BadRabbit ransomware first appeared in October 2017, when it targeted a variety of organizations in Russia, Ukraine, and other Eastern European countries. It quickly spread to other regions, impacting industries ranging from media companies to critical infrastructure.
BadRabbit, also written as Bad Rabbit, was initially believed to be a variant of the Petya and NotPetya ransomware families. This was because it shares similarities in its attack methods and encryption mechanisms but operates independently with its own specific tactics.
BadRabbit ransomware is also known by other names, including “Ransom32” and “Diskcoder.D.” It is believed to be the work of a hacker group known as “Fancy Bear” or “APT28,” which is linked to the Russian government. This group has been involved in cyberattacks against various high-profile targets globally. BadRabbit’s primary attack vector was a drive-by download, typically delivered through compromised websites masquerading as legitimate news outlets or media sources.
Once activated, BadRabbit encrypted files on infected systems and demanded a ransom in Bitcoin to decrypt the data. The ransomware primarily targeted organizations in the media, telecommunications, and transportation sectors, causing significant disruption. However, unlike other high-profile ransomware attacks, BadRabbit’s ransom demands were relatively low: typically about $300 worth of Bitcoin per infected machine.
BadRabbit was relatively short-lived compared to other ransomware campaigns, with its activities tapering off by the end of 2017. The rapid decline in its prevalence was partly due to the quick discovery of its decryption key by security researchers, which allowed affected organizations to recover their data without paying the ransom. Despite its limited financial impact, BadRabbit’s emergence highlighted the continued evolution of ransomware and its use by state-sponsored cybercriminal groups for geopolitical purposes.
NotPetya and BadRabbit ransomware
2017 was a big year for ransomware. Before that year, almost no one outside of the small specialist field of cybersecurity had any idea what ransomware was. WannaCry changed all of that. It became an international sensation, generating headlines in all news media all over the world. Following hot on the heels of WannaCry came Petya, which battered the economy of Ukraine and hijacked its public services and banks.
Despite initial appearances, the Petya attack campaign in 2017 wasn’t implemented with the Petya ransomware, abandoned by its creator. This ransomware attack that was very clearly aimed at Ukraine wasn’t even able to collect on the ransom demand it displayed on victims’ computers. It was fake ransomware, and analysts realized that it wasn’t Petya. Instead, it was a new ransomware system that was based on the code of Petya. It was renamed NotPetya.
The first attack from NotPetya occurred in June 2017. When the first BadRabbit attack rolled out in October 2017, researchers again identified similarities between NotPetya and BadRabbit. Furthermore, they decided that the system could well be a variant of NotPetya. About 67 percent of the BadRabbit ransomware code was that of NotPetya.
The main similarity between WannaCry and NotPetya was that they encrypted the Master File Table, which renders access to all files impossible without actually needing to encrypt any files individually. BadRabbit does that too. Also, in a direct copy of NotPetya, BadRabbit overwrites the Master Boot Record to make it impossible to reboot the system and get in through Safe Mode.
NotPetya and BadRabbit both focused their attacks on Ukraine. The ransom demanded by both was a similar amount – $300 in Bitcoin. While both did attack systems in Russia and other countries, the number of attacks on Ukraine was significant. All three of these 2017 ransomware attacks focused their attacks on Windows systems.
Differences between BadRabbit and NotPetya
There are a few critical differences between WannaCry and NotPetya in one camp and BadRabbit in another. Both WannaCry and NotPetya used the EternalBlue exploit to move around Windows-based networks – BadRabbit does not have that feature. BadRabbit was distributed through a fake Adobe Flash update, while WannaCry and NotPetya spread through infected email attachments.
The ransom demand for NotPetya told victims to contact an email address for instructions – an address that was not active, which raised suspicions among security analysts that NotPetya was only disguised as ransomware but had a different motivation. That purpose was later revealed to be military.
BadRabbit is an actual ransomware attack; its controllers did intend to collect money. Another distinctive feature of BadRabbit is that it puts pressure on victims with a payment deadline. After a stated period, the ransom increases.
BadRabbit doesn’t use the EternalBlue exploit to move around a network because that exploit had been closed down by a Windows update. EternalBlue used a security weakness in Server Message Block (SMB) processes within the Windows operating system. Without that conduit to use, the developers of BadRabbit used EternalRomance. This different hack used Windows Management Instrumentation Command-Line (WMIC), in conjunction with the intended use of SMB to move to other computers across a network.
How does a BadRabbit attack start?
The hackers behind BadRabbit injected extra code into legitimate websites – usually news sites. The injection was JavaScript code inserted into the HTML of the website or one of its .js files. The extra program produced a popup that falsely declared it had detected a problem with the visitor’s version of the Flash Media Player and then took them to a downloader for the latest version of the utility. That download was the installer for the BadRabbit ransomware.
What happens in a BadRabbit ransomware attack?
The encryption process of BadRabbit has two parts. One method encrypts each file individually. This is performed with AES encryption with a 128-bit key and an RSA cipher with a 2056-bit key. All files are encrypted with the same key.
The RSA system is an asymmetric cipher – the key needed to decrypt a text is different from the key used to encrypt it. You cannot derive the decryption key from the encryption key. Thus, it is safe to reveal the encryption key, which is known as the public key. The encryption key for BadRabbit file encryption is hard-coded into the program.
The encryptor generates a unique ID for the attack.
The other part of the BadRabbit ransomware attack encrypts the drive’s Master File Table with an off-the-shelf utility called DiskCryptor. This part uses AES encryption with a 256-bit key. The DiskCryptor service also installs a modified Master Boot Record, which blocks the computer on startup.
Both AES keys and the unique ID for the attack get sent to the command and control server for BadRabbit, protected by encryption provided by the RSA cipher.
The replication routine of BadRabbit ransomware
The second branch of BadRabbit spreads the virus around the network to which the infected computer is connected. This uses the Mimikatz tool to identify other hosts on the network. It then tries a series of commonly-used administrator user account names and passwords in combination to guess valid credentials.
If one of the guessed accounts exists, the replication module opens a connection to that host copies its program bundle over. The replication module also tries the EternalRomance exploit to connect to other computers and storage devices.
The BadRabbit ransom process
BadRabbit Ransomware delivers its ransom note in two ways. The first is a text file, called Readme.txt, that is saved on the encrypted drive.
This step seems to be a waste of time because the user cannot access that drive anymore. BadRabbit then reboots the computer, which restarts to the MBR that was deposited through DiskCryptor.
The message reads:
Oops! Your files have been encrypted.
If you see this text, your files are no longer accessible.
You might have been looking for a way to recover your files.
Don’t waste your time. No one will be able to recover them without our
decryption service.
We guarantee that you can recover all your files safely. All you
need to do is submit the payment and get the decryption password.
Visit our web service at caforssztxqzf2nm.onion
Your personal installation key#1: –
If you have already got the password, please enter it below.
Password#1:
The complete block on access to the computer that the boot message causes is unfortunate because it renders the computer unusable. Other ransomware creators leave the computer in a useable state because that makes it easier for the victim to arrange the payment of the ransom.
To get to the website, the user needs to download and install a Tor browser. On arriving at the website, the user sees the following screen:
The text on the screen reads:
If you access this page, your computer has been encrypted. Enter the appeared personal key in the field below. If you succeed, you’ll be provided with a bitcoin account to transfer payment. The current price is on the right.
Once we receive your payment, you’ll get a password to decrypt your data. To verify your payment and check the given passwords enter your assigned bitcoin address or your key.
Price for decryption 0.05 BTC
The Web page shows a counter with hours, minutes, and seconds. This started at 40 hours. As the site message explained, the ransom demand would increase once the counter gets down to zero.
At the time of the attacks, 0.05 Bitcoin was worth around $300.
There is a field at the bottom of the Web page into which the victim can paste that password shown in the bootup screen on the computer. When the user presses the big button next to that field, an extra part of the Web page is revealed.
This gives a unique wallet ID, into which the victim can pay the ransom. Once the payment has been made, the password for decryption appears on the screen. Entering this into the Boot Message prompt, the user gets the computer back together with all files unencrypted.
Who was behind BadRabbit?
The analysts of cybersecurity businesses and those of national security agencies around the world eventually decided that the BadRabbit ransomware was creating the Russian hacker group, BlackEnergy. This is a group that the GRU, Russian military intelligence, frequently commissions. NotPetya was created by another Russian hacker group that was associated with the GRU, called Sandworm.
How to protect against BadRabbit ransomware
The server that hosted the fake Adobe Flash download went offline shortly after the BadRabbit campaign began, effectively shutting down the attack. It seems that the ransomware had served its purpose, which, like NotPetya, was not to gather a fortune.
Although BadRabbit is no longer a threat, the GRU still has its panel of hackers to hand. It has already shown that it is willing to commission new ransomware threats periodically, often reusing code. So, there will be other ransomware attacks like BadRabbit.
In all cases to date, ransomware gets into a system either through downloads initialized by the user or infected email attachments that the user opens. So, your main line of defense against attacks like the BadRabbit ransomware lies with user education. You also need to install effective endpoint protection systems that can defend against ransomware.
If you are obliged to follow a data privacy standard to stay in business, our duties include the need to keep data available for appropriate use and for information requests from the individuals to which that data pertains. Therefore, you need to ensure that data is not destroyed as well as blocking data theft.
Here are two secure systems that you should consider installing.
1. CrowdStrike Falcon Insight
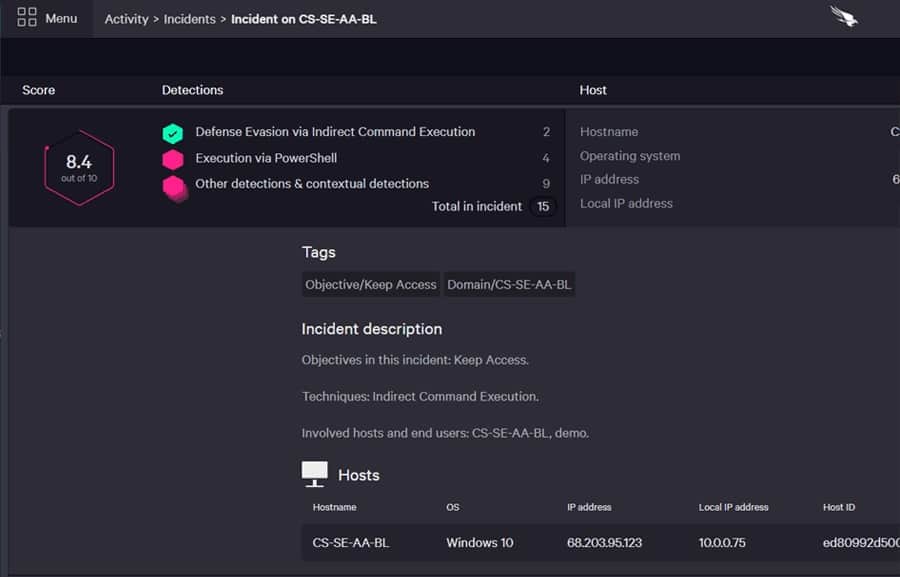
CrowdStrike Falcon Insight includes endpoint agents installed on every device and a cloud-based enterprise-wide coordinator. The device-resident part of the package is also available as a standalone product, called CrowdStrike Falcon Prevent. This is an endpoint detection and response (EDR) service.
Key Features:
- Dual-level protection
- On-device antivirus
- Cloud-based threat hunting
- Private threat intelligence
- Automated responses
Why do we recommend it?
CrowdStrike Falcon Insight protects endpoints from invasion by ransomware by scanning for malware when it arrives on a computer. The AV uses a combination of AI and Indicators of Compromise. A ransomware attack follows a sequence of events and those telltale actions will get the malware suite shut down by the Falcon system.
While the endpoint agents provide protection even when that endpoint is offline, the central system collates activity reports uploaded by Falcon Prevent and receives a threat intelligence feed that is collated from the experiences of other CrowdStrike customers.
The Falcon system is ideal for blocking new ransomware because it doesn’t rely on a blacklist to spot malware. Instead, it identifies anomalous activity. The service will implement automated responses that kill processes, isolate endpoints from the network and block suspicious user accounts.
Who is it recommended for?
This package is suitable for mid-sized and large businesses. The endpoint unit, which is called Prevent is a little too expensive for small businesses. The Insight version adds on a central, cloud-based system that gathers reports from Prevent and performs SIEM-like threat hunting. Insight spreads this intelligence to all endpoints and sends response instructions to the attacked computer.
Pros:
- Easy to expand by installing Prevent on a new computer
- Company-wide data gathering
- A central, cloud-based SIEM
- Warnings to all endpoints to shut down lateral movements
- Independent endpoint protection that continues when the device is offline
Cons:
- Too pricey for small businesses
You can get a 15-day free trial of Falcon Prevent.
2. ManageEngine DataSecurity Plus
ManageEngine DataSecurity Plus is a protection service for sensitive data and data files hosted on Windows. It monitors files and blocks unauthorized changes, which is ideal for protecting against ransomware. This package is essential for businesses following PCI DSS, HIPAA, and GDPR.
Key Features:
- Discovers sensitive data
- Categorizes data
- Protects files
- Quarantining
Why do we recommend it?
ManageEngine DataSecurity Plus takes a different approach to that implemented by CrowdStrike Falcon because it doesn’t examine the programs that are installed on the computer. So it doesn’t act as an antivirus; instead, it protects data. So, user actions and actual data movements are more important subjects of tracking.
DataSecurity Plus includes a data discovery service and a sensitive data classifier. It watches over those data stores with a file integrity monitor. Unauthorized changes to files raise alerts and trigger automated responses. Those responses can include reloading damaged files from backup and killing running processes.
Who is it recommended for?
This strategy is a last line of defense and it might worry some companies that the security system doesn’t look for ransomware or other malware. You should certainly use this system as a supplement to a firewall and an AV because there are a number of malware types, such as keyloggers, that don’t touch data but you still don’t want it.
Pros:
- Adapts to GDPR, PCI DSS, FISMA, and HIPAA
- Provides compliance auditing and reporting
- Data loss prevention
- USB device controls
Cons:
- No SaaS version
This software package installs on Windows Server. DataSecurity Plus is available for a 30-day free trial.









