IPTables is a powerful firewall tool used to manage network traffic on Linux-based systems, including Ubuntu. As one of the most widely used tools for network security, IPTables allows system administrators to define rules that control incoming and outgoing traffic based on IP addresses, ports, protocols, and other criteria. Whether you’re securing a server, setting up a secure local network, or protecting your system from external threats, IPTables provides fine-grained control over what network traffic is allowed or blocked.
In this guide, we will explore how IPTables works on Ubuntu, one of the most popular Linux distributions. You’ll learn how to configure basic firewall rules, customize your firewall setup to meet specific security requirements, and troubleshoot common issues. IPTables works by filtering packets at the network layer, offering strong protection against unauthorized access while allowing legitimate traffic to pass through seamlessly. By using IPTables, you can limit access to services, protect sensitive data, and prevent network-based attacks such as DoS (Denial of Service) or unauthorized intrusion attempts.
This guide will cover everything from setting up your first firewall rules to advanced configurations, ensuring your Ubuntu system is properly secured. By the end of this guide, you’ll have the knowledge to configure IPTables effectively, helping you to safeguard your network and control traffic flow on your Ubuntu system. Whether you’re a beginner or experienced Linux user, understanding IPTables is essential for maintaining a secure and well-managed network.
Get Set Up for IPTables
If you’re new to IPTables then one of the first things you need to do is update it or install it is using the following command:
$ sudo apt-get install iptables
While users who are new to command line interfaces find there is a learning curve attached to IPTables, the utility itself is simple enough to use. There are a range of core commands that act as your bread and butter for controlling traffic. That being said, you need to be very careful when making changes to IPTables rules. Entering the wrong command can lock you out of IPTables altogether until you address the problem within the physical machine.
Before we get to the heart of IPTables you need to make sure that you have a VPA running Ubuntu 16.04 and a local machine with an SSH client. If you already have these then it is time to begin.
IPTables Tutorial: Chains
One of the fundamental concepts to come to grips with in IPTables is that of chains. A chain is essentially a rule. The filter’s tables have three chains you’ll encounter on IPTables; INPUT, FORWARD and OUTPUT.
- INPUT – The INPUT chain is the rule that controls incoming packets. Here you can block or allow new connections. You can do this based on port, protocol, and source IP address.
- FORWARD – The FORWARD chain filters incoming packets that are being forwarded to a different end location. You’re unlikely to use this chain unless you’re routing or looking for forwarding specifically.
- OUTPUT – The OUTPUT chain is used to manage outgoing packets and connections. It is important to note that if you ping an external host then the input chain will be used to return the data back to you.
Default Chain Behaviour
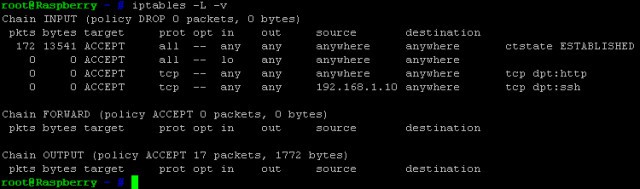
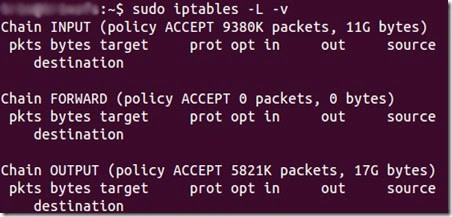
You may want to jump straight into configuring particular rules when starting out but you need to take a step back to define the default behavior first. To identify what the default behavior of your chains is, you’ll need to run the command:
$ sudo iptables -L command
This will show the following:
user@ubuntu:~$ sudo iptables -L -v Chain INPUT (policy ACCEPT) Chain FORWARD (policy ACCEPT) Chain OUTPUT (policy ACCEPT) user@ubuntu:~$
This information tells you exactly what your chains are configured to do. In the example, the input, forward and output chains have been configured to accept traffic. These settings are a good starting point as they don’t block any connections that you might want.
However, if you’re find that your policies aren’t accepting connections then you can enter each of the following commands to accept all connections:
$ sudo iptables —policy INPUT ACCEPT
$ sudo iptables —policy OUTPUT ACCEPT
$ sudo iptables —policy FORWARD ACCEPT
Once your defaults are aligned to accept all connections, you can control access to IPTables by blocking IP addresses and port numbers. This allows you to specify which connections you want to block rather than blocking everything by default.
If you’re working with particularly sensitive information then you can configure your defaults to automatically block all connections. This way you can use IPTables to pick individual IP addresses that you want to allow. To do this you need to input the following command:
$ sudo iptables —policy INPUT DROP
$ sudo iptables —policy OUTPUT DROP
$ sudo iptables —policy FORWARD DROP
The majority of users will be better off accepting all connections but it is worth remembering if you’re working on a high security server.
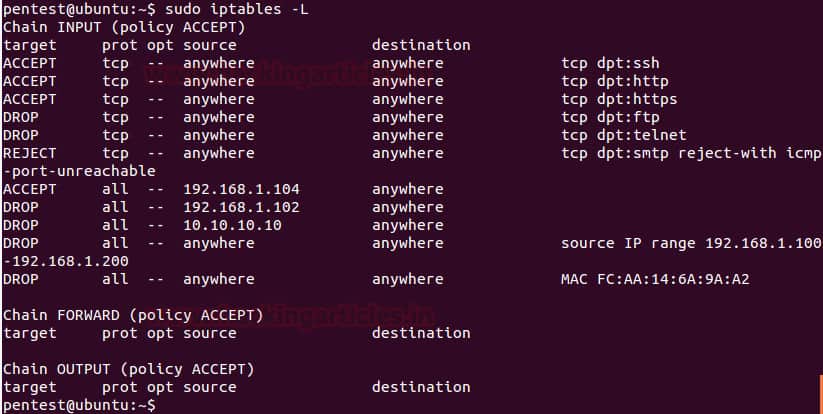
Configuring Individual Connections
Once you’ve configured your default chain behaviour it’s time to configure individual connections. This is the point where you configure what is referred to as a connection-specific response. This essentially tells IPTables how to interact when connected to an IP address or port. These responses are as follows; ACCEPT, DROP, REJECT.
As you can see in the image above, the user has defined chain rules to allow, drop, or reject the connection based on the requirements. Below is a description of what each response entails:
- ACCEPT – This configuration simply allows the connection to take place.
- DROP – Drop blocks the connection without interacting with the source in any way.
- REJECT – This blocks the attempted connection but also sends an error message. This is generally to notify the source that the connection attempt has been blocked by your firewall.
How to Allow or Block Connections
There are many different ways to block or allow connections depending on your settings. The examples below are using the covert blocking method of using Drop to drop connections without any interaction. iptables -A allows us to add additional caveats to the rules established by our default chain settings. You see how to use this command to block connections below:
Blocking a single IP address:
$ sudo iptables -A INPUT -S 10.10.10.10 -j DROP
In the example above you would replace 10.10.10.10 with the IP address you want to block.
Blocking a range of IP addresses:
$ sudo iptables -A INPUT -s 10.10.10.10.0/24 -j DROP
or
$ sudo iptables -A INPUT -s 10.10.10.0/255.255.255/.0 -j DROP
Blocking a single port:
$ sudo iptables -A INPUT -p tcp —dport ssh -s 10.10.10.10 -j DROP
Note that the ‘ssh can be replaced by any protocol or port number. It is also important to note that the -p tcp segment of the code is used to refer to whether the protocol you want to block is using UDP or TCP.
If the protocol is using UDP then you would enter -p udp instead of -p tcp. You can also block all connections from IP addresses by entering the following command:
$ sudo iptables -A INPUT -p tcp —dport ssh -jDROP
Two-Way Communication: Connection States IPTables Tutorial
Most of the protocols you encounter require communication to go both ways in order for a transfer to take place. This means that transfers are made up of an input and an output. What goes into your system is as important as what comes out. Connection states allow you to mix and match between two-way connections and one-way connections. In the example below, the SSH protocol has blocked SSH connections from the IP address but permits ones to the IP address:
$ sudo iptables -A INPUT -p tcp —dport ssh -s 10.10.10.10 -m state —state NEW, ESTABLISHED -j ACCEPT $ sudo iptables -A OUTPUT -p tcp —sport 22 -d 10.10.10.10. -m state —state ESTABLISHED -J ACCEPT
Once you’ve entered a command to change connection states you need to save your changes. If you don’t then when you close the utility your configuration will be lost. Depending on the distribution system you’re using, there are a number of different commands you can use:
Ubuntu:
$ sudo /sbin/iptables-save
Red Hat / CentOS –
$ sudo /sbin/service iptables save
OR
$ sudo /etc/init.d/iptables save
Remembering to use these commands is vital because it will eliminate the hassle of having to configure each time you load up the utility.
Deleting a Rule
Just as important as being able to save your rules is being able to delete them. If you make a mistake or simply want to eliminate an old rule then you can use the option –D command. This command needs to be combined with the number of the rule that you enter. The number tells IPTables which rule is to be deleted. For example, if you were to enter:
$ sudo iptables -D INPUT 10
Then the 10th rule you configured would be deleted.
If you want to clean house and remove a range of rules then you can use the -F command. You can do this by entering the following:
$ sudo iptables -F
This will clear the entire set of rules and flush your IPTable.
IPTables: Learn Chain Rules!
That concludes our IPTables tutorial. As you can see IPTables is a versatile tool for blocking and allowing traffic on Linux distributions. Using the utility effectively involves setting up your default configurations effectively and building additional rules on top of that. The default configurations will allow you to outline your broad traffic intentions to allow or deny traffic; the rules will allow you to structure your approach with regards to IP addresses, ports and protocols.
We’ve only scratched the surface with IPTables potential, and there are a ton of different commands that you can use to decide how you experience the traffic on your server. However, we recommend that you get the basics down before you start off with other commands. For example, you’ll want to get your head around basic chains rules before committing to anything more specialized.
Once you’ve become accustomed to how IPTables works then you can start incorporating even more rules to customize your experience. In doing so you’ll be able to specify exactly what kind of connections you will allow with much greater precision than ever before.
IPTables FAQs
What are IPTables used for?
IP tables is a singular rather than a plural. It should be written IPtables and it is a firewall system available for Linux computers. In order to make it compatible with all distros of Linux, this is a command line tool, which makes it harder to use than the popular firewall built into Windows, which is called Windows Defender. The firewall gets its name from its storage of rules, which are called chains – they are held in tables. You can use chains to filter/block traffic when they are traveling in or out of a Linux computer’s network interface.
How do I list an IPTable?
IPtables can be accessed at the command line of Linux. You should issue the command:
sudo iptables -L to get a list of all rules. The output for this command is provided in three sections. The first of these is INPUT, which relates to incoming traffic. You will see that the actions in this section are ACCEPT, DROP, and REJECT. The next section is FORWARD and the last section lists OUTPUT rules, which act on outgoing traffic.
What are IPTables and IP chains?
The packet filtering rules held in IPtables are called chains. The firewall will implement the rules in order, so you can move a line up or down the chain by altering its line number. You need to list the most specific rules first, so the top rules would deal with specific IP addresses, lower down, you would enter rules that relate to ranges of addresses, and below that rules that act on all addresses but filter on some other aspect, such as protocol. If you have ever had to set up ACLs on a router, you will understand the operating methods of IPtables chains because they are very similar.