In this Active Directory tutorial we’re going to look at what Active Directory is, how to use it, and Active Directory tools like ManageEngine AD360 and SolarWinds Access Rights Manager.
Topics include:
- What is Active Directory?
- What does Active Directory do?
- How to Set Up Active Directory
- How to Use Active Directory: Setting Up a Domain Controller, Creating Directory Users
- Active Directory Events to Monitor
- Trust Relationships (and Trust Types)
- An Overview of Active Directory Forests and Trees
- Active Directory Reporting (with SolarWinds Access Rights Manager)
- How to Find the Source of Account Lockouts in Active Directory
What is Active Directory?
Active Directory is a directory service or container which stores data objects on your local network environment. The service records data on users, devices, applications, groups, and devices in a hierarchical structure.
The structure of the data makes it possible to find the details of resources connected to the network from one location. In essence, Active Directory acts like a phonebook for your network so you can look up and manage devices easily.
What does Active Directory do?
Active Directory (AD) is a Microsoft directory service that organizes, manages, and secures network resources within a Windows-based environment. Used widely by businesses, AD offers a centralized way to handle permissions, security policies, and network resources like users, computers, printers, and applications. With AD, administrators can effectively control and streamline network operations, making it an essential tool for managing complex IT infrastructures.
One major reason to use Active Directory is centralized management. AD’s directory database contains detailed information about each network object, from user accounts and devices to access permissions. This centralized structure simplifies the enforcement of security policies and configurations across all devices and users in the organization, ensuring consistency and enhancing network security.
Another key advantage is Group Policy Management, which allows administrators to implement network-wide settings, such as password requirements, software updates, and security restrictions, with ease. This capability minimizes manual configuration and helps maintain standardized security measures.
Single Sign-On (SSO) is also a compelling reason to use AD. SSO allows users to access multiple applications and services with one set of credentials, reducing the need for multiple logins. This not only boosts user convenience but also enhances security by lowering the number of passwords at risk.
Active Directory is thus crucial for organizations seeking centralized control, streamlined administration, and a secure, efficient network environment.
Network administrators turn to AD for these main strengths:
- User Management Provides a centralized directory for creating, managing, and securing user accounts and groups within an organization.
- Authentication Verifies the identity of users and computers in a Windows domain.
- Authorization Manages user permissions, determining who gets access to which resources and what actions they can perform.
- Domain Services Structures your network resources, allowing for efficient organization, management, and search of resources within a domain.
- Policy Enforcement Allows administrators to enforce security and policies across the network through Group Policy Objects (GPOs).
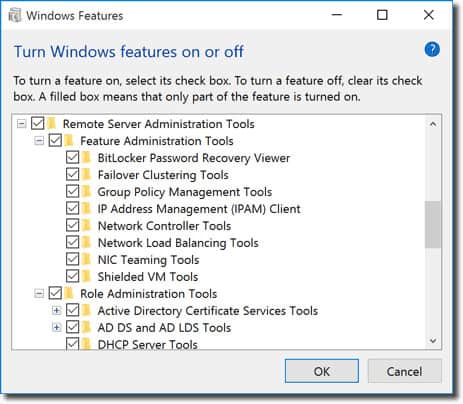
How to set up Active Directory (with RSAT)
To begin you will need to first make sure that you have Windows Professional or Windows Enterprise installed otherwise you won’t be able to install Remote Server Administration Tools. Then do the following:
For Windows 10 Version 1809 and Windows 11:
- Right-click on the Start button and go to Settings > Apps > Manage optional features > Add feature.
- Now select RSAT: Active Directory Domain Services and Lightweight Directory Tools.
- Finally, select Install then go to Start > Windows Administrative Tools to access Active Directory once the installation is complete.
For Windows 8 (And Windows 10 Version 1803)
- Download and install the correct version of Server Administrator Tools for your device: Windows 8, Windows 10.
- Next, right-click the Start button and select Control Panel > Programs > Programs and Features > Turn Windows features on or off.
- Slide down and click on the Remote Server Administration Tools option.
- Now click on Role Administration Tools.
- Click on AD DS and AD LDS Tools and verify AD DS Tools has been checked.
- Press Ok.
- Go to Start > Administrative Tools on the Start menu to access Active Directory.
How to use Active Directory: How to set up a Domain Controller, Creating Directory Users
How to set up A Domain Controller
One of the first things you need to do when using Active Directory is to set up a domain controller. A domain controller is a central computer that will respond to authentication requests and authenticate other computers throughout the network. The domain controller stores the login credentials of all other computers and printers.
All other computers connect to the domain controller so that the user can authenticate every device from one location. The advantage of this is that the administrator won’t have to manage dozens of login credentials.
The process of setting up a domain controller is relatively simple. Assign a static IP address to your Domain Controller and install Active Directory Domain Services or ADDS. Now follow these instructions:
- Open Server Manager and click Roles Summary > Add roles and features.
- Click Next.
- Select Remote Desktop Services installation if you’re deploying a domain controller in a virtual machine or select role-based or feature-based installation.
- Select a server from the server pool.
- Select Active Directory Domain Services from the list and click Next.
- Leave the Features checked by default and press Next.
- Click Restart the destination server automatically if required and click Install. Close the window once the installation is complete.
- Once the ADDS role has been installed a notification will display next to the Manage menu. Press Promote this server into a domain controller.
- Now click Add a new forest and enter a Root domain name. Press Next.
- Select the Domain functional level you desire and enter a password into the Type the Directory Services Restore Mode (DSRM password) section. Click Next.
- When the DNS Options page displays click Next again.
- Enter a domain in the NetBios Domain name box (preferably the same as the root domain name). Press Next.
- Select a folder to store your database and log files. Click Next.
- Press Install to finish. Your system will now reboot.
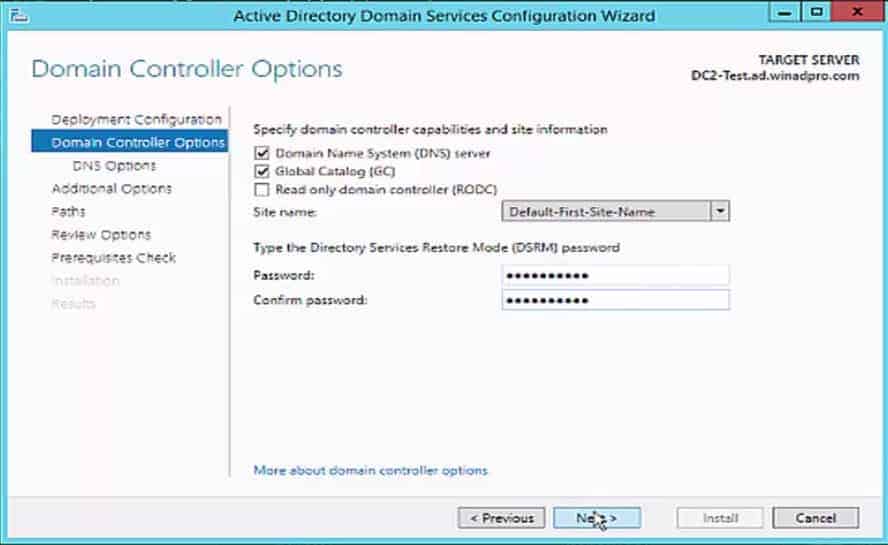
Add a Domain Controller to an Existing Domain in Windows Server 2016
The procedures for adding a domain controller to an existing domain in Active Directory are the same, no matter which operating system you have. However, these instructions were organized during an exercise on Windows Server 2016. It is always a good idea to have at least two domain controllers in your AD domain just in case one goes down.
The second Domain Controller is a separate computer from the one identified for your first Domain Controller. That second computer needs to be set up with Windows Server 2016. Get it fully patched and assign it an IP address before starting the AD setup on that machine. Then follow these steps:
- Open Server Manager, click on the Manage option on the menu ribbon and select Add Roles and Features.
- In the opening screen of the wizard, click on Next.
- In the Installation Type screen select the Role-based or feature-based installation radio button and click on Next.
- In Server Selection leave the only server in the list highlighted and press Next.
- In the Server Roles screen, Check the Active Directory Domain Services box. A dialogue box appears. Click on the Add Features button.
- Back in the main feature selection screen, click the Next button.
- This cycles through to the Features screen. Just click on the Next button. In the AD DS screen, click on the Next button.
- Finally, click the Install button. Once the installation process finishes, you will see a notice telling you that additional steps are required. Click on the link that says Promote this server to a domain controller. This brings up the Deployment Configuration screen.
- Leave the Add a domain controller to an existing domain radio button active. At the bottom of the list of options, you will see <no credentials provided>. Click on the Change button next to that.
- Enter the username and password of the Administrator account on the AD instance that you first set up. This username should be in the format <domain>\Administrator. Click OK.
- On return from the login popup, you will see that the Domain field has been populated with the domain that you entered for the user account. Click on the Next button.
- Decide whether to make this a read-only domain controller (RODC). If so, check that box in the Options screen, if not, check both the DNS server and Global Catalogue boxes.
- Enter a DSRM password and confirm it. Click on the Next button. You will see a warning but just click on the Next button again.
- In Additional Options choose your original domain controller for the Replicate from: field. Click on Next.
- Leave all of the paths in their default settings and click on Next. In the Review Options screen, click Next.
- The system will perform a prerequisites check. If that completes satisfactorily, the Install button will become active. Click it.
- Wait for the installation to complete. The computer will reboot. Log in to the machine.
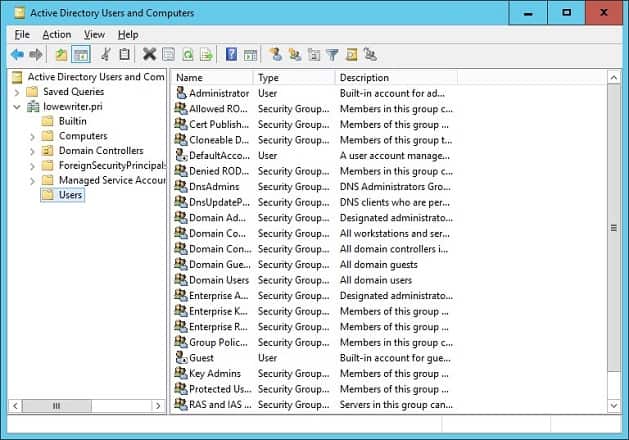
Go back to your original domain controller computer and open Active Directory Users and Computers and you will see that your new DC is listed there in the Domain Controllers folder.
Creating Active Directory Users
Users and computers are the two most basic objects that you will need to manage when using Active Directory. In this section, we’re going to look at how to create new user accounts. The process is relatively simple, and the easiest way to manage users is through the Active Directory Users and Computer or ADUC tool that comes with the Remote Server Administration Tools or RSAT pack. You can install ADUC by following the instructions listed below:
Install ADUC on Windows 10 Version 1809 and Higher or Windows 11:
- Right-click on the Start button and click Settings > Apps, then click Manage optional features > Add feature.
- Select RSAT: Active Directory Domain Services and Lightweight Directory Tools.
- Select Install and wait for the installation to complete.
- Go to Start > Windows Administrative Tools to access the feature.
Install ADUC on Windows 8 and Windows 10 Version 1803 or Lower:
- Download and install Remote Server Administrator Tools for your version of Windows. You can do so from one of these links here:
Remote Server Administrator Tools for Windows 10, Remote Server Administrator Tools for Windows 8, or Remote Server Administrator Tools for Windows 8.1.
- Right-click on Start > Control Panel > Programs > Programs and Features > Turn Windows features on or off.
- Scroll down and select Remote Server Administration Tools.
- Expand Role Administrator Tools > AD DS and AD LDS Tools.
- Check AD DS Tools and press Ok.
- Go to Start > Administrative Tools and select Active Directory Users and Computers.
How to Create New Users with ADUC
- Open the Server Manager, go to the Tools menu and select Active Directory Users and Computers.
- Expand the domain and click Users.
- Right-click on the right pane and press New > User.
- When the New Object-User box displays enter a First name, Last name, User logon name, and click Next.
- Enter a password and press Next.
- Click Finish.
- The new user account can be found in the Users section of ADUC.
Active Directory Events to Monitor
Like all forms of infrastructure, Active Directory needs to be monitored to stay protected. Monitoring the directory service is essential for preventing cyber-attacks and delivering the best end-user experience to your users.
Below we’re going to list some of the most important network events that you should look out for. If you see any of these events then you should investigate further ASAP to make sure that your service hasn’t been compromised.
| Current Windows Event ID | Legacy Windows Event ID | Description |
|---|---|---|
| 4618 | N/A | A security event pattern has been recognized. |
| 4649 | N/A | A replay attack was detected (potentially a false positive). |
| 4719 | 612 | A system audit policy was changed. |
| 4765 | N/A | SID History added to an account. |
| 4766 | N/A | The attempt failed to add SID History to account. |
| 4794 | N/A | Attempt to launch Directory Services Restore Mode. |
| 4897 | 801 | Role separation enabled. |
| 4964 | N/A | Special groups have been assigned a new logon. |
| 5124 | N/A | Security updated on OCSP Responder Service. |
| N/A | 550 | Potential DoS attack. |
| 1102 | 517 | Audit log was cleared. |
Understanding Active Directory: Forests and Trees
Forest and trees are two terms you will hear a lot when delving into Active Directory. These terms refer to the logical structure of Active Directory. Briefly, a tree is an entity with a single domain or group of objects that is followed by child domains. A forest is a group of domains put together. When multiple trees are grouped together they become a forest.
Trust Relationships and Domain Connectivity in Active Directory
Trees in the forest connect to each other through a trust relationship, which enables different domains to share information. All domains will trust each other automatically so you can access them with the same account info you used on the root domain.
Hierarchy and Database Management in Active Directory Forests
Each forest uses one unified database. Logically, the forest sits at the highest level of the hierarchy and the tree is located at the bottom. One of the challenges that network administrators have when working with Active Directory is managing forests and keeping the directory secure.
Choosing the Right Forest Design for Network Administration
For example, a network administrator will be tasked with choosing between a single forest design or multi-forest design. The single-forest design is simple, low-cost and easy to manage with only one forest comprising the entire network. In contrast, a multi-forest design divides the network into different forests which is good for security but makes administration more complicated.
How to Find the Source of Account Lockouts in Active Directory
The easiest way to find account lockouts in Active Directory is to use the Event Viewer, which is built into Windows. Active Directory generates Windows Events messages for each of its actions, so your first task is to track down the right event log.
- Open a PowerShell window by pressing the Windows key and R together. In the Run popup, type powershell and hit ENTER.
- At the command line type (get-addomain).pdcemulator
- Note down the address of the PCD Emulator domain controller, which will be shown on the next line.
- Type exit to close the PowerShell window.
- The standard event log viewer that is built into the Windows operating system will help you find the account lockouts.
- Go to the DC named as the PDC Emulator.
- Open the Event Viewer by expanding Windows Administrative Tools in the Start menu and clicking on the Event Viewer entry in that submenu.
- In the Event Viewer, expand the Windows Logs node in the left-hand menu tree. Click on Security. The Security events list will appear in the central panel of the Event Viewer.
- In the right panel of the Event Viewer, click on Filter Current Log, which will open a popup window.
- In the Event IDs field replace <All Event IDs> with 4740.
- Select a time horizon in the Logged drop-down list at the top of the form.
- Optionally, enter a username or a hostname if you are specifically looking for a lockout on a specific user or resource.
- Press OK.
- Double click on the log entry that relates to the user or resource that interests you and that has a timestamp that matches the moment you think the lockout occurred. This will open the Event Report.
The Event Report will show you the user that was locked out, the computer that the event occurred on, and the source, or reason for the lockout.
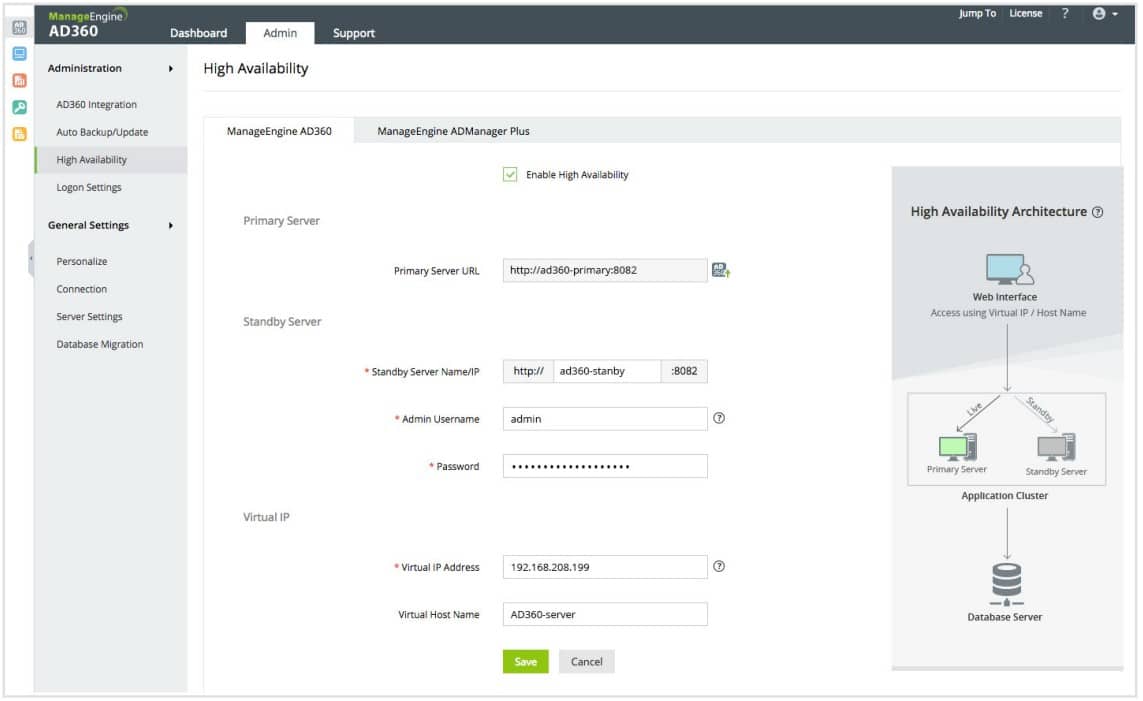
Active Directory Management with ManageEngine AD360 (FREE TRIAL)
ManageEngine AD360 is a compendium of ManageEngine Active Directory management systems plus a backup and recovery service. This package represents a good example of the tools that are available to automate the management tasks surrounding Active Directory usage. It is able to interface to AD implementations for SharePoint, Microsoft 365, Azure, and AWS, as well as the Active Directory system that you have in your Windows Server operating system.
Pros:
- Package of AD tools
- Enforces multi-factor authentication
- Audits AD objects to improve group management
- Detects inactive accounts
- User behavior analytics
Cons:
- You might only need one of the component tools
ManageEngine AD360 is available on a 30-day free trial.
Trust Relationships (and Trust Types)
As mentioned above, trusts are used to facilitate communication between domains. Trusts enable authentication and access to resources between two entities. Trusts can be one-way or two-way in nature. Within a trust, the two domains are divided into a trusting domain and a trusted domain.
Types of Trust Relationships: One-Way and Two-Way
In a one-way trust, the trusting domain accesses the authentication details of the trusted domain so that the user can access resources from the other domain. In a two-way trust, both domains will accept the other’s authentication details. All domains within a forest trust each other automatically, but you can also set up trusts between domains in different forests to transfer information.
Setting Up Trusts: Using the New Trusts Wizard in Active Directory
You can create trusts through the New Trusts Wizard. The New Trust Wizard is a configuration wizard that allows you to create new trust relationships. Here you can view the Domain Name, Trust Type, and Transitive status of existing trusts and select the type of trust you want to create.
Trust Types
There is a range of trust types in Active Directory. We’ve listed these in the table below:
| Trust Type | Transit Type | Direction | Default? | Description |
|---|---|---|---|---|
| Parent and child | Transitive | Two-way | Yes | A parent and child trust is established when a child domain is added to a domain tree. |
| Tree-root | Transitive | Two-way | Yes | A tree-root trust is established the moment a domain tree is created within a forest. |
| External | Non-transitive | One-way or two-way | No | Provides access to resources in a Windows NT 4.0 domain or a domain located in a different forest that isn’t supported by a forest trust. |
| Realm | Transitive or non-transitive | One-way or two-way | No | Forms a trust relationship between a non-Windows Kerberos realm and a Windows Server 2003 domain. |
| Forest | Transitive | One-way or two-way | No | Shares resources between forests. |
| Shortcut | Transitive | One-way or two-way | No | Reduces user logon times between two domains within a Windows Server 2003 forest. |
Active Directory Reporting with SolarWinds Access Rights Manager
Generating reports on Active Directory is essential for optimizing performance and staying in accordance with regulatory compliance. One of the best Active Directory reporting tools is SolarWinds Access Rights Manager (ARM). The tool has been created to increase visibility into how directory credentials are used and managed. For example, you can view accounts with insecure configurations and credential abuse that could indicate a cyber attack.
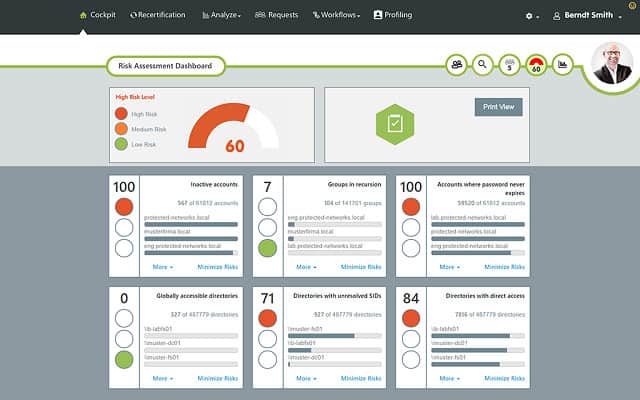
Using a third-party tool like SolarWinds Access Rights Manager is beneficial because it provides you with information and features that would be much more difficult or impossible to access through Active Directory directly.
Pros:
- Makes AD management easier through visualizations and reporting
- Provides a clear look into permission and file structures through automatic mapping and visualizations
- Preconfigured reports make it easy to demonstrate compliance
Cons:
- SolarWinds Access Rights Manager is an in-depth platform designed for sysadmin which may take time to fully learn
As well as generating reports you can automatically delete inactive or expired accounts that cybercriminals target. SolarWinds Access Rights Manager starts at $3,444 (£2,829). There is also a 30-day free trial version that you can download.
See also: Access Rights Management
Final Words
Active Directory is one of the best tools for managing resources in your network. In this article, we’ve just scratched the surface of the potential of this tool. If you’re using Active Directory remember that it is a potential entry point for cyber attackers. Making a note of key directory events and use a directory monitor will go a long way towards minimizing the risk of a malicious attack and protecting the availability of your service.
Active Directory FAQs
What is the difference between an Active Directory and a Domain controller?
Active Directory is an authentication system. A domain is a collection of objects, which are users, computers, and devices that all have access rights managed in the same Active Directory database. The domain controller is the authentication management system that implements Active Directory functions on the domain’s database objects.
How to enable the Security Auditing of Active Directory?
In order to start security auditing within Active Directory:
- Log in to Windows Server as an administrator.
- Go to Start, click on Administrative tools, and select Group policy management console.
- Get to the domain/OU to be audited.
- Right-click on the Group Policy Object, and choose Edit. This will open the Group Policy Management Editor.
- In the left-hand tree menu, expand Computer Configuration, then Policies, expand Windows Settings, then Security Settings, and finally Local Policies. Click on Audit Policies.
- In the main panel of the Editor, click on Audit object access and select both the Success and Failure options.
- Click on Audit directory service access and select both the Success and Failure options.
What is the difference between Active Directory and LDAP?
The Lightweight Directory Access Protocol (LDAP) is an open standard that outlines how access rights can be managed. Active Directory is an access rights management system, written by Microsoft. Active Directory is an evolution of the concepts defined in LDAP.
What are Active Directory and Single sign-on and what are the differences between them?
Single sign-on (SSO) gives each user access to several systems with just one authentication procedure. Active Directory (AD) is an access rights management system that can implement an SSO environment.
Can I install Active Directory on client operating systems?
No. Active Directory is a server function and it is integrated into the Windows Server operating system. Logically, any client running Active Directory would become a server.
What should you look for in Active Directory tools?
We reviewed the market for Active Directory monitoring software and analyzed the options based on the following criteria:
- An interface that offers an easier way to organize Active Directory
- Reporting functions for auditing
- The ability to monitor many AD instances
- Tracking for replication, synchronization, backup, and migration
- Fast account status identification
- A free trial that provides a no-cost assessment period
- Value for money from a tool that pays for itself in efficiency improvements





This is a very clear and detailed resource containing valuable, easy to understand information. Thank you!
excellent article to understand AD and different terms.
This is one of the best articles for beginner to lean about AD.
Thanks for posting this clear and eye-opening article.
Nicely put together. It’s a brilliant rundown. Good job!
Easy to understand than you so much
it is good explanation. especially in installing and configuring the active directory. thank you