding of what aspects make up an effective voting system:
- Security – Voting systems need to be secure to prevent attacks and tampering from adversaries, whether they be foreign nations, our own political parties, or other interest groups.
- Accuracy – We need systems to return a result that accurately reflects the way people voted. An impenetrable voting system would be useless if it just guessed the outcome.
- Verifiability – It’s also important to be able to verify that the vote is accurate. Otherwise, the electorate may not trust the result, which could undermine the validity of an election.
- Anonymity – Keeping votes a secret is crucial, because it allows people to vote for who they truly want to. If a person’s vote can be discovered by others, they may be coerced or pressured into voting for a different candidate. People may be paid to vote a certain way, physically threatened, pressured by their peers, or feel that they have to vote a certain way to advance their career.
- Usability – A voting system needs to be easy to use. If it’s too complex, people may refuse to vote, or not be able to cast their vote correctly.
- Speed – The election result needs to be determined within a reasonable timeframe.
It can be difficult to design effective voting systems comes because these aspects are often in conflict with each other. One of the biggest complications involves trying to keep votes anonymous while still being able to verify them.
The easiest way to verify votes would be to keep a public list of how people voted, but this would obviously violate the anonymity of the vote. These trade-offs are what makes it far more complex to secure electronic and internet voting in comparison to systems such as online banking.
Electronic & internet voting: The underlying cryptography
Before we get into the intricacies of voting and how it can use cryptography, let’s go through some of the fundamental cryptographic concepts involved.
Cryptography is especially useful when it comes to finding solutions for security, accuracy, verifiability and anonymity. Various cryptographic techniques can be used to produce three major properties that are particularly useful in voting systems:
- Confidentiality – This involves keeping information a secret from unauthorized parties. It is generally achieved through encryption.
- Authentication – Authentication is the process of validating that an individual is who they say they are, and that any data transfer is truly coming from them. It is often done with digital signatures.
- Integrity – Data’s integrity refers to whether it retains its initial form and hasn’t been tampered with. Data integrity is often also proven with digital signatures.
Encryption
One of the most basic cryptographic techniques is encryption. At its essence, it involves using a code to keep messages secret from adversaries, which gives data the property of confidentiality. Encryption is an ancient technique, first used by the Greeks and other early civilizations.
The first types of encryption were incredibly simple, such as the Caesar cipher, which involves replacing each letter with another according to a prearranged code.
A basic example involves replacing each letter with the one that comes after it in the alphabet. Under this type of scheme, each “a” would become a “b”, each “b” would become a “c”, each “c” would become a “d” and so on.
Using this kind of system, known as an algorithm (or more specifically, a cipher), the message “Buy me a pony” becomes:
Cvz nf b qpoz
When data or a message is encoded with encryption, the original information can only be accessed by those who know or can figure out the code. This keeps the information away from prying eyes, but allows anyone that you have shared the code with to access it.
Over time, we’ve gotten much better at cracking codes, which means that contemporary algorithms need to be incredibly complex in order to keep our data safe from attackers. These days, encryption and decryption are done with computers and a lot of mathematics.
Different types of encryption can be used at many stages of the voting process to help keep the election both secure and anonymous.
Symmetric-key encryption
Symmetric-key encryption is probably the form of encryption that is most familiar to you. It involves taking a message or data, and putting it through a specific algorithm alongside a key, which is a secret value that acts similarly to a password.
Under this type of cryptography, the same key is used in both encryption and decryption. These days, the most commonly used symmetric-key algorithm is AES.
Two major considerations are involved in protecting data with encryption. The first is that an adequately secure algorithm must be used – if you use a weak or outdated one, your adversaries may be able to crack it easily.
The second consideration is that to ensure security, the keys need to be handled appropriately. Encryption keys need to be generated, exchanged, used, and stored in a secure manner, otherwise they may fall into the hands of attackers, who will then be able to access all of your encrypted data.
Symmetric-key encryption is critical in many aspects of secure electronic and internet voting systems. It is involved in securing vote data both at rest and in transit, and in some of the other cryptographic techniques that we will cover later on.
Public-key encryption
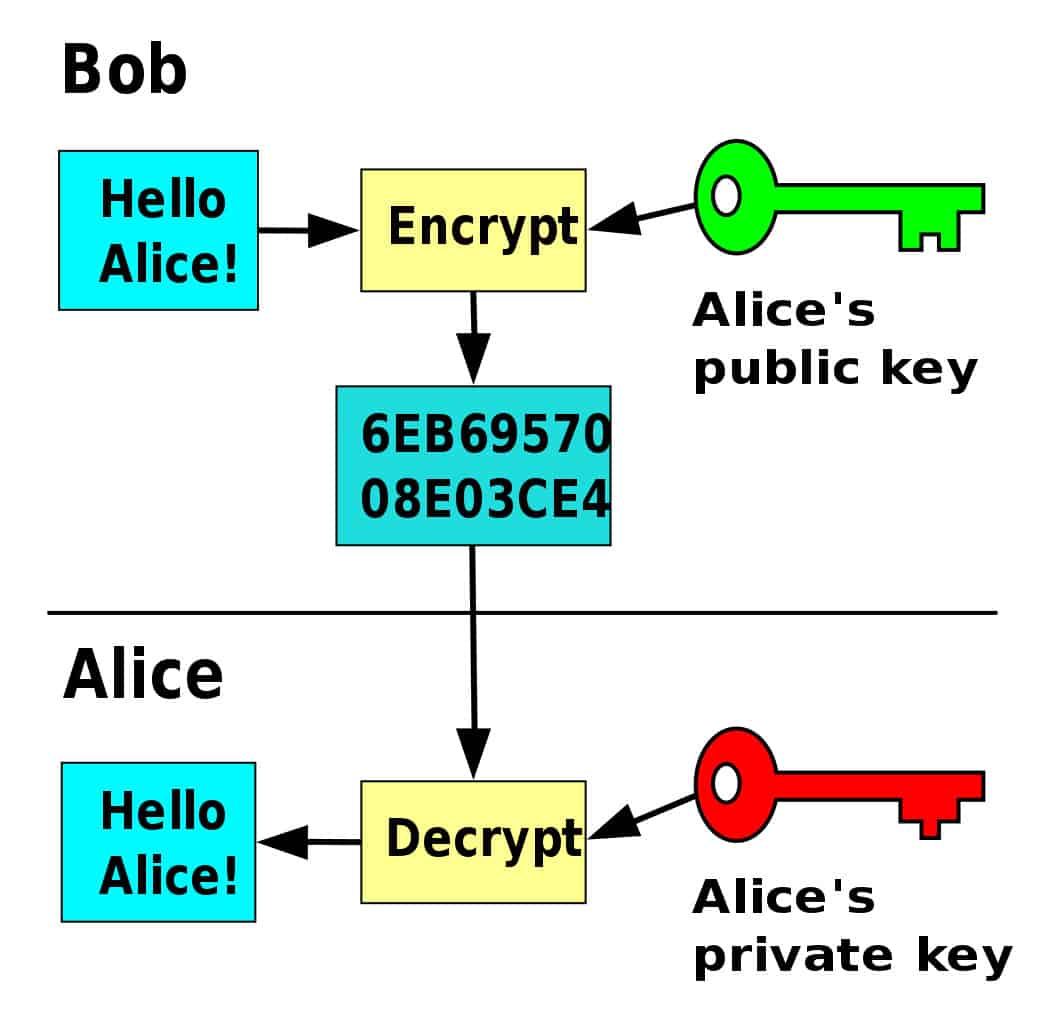
In the 1970s, the cryptography world was shaken up with the development of public-key encryption, also known as asymmetric encryption. New cryptographic systems used two separate keys in the encryption and decryption processes, rather than just relying on a single key for both practices. Public-key encryption uses a public key, which is shared openly, and a private one, which must be kept secret.
One of the main benefits of these systems is that data encrypted by someone’s public key can only be decrypted by the matching private key from the key pair. This interesting feature allows people who have never met before to communicate securely.
Why is public-key encryption important?
Let’s take a step back and return to symmetric-key encryption for a moment. This will demonstrate why public-key encryption was such an important development.
Symmetric-key cryptography has been around for thousands of years, and it’s excellent for safely communicating with someone that you already have contact with. As long as you have a secure channel or can see your intended recipient in person, you can simply tell them which algorithm and key you want to use, then use it to encrypt your future communications.
While this system is incredibly useful in a range of situations, what do you do if you want to communicate safely with someone you have never met before, but you don’t have a secure channel where you can safely exchange the key?
If you don’t encrypt the communications, an attacker will easily be able to access the data. If you encrypt them without sharing the key beforehand, attackers won’t be able to access them, but neither will your recipient.
If you try to share a key with your recipient over an insecure channel, then an attacker could intercept the key and read the subsequent communications. This was one of the biggest problems in cryptography for a long time.
The discovery of public-key cryptography was a big step for the field, because it gave people a way to communicate securely with those that they hadn’t had a chance to exchange keys with beforehand.
Before its development, if you were a spy and needed to send a message to an ally that you hadn’t met before, you would probably have to go to the effort of arranging a face-to-face meeting, which can be dangerous and impractical.
With public-key cryptography, anyone can safely communicate with someone they don’t know, simply by finding their public key. These keys can be found on key servers, personal websites, or even by simply asking the intended recipient. If the person you want to talk to doesn’t already have a public key, then you can ask them to generate a key pair so that you can communicate securely.
Public key algorithms are a crucial part of authorization and digital signatures, which are used quite heavily in both electronic and internet voting schemes.
How public-key encryption is used in practice
To safely send a message or data, you would encrypt it with a public-key algorithm like RSA and the public key of your intended recipient. Once data has been encrypted with someone’s public key, it can only be decrypted by their matching private key. This is due to an interesting quirk in the mathematics involved in these algorithms.
A diagram of how public-key encryption works. Public key cryptography by David Göthberg licensed under CC0
If your recipient wants to reply to you, they can create a message and encrypt the data with your public key, so that it can only be decrypted by your private key. In this way, you can securely communicate back and forward without having to share a key beforehand.
Public-key algorithms like RSA are resource-heavy and slow. In practice, we don’t use them to encrypt the entirety of our communications. Instead, we just use them to encrypt the symmetric key, which in turn encrypts the bulk of the data that is being transmitted. This works out to be far more efficient.
Homomorphic encryption
Homomorphic encryption is an emerging type of cryptography that allows computations to be made on encrypted data. Let’s say you are making a purchase and all of the payment information is encrypted. If the transaction has to be sent to a third party to impose tax, shipping fees, or something else, then the data would typically have to be decrypted if a traditional encryption algorithm is used.
This presents a point of weakness – whenever data is turned back into plaintext, it is exposed and gives attackers opportunities to access it.
One of the main benefits of homomorphic encryption schemes is that you can perform computations on encrypted data – it doesn’t have to be decrypted first. With homomorphic encryption, the transaction data could have the tax added without having to be decrypted first, which eliminates the above-mentioned point of weakness.
Practical homomorphic encryption schemes are still in the relatively early stages of development, however they may eventually have the potential to solve some problems in online-voting schemes. One of the most promising applications of homomorphic encryption is that it could be used to tally encrypted votes without compromising the anonymity of individual voters.
Hashing
Cryptographic hash functions are algorithms that have several distinct properties:
- A given input will always return the same output.
- Outputs are always the same length, no matter if the input is a single comma or the whole Bible.
- The chances of two different inputs returning the same output are so small that we don’t worry about them. For all practical purposes, we consider each output unique to a given input.
- A slight change to the input will lead to a completely different output. If you change even a single letter of the input, the new output won’t look anything like the old one.
- It is not feasible to determine the input from the output of a secure hash function.
Let’s take a look at an online SHA-256 calculator. SHA-256 is the current gold standard when it comes to cryptographic hashing algorithms. When we put the sentence “Buy me a pony” into the function, it will return the following every time:
6e441ca056d8db576e273c98924002358e246e8bd3ab4aac5be1ee9edd39f5fc
If we simply enter the letter “B”, you will notice that we get an output of the same length, however it’s a completely different value:
df7e70e5021544f4834bbee64a9e3789febc4be81470df629cad6ddb03320a5c
If we change just a single letter of our original sentence, making it “Buy me a pond”, you will notice that the new output has very little in common with the old one:
6a9732000b903e7c308aba837beff1335f16d0511063d98530f68503b23c12d2
One of the most important features of hash functions is that no one can figure out the original input from the hash alone. As long as a secure hash function is being used, you cannot take the hash value and figure out that the initial input was “Buy me a pony”.
Checksums
Cryptographic hash functions can be used as checksum algorithms. These have a variety of uses, such as verifying the integrity of software. This practice is based on the principle that secure hash functions always spit out the same result for a given input.
If we know the hash value for a legitimate piece of software, we can take a hash of the code for the software that we have in front of us. If the two match, then we can assume that the software is legitimate and safe to use.
If the software has been altered in even the slightest way, then the checksum algorithm will return a hash value that is different to the legitimate hash value. This indicates that there are either errors in the code, or that the software has been tampered with. If this is the case, the software should be examined more thoroughly to determine what the problem is.
Digital signatures
Digital signatures involve both public-key encryption and hash functions, which allow us to authenticate the source and the integrity of data. Being able to authenticate who someone is, and whether data has been tampered with are incredibly important in a range of different scenarios, especially when it comes to electronic voting.
Let’s say that you want your friend to be able to verify that the messages they receive actually come from you and not an impostor, and you also want them to be able to check whether the data itself arrives in its original, unaltered form.
This can be done with a digital signature algorithm like RSA and a secure hash function like SHA-256. The first step would be to type out your message or select your data, then run the entire thing through a hash function.
You would then take that hash value and digitally sign it with your private key. This involves applying your private key to the hash with the RSA decryption algorithm. The result would be the digital signature.
You would then send the message to your friend alongside the digital signature.
If your friend wanted to verify that the message truly comes from you and that it hasn’t been altered, they would take the digital signature and send it through the RSA encryption algorithm alongside your public key.
If the message has been authentically signed by your private key and has not been altered since the signing, the result will be the hash value of the message. To determine the message’s authenticity, your friend simply needs to put the message they received through the same hash function and compares the results.
If the two values are the same, they can assume that the message is truly from you and that it hasn’t been tampered with. If the values are different, the message may have been sent by an impostor, it could have been altered since it was signed, or there may have been an error in the process.
Digital signatures can seem kind of complex. If you want to understand them in greater detail, check out our comprehensive guide. It’s important to get a good understanding of them because digital signatures are a key part of the authentication processes in both electronic and internet voting.
Mix networks
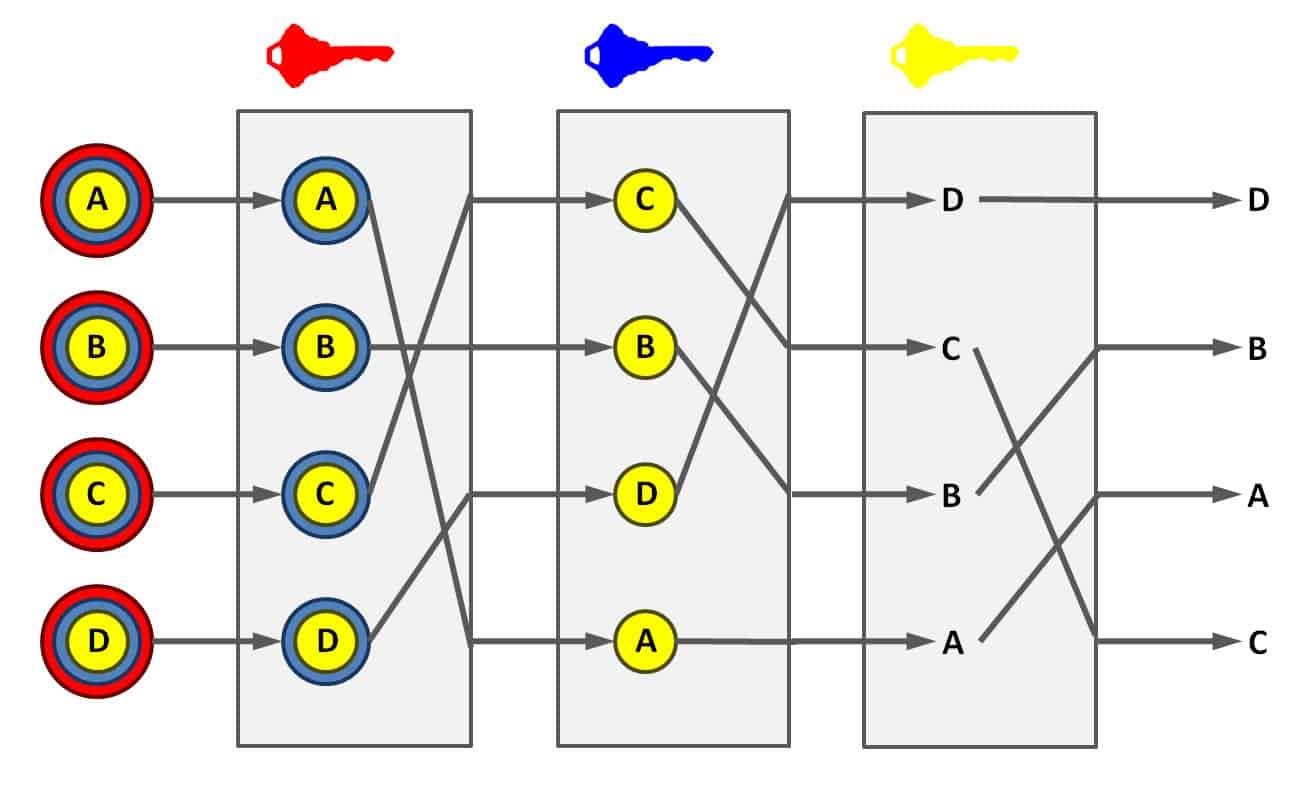
Mix networks are routing protocols that use public-key cryptography to obscure the relationship between messages, their senders, and the recipients. In a mix network, messages are encrypted with the public keys of a number of different proxy servers, as well as the public key of the recipient, then they are sent through a chain of servers.
Once messages are sent, they are shuffled at each proxy server along the chain, which also strips off its layer of encryption using the server’s private key. The proxy server then sends off the messages in a random order to the next proxy server, which repeats the process.
A diagram of how mix networks decrypt data at each proxy server. Mix network by Primepq licensed under CC0
When messages arrive at the final server, they have been shuffled around multiple times, making it difficult for attackers to track which messages came from where. The last proxy server uses its private key to strip off the encryption, then sends the messages to their recipients. The recipients then use their private keys to access the contents of the messages.
Mix networks are an important part of the Estonian voting process, because they help to preserve the anonymity of the vote.
Cryptographically secure pseudo-random number generators
Several aspects of voting require random numbers in order to retain the anonymity of the election and prevent attacks. These include key generation, salting, nonces and vote shuffling. If the numbers that are used aren’t truly random and patterns can be found, this opens up the door for attackers to either corrupt or deanonymize the vote.
Since elections face significant threats, they need random number generators that can produce a high degree of entropy (randomness) to prevent patterns and correlations from appearing in the numbers. Because of this, voting systems should implement cryptographically secure pseudorandom number generators (CSPRNGs) that are designed to produce sufficiently random values.
How is cryptography used to secure electronic voting?
The electronic voting process seems similar to paper-based voting, because you still have to go to a central polling location to cast your ballot. The difference is that it uses electronics at some stage of the process, such as vote casting, transmission, or tabulation. You may already be voting electronically without even realizing it.
Because electronic voting involves machines that we can’t see inside of, it comes with a whole new set of risks and complications. Cryptography can be used to help secure electronic voting in a range of different ways, although it depends on which systems are being used. While cryptography is certainly useful and can make these systems more secure, it’s no silver bullet.
In real-world voting systems, cryptography often isn’t implemented where it should be, and if is, it’s often “…either incomplete, improperly implemented, or undermined by poor key management,” according to a paper by Michael Dunn and Lawrence Merkle.
Let’s examine how cryptography can be used in each step of the voting process, even though it’s often ineffective in practice due to poor implementations.
Electronic pollbooks
When a voter arrives at the polling station, the first electronic voting system that they may encounter is an electronic pollbook. These are essentially digital substitutes for the huge three-ring binders that contain voter-registration information.
Election officials can use electronic pollbooks to look up voters, verify them and conduct other processes to make sure that the person is voting legitimately. These pollbooks contain important information, which could be compromised in a number of different ways if left unprotected.
If electronic pollbooks record the order that people vote in, there is the potential that they can be used to deanonymize the vote. All an attacker would have to do is align the vote record with the data from the electronic pollbook to figure out how each person voted, which could lead to voter intimidation.
Since electronic pollbooks contain significant amounts of voter information, the data needs to be encrypted with a scheme like AES when it is both at rest and in transit. Not only would this protect the privacy of voters, but it would also prevent attackers from altering data or compromising the system in other ways.
Before electronic pollbook software is run, it should be verified that it is legitimate with a checksum. If the hash value for the software on the machine matches the official hash value, then it can generally be assumed that the software is legitimate and can be used safely.
Direct-recording electronic voting machines
A direct recording electronic voting machine. ES&S Express Vote by Douglas W. Jones licensed under CC0
Once a voter has been verified with either an electronic pollbook or a traditional one, the election official authorizes the person to vote. If the polling place uses direct-recording electronic (DREs) voting machines, voters may be given a token or a smartcard which allows them to cast their ballot on the machine. These cards typically contain cryptographic keys that let the machine know the person has been authorized to vote
On top of this, the machines are secured by administrative keys, so only election officials are allowed to set up the machines and make changes. These keys can be used to digitally sign various aspects of the process, such as how a candidate’s name is displayed and attached to the vote count. In real-life applications, key management in DREs is often done poorly, which leads to insecure systems.
According to the Dunn and Merkle report, these systems often either use weak and outdated encryption schemes, or they fail to manage their keys securely. There has been a wide range of different examples of poor key management.
One example of an insecure practice involves having the key hardcoded to the machine. This means that if an attacker has access to one of the machines with a hardcoded key, then they would also have the key to every machine of the same model. This is particularly worrying, because many of these machines can easily be bought off eBay.
Other voting machines have had their keys leaked on the internet, while some just have weak keys that are easy to crack. Each of these examples of poor key management is a serious security issue, which makes the systems vulnerable to attackers.
The same report also stated that several different machines do not use adequately random numbers. One example is a DRE model from Brazil, which uses a timestamp as a seed. Since the number is not random, it means that attackers could easily deanonymize the vote.
Just as with electronic pollbook software, the software on DREs should be checked for legitimacy before it is used. The code should be run through a checksum to verify that it hasn’t been altered or tampered with. If the hashes match, it is likely that the software is safe to use.
Storage
Once ballots have been cast, they should be encrypted while they are stored on the DRM. This prevents attackers from being able to view votes, and makes it much more difficult to alter them.
Unfortunately, votes aren’t always encrypted while they are in storage. There have even been cases where researchers have purchased old voting machines off eBay and viewed the vote tally from the last election they were used in.
This means that the votes were just sitting on the machine, unencrypted, and hadn’t even been erased when the election was completed. This is a huge security and privacy violation.
Transmission
Votes also need to be encrypted when they are in transit to prevent attackers from intercepting them and tampering with the result. In transmission, security protocols like TLS are often used. This is a hybrid system that combines public-key encryption ciphers like RSA, with symmetric schemes like AES, as well as other security features. In recent years, Switzerland has turned to using quantum key distribution to detect whether there is a risk of attackers intercepting its encryption keys.
Tabulation
The final result is the most critical part of the election. If attackers could find a way to alter it without being detected, they could change the winner. Even if adversaries were detected before the election was finalized and the attacks could be stopped, it would still sow immense distrust into the system and make many voters question the legitimacy of the election.
It’s critical to make sure that the correct software is being used on the vote tallying machine. This means that checksums are needed to verify the code hasn’t been modified. These machines also need to be locked down so that they can only be accessed by the keys of authorized personnel. The keys must be securely managed to prevent attackers from tampering with the results as well.
How is cryptography used to secure internet voting?
Voting over the internet, also known as i-voting, has become an appealing idea in recent years. Since 2007, Estonia has allowed its citizens to vote online in national elections if they choose to do so. Online voting has also been implemented in narrower forms in countries such as Switzerland and Australia.
There is a range of different online voting systems in current use, as well as a number of proposed schemes. We will focus on the Estonian system, because it’s the most widely used example and it has undergone the most scrutiny.
The other systems use many of the same cryptographic concepts, but there are often tweaks or other elements involved. Over time, new systems and updates will continue to be developed. These may end up being more effective and perhaps have additional security benefits.
Digital identity cards
The Estonian i-voting system is built on top of the nation’s digital identity cards. These are used by voters to authenticate that they are authorized to vote. These are mandatory cards which can be used for a range of different identification processes.
One of the most important aspects is that the cards contain a public and private key pair that can digitally sign documents. A digital signature is made with the individual’s private key, and their identity can be authenticated with their public key.
When a person wants to vote, they download the election application onto their computers. They then plug in a USB card reader, which scans their ID. To authenticate themselves, they enter a personal PIN number. Alternatively, voters can use another identification system that is connected to their cell phone number. They enter the number into the application, as well as their PIN number.
In both cases, the systems authenticate the voter by checking their details against the electoral record. This makes it incredibly difficult to cast fraudulent votes, because an attacker would have to possess both the digital identity card and the PIN number of a voter.
Public-key encryption
To protect the anonymity of the vote and keep it secure, Estonian i-voting uses a double envelope system. Once a user has accessed the voting application on their computer, they cast their ballot, and a random number is added to the data.
The vote and the random number are then encrypted with a public key that is specific to the election. This forms the inner envelope, which is used to keep their vote anonymous.
Digital signatures
Once the ballot is encrypted in its inner envelope, it is digitally signed with the voter’s private key. The vote is then sent to a virtual ballot box. During transmission, it is kept safe with a security protocol called TLS.
TLS is comprised of a number of different cryptographic techniques, and it is used to keep your information secure whenever you exchange sensitive information on the web, such as when you are logging into your bank account or entering your password into Facebook. Whenever you connect to a site that uses TLS, you will see a little green lock to the left of the URL, as well as https, rather than http, in the site’s address.
All of the votes are then collected and sorted. Voter eligibility is also checked, and those votes which are ineligible are removed, as well as any multiple votes (the Estonian system allows voters to cast an unlimited number of ballots, but only their last one is counted, as an anti-coercion measure).
Sorting the votes & removing the digital signature
The i-votes are then sorted by the voter’s electoral district, and the digital signatures are removed from the votes. This strips the voter’s identity from the ballot. The votes are then shuffled through a series of servers in a mix network, which makes it infeasible to connect a vote with the identity of the person who cast the ballot. This step retains the anonymity of the vote and helps to prevent intimidation from occurring.
Decryption & final count
The shuffled votes are then moved to an air-gapped server to have the encryption stripped away. This server isn’t connected to the internet or any other networks, which prevents attackers from being able to compromise it virtually. The votes are then decrypted with the election-specific private key.
Rather than having the key controlled by a single person, several election officials must collaborate in order to assemble the complete key. To decrypt the vote, the officials must input their authentication tokens into the server, then enter their PIN numbers. This makes it far more difficult to tamper with the election result, because an attacker would have to compromise all of the officials in order to gain access.
Once the votes have been decrypted, they are transferred to an air-gapped vote counting server where they can quickly be tallied. Once the votes have been counted, the winner of the election can be announced.
Together, these systems use cryptography and meticulous organizational practices to conduct a relatively secure and anonymous vote over the internet.
Verifying the vote
Many people are skeptical about online voting. After all, you can’t really see what’s going on between your computer and the servers. In a paper ballot, you physically put your ballot in the box, and trust that the impartial observers will take care of it from there.
An online system such as Estonia’s conducts so many of its processes in the ether, which can make it hard for people to trust that their vote has been counted correctly.
To combat these fears, Estonia launched a verification system that allows people to check their votes and ease their minds. While online votes must be placed through an application on the voter’s computer, vote verification can only be done through an app on a person’s phone or tablet.
This separation is a security measure – if both processes were done through the voter’s computer, an attacker would only have to corrupt one device in order to manipulate the person’s vote without detection. Under Estonia’s system, attackers would have to infiltrate both devices.
When a person completes their vote, a QR code is displayed on their computer screen. The voter can scan it with the election app on their phone or tablet. The app will then display the person’s ballot as it was received by the server, so they can check whether their vote was placed correctly.
Does cryptography make electronic & internet voting secure?
If electronic or internet voting systems are going to be used, then cryptography is an important part of keeping them safe. Despite its usefulness, cryptography alone is not enough to secure these systems.
You can use all of the latest and most impressive cryptographic techniques, but still have a highly vulnerable system if they aren’t properly implemented. This is because relatively secure system requires planning. The right organization, processes, implementation and oversight need to be in place if you want the system to be even remotely secure. If these other aspects are neglected, all of the cryptography in the world can’t keep the system safe.
Even with the right cryptography, organization, processes, implementation and oversight in place, there is no guarantee of complete security. It simply doesn’t exist. If you build a 100-foot wall, someone can always build a 101-foot ladder.
Even in an absolute best case scenario, it’s not completely infeasible for a serious attack to slip through undetected. Such an attack has the potential to compromise a large number of votes and the result of an election. It’s worrying to think that there is even slight potential for this to happen, all without us ever finding out. This risk is a significant concern for both electronic and internet voting.
Such a massive attack is unlikely to happen in a paper-based election, simply because it would involve compromising far too many people. Any conspiracy operating at such a large scale would surely be found out. While paper elections do come with their own problems and inefficiencies, there is a far lower chance of an election catastrophe occurring.
As technology progresses, cryptographic techniques will improve, as will the systems that we use for both electronic and internet voting. At the same time, the attacks against these systems will also become more sophisticated.
It’s hard to say what will happen in the future, but at least at this stage, internet and electronic voting bring some risks that cryptography can’t completely resolve. For now, it may be best to stick to paper voting – it’s worked well enough for hundreds of years.
Is it really worth risking the viability of our democracies just so that we can vote from the comfort of our couches?