What is an Always On VPN?
Microsoft DirectAccess (originally introduced with Windows Server 2008 R2) was once recognized as the best Microsoft VPN-like solution that connects users to internal corporate networks over the internet without the need for a traditional VPN. However, over the years, DirectAccess proved difficult to implement for most organizations and had limitations that affected its adoption. This led many organizations to resort to using alternative third-party solutions to get past the challenges. As a result of those developments, Microsoft decided to introduce new technology in Windows Server 2016 and Windows 10 that is designed to do all that DirectAccess promised but couldn’t deliver and much more. This new remote access technology is called Always On VPN.
Here is our top pick for an Always On VPN:
- Check Point’s SASE Always On VPN EDITOR’S CHOICE solution enhances device security and supports cloud-agnostic integration, enabling secure access to corporate networks for remote workers, seamless integration with cloud platforms, and granular user segmentation. It offers additional features like secure remote access, IP whitelisting for network control, and quality assurance testing with extensive server coverage for international market analysis. Access a free demo.
Microsoft Always On VPN is a replacement for DirectAccess VPN technology. It was designed to provide a secure connection to the internet for individual users, as well as secure remote access to corporate networks for corporate users. The term “Always On” means that the VPN connection is always on and securely connected after the connection has been established. Supported clients of Always On VPN include domain-joined and non-domain-joined (workgroup) clients, Azure AD-joined devices, and BYOD clients.
With Always On VPN, IT administrators can create and deploy secure VPN solutions even to applications hosted on Azure with minimal effort. To take full advantage of Always On VPN’s advanced features, devices should be joined to Azure AD. By integrating Always On VPN with Azure, organizations can easily implement Identity and Access Management (IAM) processes and grant mobile employees access to cloud or on-premise applications with peace of mind.
Always On VPN as a generic term
Always On VPN originated as a Microsoft-specific service; the term has since been adopted more broadly and now appears as a feature in many VPN solutions.
“Always On VPN” describes a configuration that keeps a device continuously connected to a secure virtual private network without requiring user intervention. This persistent connection is especially important for protecting data and maintaining privacy when devices move between trusted and untrusted networks. By automatically establishing a VPN connection at startup or when network changes occur, it ensures all traffic is encrypted and routed through a secure server, reducing the risk of interception or eavesdropping.
Most VPNs implement Always On functionality using two main mechanisms. The first involves configuring the VPN client to launch automatically during system startup, ensuring the connection is established as part of the desktop’s routine processes. The second is the kill switch, which blocks internet access if the VPN connection drops or is not active. This prevents unprotected traffic from leaving the device and ensures the connection is re-established securely. For the kill switch to work effectively, the VPN client must be active and set to a default server location, making the system particularly useful for corporate VPNs that connect remote workers to office networks or link multiple sites.
Always On VPN is common in industries such as healthcare, finance, and government, where compliance and data security are critical. Its capabilities typically include multi-factor authentication, support for multiple device platforms, and integration with management tools for simplified configuration and monitoring. In practice, the Always On VPN client functions as a secure gateway to corporate resources, maintaining continuous protection across all network activity.
How does Always On VPN work?
Always On VPN works as an automated service that allows a client to establish a VPN connection without any user interaction unless a multi-factor authentication mechanism is enabled. This is made possible by a technology known as the VPNv2 Configuration Service Provider (CSP) that allows the built-in Windows 10 VPN client to be configured using an MDM solution such as Intune, or PowerShell. Always On VPN is infrastructure independent and it does not require any additional cost for software licenses.
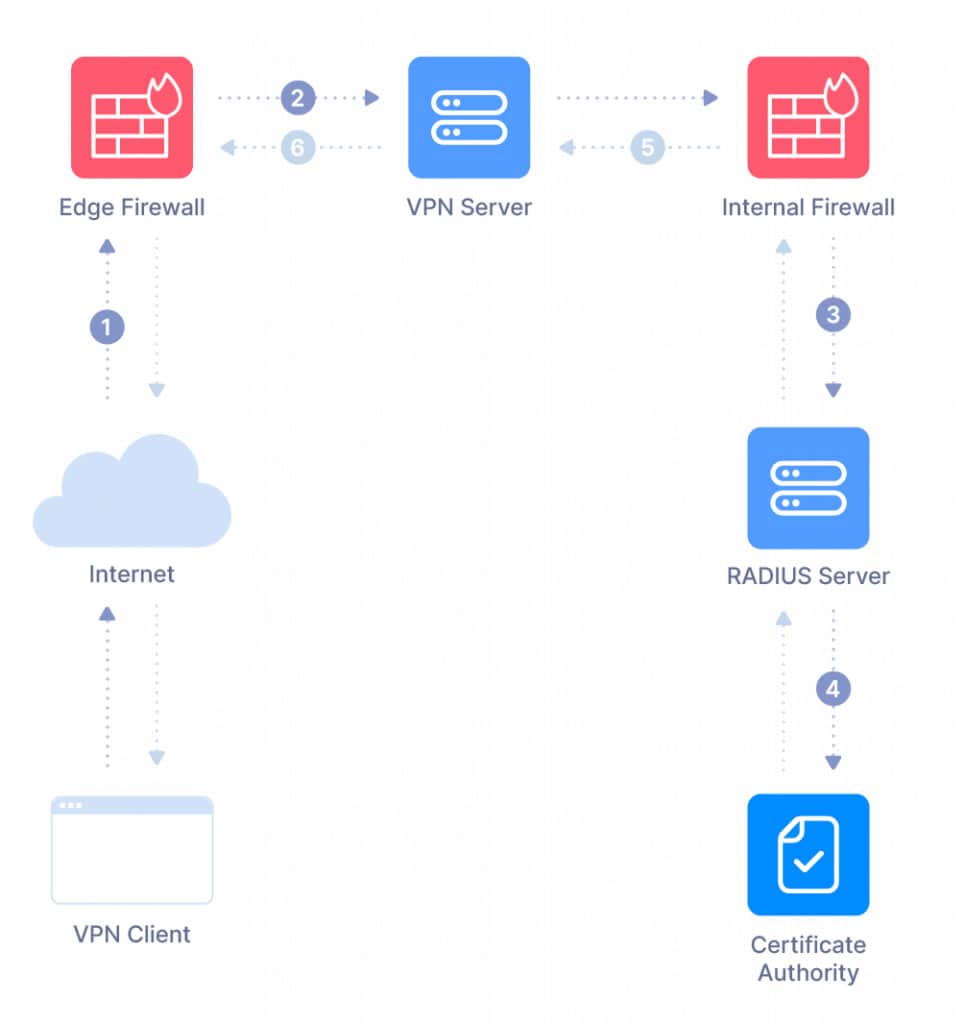
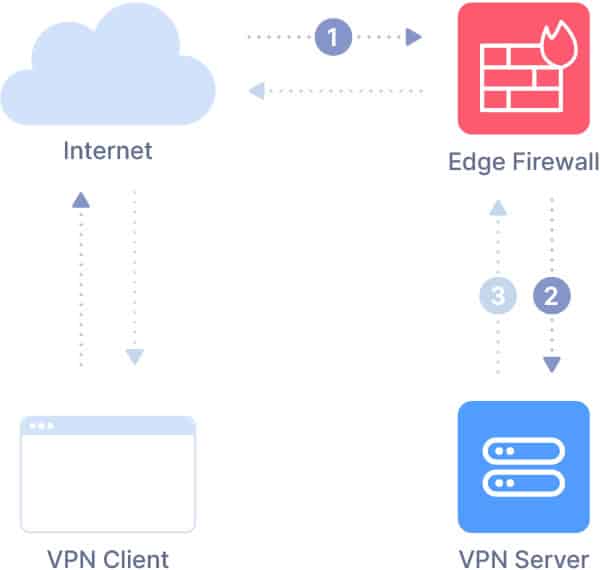
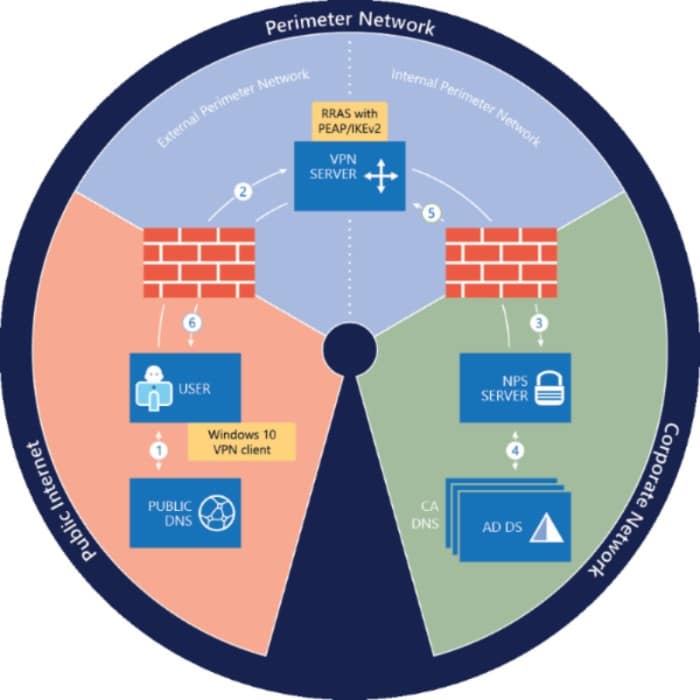
It can be deployed using Windows Routing and Remote Access (RRAS) or any third-party VPN device. A certificate authority is required to issue certificates to the servers and clients. The certificates will be used to authenticate the VPN connection. Authentication can be provided by Windows Network Policy Server (NPS) or any third-party RADIUS platform. Always On VPN connections use two types of tunnels for secure remote access services. These two types of tunnels are
User Tunnels: The user tunnel is established when a user logs into their network device such as a computer to access their resources in the corporate network through the Always On VPN service. This type of tunnel is ideal for granting access to file shares or applications.
Device Tunnels: A user does not need to be logged into a computer for a device tunnel to be established. The device tunnel is established once a computer is powered on and connected to the internet. This type of tunnel is ideal for granting access to Active Directory or other management servers like Configuration Manager.
Because device and user tunnels operate separately from their VPN profiles, they can be connected at the same time and use different authentication methods or configuration settings. Always On VPNs use the default Windows 10 built-in Extensible Authentication Protocol (EAP) for secure authentication via username and password or certificate-based login methods. EAP-based authentication can be used only with a built-in VPN type such as IKEv2, L2TP, PPTP, or Automatic.
How can you deploy Always On VPN in your organization?
Always On VPN can be set up as a remote-access or business VPN that allows mobile employees or remote workers to access their company’s intranet from home or anywhere in the world using their personal computers or mobile phones. Always On VPN technology provides significant advantages for enterprise customers looking for simplified automatic access to the corporate network while maintaining a high level of security. It can easily integrate with most cloud services such as Azure, AWS, Salesforce, and others while preventing service disruptions for mobile employees.
There are two deployment scenarios for the Microsoft Always On VPN technology. The first is Always On VPN only, and the second is Always On VPN with VPN connectivity using conditional Azure Active Directory access. Always On VPN allows network administrators to set granular routing policies from users to the application level. This helps secure access to critical business applications that require special remote access. The following infrastructure components are required to implement an Always On VPN solution in an organization:
- Domain Controllers
- DNS Servers
- Network Policy Server (NPS)
- Certificate Authority Server (CA)
- Routing and Remote Access Server (RRAS)
Once the infrastructure is set up, you can then enroll and connect clients to your on-premise network securely by making the following changes to your network infrastructure as recommended by Microsoft:
- Active Directory domain infrastructure—both internal and external Domain Name System (DNS) zones are required.
- Active Directory-based Public Key Infrastructure (PKI) and Active Directory Certificate Services (AD CS).
- Modify an existing NPS server configuration or install a new one (either virtual or physical) if there is none.
- RAS Gateway VPN server with support for IKEv2 VPN connections and LAN routing.
- Your perimeter network should include two firewalls configured to allow the traffic that is necessary for the proper functioning of both VPN and RADIUS communications.
- Your perimeter network should also include a server (physical or virtual) with two network adapters to install Remote Access as a RAS Gateway VPN server.
- Physical server or virtual machine (VM) on your perimeter network with two physical Ethernet network adapters to install Remote Access as a RAS Gateway VPN server. VMs require virtual LAN (VLAN) for the host.
- The account to be used for the setup and configuration must have the required admin rights or be a member of the Administrator group.
The table below shows some of the most common features and functionalities of Always On VPN as it applies to corporate organizations and users. If you currently use DirectAccess, Microsoft recommends that “you investigate the Always On VPN functionality carefully to determine if it addresses all of your remote access needs before migrating from DirectAccess to Always On VPN”.
| Functional area | Always On VPN |
|---|---|
| Seamless, transparent connectivity to the corporate network | You can configure Always On VPN to support auto-triggering based on application launch or namespace resolution requests |
| Use of a dedicated Infrastructure Tunnel to provide connectivity for users not signed into the corporate network. | You can achieve this functionality by using the Device Tunnel feature in the VPN profile. |
| Use of manage-out to allow remote connectivity to clients from management systems located on the corporate network | You can achieve this functionality by using the Device Tunnel feature in the VPN profile combined with configuring the VPN connection to dynamically register the IP addresses assigned to the VPN interface with internal DNS services |
| Fall back when clients are behind firewalls or proxy servers | You can configure it to fall back to SSTP (from IKEv2) by using the automatic tunnel/protocol type within the VPN profile. |
| Support for end-to-edge access mode | Always On VPN provides connectivity to corporate resources by using tunnel policies that require authentication and encryption until they reach the VPN gateway |
| Ability to determine intranet connectivity when connected to the corporate network | Trusted network detection provides the capability to detect corporate network connections, and it is based on an assessment of the connection-specific DNS suffix assigned to network interfaces and network profiles |
| Support for servers behind an edge firewall or NAT device | Always On VPN gives you the ability to use protocols like IKEv2 and SSTP that fully support the use of a VPN gateway that is behind a NAT device or edge firewall. |
| Use security groups to limit remote access functionality to specific clients | You can configure Always On VPN to support granular authorization when using RADIUS, which includes the use of security groups to control VPN access |
| Compliance using Network Access Protection (NAP) | The Always On VPN client can integrate with Azure conditional access to enforce MFA, device compliance, or a combination of both |
| Domain-joined devices with Enterprise SKUs requirement. | Always On VPN supports domain-joined, non-domain-joined (workgroup), or Azure AD–joined devices to allow for both enterprise and BYOD scenarios |
| Support for multiple domains and forests | The Always On VPN platform has no dependency on Active Directory Domain Services (AD DS) forests or domain topology because it doesn't require the VPN client to be domain joined to function. |
| Support for both split and force tunnel for internet/intranet traffic separation. | You can configure Always On VPN to support both force tunnel (the default operating mode) and split tunnel natively. |
| Name resolution of corporate resources using FQDN, and DNS suffix | Always On VPN can natively define one or more DNS suffixes as part of the VPN connection and IP address assignment process |
| Support for both IPv4 and IPv6 | With Always On VPN, users can access both IPv4 and IPv6 resources on the corporate network |
Table 1.0 | Always On VPN enterprise features and functionalities | Table Credit: Microsoft
An Always On VPN solution fromCheck Point’s SASE
Check Point’s SASE Always On VPN (GET DEMO)
Many modern businesses have transitioned their local network environment, business applications, and data into the cloud, and conventional VPNs such as those described above are no longer enough to ensure data security. For organizations whose business LAN environment or day-to-day business applications (such as ERP or Active Directory Services) have moved to the cloud, the Check Point’ SASE Always On VPN solution (formerly Perimeter 81) offers the best alternative for cheap and secure access.
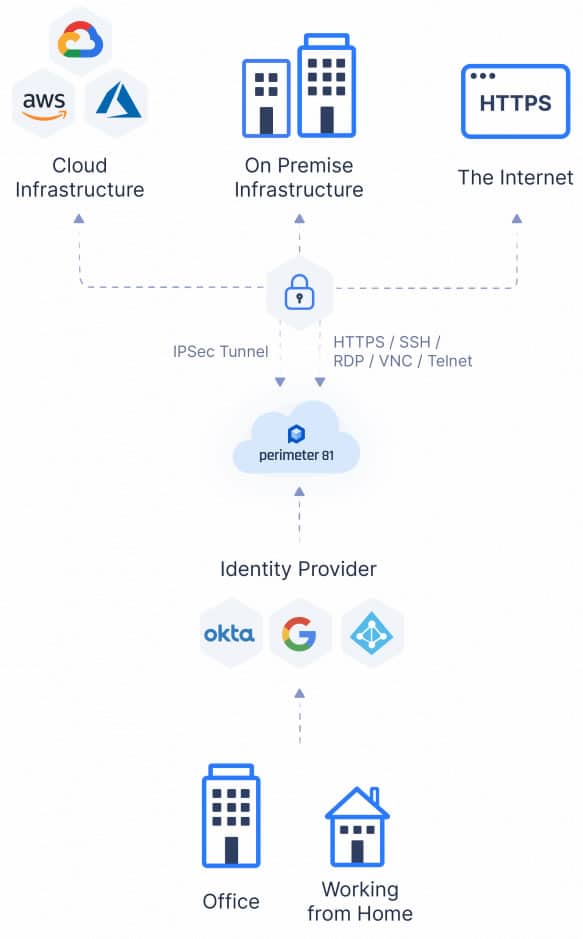
The Check Point’s SASE platform is a scalable hardware-free solution that helps organizations provide secure access to their network infrastructure and digital assets. The solution is ideal for SMBs, especially those looking for a modern alternative to traditional corporate VPN systems. Combined with Secure Access Service Edge (SASE) technology—a network architecture that integrates VPN and SD-WAN capabilities with cloud-native security functions (such as firewalls, CASB, ZTNA), the Check Point’s SASE Always On VPN consists of four key capabilities:
- Unified Network Platform: One cloud-based platform that provides access management, monitoring, permissioning, among other capabilities.
- Zero Trust Network Access (ZTNA): Checks the identity and integrity of devices irrespective of location and provides access to applications and services based on the confidence of device identity and device health in combination with user authentication.
- Multi-Tenant Cloud: Segments the network according to your security policies to ensure better protection for network resources.
- Clients Access Control: Support for 2FA and single sign-on across PC and Mac desktops, iOS and Android devices, and the web.
The Check Point’s SASE Always On VPN solution offers the following benefits to organizations:
- Devices Security: Provides secure access to corporate networks for all remote workers and devices including support for BYOD policies, split tunneling, network auditing, and monitoring
- Cloud Agnostic Integration: One of the biggest advantages of an Always On VPN is that they’re cloud-friendly and cloud-agnostic, which means that it can seamlessly integrate into any cloud-based platform or on-premises environment. Check Point’s SASE Always On VPN technology supports seamless Azure integration, automatic network deployment, multi-tunneling gateway connections, DNS filtering, and more.
- User Segmentation: Check Point’s SASE platform provides granular policy-based permissioning that helps organizations exercise greater network access control.
- Secure Remote Access: Automatic Wi-Fi security lets remote workers connect to sensitive corporate network resources from the public internet without compromising security.
- IP Whitelisting: Allows network admins to explicitly define the IP addresses that are allowed to access the network, and grant access to trusted sources by assigning static IP addresses.
- Quality Assurance Testing: With 700 servers in various regions and 36 countries, your QA team can easily switch geo-location and check the quality of your product in your key international markets.
When you sign up with Check Point’s SASE, you get a full management platform where you can build, manage, and secure your network. Check Point offers flexible payment plans with billing occurring on a yearly or monthly basis. An online demo is available on request to enable you to test drive the solution before purchase.





