Network Address Translation (NAT) is a critical technology that plays a pivotal role in modern networking. It serves as an intermediary between private networks and the broader internet, enabling multiple devices within a private network to access external resources using a single public IP address. This capability not only conserves the limited pool of IPv4 addresses but also enhances security by obscuring internal network structures from external entities.
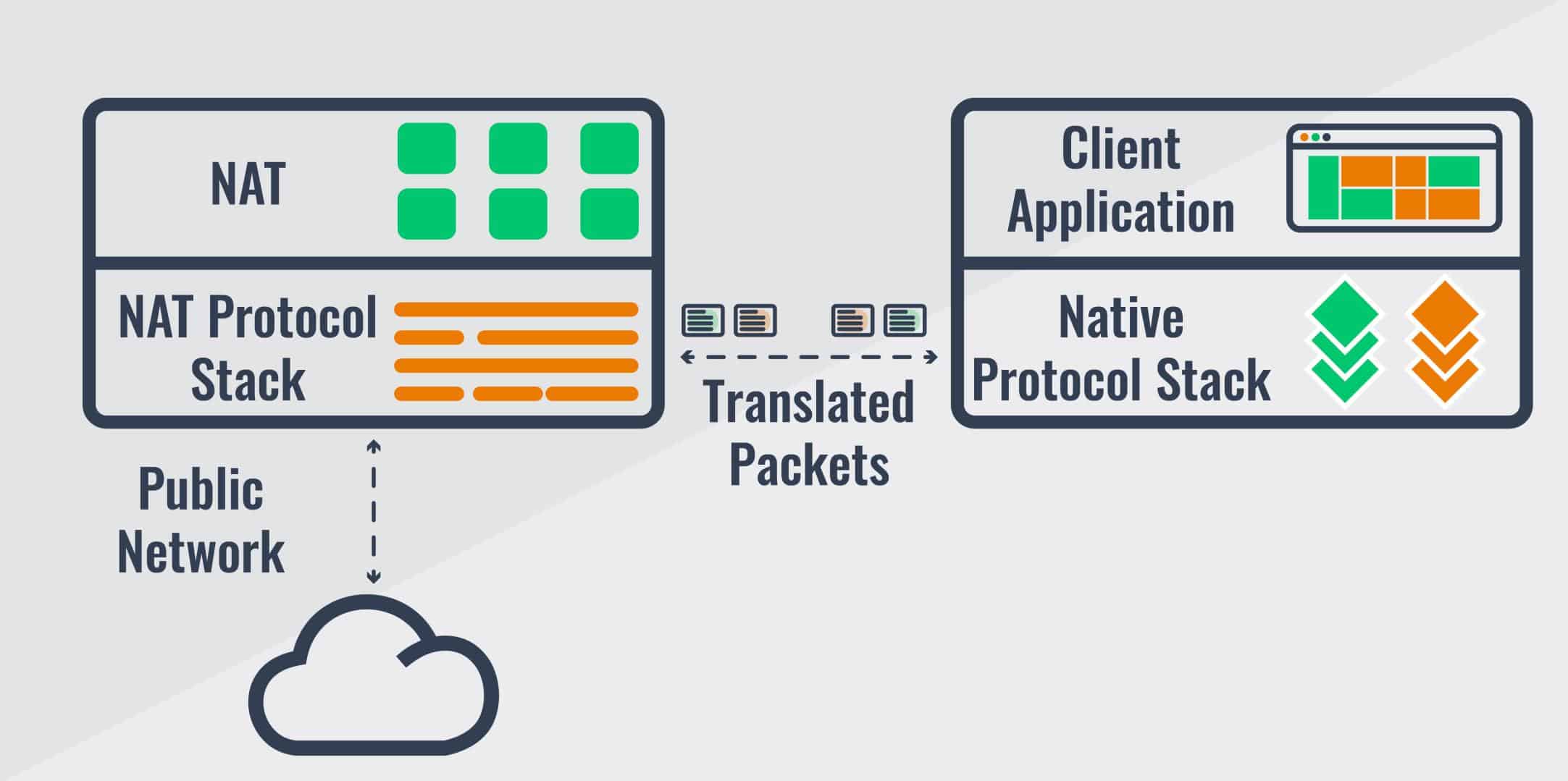
NAT operates by modifying the IP address information in packet headers as data traverses between internal and external networks. When a device on a private network sends a request to the internet, NAT replaces its private IP address with the public IP address of the router. Upon receiving a response, NAT reverses the process, ensuring data reaches the correct internal device.
There are several types of NAT, including static NAT, dynamic NAT, and the most commonly used: NAT overload, or PAT (Port Address Translation). NAT overload allows multiple devices to share a single public IP address by mapping their connections to unique port numbers. This efficient use of limited IP addresses makes NAT overload indispensable in residential, commercial, and enterprise environments.
In this article, we’ll explore how NAT works, its various implementations, and the crucial role of NAT overload in optimizing IP address usage.
How NAT works
Network Address Translation allows hosts in a local area network (LAN) to seamlessly communicate with hosts in an external network and vice versa. It allows IP addresses to be mapped from one address realm to another. With NAT, several private network devices can share a single public IPv4 address to communicate with other devices in the public network.
The need for IP address translation arises when a network’s internal private IP addresses cannot be used outside the network, mainly because they are allocated for private use, and therefore unfit for external communication. The primary objective for NAT just like Classless Inter-Domain Routing (CIDR) and Variable Length Subnet Mask (VLSM) was to slow the depletion of available IP address space by allowing many private IP addresses to be represented by a smaller number of public IP addresses. NAT is also very useful in situations where an organization switches to a new internet service provider (ISP) and still wants to retain its internal address scheme, or when two companies that have identical internal addressing schemes merge. The table below highlights the pros and cons of using NAT.
Pros and Cons of Implementing NAT |
|
|---|---|
Pros | Cons |
Preserves IPv4 public IP addresses | IP address translation introduces delays in switching pathways |
Increases flexibility when connecting to the internet | Certain applications will not function with NAT enabled |
Eliminates address renumbering as network changes, and reduces address overlap occurrence | Loss of end-to-end IP traceability |
Improves security and helps maintain the privacy of the LAN | Undermines the end-to-end principle of internet design, and therefore poses a problem for internet applications designed on the basis of the principle. |
Types of NAT implementation
NAT can be implemented in four different ways:
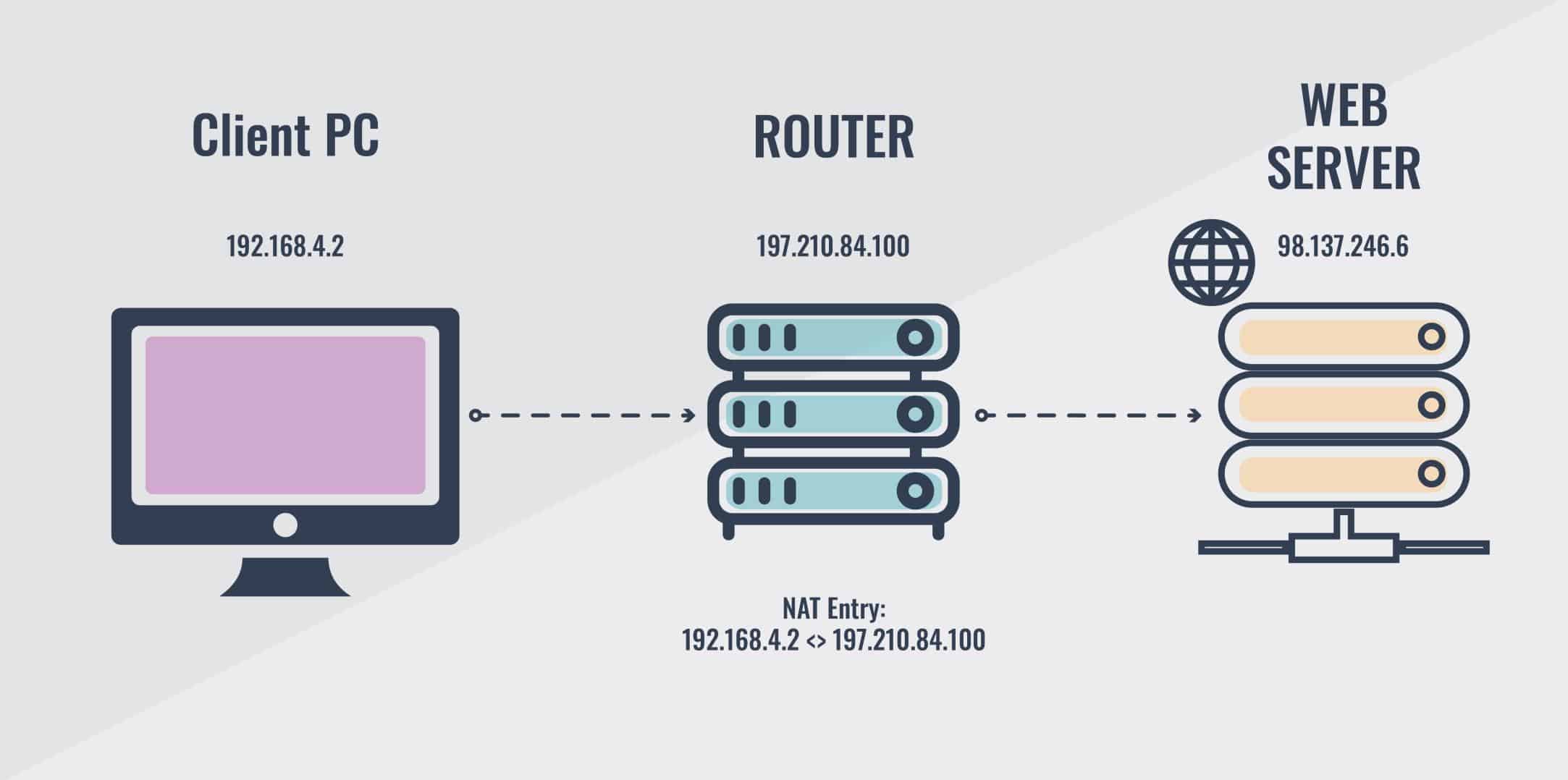
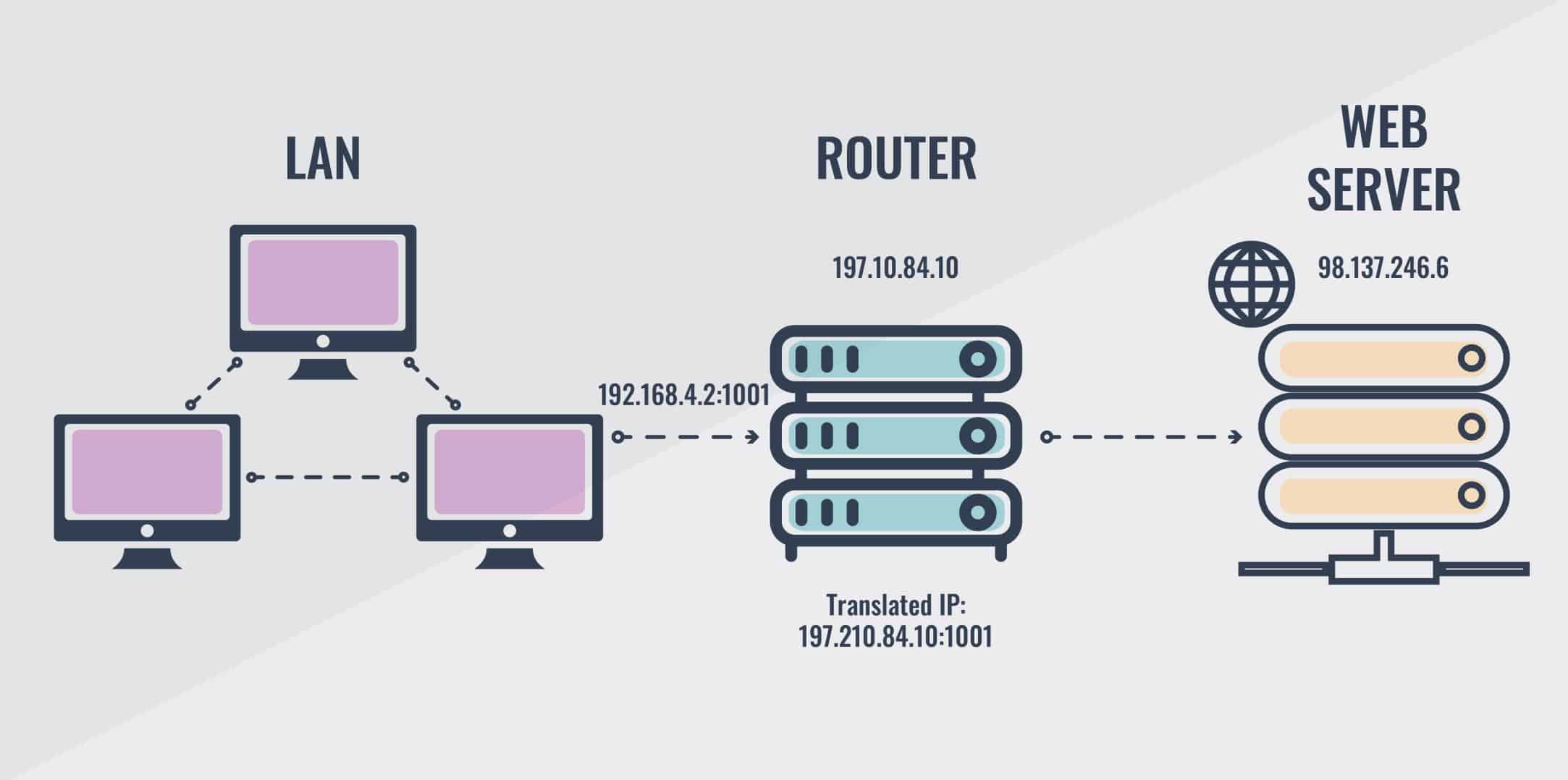
Static NAT: This type of NAT implementation is designed to allow one-to-one mapping of internal private IP addresses to external public IP addresses. In other words, when passing through a router, the internal IP address of the computer changes from 192.168.4.2 to 197.210.84.100 and vice versa. But, bear in mind that the static NAT requires you to have one public IP address for every host on your network.
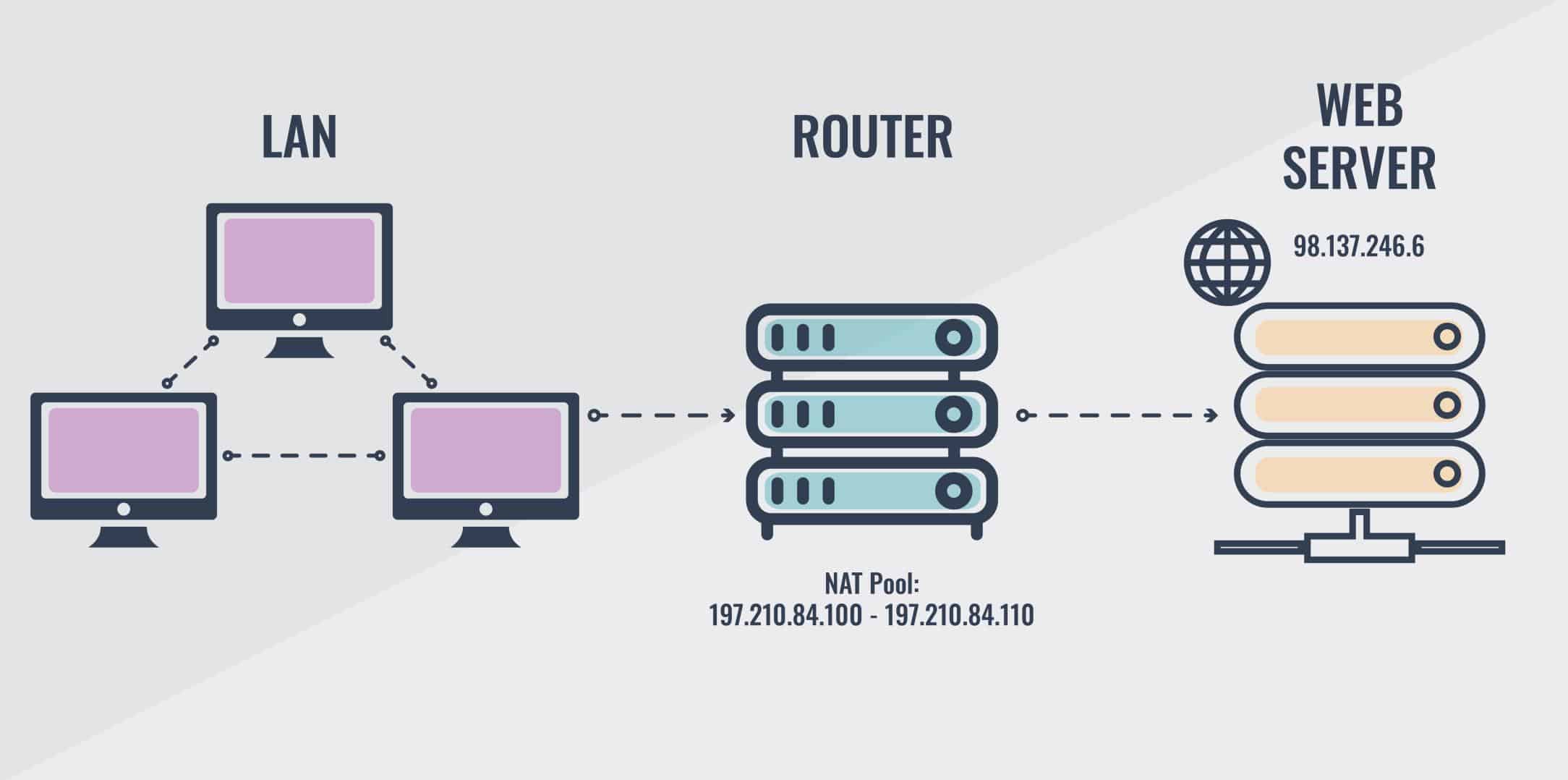
Dynamic NAT: This type of NAT implementation is designed to map an internal private IP address to an external public IP address from a pool of public IP addresses. You don’t have to statically configure your router to map an inside address to an outside address as you would, using static NAT. However, dynamic NAT requires you to have enough public IP addresses for every host that wants to communicate with the outside world; otherwise, the number of hosts that can simultaneously communicate with the outside world will be limited by the number of available public IP addresses.
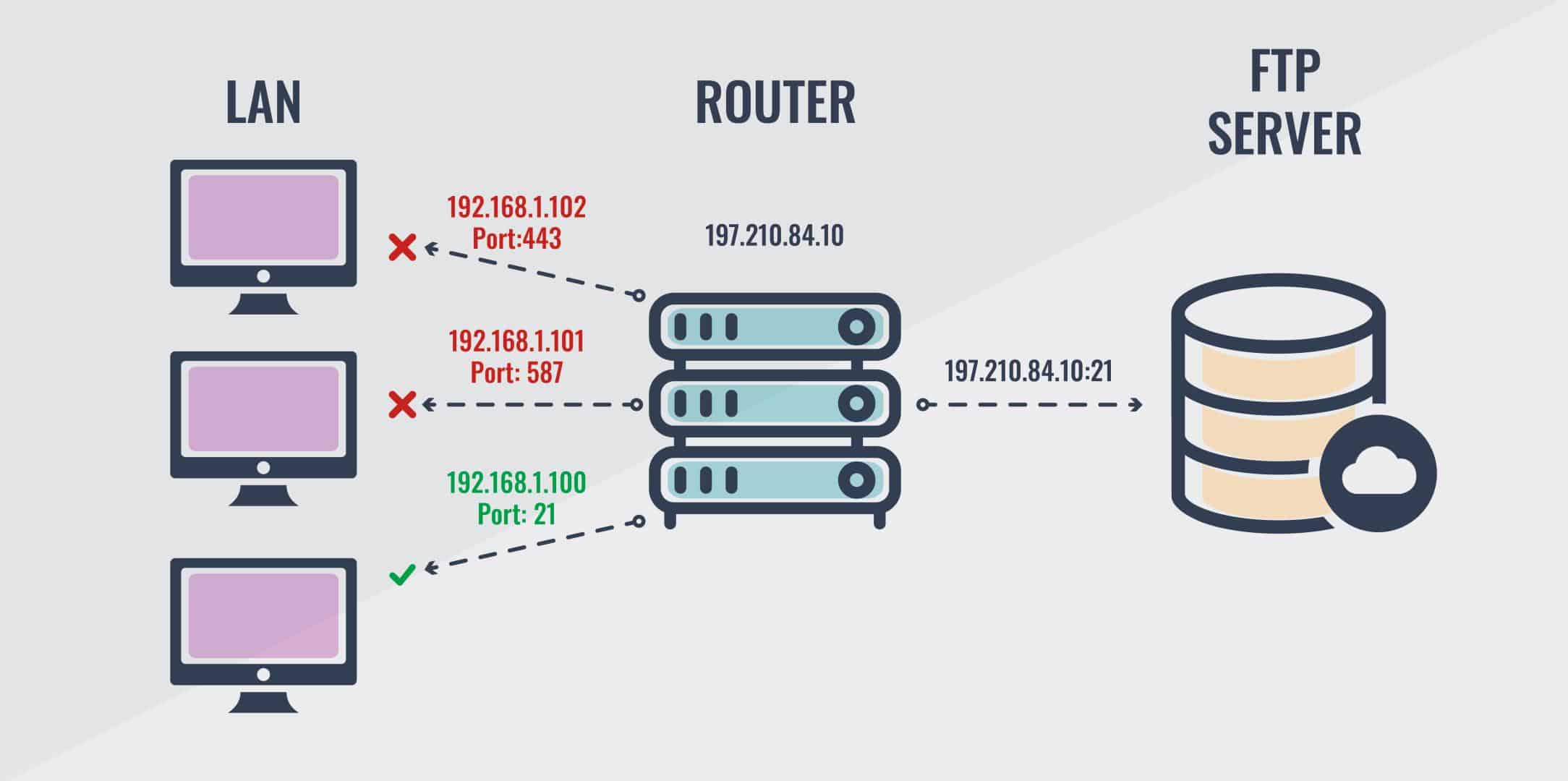
Port Forwarding: Port forwarding is an implementation of NAT that forwards a communication request from one address and port number combination to another while the packets are traversing a network gateway, such as a router or firewall. This technique is most commonly used to make application services running on a host on a private network available to hosts on a public network such as the Internet. Just as a device needs an IP in order to be identified in a network, services running on the device such as SMTP or FTP, also need to be identified to enable external communication. Port numbers help in identifying these services, and port forwarding is the technique that makes the service available to hosts on a public network. Whenever a service needs to communicate, the port number helps identify the right destination/source on the device and helps in an appropriate data transfer
NAT Overloading: NAT Overloading, also known as Port Address Translation (PAT) is designed to map multiple private IP addresses to a single public IP address (many-to-one) by using different ports. In other words, a single public IP address can be used for several internal private IP addresses, hence the term overloading. Interestingly, this is the most predominant and is the default form of NAT implementation in today’s networks. Why is this so predominant? Well, the answer is simple: It’s because by using NAT overload, you get to have thousands of users connect to the internet using only one real public IP address. NAT overload is one of the main reasons why the IPv4 address space has lasted this long. We’re going to explain in detail how NAT overloading works, and how you can configure it on your Cisco router.
How NAT overloading works
NAT overloading enables multiple devices in a LAN to use the same public IP address to communicate with the outside world at the same time. Typically, packets passing from the private network (LAN) to the public network (internet) will have their source IP address modified, while packets passing from the public network back to the private network will have their destination address modified.
Since private IP addresses are unrouteable on the internet, the only way client devices in a LAN can communicate with the outside world is to point them to a router with a public IP address, and allow the router to mediate between them and the public network. In NAT overloading, the router achieves this mediation by swapping the private IP addresses and port numbers of the client devices with its own public IP address and available port number. This technique works primarily by taking advantage of the TCP and UDP port numbers. As traffic passes from the LAN to the internet, the source address in each packet is translated automatically from a private address to a public address. This appears to servers on the internet as the primary source of the data packet. The router tracks the destination address and port number about each active connection based on the entries in the NAT table. When the router receives a response, it uses the connection tracking data it captured in the NAT table during the outbound phase, to determine the private IP address on the LAN to which to forward the response. Here’s an illustration for further clarification:
Imagine a LAN with the network ID 192.168.4.0/26 and usable host range 192.168.4.1–192.168.4.63, and a default gateway router assigned with the private IP address 192.168.4.1, and the public IP address 197.210.84.100. Now, if a computer in the LAN wants to communicate with the outside world, here is what happens:
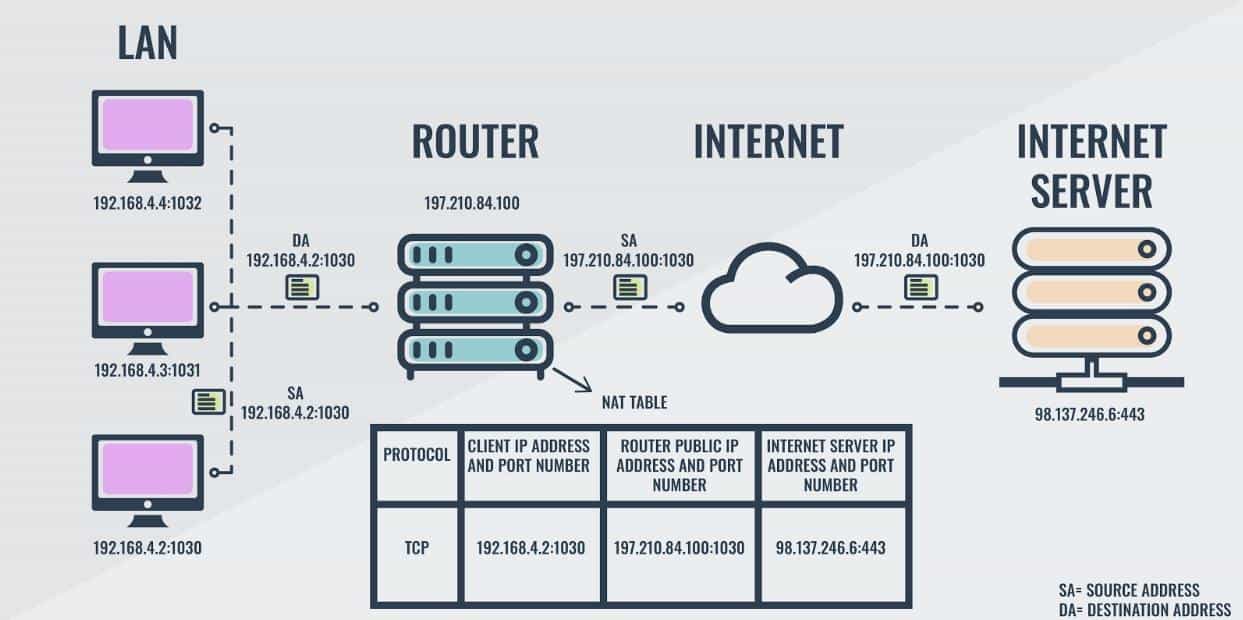
Let’s say a computer with the internal IP address 192.168.4.2 and port number 1030 wants to download some data from an internet server with the public IP 98.137.246.6 at port 443. The computer forwards this download request to the router with the following information: Client device 192.168.4.2 wants to establish a connection on port 1030 to internet server 98.137.246.6 on port 443. In order to process this request, the router has to replace the source IP address and port number of the LAN device with its own IP address and the corresponding or available port number. Thus, 192.168.4.2:1030 is translated to 197.210.84.100:2040 as shown in Figure 6.0 above. All relevant information is stored in the NAT table on the router as shown in the diagram
Protocol | Client IP Address and Port Number | Router Public IP Address and Port Number | Internet Server IP Address and Port Number |
|---|---|---|---|
TCP | 192.168.4.2:1030 | 197.210.84.100:1030 | 98.137.246.6:443 |
Once the internet server receives the request, it responds with the requested data packet which is then forwarded to the requesting device through the router based on the connection information on the NAT table. In addition to IP addresses and port numbers, the router also captures idle time-out associated with each connection in the NAT table. Whenever new traffic is received for a client, its time-out is reset. When the time-out expires, the entry is deleted from the NAT table. This ensures that the NAT table is kept to a reasonable size, and ports don’t remain perpetually open during inactivity and become a doorway for cyber-attacks.
How to configure NAT overloading on a Cisco router
In order to configure NAT overloading on a Cisco router, the following steps are required:
- Configure the router’s internal interface using the ip nat inside command
- Configure the router’s external interface using the ip nat outside command
- Configure access-list that includes a list of the internal source addresses that requires translation
Enable NAT overloading with the ip nat inside source list ACL_NUMBER interface TYPE overload global configuration command
Description | Command |
|---|---|
Define the internal interface on the router | Router(config)#int fa0/0 |
Configure router with the NAT inside a command | Router(config-if)#ip nat inside |
Define the external interface on the router | Router(config-if)#int s0/1 |
Configure router with the NAT outside command | Router(config-if)#ip nat outside |
Define an access list that includes all private IP addresses we would like to translate | Router(config-if)#access-list 1 permit 192.168.0.0 0.255.255.255 |
Enable NAT and refer to the above ACL and the interface whose IP address will be used for translations | Router(config)#ip nat inside source list 1 interface s0/1 overload |
Once you have configured NAT overload on your router, you need to be able to verify the configuration. In order to verify the NAT translations, we can use the following commands:
Description | Command |
|---|---|
Show basic IP address translation information | Router#show ip nat translation |
Show the sending address, the translation, and the destination address on each debug line | Router#debug ip nat |
As the internet continues to expand at an exponential rate, NAT overloading has become the de facto standard for devices on a private network with IPv4 addresses to gain access to the public network, while slowing the depletion of the IPv4 addressing space. This has managed to conserve the IPv4 address for the last 30 years. But in November 2019, RIPE Network Coordination Centre announced that it has officially run out of IPv4 addresses. A longer-term solution to the eventual exhaustion of the 32-bit IPv4 address space is the 64-bit IPv6 protocol.
However, NAT is not commonly used in IPv6 networks. The large addressing space of IPv6 rules out the need for its conservation as every device can potentially be assigned a unique public IP address. Instead of the 4.3 billion IPv4 addresses, there are now potentially 3.4 duodecillion IPv6 addresses available to connect devices to the internet. This basically renders NAT implementation in IPv6 unnecessary. Nonetheless, NAT can still be used to protect the privacy of IPv6 private networks from public networks. But for now, as long as IPv4 is still in use, NAT overloading will continue to enable several devices in private networks to share a single public IPv4 address to communicate with other devices in the public network.
Network address translation FAQs
Which NAT overloading function matches the command access-list 1 permit 10.1.1.0 0.0.0.255?
A router command that includes the command access-list sets up Access Control List (ACL for IP addresses on the local network. The address 0.0.0.255 is a wildcard.
What does NAT overloading use to track multiple internal hosts that use one inside global address?
NAT overloading uses port numbers to identify each local host. This is why the technique is also called also known as Port Address Translation (PAT).
How does NAT overloading provide one-to-many address translation?
The NAT system assigns a unique TCP/UDP port to each session. The port numbers that the system uses must be clear of the well-known port numbers that could already be on the communication with an outside destination.