Bot attacks are increasingly becoming a major threat to businesses across a wide range of industries. These automated programs, commonly known as bots, can be used to steal sensitive information, disrupt online services, inflate traffic metrics, and damage brand reputation.
As this type of automated threat continues to grow, organisations are placing greater emphasis on dedicated bot protection solutions. These platforms are built to identify and stop automated activity that attempts to mimic real users, helping to preserve application performance, protect data, and maintain trust in digital services.
Here is our list of the best bot protection software packages:
- MailWasher EDITOR’S CHOICE An on-premises email protection system that intercepts mail between the server and the client. Runs on Windows or Linux. Start a 30-day free trial.
- Cloudflare Bot Manager A bot blocker from a very large network that is often offered for free to new website owners through their hosting service.
- TitanHQ Email Security Available as a SaaS platform or as a network appliance and monitors outgoing email as well as the inbound mail.
- DataDome This cloud-based traffic assessment system offers pass or fail advice to your web server and also performs vulnerability scanning.
- Reblaze Bot Management A cloud-based proxy server that filters requests with speed as its key selling point.
- Radware Bot Manager This is a plug-in that assesses each connection request and returns an accept or reject signal to your web server.
- Trustifi Inbound Shield An email spam blocker that also scans for phishing and malware. This is a cloud-based system.
Bot protection platforms typically use advanced algorithms to analyse user behaviour, traffic patterns, and other signals to distinguish between legitimate users and automated threats. They are capable of defending against a variety of attacks, including credential stuffing, account takeover, scraping, denial-of-service (DoS), and spam activity. By combining machine learning with threat intelligence, these systems can adapt to evolving attack techniques and reduce the likelihood of successful exploitation.
Modern bot protection solutions also provide real-time monitoring and response capabilities, enabling security teams to identify and block malicious activity as it happens. Many include reporting and analytics features that offer visibility into attack trends and potential impact, alongside enforcement tools such as CAPTCHA challenges, rate limiting, and IP blocking.
In this guide, we will explore the top bot protection software solutions available, comparing their features, benefits, and pricing models. With the right protections in place, businesses can safeguard their digital assets, improve user experience, and reduce exposure to bot-driven threats.
Bot blocking
Step one in bot protection is to identify traffic that originated from a botnet or a spam email server. Several strategies can be implemented to spot bot activity but one of the most effective lies with shared intelligence platforms that create lists of known bot IP addresses.
Some blacklists are maintained by non-profit organizations, while others are compiled privately y large cybersecurity businesses that offer spam filters and DDoS protection. In the latter instance, the security provider adds to its blacklist each time it detects suspicious activities deriving from a previously unlisted address.
Botnet blockers that prevent attacks on websites use three basic strategies:
- Blacklists
- Activity tracking
- Challenges
Email spam filters are similar, but as email is not as interactive as website access, challenges aren’t possible so the systems they use are:
- Blacklists
- Threat intelligence feeds
- Content scanning
Blacklists are a form of threat intelligence. They are contributed to by many different organizations and identify the IP addresses that are the sources of bot activity. Some businesses, such as games servers operate their blacklist strategies and will block entire ranges of IP addresses, often locking out innocent visitors whose IP addresses just happen to fall within the currently-blocked range.
Banning ranges of IP addresses is an example of an unsuccessful bot protection strategy. Bot protection aims to weed out malicious traffic while allowing genuine transactions through seamlessly.
By the measure of seamless access, challenges aren’t very effective either. The general public gets annoyed by those “I am not a robot” checkboxes and the demand to identify pictures of boats or traffic lights. However, as this method is now so prevalent, the public has become used to the inconvenience. There are more sophisticated systems available.
The best bot protection software
Our methodology for selecting bot protection software
We reviewed the market for bot protection software and analyzed the tools based on the following criteria:
- A strategy that can block bot traffic without disturbing genuine visitors
- A system that combines bot protection with other system security measures
- A service that pre-filters traffic for bot protection
- A threat intelligence network that spots new campaigns
- Rapid action
- A free trial, a money-back guarantee, or a demo for a no-risk assessment opportunity
- Good value for money from an efficient service at a fair price
The key to both botnet blocking and spam filtering is the blacklist. Any strategy that allows valid traffic through without delay is preferable. With these selection criteria in mind, we looked for cloud-based systems that have scalable pricing structures and operate quickly.
1. MailWasher (FREE TRIAL)
MailWasher is an on-premises email management system that includes bot protection systems. There are two operating models of MailWasher. One works in the email client and the other integrates into the email server.
Key Features:
- On-Premises Software: Deploys locally, providing control over email security without reliance on cloud services.
- Choice of Client or Server Protection: Available for both email clients and email servers, offering flexibility in deployment.
- Free Version: Offers a limited free version suitable for single email address protection.
- Blacklist System: Uses blacklists to identify and block spam emails, bouncing them back to senders as if the address was malformed.
- Compatibility: Compatible with various email clients, including Outlook, Thunderbird, Gmail, Hotmail, and more.
- Sandboxing and Previewing: Allows emails to be sandboxed and previewed before they are fully received.
Why do we recommend it?
Mailwasher is a cost-effective and versatile email management system, providing robust spam and malware protection for small businesses. Its compatibility with various email clients and the option for on-premises deployment make it an attractive choice for those wary of cloud-based solutions.
A disadvantage of the Mailwasher deployment model is that it allows malicious emails onto your system before they can be checked. Cloud-based systems have the attraction of preventing that contact. However, some small business owners are suspicious of cloud services and prefer to keep their systems in-house. If that is the case with you, Mailwasher could be a good solution.
MailWasher Pro plugs into email clients and is compatible with Outlook, Outlook Express, Incredimail, Thunderbird, Windows Live Mail, Gmail, Hotmail, EM Client, and Yahoo. This version only runs on Windows. MailWasher Server is available for Windows and Linux.
Both systems use a blacklist system and they bounce back emails from spambots as though the email address was malformed. The Mailwasher Free edition is the same as MailWasher Pro but it is limited for use with one email address.
Who is it recommended for?
Mailwasher is ideal for small businesses and individual users who prefer an on-premises solution for email security. It’s particularly suited for those looking to protect single or limited email addresses and wanting to maintain control over their email management without relying on cloud services.
Pros:
- Cost-Effective: A low-cost solution ideal for small businesses looking to enhance email security.
- Email Client Compatibility: Supports a wide range of popular email clients, making it versatile for different user preferences.
- Malware Blocking: Includes features to block malware from email attachments and links.
Cons:
- Not Suitable for Large Businesses: May not be sufficient for larger organizations with extensive email security needs.
- On-Premises Limitation: Lacks the preventive advantages of cloud-based systems, as malicious emails reach the system before being checked.
You can get a 30-day free trial of MailWasher Pro and MailWasher Server.
EDITOR'S CHOICE
Mailwasher is our top pick for bot protection software because this system manages the most prevalent bot activity that your business will face: spam. Malwasher Pro is an email client plug-in that is compatible with Outlook, Incredimail, Thunderbird, and more. That unit is only available for Windows. Mailwasher Server connects to your email server and that tool is available for Windows and Linux. Whichever option you choose, the tool will scan all incoming emails and remove those that are believed to be spam. An administrator can examine the server quarantine area and the user can look at the spam that was sandboxed from the email client. It is possible to mark a suspended email as OK, so it and subsequent emails from that sender, will go to the intended inbox. Mailwasher Pro is available as a free app for iOS and Android.
Download: Get a 30-day free trial
Official Site: https://www.firetrust.com/products/mailwasher-pro/download
OS: Windows, Linux, iOS, and Android
2. Cloudflare Bot Manager
Cloudflare has a free tier and it has gained a big market advantage by promoting that free service through Web hosting providers. The Cloudflare system serves more than 28 million HTTP requests per second.
Web servers that are protected by Cloudflare get all of their incoming requests diverted to the Cloudflare servers instead. Cloudflare simultaneously offers a content delivery network (CDN) so in most cases, not only will the system filter out bot traffic but it will deliver web pages to genuine requestors. The CDN speeds up the delivery of web pages by directing requests to data services that are geographically close to the requestor. Thus, the requested content doesn’t have to travel very far.
Key Features:
- Widely-Used: Handles more than 28 million HTTP requests per second.
- DDoS Absorption: Provides strong protection against DDoS attacks by absorbing malicious traffic.
- Internal Blacklist: Utilizes multiple layers of checks to maintain an up-to-date internal blacklist.
- Fingerprinting: Uses advanced browser fingerprinting to identify unique browser characteristics and deter bots.
- Fast Processing: Accelerates content delivery via a content delivery network (CDN).
Why do we recommend it?
Cloudflare Bot Manager is a robust and widely-used solution that not only protects against various bot attacks but also enhances web page delivery speeds. Its integration with a global CDN and advanced fingerprinting techniques make it a powerful tool for securing web applications.
The Cloudflare blacklist operates on several layers of checks. This takes into account the fact that most web users don’t have a fixed IP address so just blocking traffic to an address punishes people for the actions of the previous users of the address. To do this, the service uses a technique called browser fingerprinting, which goes beyond the characteristics of the browser and checks on a range of factors, such as the operating system version and computer’s identifiers.
Cloudflare can also spot bots used for content scraping and credentials stuffing. It can identify inventory hoarding activity in shopping cart systems and spam emails. The basic Cloudflare plan is Free and that also includes a free SSL certificate. Larger businesses will need the capacity and extra features offered by the three paid plans.
Who is it recommended for?
Cloudflare Bot Manager is ideal for businesses of all sizes that require comprehensive web protection and enhanced content delivery. It’s especially suited for e-commerce platforms and enterprises needing robust defense against automated threats.
Pros:
- Ubiquitous Web Protection: Widely recognized and trusted for web protection services.
- Comprehensive Bot Protection: Shields against a variety of automated attacks, including content scraping and credential stuffing.
- Email Spam Filter: Includes spam filtering for email protection.
- Integrated CDN: Enhances web page loading speeds by leveraging a global CDN.
- E-commerce Protection: Guards against inventory hoarding and other e-commerce related threats.
Cons:
- Processing Delays: Checks can sometimes introduce delays in processing requests.
Cloudflare Bot Management is packaged in with a bundle of useful web management services. Your web server will only be accessed by the Cloudflare system checking for updates. All other requests for your web pages will be delivered directly from the Cloudflare data centers. As no one can get to your web server, there is no way any bot traffic can harm it. Cloudflare was one of the first DDoS protection services and its comprehensive free starter package is so far ahead of the competition that rivals struggle to compete with it.
Get started for free: https://www.cloudflare.com/plans/free/
Operating system: Cloud-based
3. TitanHQ Email Security

TitanHQ Email Security is an email filtering service that tracks both incoming and outgoing emails. The system offers bot protection when examining incoming emails and data loss prevention when handling outgoing mail.
Key Features:
- Spambot Blacklist: Utilizes a blacklist to block emails from known spam sources.
- Phishing and Impersonation Detection: Identifies and blocks phishing attempts and impersonation attacks.
- Malware Blocking: Scans emails for malware and suspicious links.
- Behavior Analytics: Uses behavior analytics to detect impersonation attempts and account takeovers.
- Data Loss Prevention: Protects against data loss by monitoring outgoing emails.
Why do we recommend it?
Email Security provides robust email filtering and protection against a wide range of threats, including spam, phishing, and malware. Its flexible deployment options and comprehensive security features make it a versatile choice for businesses looking to enhance their email security.
Bot protection systems include a blacklist of known spam sources plus searches for keywords that indicate known spam or phishing campaign texts. The service will also scan for spoofing. Other actions in the inbound filter include link checking and malware detection.
The system will hold back suspicious emails for manual inspection. The service can also be used to implement custom email blocks by defining a list of words to detect in email contents. The Email Security system uses behavior analytics to identify impersonation attempts and account takeovers.
Who is it recommended for?
Email Security is ideal for businesses needing comprehensive email filtering and data loss prevention, especially those using Microsoft 365. It’s suitable for organizations looking for both on-premises and cloud-based deployment options to secure their email communications.
Pros:
- Comprehensive Email Filtering: Scans both incoming and outgoing emails for enhanced security.
- Flexible Deployment: Available as both an on-premises appliance and a cloud service.
- Customizable Filtering: Allows custom email blocks by defining specific keywords to detect in email content.
- Microsoft 365 Integration: Offers a plug-in for seamless integration with Microsoft 365.
Cons:
- Limited Gmail Integration: Does not integrate with Gmail, which may limit its applicability for some users.
Email Security is offered as an appliance and it is also available as a cloud service. If you use Microsoft 365, you can get a Email Security plug-in to integrate the bot protection system.
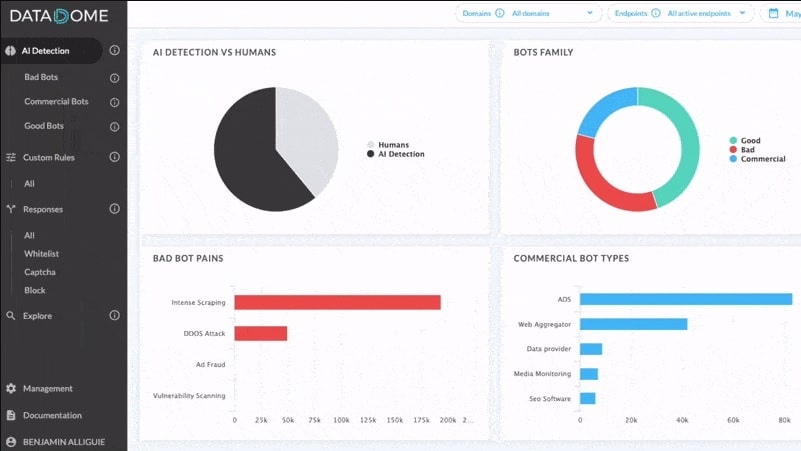
4. DataDome
DataDome is an AI-based bot protection system that rates requests rather than filtering them. This service is particularly active at protecting mobile apps and APIs. The Data Dome system works with your web server instead of replacing it. By use of a plug-in, your web server acquires access to the DataDome assessment engine. This issues a pass or fails instruction to your server for each incoming request. Each assessment takes about 2 milliseconds.
This traffic analysis system can block DDoS attacks, scraping, account takeover, and credentials stuffing. It also operates as a vulnerability scanner.
Key Features:
- Advises Your Web Server: Integrates with your server to assess and rate incoming requests.
- Pass or Fail Instruction: Issues quick pass or fail decisions for each request, with a 2-millisecond response time.
- Vulnerability Scanner: Identifies and scans for potential vulnerabilities in your web applications.
- Hacker Attack Blocker: Protects against DDoS attacks, scraping, account takeovers, and credential stuffing.
- Activity Logging and Analysis: Logs activities for detailed analysis and system hardening.
Why do we recommend it?
DataDome offers a sophisticated AI-based bot protection system that integrates seamlessly with your existing web server, providing quick and effective threat assessments. Its advanced vulnerability scanning and hacker attack blocking capabilities make it a powerful tool for maintaining web security.
The strategy of DataDome is agile and is less likely to cause access delays than the Cloudflare methodology. However, it is only suitable for businesses that have web servers with a large capacity because it doesn’t pre-filter traffic and so doesn’t reduce the load on web servers under attack.
Who is it recommended for?
DataDome is best suited for large enterprises with substantial web server capacities that require detailed, real-time bot protection and vulnerability scanning. It’s ideal for businesses that prioritize maintaining control over web delivery while seeking robust security measures.
Pros:
- Web Delivery Control: Allows you to maintain full control over web delivery while using the protection system.
- System Hardening: Enhances the security of your web server through continuous assessment and logging.
- Activity Analysis: Provides detailed logging and analysis features to understand and mitigate threats.
Cons:
- No Traffic Reduction: Does not pre-filter traffic, which means it doesn’t reduce the load on web servers under attack.
- High Cost: Significantly more expensive than competitors, making it suitable primarily for large corporations.
There are three plans for DataDome; Business, Corporate, and Enterprise. All of them are considerably more expensive than Cloudflare’s plans, so this is only a solution that would be considered by large corporations. You can assess DataDome with a 30-day free trial.
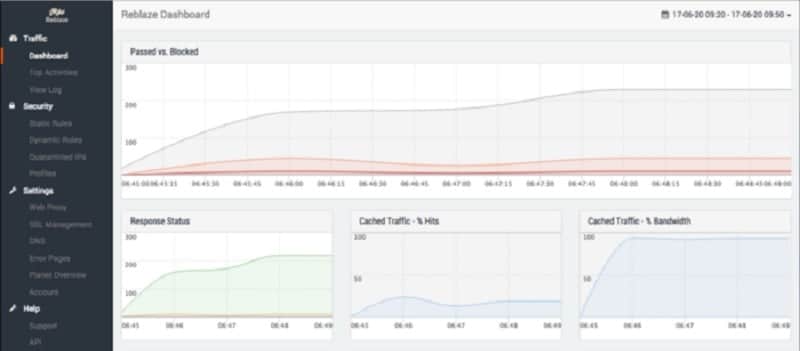
5. Reblaze Bot Management
Reblaze Bot Management has speed as its main selling point. It can process each incoming request in 0.5 milliseconds and legitimate users won’t notice any delay when accessing a website that is defended by the Reblaze bot protection system.
Key Features:
- Fast Processing: Processes each incoming request in just 0.5 milliseconds, ensuring no noticeable delay for legitimate users.
- DDoS Absorption: Efficiently absorbs and mitigates DDoS attacks to protect your web server.
- Screening: Filters incoming traffic through a multi-phase screening process that includes profiling and behavior analysis.
- Proxy Server: Routes all web traffic through a proxy server, reducing the load on your web server.
- Cloud-Based Dashboard: Provides live traffic performance data and attack analysis for enhanced security and market insights.
Why do we recommend it?
Reblaze Bot Management offers a high-speed, sophisticated bot protection service that efficiently filters out malicious traffic while maintaining fast access for legitimate users. Its comprehensive traffic validation and detailed analysis tools make it an excellent choice for robust web security.
Reblaze operates a proxy server. The worldwide DNS records for your website get altered so that all requests go to the Reblaze system instead of to your web server. Reblaze then checks through every incoming request and drops those that are malicious. Only genuine requests get forwarded to your web server over a secure VPN connection. This service greatly reduces the load on your system.
It receives your web traffic and filters it, passing on only legitimate users. The processing of each connection request takes only 0.5 milliseconds.
Despite being fast, the Reblaze filtering strategy is not brief. It passes through four phases that include profiling and behavior analysis. This is a very sophisticated bot protection service from a platform that also offers a web application firewall, a content delivery network, account takeover protection, and compliance reporting.
The Reblaze platform includes a cloud-based dashboard that displays live traffic performance data and also offers attack analysis services. The information given by the dashboard can also be useful for market analysis because it shows aggregated data about the source of your genuine traffic and factors such as the time of the day that sees the most activity.
Who is it recommended for?
Reblaze is ideal for businesses of all sizes looking for a fast, reliable bot management solution that offers detailed traffic analysis and comprehensive protection. It’s especially suited for companies that require efficient DDoS mitigation and advanced profiling for enhanced security.
Pros:
- Comprehensive Traffic Validation: Ensures thorough screening of all incoming requests to block malicious traffic.
- Detailed Activity Logging: Logs and analyzes traffic data, useful for both security and market analysis.
- Sophisticated Bot Identification: Identifies various types of bot traffic with advanced profiling and behavior analysis.
Cons:
- Undisclosed Pricing: The pricing structure is not publicly available, which can complicate budgeting and comparison.
You can assess Reblaze with a 30-day free trial.
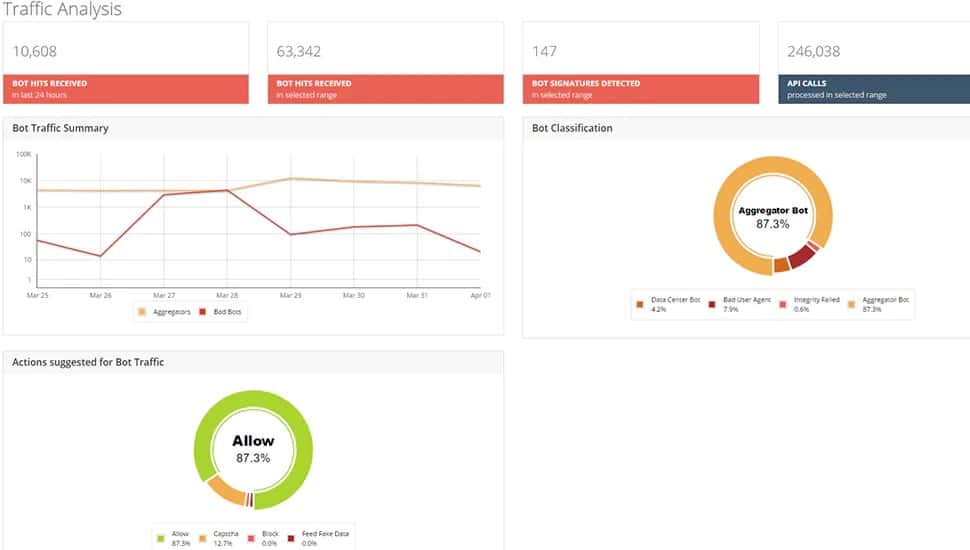
6. Radware Bot Manager
Radware Bot Manager has a name that is similar to Reblaze but an operating methodology that is similar to that of DataDome. Radware takes a connection request as input and assesses it. It then passes a signal back that informs the server whether to accept or reject the connection.
The Radware system modifies its assessments over time by using the AI methodology of machine learning. As each request is processed, its characteristics are noted. Thus, the Radware system will adjust its assessments according to that pattern of activity regularly experienced by that web server.
Key Features:
- AI-Based Assessments: Utilizes machine learning to continuously improve and adapt its threat assessments.
- Pass or Fail Response: Issues quick responses to web servers to accept or reject connection requests.
- Web Server Plug-In: Integrates seamlessly with existing web servers through a plug-in.
- reCAPTCHA Challenges: Implements reCAPTCHA challenges for additional bot verification.
- Fake Data Responses: Sends fake data to suspicious sources to confuse and deter bot controllers.
Why do we recommend it?
Radware Bot Manager leverages advanced AI and machine learning to provide adaptive and effective bot protection. Its ability to assess and refine responses in real-time, along with unique defense mechanisms like sending fake data, makes it a robust choice for enhancing web security.
Radware offers several bot protection options, which include a reCAPTCHA challenge and a defense response that sends back fake data to suspicious sources to confound bot controllers.
Radware also produces a web application firewall. There is an option to host the Radware system on your site as a virtual appliance.
Who is it recommended for?
Radware Bot Manager is ideal for businesses seeking an intelligent, adaptive bot protection solution that integrates with existing web infrastructure. It’s particularly suited for organizations looking for advanced threat mitigation techniques and customizable defense options.
Pros:
- Traffic Source Assessment: Continuously evaluates and adjusts based on the traffic patterns experienced by the web server.
- Adaptable Responses: Uses AI to adapt and refine its defense strategies over time.
- Active Defense Option: Can actively respond to threats by sending back fake data to bot controllers.
Cons:
- Malicious Traffic Reaches Server: Does not pre-filter traffic, so malicious requests still reach the web server before being assessed.
Radware Bot Manager is available on a 30-day free trial.
7. Trustifi Inbound Shield
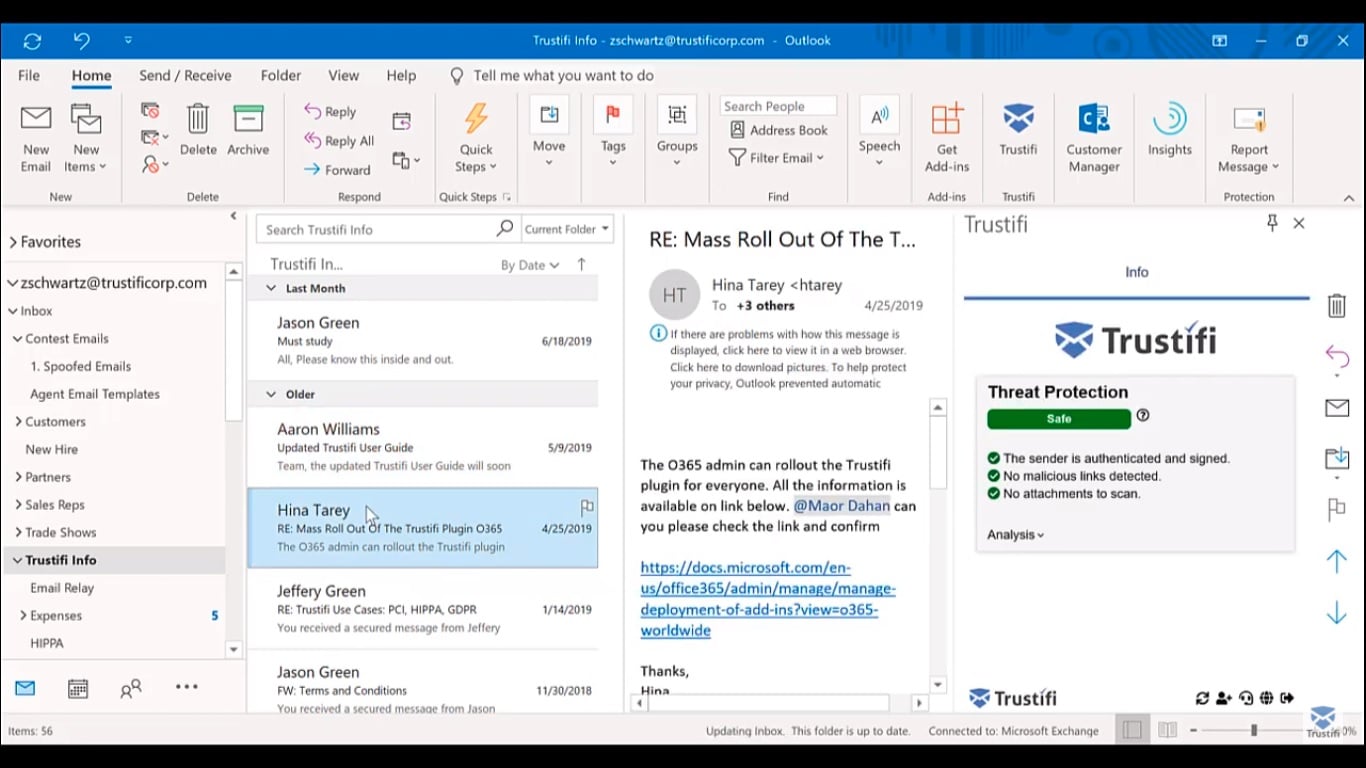
Trustifi Inbound Shield is an email detection system that identifies messages originating from spambots, and also scans for malware. The system is hosted in the cloud and you integrate it into your email system through the use of a plug-in. The service also provides a scanner that plugs into mail client software. The bot protection system can be applied to your on-site email servers and also Microsoft 365 and Google Workspace.
Key Features:
- Spambot Protection: Blocks emails originating from known spambots using blacklists.
- Account Takeover Detection: Identifies and prevents attempts to take over user accounts through impersonation.
- Malware Scans: Scans emails and attachments for malicious code and removes dangerous links.
- Phishing and Bulk Email Blocker: Effectively blocks spam, phishing emails, and bulk emails.
- Cloud-Based Integration: Integrates with on-site email servers, Microsoft 365, and Google Workspace through a plug-in.
Why do we recommend it?
Trustifi Inbound Shield offers comprehensive email security, protecting against a wide range of threats including spam, phishing, and malware. Its integration with major platforms like Microsoft 365 and Google Workspace, along with its advanced AI capabilities, makes it a reliable choice for safeguarding email communications.
Trustifi will block spam, phishing emails, and bulk emails. The system operates blacklists to quickly block emails from known spambots and it also applies AI to look at the likelihood that an email is genuine. This utility can catch impersonation attempts that are used in typical business email compromise (BEC) attempts. You can also catch account takeover with this tool.
The system scans emails and their attachments for malicious code. It also checks any links that it encounters and removes them if they lead to infected or fake webpages. Suspicious emails and attachments will be quarantined for manual inspection.
Who is it recommended for?
Trustifi Inbound Shield is ideal for businesses looking for robust email protection that integrates seamlessly with existing email systems. It’s particularly suited for organizations using Microsoft 365 or Google Workspace, needing advanced security measures against spam, phishing, and malware.
You can request a demo to assess Trustifi Inbound Shield.
Pros:
- Comprehensive Email Protection: Checks for spam, phishing, impersonation, and account takeover attempts, ensuring robust email security.
- Malware and Link Scanning: Scans emails and attachments for malware and malicious links, quarantining suspicious items for manual inspection.
- Seamless Integration: Easily integrates with popular platforms like Microsoft 365 and Google Workspace.
Cons:
- No Free Trial: Does not offer a free trial, which may limit initial user assessment.