The Dark Web is a secret part of the World Wide Web that is frequently accessed by terrorists, pedophiles, and criminals of all kinds.
Hacker websites on the Dark Web share lists of email addresses and account credentials to enable cyber thieves to break into the accounts of people on personal and business systems to steal their money and the assets of the businesses that they work for.
As a network administrator, how should you be taking steps to protect your company from the threats that hide in the Dark Web? Is there anything that you could feasibly do? What is the Dark Web, anyway?
Here is our list of the best dark web monitoring tools for network admins:
- Flashpoint Ignite EDITOR’S CHOICE This cloud-based threat intelligence platform offers real-time insights, streamlined workflows, and actionable alerts. Its intuitive interface and robust analytics enhance cybersecurity strategies, making it invaluable for proactive threat management.
- DarkOwl Vision A threat intelligence service that includes a Dark web scanner as an information source.
- CrowdStrike Falcon Intelligence This intelligence feed scans the Dark Web for mentions of your brand and corporate identifiers, such as email addresses on your domain.
- SpyCloud ATO Prevention Account takeover prevention with a threat intelligence database derived from Dark Web scans.
- ReliaQuest GreyMatter Digital Risk Protection A corporate brand protection service.
- DigitalStakeout A data loss prevention system and threat protection system that includes a Dark Web scanner.
- Alert Logic Dark Web Scanner An account takeover prevention system based around a Dark Web scanner.
- ACID Intelligence A threat intelligence service that scans all known sources of illegal data.
- WhatsUp Gold A network traffic monitor that can identify traffic from the Tor network.
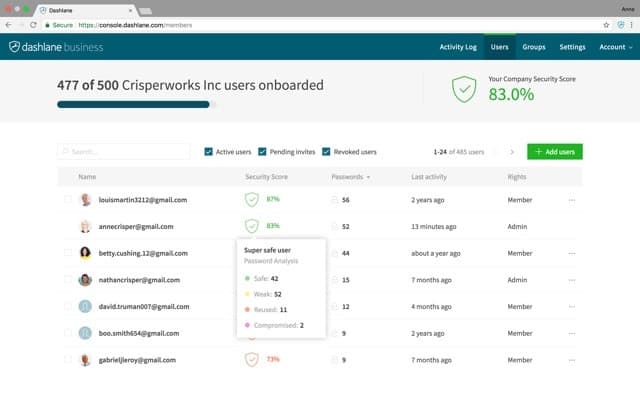
- Dashlane Business A comprehensive password protection system that includes a Dark Web scanner.
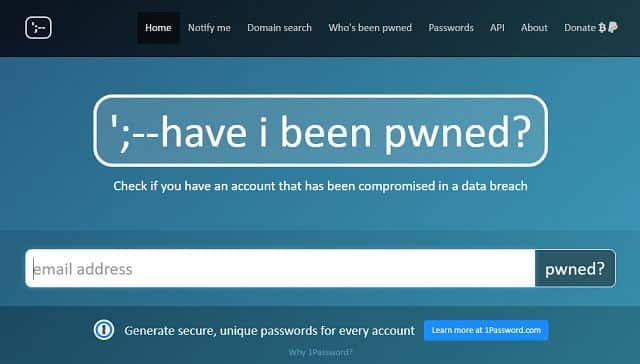
- Have I Been Pwned? A free email address-related Dark Web scan.
The Deep Web and the Dark Web
Before tackling the topic of blocking the Dark Web from damaging your company’s operations, we first need to explore exactly what the Dark Web is and how it relates to the Deep Web.
The Clear Web
In Deep Web/Dark Web terminology, the World Wide Web that the general public uses is called the Clear Web. This is a collection of websites that can all be accessed through a search engine.
You don’t have to go through a search engine to get to a website because you can just enter its address in the address bar of your browser or click on a link on another page. However, the test of whether or not a website has been discovered by at least one search engine and indexed by it is the defining characteristic of the bona fide web that we all know about. Another term applied to this publicly-known World Wide Web is Clearnet.
The Deep Web
The Deep Web is just as accessible as a Clear Web site by typing in the address or following a link. However, the sites on the Deep Web aren’t indexed by search engines. Search engines use a type of software, called a “web bot.” In Google’s instance, those programs are called “Googlebots”.
The Dark Web
Pages on the Dark Web aren’t accessible by search engines, so they are also part of the Deep Web. The defining characteristic that makes a website part of the Dark Web is how it is accessed.
The sites on the Dark Web make themselves difficult to find and to access. It is only possible to see these sites through a Tor browser. Tor is a web security system. The name was originally TOR, standing for “the onion router.” Traffic gets randomly routed through the computers of volunteers all over the world. Before being sent, each web page request is encrypted several times over, with each layer decoded by a key, which is only held by one of the computers on the route.
Tor was invented by the US Navy to secure its own communications and is used by government security agencies and police forces worldwide. Tor has its own browser, which is an offshoot of Mozilla Firefox and has all of the necessary encryption processing for Tor built into it.
Criminal activity on the Web
Hackers and thieves do not limit their online presence to the Dark Web. There are scam websites on the Clear Web. Many reputable organizations have a presence on the Dark Web. So, the Dark Web itself is no more of a threat to the world’s businesses than the regular World Wide Web.
When journalists and cybersecurity consultants refer to the threat of the Dark Web, they are using the term as a shorthand for criminal activity on the Web in general.
Dark Web Scanners
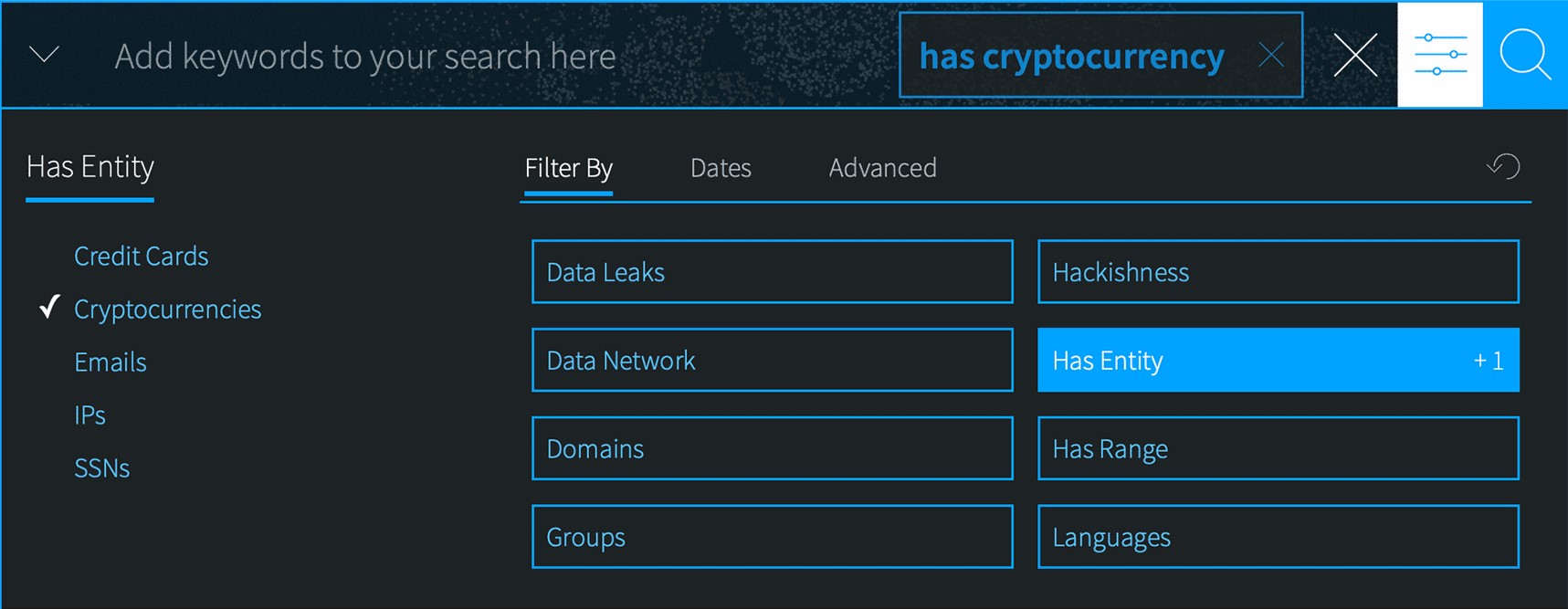
Cybersecurity service providers have a more precise definition of the Dark Web. Some sites and forums on the Dark Web are used by hackers to buy, sell, and share data stolen from businesses – specifically, login credentials, online identity data, such as social security numbers, and financial account information, such as credit card numbers. Not all of these sites are configured on the Dark Web. Some are Clear Web sites and some are Deep Web sites.
So, when we look for solutions to Dark Web threats, we are looking for services that know where those credential-sharing sites are and how to search through the data that they contain. Those tools are called “Dark Web scanners.”
Some Dark Web online protection services are dubbed “monitors.” However, these are the same as scanners because they simply search through the lists of stolen user credentials, and personal and financial data that are available on the web, be it Dark, Deep, or Clear.
The best dark web monitoring tools for network admins
Our methodology for selecting a Dark Web monitoring tool
We reviewed the market for Dark Web intel systems and analyzed tools based on the following criteria:
- A data-gathering team with access to Dark Web forums and sales sites
- Scraping scanners of well-known Dark Web sites
- A facility to filter results to those relevant to a specific company
- A fast data collection service
- Bulk digital feeds and human-readable reports
- A sample report or a free consultation for assessment purposes
- A good deal on a subscription that provides a fast and comprehensive intel system
With these selection criteria in mind, we investigated Dark Web intel-gathering systems that can give companies fast warnings on impending threats and leaked sensitive data.
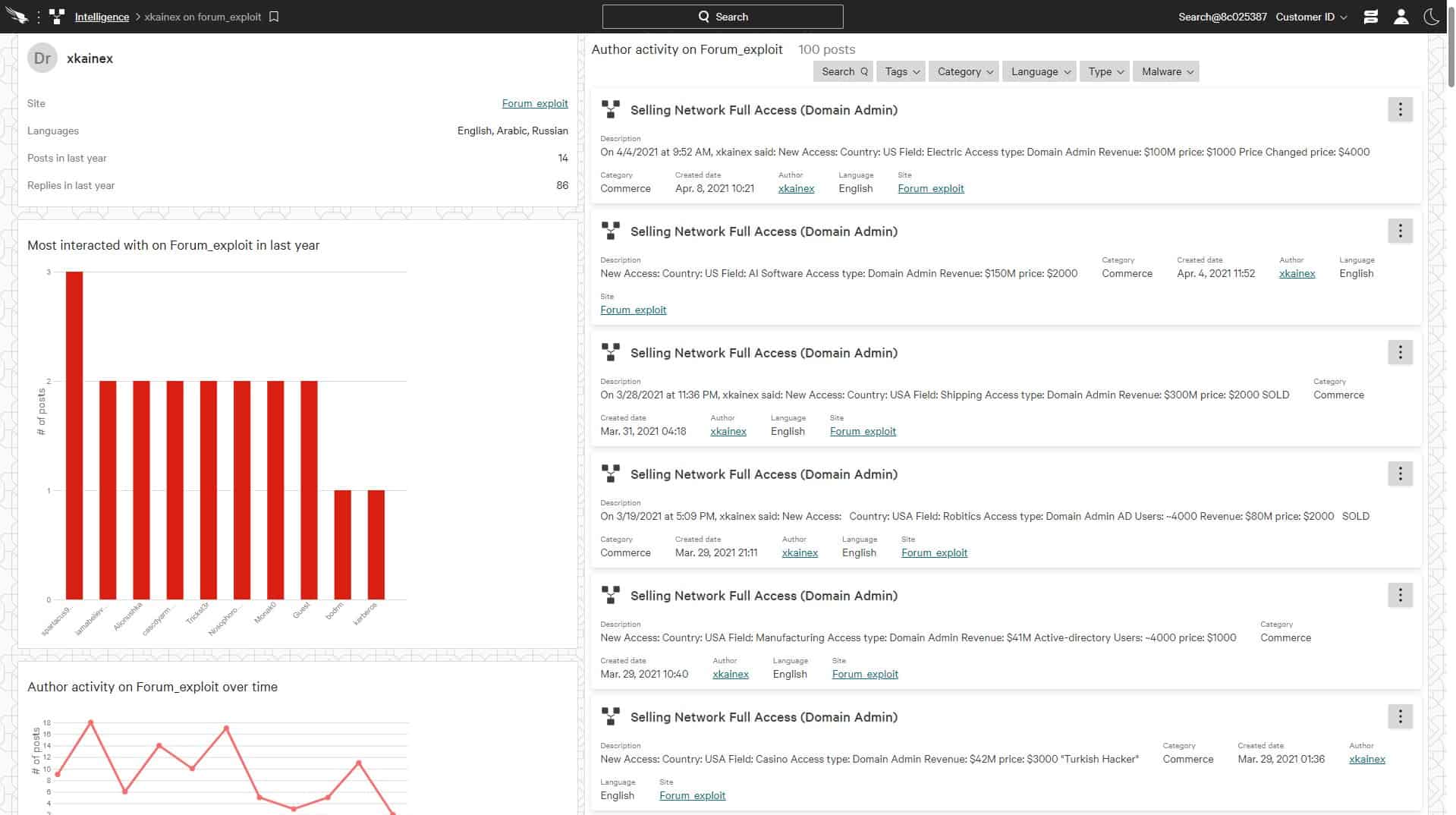
1. Flashpoint Ignite
Flashpoint Ignite is an advanced threat intelligence platform designed to help organizations proactively detect, analyze, and respond to emerging cyber threats. By providing real-time alerts, enriched data, and customizable workflows, Ignite empowers security teams to make informed decisions, streamline incident response, and fortify their defenses against sophisticated attacks in dynamic environments.
Key Features
- OSINT System: Open-source intelligence
- Dark Web Scans: Stolen credentials discovery
- Alerts: List of compromised accounts
- Threat Analysis: Intelligence reports
- Actionable Results: Account security protection
Why do we recommend it?
Flashpoint Ignite is a good example of an easy-to-use online search tool that offers a much cheaper and quicker service than the CrowdStrike offering. This system supplements its Dark Web searches with regular analysis reports and warnings about potential attacks that chatter indicates will be launched against specific industries or countries.
This is an online service that operates like a search engine. The user enters a name, a social security number, or an email address and then searches through sources in Dark Web marketplace, social media sites, and forms to find incidences of those details up for sale, or openly appearing on free lists.
The tool will also look for websites that mention the named person – information about people is collected for “doxing”, which gathers information to enable a charlatan to either target or impersonate that person in a phishing attack.
The service can identify data breaches and search out malicious information stores that hold data on businesses as well as individuals.
Who is it recommended for?
The Flashpoint Ignite package is a self-service tool. You get access to the Flashpoint site and then you can perform as many checks as you like for as long as you subscribe. So, you would probably prefer this option if you have cybersecurity experts on your payroll.
Pros:
- Scans: Social media, hacker forums, Dark Web, and news sites
- Brand Protection: Also regional reputational damage documentation
- Warnings: Weak password identification
- Compromised Account List: A feed that can be integrated into automated processes
- Unlimited Threat Detection: Worldwide scanning
Cons:
- No Price List: Deters small businesses
EDITOR'S CHOICE
Flashpoint Ignite is our top pick for a Dark Web monitoring tool due to its comprehensive capabilities and user-friendly design. In an era where cyber threats are becoming increasingly sophisticated, monitoring the Dark Web is critical for organizations to protect sensitive information, detect potential breaches, and stay ahead of cybercriminal activities. Flashpoint Ignite excels in this space by providing real-time visibility into illicit online activities, including forums, marketplaces, and private channels where threat actors operate. One of the platform’s key strengths is its ability to deliver actionable intelligence. Flashpoint Ignite goes beyond simple data collection, offering enriched context and insights that help organizations quickly assess risks and respond effectively. Its advanced search and alerting features allow users to track specific keywords, such as leaked credentials or intellectual property, ensuring no critical threats go unnoticed. Another important feature is the service’s attractive dashboard, which simplifies complex threat intelligence management tasks. Ignite integrates with existing security systems, enabling teams to manage threats efficiently without disrupting workflows. Additionally, the platform supports customizable dashboards and automated workflows, reducing the manual effort required for threat analysis. Flashpoint Ignite also offers support and training resources, ensuring users maximize the platform’s capabilities.
OS: Cloud based
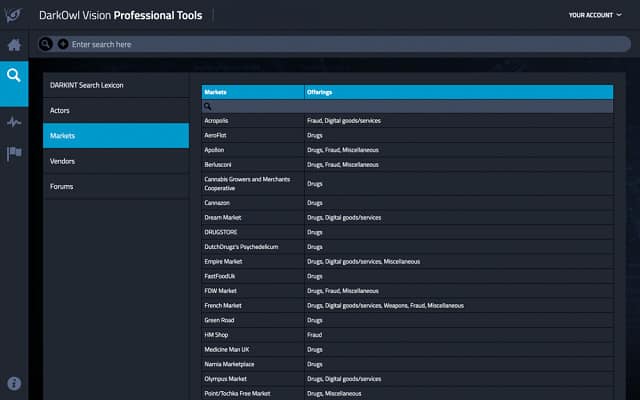
2. DarkOwl Vision
Vision, by DarkOwl, is a Dark Web scan tool that indexes the content of malicious sites all over the World Wide Web to identify data stolen from its clients.
Key Features
- A Search Tool: Online database
- Subscription: Gets access to the DarkOwl database
- Hacking Intelligence: Sourced from the Dark Web
- Automated Reporting: Alerting mechanism
Why do we recommend it?
DarkOwl Vision is a cross between the CrowdStrike and Echosec services on this list. Like CrowdStrike, this system requires you to set up a list of identifiers for your company, which include domain names, addresses, and product names. The Echosec then adds those words to its regular Dark Web crawlers. You get notified whenever anything turns up.
The Vision system searches for mentions of the client company’s domain and email addresses in hacker data exchanges. The search is an automated process. This information is constantly updated by repeated scans and those disclosures are made available in the dashboard for those subscribing companies to which the data pertains.
The DarkOwl vision system is integrated into a package of intelligence services, called Darkint Suite. Another element in this suite is Darkint Score, which is a vulnerability assessment of the client company’s exposure to Dark Web data loss.
Darkint Suite’s data feeds can be integrated into applications through an API. The DarkOwl service is a threat intelligence database; it does not monitor infrastructure or network traffic. Companies subscribing to DarkOwl will also need threat protection and data loss protection software to fully protect their systems.
Who is it recommended for?
The DarkOwl system is a mid-market option because it provides results for its customers rather than expecting them to perform searches themselves. The value of the service lies in its search algorithms. As it is an entirely automated service, it is a lot cheaper than the CrowdsStrike package.
Pros:
- Analysis tool: An interface for manual Dark Web data searches
- Extent: Search across databases or focus on one source of account compromise information
- Automation: Allows users to set up searches that will run constantly to extract new data
- Results: Alerts for discoveries of compromised accounts
Cons:
- Manual Tool: Automated monitoring is better with the API products of DarkOwl
3. CrowdStrike Falcon Intelligence
CrowdStrike Falcon Intelligence is a research service that scours Dark Web sources for mentions of your company’s assets. These include brands, corporate identities, the email addresses of people within your business, and mentions of key executives and employees.
Key Features
- Tailored Reports: Analysis of event discoveries
- Intelligence Feeds: Input for automated systems
- Research Center: Human cybersecurity expert
Why do we recommend it?
CrowdStrike Falcon Intelligence scans through the Dark Web looking for signs that the identities that you register with the service are being traded by hackers. These identities can include the names, addresses, and email addresses of your employees, key personnel, and administrators.
The information that you receive from this service offers a double check on PII security. Key information on your customers should be kept safe. However, if PII is stolen from your business, it is likely to end up for sale on the Dark Web. Knowledge of this leak should have been caught by your data loss prevention system. However, if you don’t have data protection in place, the Falcon Intelligence Recon service gives you a chance to catch up.
Who is it recommended for?
Effectively, this is a managed security service and it is a very high quality package. All companies need a service like this and the CrowdStrike package is the leading reconnaissance service on this list. As the system includes the input of consultants as well as automated scanners, this is a pricey system. Small businesses on tight budgets should look to one of the other services on this list rather than skipping this category of protection altogether.
Pros:
- Three Plan Levels: Starting with automated intelligence gathering within a network
- Daily Reports: Provide information on general industry threats
- Tailored Threat Intelligence: Focuses on the subscriber’s accounts and business area
Cons:
- You Might Already Have it: The base plan is included with all standard Falcon packages
Falcon Intelligence is a subscription service and part of the CrowdStrike family of products that are offered from their Falcon SaaS platform. You don’t have to download and install any software in order to use the Falcon Intelligence service. You can start on a 15-day free trial.
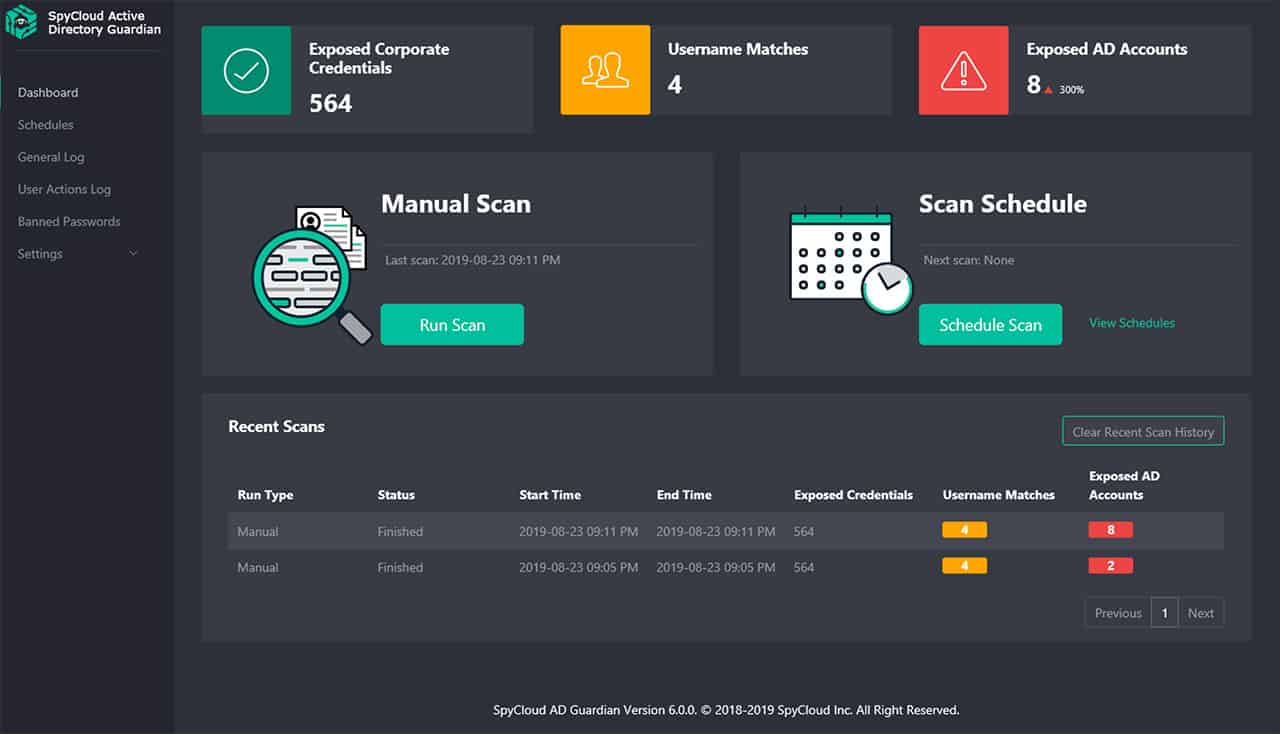
4. SpyCloud ATO Prevention
SpyCloud offers two services for account takeover (ATO) prevention – one to cover the employees of companies and the other to protect the customers of online services.
Key Features
- Retroactive Detection: Spots compromised accounts
- Detailed Scanning: Looks through Dark Web sources
- Security Assessments: Identifies password accessibility
Why do we recommend it?
SpyCloud ATO Prevention is an identity protection service with a version available for businesses. The business service also includes a system hardening system that scans through Active Directory and recommends tighter account groups and stronger passwords. The system gathers account names and adds them automatically to Dark Web scans. The service also includes an address scanner for incoming traffic and emails, looking for known sources of malicious activities.
ATO protection concentrates on protecting the accounts that businesses set up for access to their resources, such as network logins or user accounts at websites. A major part of the service involves detecting accounts that have already been compromised.
The ATO prevention service includes a cloud-based threat intelligence database, which warns clients of compromised accounts. The information on disclosed credentials is discovered by a Dark Web scanning tool. Other elements in the threat intelligence system include known sources of phishing and impersonation attacks, which gives the protecting agent software guidance on which incoming emails to block.
The service also proactively monitors Active Directory and sets up stronger password policies, such as password rotation and enforced password complexity.
Who is it recommended for?
The SpyCloud business package combines Dark Web scanning with internal scans for weaknesses plus constant traffic address checks. This is a strong combination and involves a great deal of automation so busy network administrators will be able to use this service without specific cybersecurity skills.
Pros:
- Breach Detection: Scans the Dark Web for credentials that have already been stolen
- Security Weakness Analysis: Identifies how credentials were stolen
- Threat Prevention: Maintains a list of malware and infected sites used for credentials theft
Cons:
- Research System: Supplies data rather than solutions
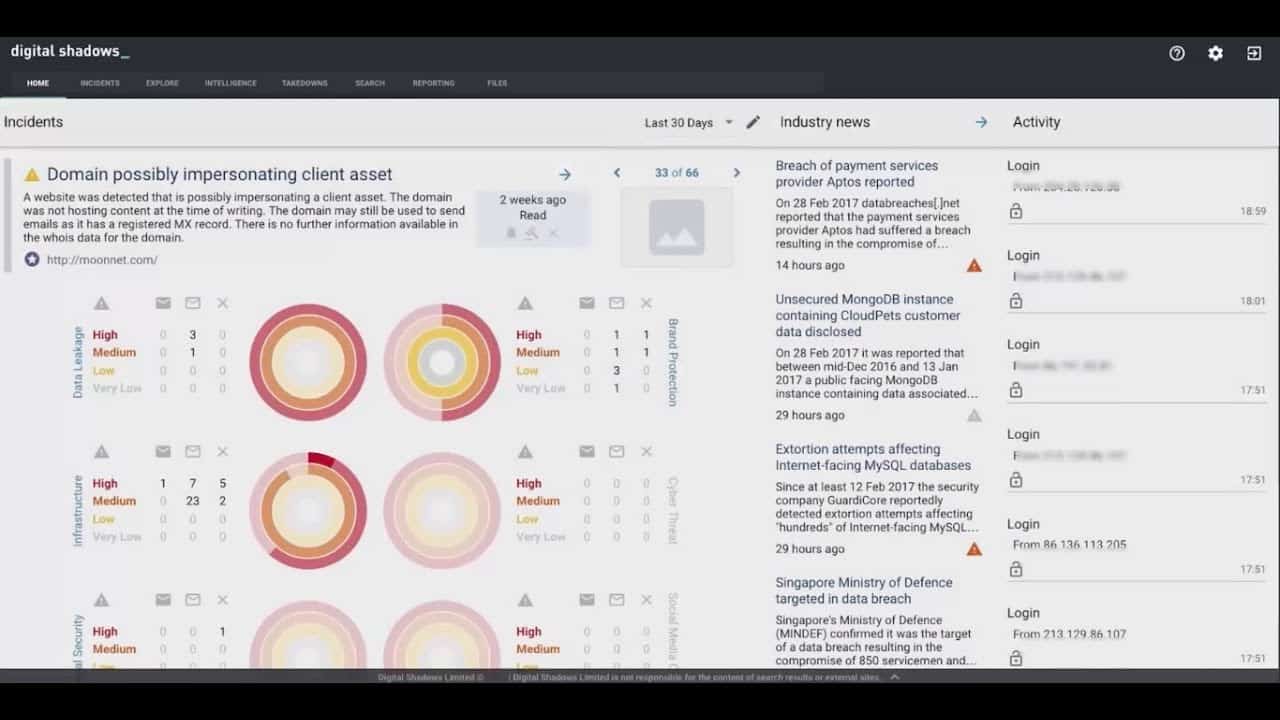
5. ReliaQuest GreyMatter Digital Risk Protection
ReliaQuest GreyMatter Digital Risk Protection is particularly concerned with protecting the brand and reputation of the companies that use its services. Rather than focusing on account protection, this service protects both the image and trade secrets of the companies that it serves.
Key Features
- Hacking Research: Scans the Dark Web
- General Threats: Also scans the clear Web
- Unintended Disclosure Identification: Social media scanning
Why do we recommend it?
The ReliaQuest GreyMatter Digital Risk Protection service looks for intellectual property leaks and the disclosure of offers for sale of details about a company’s premises, security systems, and trade secrets.
For example, the GreyMatter Digital Risk Protection looks for company procedural documents, site plans, and internal memos that have found their way onto other sites that are known for trading in corporate data illegally. One incident that the ReliaQuest site recounts is its discovery of ATM designs that it alerted one of its clients about. That client was the bank that used the compromised ATM design.
Who is it recommended for?
While all companies need this service, innovators, engineering design firms, and companies that compete in highly competitive markets with thin profit margins would benefit most from using the ReliaQuest GreyMatter Digital Risk protection system.
You can examine GreyMatter Digital Risk Protection by accessing a demo.
Pros:
- A Searchable Database: Sourced from Dark Web, Deep Web, code repository, social media, and open Web scans
- Readable Intel Reports: Compiled by ReliaQuest analysts
- Automated Alerts: Raise on the discovery of compromised accounts
Cons:
- No Free Trial: Can’t try it before you buy
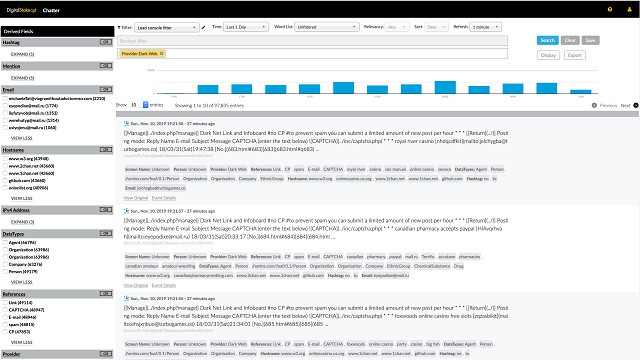
6. DigitalStakeout Scout
Scout, from DigitalStakeout, is a Dark Web threat intelligence service. The system includes workflows and machine learning to detect anomalous behavior on the network. It then references the external source or destination of that internet traffic with its Dark Web Scanner and threat intelligence database to identify the malicious actor participating in the suspicious activity.
Key Features
- Hacking Research: Dark Web monitoring
- Breach Intelligence: Credentials theft identification
- General Threat Alerts: Intelligence on hacker campaigns
Why do we recommend it?
The DigitalStakeout Scout package is a network-based intrusion detection system (NIDS) that scans for anomalous behavior and then refers to a database of known suspicious addresses. Threats are highlighted with an alert sent to the network administrator. A second strand of the service scans the Dark Web for data leaks relating to the protected business with particular attention paid to intellectual property and trade secrets.
As such, Scout is a data loss prevention system and an insider threat protector as well as a threat-protection system. Scout doesn’t include any remediation procedures. When a Dark Web threat is spotted, Scout raises an alert in the monitoring dashboard. It is up to the network administrator to shut down the traffic either manually or by deploying threat mitigation software.
The service also protects the brands and reputation of customers by scanning all websites for harmful content about those companies. The relevant source and text of the discovered content is then posted in the Scout dashboard.
Who is it recommended for?
This is a valuable package because it combines two services. You will need to have an IDS on your network. There are many excellent free NIDS available and you could also consider a SIEM system as an alternative to the DigitalStakeout system.
Pros:
- Comprehensive Searches: Scans all hacker forums and sales sites
- Retroactive Discovery: Identifies account credentials that have already been stolen
- Customizable Alerts: Cuts out notification flooding
Cons:
- Informational Resource: A source of information on threats rather than a system to prevent attacks
7. ACID Intelligence
The ACID Intelligence service gathers threat intelligence from social networks, criminal sites, chat systems, the Deep Web, and the Dark Web. The information found from these sources allows the service to warn its customers of any threats that may be about to occur and also of any data leaks that have occurred.
Key Features
- Extensive Research: Deep, Dark, and clear Web scanning
- Customizable Alerts: Reduces excessive notifications
- Employee Activity Research: Scans social media and chat systems
Why do we recommend it?
ACID Intelligence is a bot-driven scanner of the Dark Web and social media. This is very similar to DarkOwl Vision in that it is an automated service that occurs without the involvement of the client once you enter identities to add to the search list. The system will notify you if it discovers a data leak or a threat.
The data searches are performed by web bots and so they continue to operate around the clock. The data type that the threat intelligence system looks for include account credentials, e-mail addresses and email contents, domain names, payment card data, intellectual property, insider information, personal information about employees, and mentions of the company and its employees in the context of threats.
Customers of the service get access to an account-protected dashboard where alerts are displayed when cyber threat intelligence related to that has been identified. This information is sent to the console as soon as it is encountered and it is also sent to a key contact at the client company via email.
Who is it recommended for?
Dark Web scanners are useful for every business. You don’t need to have any cybersecurity expertise to use this service but you will need administrator skills to deal with the information that you receive if a threat is detected. For example, you will need to force all users to change their passwords if a credentials leak is detected.
Pros:
- Threat intelligence: Identifies attack plans as well as stolen account credentials
- Deployment Options: Offers a hardware-based version for public sector buyers
- Remediation Automation: Can feed data into SIEM and SOAR packages
Cons:
- No Free Trial: You can’t test the system before buying
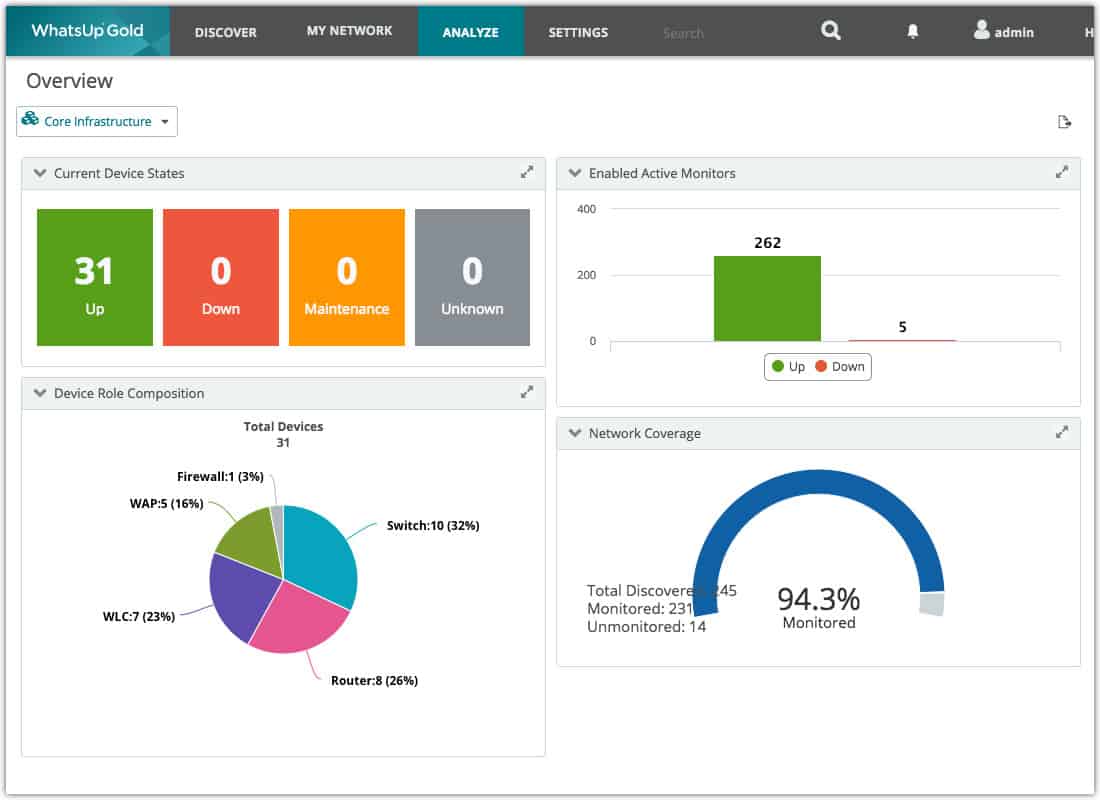
8. Progress WhatsUp Gold
WhatsUp Gold is a network monitoring system. The software for this system installs on Windows Server. The core module of this platform is a network device monitor and it can be enhanced by a number of add-on modules. One of those add-ons is the Network Traffic Analyzer.
Key Features
- Network Scanner: Monitors suspicious network activity
- Traffic Analysis: Tracks connections out to Dark Web
- Breach Notifications: Alerts for possible intrusion
Why do we recommend it?
Progress WhatsUp Gold is a network device monitoring system that has add-on modules to watch over other resources. One of those additional units is a traffic analyzer. The WhatsUp Gold Network Traffic Analyzer includes a threat intelligence reference database that lists known entrance and exit points for the Tor network. Tor provides source and path obfuscation across the internet and is sometimes used by hackers to cover their tracks.
The Network Traffic Analyzer is able to trace the source of incoming traffic and watch where outgoing traffic goes to. The service maintains a database of Tor network entry and exit points and keeps this list constantly updated. When the Network Traffic Analyzer spots one of these addresses as a source or destination of traffic on the network, it alerts the network administrator.
Not all traffic on Tor is malicious. However, there needs to be a reason why someone within your company should be accessing the network at work. The information that Tor traffic is on your network will allow you to identify points for further investigation.
Who is it recommended for?
The Tor detector of WhatsUp Gold is a unique feature that almost no other network threat detection system provides. However, this reference can result in a lot of false-positives because there is a lot of legitimate traffic on the Tor network. Manby types of threats such as DDoS attacks, phishing, and spam email do not use the Tor network – they use source address spoofing instead. So, the cybersecurity value of this service is up for debate.
Pros:
- Connection Tracking: Can identify data transfers out to hacker sites
- Anomaly Detection: Spots suspicious communication, which can indicate the presence of an advanced persistent threat
- Historical Analysis: Provides analysis of external communications over time
Cons:
- General Traffic Analysis: Not specifically a Dark Web scanner
9. Dashlane Business
The Dashlane Business package is a complete account protection service. It includes password protection, secure file storage, and Dark Web site scanning. The scanner looks for login credentials, credit card numbers, Social Security numbers, phone numbers, and postal and IP addresses – all both for the company and for its employees.
Key Features
- Team Credentials Management: Confidential password distribution
- Reduces Risk: Protects privileged passwords
- Password Protection: Encrypts all passwords
Why do we recommend it?
Dashlane Business is a bot-based Dark Web scanner, similar to ACID Cyber Intelligence and DarkOwl Vision. You enter your business’s identities in the Dashlane dashboard and the service then performs an extensive initial Dark Web scan specifically for those markers. After that, your identities are added to the database of words to match for in the regular, periodic sweeps by the Dashlane bots.
This is a cloud-based service and it includes access to the Dashlane customer dashboard through a browser or a mobile device app. When a customer signs up for the service, the Dashlane bots perform an initial Dark Web sweep to discover all existing data about that business. From then on, the company’s identity will be part of the search bot’s target terms and if any new instances of corporate data arise, the Dashlane system notifies that customer immediately. Alerts appear in the dashboard and are also sent out by email.
Who is it recommended for?
The Dashlane system is one of the options that all businesses should consider to get business identity protection. This service, like the ACID and DarkOwl systems, is a hands-off process that doesn’t require any involvement from the technicians of the protected company. If a data disclosure is detected, you get a notification in the Sashlane dashboard. It is then up to you to take evasive action.
Pros:
- Encryption: Makes passwords impossible for either people or programs to read
- Automatic Password Field Filling: Enables the implementation of complex passwords that are impossible to guess
- Breach Research: Includes a Dark Web scanner to discover stolen credentials
Cons:
- Dark Web Scanning is Secondary: Mainly focused on password protection
10. Have I Been Pwned?
Have I Been Pwned? is a Clear Web site that performs free searches of the Deep Web and the Dark Web for personal or business information. It isn’t necessary to sign up for an account, you just need to enter an email address in the single input field on the service’s Home page.
Key Features
- No Charge: Free service
- Disclosure Database: Searches known lists for email addresses
- Ongoing Alerts Available: Set up an account for free
The results of the search show all data leak events that involved that email address, resulting in the address being displayed in Dark Web attack lists. The service only reports on email address-related data leaks.
Companies can get a scan for all email addresses on their domains. It is also possible to set the service to permanently monitor for new incidences and notify you by email should they arise. You have to verify that you are the owner of the email domain to use this service.
Pros:
- Stores Compromised Accounts: Maintains copies of commercially available stolen email credentials
- Online Search: Provides on-demand checks
- Long-Term Vigilance: Lets users sign up for free to get alerts of future breaches
Cons:
- Suitable for the General Public: Not suitable for businesses tracking many email addresses
Defeat the Dark Web
There are many defense strategies to protect yourself from hackers and the ability to find out what hackers have on you is a distinct advantage. Some of the tools in this list include threat remediation processes, while others just warn you which accounts have been compromised and leave you to fix the problem. You will probably have your own preferred working practices that will lead you to one of these groups.
Dark Web Monitoring FAQs
What do I do if I find my employee information on the Dark Web?
If you find information about your employees on the Dark Web, you are lucky. It is better to know about this disclosure than to be unaware. There is nothing you can do to wipe that information from other sites. However, this is a warning to tighten up your network security and enforce a password change on all system users through your access rights management system.
Why is the dark web allowed to exist?
There is nothing intrinsically illegal about the configuration of the Dark Web. All forms of communication can be used for good or evil. Secure chat apps are frequently used by smugglers, terrorists, and child molesters, but no one suggests that WhatsApp or Signal should be shut down.
How often should I scan the Dark Web for data breaches?
The best Dark Web scanners operate constantly. There is no point in scheduling a total scan of the Dark Web say, once a month because as soon as credentials on your network are published, your business is exposed. The best Dark Web scans spot protected accounts as soon as their details appear on a Dark Web forum, enabling users and account administrators to change login credentials immediately.
See also: Best VPN for Dark Web











Hmm, I also use occasionally Immuniweb, and get good results. Specially with cybersquating domains…
Free dark web monitoring tool: https://www.immuniweb.com/darkweb/
That’s a good suggestion. ImmuniWeb has some excellent tools.
To be honnest, i’ve tried Haveibeenpwned and ImmuniWeb.
ImmuniWeb gave me no result except fake Cybersquatting Domain Name. None of them are registered or used.
the 4 others type of breach (dark web security incidents, phishing, typosquatting, fake accounts on social media) gave nothing too.
I’ve tried Haveibeenpwned for emails and domain, and we have found some real breach (online services) that their Database has been exposed on DW, and it tell what’s the nature of data compromised. They have an API that cost almost nothing per month to do check when you want automatically.
Hello, I will keep it simple
will this program help me find out who the hacker who is disrupting my life and mind.
Im currently working off other computers and i need to try to stay under the radar. I have a plan and i need to increase my capabiltiy to be able to find out who and why
I have ideas. and Im not letting down because they want to destroy my life because of jealousy
they took away the one person i like and who knows it may be him. lol
i dont want to invest into something I don’t need. they have hacked my home, they come into my house and disable security systems, etc. im computer savy but not an expert, im becoming one.
Thank you albert.
they monitory my phones, hacked it yesterday watching me. they monitor my web searches and dark web, you name it. I have nothing to hide but to find out who and that will give me the anwer police needs, they are trying to make me look like im the crazy person, but they have it all wrong. im becoming crazy and obsessed with this bc i allowed them in my life by choice thinking they were harmless and people are not all good.
Albert Martinez
can you pls get back to me