Defending your network infrastructure against cyber attacks is not an easy task. The attacker has an advantage over the defender. An attacker can attack from anywhere at any time. A defender would have to defend everywhere all the time, and this can be challenging.
Vulnerability assessments, penetration testing, and red and blue teaming, among others have long been the tools of choice for the defender. But they suffer from two key disadvantages: They are not dynamic and resource-efficient. New vulnerabilities and attacks that exploit those vulnerabilities can arise at any time, meaning they may go undetected until the next scheduled vulnerability assessment or penetration testing service is conducted. So how do you ensure vulnerabilities and attacks are discovered as they arise?
Here is our list of the best breach and attack simulation (BAS) tools:
- SafeBreach EDITOR’S CHOICE This a cloud-based system that provides an attack scenario library that is gathered from the experience of other companies during real-world hacker intrusions and software-based attack campaigns.
- Picus Security This cloud SaaS package provides a library of attack scenarios and an environment to launch them.
- Cymulate A SaaS package that includes a test environment to launch attacks on a range of IT assets, including firewalls and email systems.
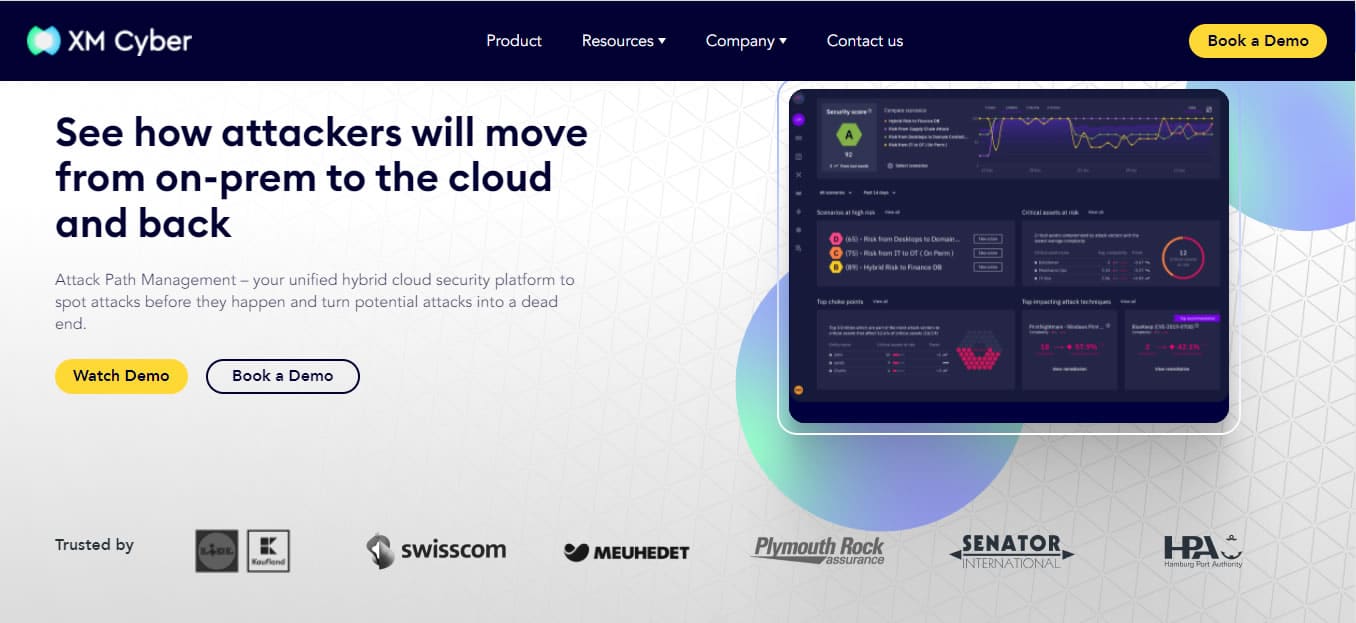
- XM Cyber An Attack Path Management platform on the cloud that probes the security of on-premises systems and cloud services.
AttackIQ An automated security tester that launches attacks against your system for research purposes. - CyCognito This SaaS package explores a system, documents it, identifies possible weaknesses, and tests them with attacks.
Automation and AI technology hold the key. AI technology has the potential to upend the longstanding advantage that attackers have over defenders. Automation and AI will allow computers to take over key security tasks from humans, and then do them faster and at scale. This is where Breach and Attack Simulation (BAS) technology comes into play. Gartner defines BAS technologies as tools “that allow enterprises to continually and consistently simulate the full attack cycle (including insider threats, lateral movement, and data exfiltration) against enterprise infrastructure, using software agents, virtual machines, and other means”.
BAS tools help make security testing and defense mechanisms more consistent and automated by providing continuous testing while alerting stakeholders about existing gaps in the security posture. A breach simulation can simulate malware attacks on endpoints and covert data exfiltration in your network. In this article, we’re going to review the leading BAS tools in the market. Hopefully, this will guide you in the process of choosing the right one for your business.
The Best Breach and Attack Simulation (BAS) Tools
Our methodology for selecting a breach and attack simulation tool
We reviewed the market for BAS systems and tested tools based on the following criteria:
- A method to connect to an existing system to launch external attacks
- An option to conduct internal attacks
- Scenarios of typical attack playbooks
- Comprehensive attack analysis
- Solution for security improvements to block simulated attacks
- A system that provides extensive test activity reports for compliance reporting
- A good service that is worth paying for and is offered at an accessible price
1. SafeBreach
SafeBreach is one of the pioneers in the breach and attack simulation solution. The company’s BAS platform enables organizations to see their overall security posture from an attacker’s perspective and to proactively predict attacks, validate security controls, and improve response efforts. SafeBreach BAS platform can simulate various breach methods used by attackers continuously, and identify breach scenarios across the network infrastructure. SafeBreach prides itself on having the largest attack playbook in the industry—24,000 attacks and counting.
Key Features:
- Automated Attack Simulations: Simulates real-world cyberattacks across the entire cyber kill chain, allowing you to see how your defenses would respond to various threats.
- Extensive Attack Library: Offers a vast library of pre-built attack scenarios based on MITRE ATT&CK framework and includes simulations of zero-day exploits and emerging threats.
- Customization Options: Allows you to customize attack simulations to match your specific IT environment, security posture, and industry threats.
- Real-Time Threat Detection and Analysis: Provides real-time visibility into ongoing attack simulations, helping security teams identify and respond to potential breaches quickly.
- Detailed Reporting and Analytics: Delivers comprehensive reports with insights into vulnerabilities identified, attack paths taken, and overall security effectiveness.
- Integration with Security Tools: Integrates with various security information and event management (SIEM) and security orchestration, automation, and response (SOAR) tools for a more holistic security posture.
Why do we recommend it?
SafeBreach is a very comprehensive platform for attack testing. It provides a library of attack playbooks to find strategies that match your site’s sensitivities. You can look for previous attacks that targeted businesses like yours or data similar to yours. The resolution recommendations will help you tighten your security.
The platform can be integrated with several third-party security tools such as SIEM, SOAR, workflow, and vulnerability management tools. Common use cases include threat assessment, security control validation, cloud security assessment, and risk-based vulnerability management. The platform is ideal for enterprises in any vertical or for service providers, MSPs, and technology vendors that want to offer BAS capabilities to their customers.
SafeBreach helps organizations manage their security posture using the following four-step approach:
- Attack The platform enables you to search and execute preconfigured attack scenarios to replicate common threats.
- Analyze Access powerful insight into the status of your organization’s security posture by aggregating and visualizing attack path and security-control performance data. Leverage the MITRE ATT&CK framework to understand overall organizational risk exposure.
- Remediate The SafeBreach platform provides actionable insights to identify security gaps and prioritize remediation efforts based on their level of risk.
- Report The availability of customizable dashboards and personalized reports makes it easier to communicate existing gaps and remediation priorities to the understanding of key stakeholders.
SafeBreach offers a partner program for vendors and service providers that want to incorporate BAS technology into their capabilities. Product pricing and licensing details are not available on their website, but you can contact them directly for a price quote. A free personalized online demo is available on request.
Who is it recommended for?
This is a high-end service and the company doesn’t publish its prices, so it is probably going to be beyond the budgets of small businesses. SafeBreach’s client list includes PayPal, NetFlix, Experian, Pepsi, and Deloittes, so companies that sign up for the package will be in good company.
Pros:
- Reduced Risk of Breaches: Proactive identification and remediation of vulnerabilities can significantly reduce the risk of successful cyberattacks.
- Enhanced Security Awareness: Simulations can raise awareness among security teams and business stakeholders about potential cyber threats.
- Scalability and Automation: The cloud-based platform offers scalability and automates attack simulations, saving time and resources.
- Tailored Threat Playbook: Users can customize their threat playbooks based on current attack strategies from threat intelligence feeds, ensuring that testing remains relevant and up-to-date.
- Guides for Blocking Attacks: The platform provides guidance on how to block successful attack tests, helping improve the organization’s security posture.
Cons:
- Complexity: Setting up and managing complex attack simulations might require specialized security expertise.
EDITOR'S CHOICE
SafeBreach is our top pick for a breach and attack simulation tool because it provides a library of real-world attacks and enables you to run them on your own system to test whether your security measures are adequate. You can also sign up to third-party threat intelligence feeds and channel their information into the breach and attack simulator. You also have the option to create your own scenarios to test your latest security improvements.
OS: Cloud-based, compatible with Azure, AWS, and Google Cloud Platform
2. Picus Security
Picus Security is an award-winning security control validation platform and one of the leading pioneers of BAS technology that helps companies improve their cyber resilience. Picus evaluates your security controls using thousands of preconfigured attack scenarios and shows you exactly where gaps exist and how to mitigate them.
Key Features:
- Scenario Library and Customization: Provides a library of pre-built attack scenarios and the ability to customize them to match your specific IT environment and threat landscape.
- Continuous Security Validation: Offers ongoing attack simulations to continuously assess your security posture and identify potential weaknesses.
- Risk-Based Vulnerability Management: Prioritizes vulnerabilities based on the likelihood of exploit and potential impact, aiding in efficient remediation efforts.
- A Pentesting Tool: The platform includes pentesting capabilities, enabling users to conduct penetration tests to assess the security posture of their systems.
- Attack Surface Validation: Picus Security validates the attack surface, helping organizations understand potential entry points and weaknesses in their security defenses.
Why do we recommend it?
Picus Security is a strong rival to the SafeBreach platform. It offers a library of typical attacks but these are not extracted from real-world attacks like the Safebreach system. The Picus Security system includes playlists for all of the typical attacks that any business is likely to face, so it is more like a penetration testing tool.
Picus Security’s key product offerings include:
- Picus Threat Library A broad repository of threat and attack techniques such as malware, vulnerability exploit, web application attack samples, and nation-state attack scenarios designed to enable your security team to keep up with the changes in the adversarial context. Picus Threat Library content is mapped to the frameworks of MITRE ATT&CK, cyber kill chain, OWASP, and Common Vulnerabilities and Exposures (CVE), among others, to ensure the threat library is up-to-date at all times.
- Picus Threat Emulation Module Picus Threat Emulation Module checks networks, web applications, endpoints, and email security controls for their readiness level for red team practices. It also serves as a bridge between your defensive capabilities and the adversarial scenarios in Picus Threat Library and links the identified gaps with the Picus Mitigation Library to speed up remediation efforts.
- Picus Mitigation Library Picus Mitigation Library provides the security teams with the right mitigation technique and industry insights and best practices. This enables security teams to know when and how to step in to mitigate security risks and data breaches.
- Picus Detection Analytics This module automatically queries SIEM, EDR, and other security logs to find differences in the available and expected events. It utilizes the extensive adversarial context from the Picus Threat Library to provide minimal to zero false positives.
Who is it recommended for?
This is a very comprehensive attack testing system that has attracted some premium companies to its client list. These include ING Bank, Turkish Airlines, Trend Micro, and Mastercard. There is no single industry sector that would need this tool more than any other – it has broad appeal across all sectors but is geared towards servicing large multinationals.
Pros:
- Reduced Risk of Breaches: Proactive identification and mitigation of security weaknesses can significantly decrease the risk of successful cyberattacks.
- Ease of Use: Compared to some BAS tools, Picus Security is known for its user-friendly interface and streamlined approach to attack simulations.
- Cost-Effectiveness: Picus Security might be a more cost-effective option compared to some BAS solutions, especially for smaller organizations.
- Cloud Security: Supports testing and validation for cloud environments, helping organizations secure their cloud resources.
- Vulnerability Scanning: The platform includes vulnerability scanning capabilities, identifying weaknesses in both on-premises systems and cloud resources.
Cons:
- No Price List: Picus Security does not provide a publicly available price list, making it challenging for organizations to assess cost considerations upfront.
The combined on-demand use of these products—Picus Threat Library, Picus Threat Emulation Module, Picus Mitigation Library, and Picus Detection Analytics delivers a complete cyber kill chain service that ranges from threat development to validation and mitigation. A free online demo is available on request.
3. Cymulate
Cymulate is a SaaS-based platform that provides breach and attack simulation, continuous automated red and purple teaming service, and validation services for email gateway, web gateway, web application firewall, endpoint security, and data exfiltration (DLP), and Advanced Persistent Threat (APT) attacks. Cymulate empowers organizations to proactively protect their business-critical assets by making it easier to simulate real attacks and optimize security posture.
Key Features:
- Multi-Vector Attack Simulations: Simulates attacks across various vectors, including network, endpoint, cloud, and email, providing a comprehensive assessment of your security posture.
- Continuous Attack Validation: Enables ongoing attack simulations to continuously test your defenses and identify potential security weaknesses.
- System Hardening: Provides tools and recommendations for system hardening, helping organizations strengthen their security posture by addressing identified vulnerabilities and implementing best practices.
- Recovery Plan Testing: The platform allows for testing recovery plans, ensuring that organizations can effectively respond to and recover from security incidents and breaches.
- Kill-Chain Scenarios: Cymulate simulates kill-chain scenarios, enabling organizations to understand and mitigate the various stages of an attack from initial compromise to data exfiltration.
Why do we recommend it?
Cymulate is another SaaS package that is delivered from the cloud and has a Breach and Attack Surface testing module. This system can be used to test existing security measures or to give recovery procedures a dry run. The tool provides standard attack vectors and also allows the creation of custom scenarios.
With just a few clicks, Cymulate can initiate thousands of machine-based attack simulations on your network to test your security controls and identify vulnerabilities, and shows you exactly where you’re exposed including guidance on how to fix it.
Key features and capabilities include:
- The ability to test both perimeter and internal security controls, and all phases of an attack, from pre-exploitation to post-exploitation.
- The ability to test continuously, periodically, and on-demand without interfering with business operations.
- The ability to update continuously to deliver simulations that mirror common modern attack scenarios including those found in the wild, dark web, and sophisticated nation-state attacks.
- The ability to provide comprehensive reports and recommendations for remediation and how to prioritize them based on exploitable vulnerabilities.
With Cymulate, organizations can better manage their security posture using the following three-step approach:
- Simulate Attacks Enables you to launch attacks across the entire MITRE ATT&CK framework with the flexibility to run end-to-end red team campaigns or specific attack techniques with a wide range of attack scenarios.
- Know Your Security Gaps This step allows you to gain visibility into your current security exposure, exploitable vulnerabilities, and other security gaps after carrying out the simulated attacks. It measures and tracks your security performance with a risk score based on proven methodologies, including NIST, CVSS V3, and Microsoft DREAD.
- Remediate with Actionable Insights This step allows you to optimize your security posture with clear, prescriptive guidance. The insights obtained to enable you to prioritize resources and budget based on your risk exposure level.
Who is it recommended for?
This system is another Breach and Attack Simulation platform that doesn’t publish its price list. This is a factor that is going to deter small businesses from enquiring about the product. However, Cymulate does offer a free trial of the entire platform, so that provides an entry point for any business that needs a BAS service.
Pros:
- Streamlined Reporting and Analytics: Automated reports provide valuable insights into security weaknesses and overall security posture.
- Vulnerability Tests: Cymulate offers vulnerability tests tailored to commonly encountered attack scenarios, ensuring that organizations are prepared to defend against real-world threats.
- Actionable Remediation Guides: The platform provides actionable guides on how to remediate discovered weaknesses, helping organizations quickly and effectively address vulnerabilities.
- Exposure Analytics: Cymulate includes exposure analytics, offering insights into the organization’s security posture and identifying areas of high risk that need attention.
Cons:
- Implementation Time: Depending on the complexity of your IT environment, implementing and configuring Cymulate might take some time.
Cymulate BAS service can be easily deployed via the AWS marketplace. A private demo and a 14-day free trial are available on request.
4. XM Cyber
XM Cyber is a leading hybrid cloud security company that provides an award-winning Attack Path Management platform that lets organizations continuously visualize their on-prem and cloud networks from the perspective of an attacker to spot attacks before they happen. This is achieved via continuous simulated attacks. These simulations then expose real-life security gaps stemming from identified vulnerabilities, human errors, and misconfigurations.
Key Features:
- Risk Assessment: XM Cyber conducts comprehensive risk assessments to identify vulnerabilities and potential attack paths within an organization’s network.
- Attack Path Management: Maps potential attack paths based on real-world adversary tactics, techniques, and procedures (TTPs) to understand how attackers might exploit vulnerabilities in your environment.
- Exposure Management: Identifies exposed assets and prioritizes vulnerabilities based on their potential impact on critical business functions.
- Simulated Breach Scenarios: Simulates potential breach scenarios based on identified attack paths, allowing you to see the potential consequences of a successful attack.
- Proxy Spoofing: XM Cyber includes proxy spoofing capabilities, allowing it to simulate advanced attack techniques and test the network’s defenses against sophisticated threats.
Why do we recommend it?
XM Cyber is a security platform that protects and tests both on-premises systems and cloud services. This package runs continuously, so once you have ironed out all of your security weaknesses, any new services you add will be immediately assessed. This is a cloud-based SaaS package.
The platform identifies an organization’s most critical assets, analyzes every potential attack path, and offers remediation options based on your risk level and its associated impact. XM Cyber helps organizations manage their security posture using the following four-step approach:
- Contextualize This step uncovers hidden connections between misconfigurations, vulnerabilities, and overly permissive identities that compromise critical assets. It also detects lateral movement opportunities and gives you a true visualization of an attacker’s approach with graph-based modeling.
- Prioritize Enables you to run simulated scenarios 24/7 against the newest threats aligned with MITRE ATT&CK techniques. This allows your team to discover, understand, prioritize, and eliminate risk, and direct resources to resolve the most damaging attack paths with step-by-step remediation guidance.
- Resolve This step enables you to save analyst time by cutting off attack paths and eradicating key risks at the right point; allowing you to automatically feed guided remediation into your ticketing system.
- Improve This step supports continuous 24/7 monitoring of your hybrid network environments for new cyber risk exposures to improve your security posture. It also allows you to easily communicate to the board the impact of security investments with data that shows how your security posture is improving.
Who is it recommended for?
This package has strong cloud testing features while still providing network external attack surface probing. So, this is a good choice for companies that operate hybrid systems covering both on-premises and cloud resources. Once again, the company doesn’t publish a price list, so it won’t appeal to cost-sensitive small businesses.
Pros:
- Focus on Attack Paths: Moves beyond just identifying vulnerabilities and focuses on how attackers might exploit them, providing a more actionable perspective.
- Prioritization of Vulnerabilities: Helps prioritize vulnerabilities based on potential impact, allowing security teams to focus on the most critical issues first.
- Improved Security ROI: By focusing on exploitable vulnerabilities, XM Cyber can help organizations get more value out of their existing security investments.
- Continuous Testing: The platform offers continuous testing, enabling organizations to identify and address vulnerabilities in real-time and maintain a robust security posture.
- User-Friendly Interface: Known for its user-friendly interface and ease of use compared to some complex BAS tools.
Cons:
- Focus on Internal Network: XM Cyber might have a stronger focus on simulating attacks originating within the internal network compared to external attacker methods.
The XM Cyber comes with an intuitive dashboard that offers simplified navigation and flexible unlimited assessments of scenarios and configurations. XM Cyber does not publicly disclose its pricing on its website. Prospective customers will need to directly contact the vendor for a custom quote. A free online demo is available on request.
5. AttackIQ
The AttackIQ Security Optimization Platform is based on BAS technology. AttackIQ automatically tests security programs for gaps by emulating the attackers’ behavior and generates real-time performance data and mitigation strategies to improve your security posture. It is a SaaS agent-based solution that can be deployed on-premises or in the cloud.
Key Features:
- MITRE ATT&CK Framework Alignment: Attack simulations are mapped to the MITRE ATT&CK framework, ensuring they cover a wide range of attacker tactics, techniques, and procedures (TTPs).
- Multi-Stage Attack Simulations: Simulates complex, multi-stage attacks that mimic real-world attacker behavior, providing a more realistic assessment of your defenses.
- Endpoint Security Testing: Evaluates the effectiveness of your endpoint security controls against various attack techniques.
- Post-Exploitation Analysis: Analyzes how attackers might move laterally within your network after gaining initial access, offering insights into potential damage.
- Threat Intelligence Integration: Integrates with threat intelligence feeds to keep attack simulations up-to-date with the latest threats.
Why do we recommend it?
AttackIQ is a little simpler than the tools at the top of this list. It implements tests for the MITRE ATT&CK list rather than sampling real-world attacks. However, it has to be said that most hacker attacks in the world are variations on the MITRE ATT&CK list.
AttackIQ’s scenarios and assessment templates align to the MITRE ATT&CK framework and reflect up-to-date threat intelligence to help improve the defense capabilities from endpoint detection and response to next-generation firewalls to security segmentation capabilities to native internal security controls in cloud providers.
Other features and capabilities include:
- Tests the defense capabilities that matter most to you, from endpoint detection to next-generation firewalls, and other internal and external security controls.
- Generates granular information about control detection and prevention to improve effectiveness.
- Recreates and evokes adversary behaviors across the modern hybrid cloud infrastructure, and validates cloud platform native security controls to optimize cloud infrastructure investments.
- Employs the use of AI and machine-learning-based cyber defense technologies, and generates granular information about security control detection and prevention to improve effectiveness.
- Code-based compilations of adversary behavior and thousands of scenarios are built into the AttackIQ platform.
- Generates insightful reports about the details of a specific security assessment, and security control changes over a specified period.
Who is it recommended for?
This is another platform that doesn’t publish its price list. The package operates from the cloud, so it is strong at performing external attack surface testing. The platform has some very large multinationals on its client list, including GE, JetBlue, and SA Power Networks.
Pros:
- Threat-Informed Approach: Integration with threat intelligence ensures simulations reflect the latest attack trends.
- Automated Workflows: Automated reporting and remediation workflows can streamline security operations.
- Realistic Attack Simulations: MITRE ATT&CK® alignment and multi-stage attack simulations provide a realistic picture of your security vulnerabilities.
- Machine Learning Techniques: AttackIQ employs machine learning techniques to adjust and optimize tests based on the latest threat intelligence, ensuring that testing remains relevant and up-to-date.
Cons:
- No Price List: Similar to other advanced security platforms, AttackIQ does not provide a publicly available price list, which can make it challenging for organizations to determine the cost of implementing the platform.
AttackIQ does not provide pricing details on its website. Prospective customers would have to directly contact the vendor for a quote. A free on-demand demo and a personalized one-on-one demo are available on request.
6. CyCognito
CyCognito is a SaaS-based BAS platform that takes the attackers’ perspective in analyzing your network assets for vulnerabilities that will be most attractive to cybercriminals. It then identifies and prioritizes the critical points of exposure that attackers can most easily exploit and offers prescriptive remediation guidance. As with most SaaS applications, CyCognito requires no deployment, integration, or configuration.
Key Features:
- Attack Path Modeling: Identifies potential attack paths that attackers might exploit to gain access to your critical systems and data.
- Exploit Verification: Goes beyond identifying vulnerabilities and attempts to exploit them in a controlled environment to validate their severity.
- Business Risk Context: Prioritizes vulnerabilities based on their potential business impact, helping security teams focus on the most critical issues.
- Asset Discovery: Automatically discovers and maps all assets across the entire organizational infrastructure, including shadow IT, to provide a comprehensive view of the attack surface.
- Active Security Testing: CyCognito performs active security testing on discovered assets to identify vulnerabilities and misconfigurations that could be exploited by attackers.
Why do we recommend it?
CyCognito will scan not only all of your systems but all of your companies and divisions. This tool uses a range of external information sources to research a business before launching an attack. This enables it to choose different levels in the corporate structure to probe. This can unearth a less protected division that can provide an internal route into more sensitive assets.
CyCognito helps organizations manage their security posture using the following five-step approach:
- Graphs Business and Asset Relationships The CyCognito platform uses ML and a graph data model to reveal and relate all business relationships in your enterprise and cloud environments.
- Determines Business Context This step helps you determine business context to enable your organization to continuously understand which assets and what data belong to which departments or subsidiaries within your organization, the business processes associated with those assets, and what risks and attack paths the assets are exposed to.
- Tests Security at Scale CyCognito tests identifies and uncovers Common Vulnerabilities and Exposures (CVEs) and attack vectors that malicious actors could use to breach your most critical assets, including data exposures, misconfigurations, and even zero-day vulnerabilities.
- Prioritizes Risks This step identifies and prioritizes your organization’s most critical risks, making it easy for your security teams to know where to focus remediation efforts.
- Accelerates Remediation For every risk that’s identified, the CyCognito platform provides detailed and actionable remediation guidance and exploit intelligence so that your security teams can have a clear path forward.
Who is it recommended for?
This system is suitable for large organizations with many divisions. A parent company can get all of its assets covered by this multi-layered testing system. The platform performs continuous testing so it will examine any new system you add on as soon as it is live.
Pros:
- Unique Focus: CyCognito’s focus on external attack surface discovery provides valuable insights that traditional BAS tools might miss.
- Exploit Verification: Verifying vulnerabilities through exploit attempts provides a more accurate picture of your security posture.
- Reporting and Remediation: Offers detailed reports that highlight vulnerabilities and recommends remediation steps.
- Continuous Testing: The platform conducts continuous testing, ensuring that security assessments are always up-to-date and reflecting the current state of the organization’s attack surface.
Cons:
- Cost: CyCognito can be a costly solution, especially for smaller organizations.
- Limited Scope: Primarily focuses on external attack surface, potentially neglecting internal threats that some BAS tools can simulate.
CyCognito does not provide pricing details on its website but you can contact the vendor directly for a quote. However, you can sign up for a custom demo to see how the platform works.