Endpoint management is a cornerstone of modern IT operations, and finding the right software to streamline and secure this process is crucial for organizations of all sizes. Endpoint management tools are designed to help IT teams effectively oversee and safeguard the myriad of devices connected to their networks, such as laptops, desktops, mobile devices, and even IoT endpoints.
Here is our list of the best endpoint management software:
- NinjaOne Endpoint Management EDITOR’S CHOICE This SaaS package is a management service for desktops, laptops, and virtual systems and allows centralized management of those devices no matter where they are. Start with a 14-day free trial.
- Atera (FREE TRIAL) This SaaS platform provides remote monitoring and management systems in versions for IT support teams and managed service providers. The service can install and update the software on each endpoint and also gain remote access for maintenance tasks and user support. Access a 30-day free trial.
- SuperOps RMM (FREE TRIAL) Cloud-based system provides asset management and alert management functions for MSPs. This package works alongside a SuperOps PSA bundle. Access the 14-day free trial.
- Acronis Cyber Protect Cloud (FREE TRIAL) This cloud-based system backup and security package has a supplementary module that provides software management. Access the 30-day free trial.
- ManageEngine Endpoint Central (FREE TRIAL) Provides the best overall experience for PC and mobile endpoint management while offering remote assistance tools for support teams. Get a 30-day free trial.
- BMC Helix Client Management This SaaS package is a Service Desk system that provides endpoint management functions covering hardware and software support.
- Scalefusion UEM Offers device management capabilities that can operate controls for desktops and laptops running Windows, macOS, and Linux and mobile devices running iOS and Android. It is a cloud-based platform.
- Trellix XDR Platform This cloud platform coordinates the protection of all endpoints on a network and also scans the network for threats.
- VMware Workspace One UEM Can easily customize workspaces per group or department
- Microsoft Intune Integrates well into other Microsoft services and tools
- Ivanti Unified Endpoint Manager Focuses heavily on providing large-scale enterprise UEM solutions
The primary purpose of endpoint management software is to centralize and automate device management. However, these tools go beyond basic monitoring, incorporating advanced features like software deployment, patch management, security enforcement, and asset inventory tracking.
With the rise of remote work, bring-your-own-device (BYOD) policies, and distributed environments, maintaining control over endpoints has become increasingly complex. These tools enable IT administrators to ensure devices are compliant with security policies, up-to-date with necessary patches, and protected against potential vulnerabilities. They also provide a unified platform for handling tasks like configuration management, troubleshooting, and deploying operating system updates.
Endpoint management tools enhance security by offering features such as endpoint detection and response (EDR), antivirus integration, and real-time threat monitoring. They also help organizations meet regulatory compliance requirements by providing detailed reporting and audit trails. For businesses aiming to minimize downtime and improve productivity, these tools are invaluable as they facilitate rapid issue resolution and proactive management.
Whether your organization is focused on improving operational efficiency, strengthening security, or ensuring constant service, endpoint management software is essential. By choosing a solution tailored to your specific needs, you can enhance control, reduce administrative overhead, and safeguard your IT infrastructure. Explore our guide to the best endpoint management tools to discover the right fit for your organization.
What to look for in endpoint management software
Unified Endpoint Management (UEM) Overview
For example, Unified Endpoint Management (UEM) is designed to cater to all your management needs for both mobile and desktop devices. This centralizes security, patching, and performance monitoring, backup and recovery, and more. Large MSPs and enterprises usually prefer this approach to endpoint management. UEM can also detect new devices and identify threats such as rogue access points or non-company devices. UEMs often contain everything you need for endpoint management and remote access but tend to be priced higher.
Related post: Best Unified Endpoint Management
Remote Monitoring and Management (RMM) Overview
Remote Monitoring and Management (RMM) provides endpoint management by remotely gathering data on each endpoint. Administrative tasks and scripts can also be carried out remotely, usually without impacting the end user’s workflow. RMM is ideal for MSPs and multi-site organizations that need endpoint management but can’t deploy on-site staff. RMM tools can provide endpoint management but also feature a host of tools designed for support technicians. In addition, many RMM integrates into service desk applications to automatically generate tickets when an issue is detected.
Endpoint management options
The Importance of Endpoint Management
Endpoint management is the core requirement of any business. Users touch the endpoints and they care about them – they need them to work properly and whenever endpoints malfunction, users take it personally. Users don’t care about the network – it’s something they don’t see and they don’t understand.
Dividing Endpoint Management: Hardware and Software
Endpoint management is concerned with two basic categories: hardware provision and software management. Hardware asset management is concerned with the depreciation period for each endpoint purchase. Software management is the most time-consuming aspect of endpoint management.
Challenges and Solutions in Software Management
Software management requires license management to ensure that you aren’t installing more copies of the software than you have licenses for. You also need to ensure that users aren’t installing their own favorite software on devices and that viruses can’t get onto the endpoints. So, with this category of endpoint management, you need to look at software deployment systems and patch management. At this point, you are moving into security monitoring.
The Best Endpoint Management Software
Many endpoint management software companies are looking to be an “all in one” solution by providing everything from remote access to patching under one platform. To simplify your choice, think about which features are most important to you.
Here is our methodology and key criteria for selecting endpoint management software:
- We looked for scalable systems that offer the same level of service no matter how large the fleet that needs to be managed – this is effectively dealt with by -er-device pricing.
- The system should integrate strong security features, including encryption, multi-factor authentication, and regular updates to safeguard your endpoints.
- A service that is able to integrate with third-party tools or other modules from the same platform would get priority.
- We prefer systems that offer user-friendly interfaces, so they can be easily managed by anyone with minimal training – built-in usage guides are also a plus.
- Task automation features get tools onto our list because we know that our readers are looking for ways to improve efficiency and lower costs.
- We made sure that the systems meet industry standards and regulatory compliance requirements.
- Total cost of ownership should be reasonable, with the system paying back its acquisition cost through improved services.
With these criteria in mind, we selected a range of tools that will provide options for all our readers. Almost all of the systems we selected are cloud-based SaaS systems, but we made sure to include at least one package for companies that don’t like could systems.
1. NinjaOne Endpoint Management (FREE TRIAL)
NinjaOne Endpoint Management is a cloud-based service that lets you manage desktops and laptops no matter where they are located. This service enables you to create a group of all of the devices that your users have, whether they are corporate-owned or user-owned. They can be on many company sites or in the homes of telecommuting staff.
Key Features:
- Fleet Device Management: Manages devices running Windows, Linux, and macOS
- Automated Monitoring: Monitors network activity
- Remote Access: Includes remote desktop and remote control
- Vulnerability Scanning: Looks for outdated software
- Software Repair: Patch management
Why do we recommend it?
NinjaOne is another cloud-based RMM package and its Endpoint Management service is very similar to that offered by Atera. Alongside discovery and inventory services for all on-site equipment, this system is able to manage endpoints running Windows, macOS, and Linux by providing patch management and automated maintenance routines.
The service is able to watch over virtual systems, such as hypervisors, as well as physical endpoints. The tool compiles hardware and software inventories, spotting operating systems and software packages that are out of date and need updating. This discovery leads to a patch manager fixing the problem. The package also offers a software license manager and an automated software deployment tool.
You can use this system to provide technicians remote access to the protected devices for troubleshooting and problem fixing. This option also allows technicians to take control of the remote devices.
The NinjaOne platform has a multi-tenant option, which is suitable for use by managed service providers. However, the platform is also available for use by in-house IT operations teams. Endpoint Management is one unit on the NinjaOne platform. The entire system provides all of the software that a support department needs to manage IT inventory and support users.
Who is it recommended for?
This system is a SaaS package and it can be used by IT departments and managed service providers. The full NinjaOne package also provides a ticketing system for service requests. Technicians can use a remote access utility to manually troubleshoot device problems and there is also a remote desktop feature.
Pros:
- Multi-Tenant Architecture: Suitable for use by MSPs or IT operations teams
- Monitor Endpoints Wherever They Are: Create a group of geographically scattered devices
- Centralize Management: Creates hardware and software inventory
- Tracks Physical and Virtual Systems: Monitors virtualizations
- Alerts for Performance Problems: Leave the system to watch over regular activity
Cons:
- No Price List: You have to consult the sales department
As a SaaS package, the NinjaOne Endpoint Management system includes the server to run the software and cloud storage space for logs. You don’t have to download any software to access the Endpoint Management console but the system will download agents onto managed endpoints during the setup process. G2’s consistent acknowledgment for 11 times in a row underlines NinjaOne’s strength in RMM, Patch Management, and Endpoint Management. You can register for a demo to examine the NinjaOne Endpoint Management system or you can evaluate the software on a 14-day free trial.
EDITOR'S CHOICE
NinjaOne Endpoint Management is our top pick for an endpoint management software package because this tool is hosted on the cloud, so you don’t need to organize server space for the software or data and you don’t need to perry about keeping the service up to date – NinjaOne technicians do that for you. NinjaOne Endpoint Management supports a wide range of device types, including Windows and macOS computers, Linux systems, and mobile devices like iOS and Android smartphones and tablets. This versatility allows IT teams to manage diverse environments, from traditional office setups to modern Bring Your Own Device (BYOD) scenarios. Services in the package include real-time monitoring, automated patch management, and remote access for troubleshooting and manual problem resolution. The mobile device management module includes tracking, locking, and wiping for security. It enables fleet devices from being used to access non-approved apps and a phone or tablet can be set up with a full complement of software with the application of a pre-defined profile. User-owned devices can be enrolled through an automated sign-up process and all devices are scanned for security issues before being allowed to connect to the network and corporate services. Patching is available for workstations and servers running Windows, macOS, and Linux. Automated and manual maintenance tasks can be implemented even if the device is turned off, thanks to a Wake-on-LAN feature. Devices can also be rebooted and turned off remotely.
Download: Start 14-day FREE Trial
Official Site: https://www.ninjaone.com/freetrialform/
OS: Cloud-based
2. Atera (FREE TRIAL)
Atera is a single codebase, cloud platform for IT Departments and Managed Service Providers that includes Remote Monitoring and Management (RMM) and Professional Services Automation (PSA). Atera’s RMM offers many capabilities that support the management of endpoint devices and is also useful for the IT Operations departments of multi-site businesses.
Key Features:
- Scaleable Subscriptions: Pay-per-technician pricing
- Live Remote Monitoring: For IT management
- Multi-Platform Agent: Support for Windows, macOS, and Linux
- Integrations with Software: Bitdefender, Acronis, and Open AI
Why do we recommend it?
Atera is a remote monitoring and management package that is delivered from the cloud. This system includes endpoint management functions synch as patch management and maintenance automation. The patch management scheduler can also be used to implement standard tasks such as reboot or the removal of temporary files.
A Network Discovery service is available as an optional feature of the RMM package. This will scour the client’s system and record all of the equipment connected to the network. With this sweep, the network discovery system creates an IT asset inventory. That service is useful for the ongoing management of a client site but it is also a useful aid for sales team when compiling quotes and organizing contracts – new clients often don’t know exactly what assets they have on-site.
Identifying each endpoint and network device enables the RMM system to scan each endpoint periodically for status problems automatically. It also enables an automated software management service to operate.
The Atera system’s IT asset management services include the compilation of a software inventory for each monitored endpoint. The system then consolidates those lists into one central register of operating systems and software packages with their current version numbers. The software inventory automates the task of software license management and also assists the sales team in right-sizing contracts.
Patch management is a crucial function in endpoint management and this is a key service in the RMM package from Atera. The Atera system includes a lot of automation because the designers of the platform realized that IT teams need to squeeze as much value as possible out of their teams of technicians. Thus, much of the patch management system within the RMM service is automated.
When an update becomes available for any of the systems listed in the software inventory, the Atera patch manager identifies them and copies over their installers. When working for a new client, the patch manager’s processes will begin by bringing all software up to the latest versions, which could involve the application of a series of patches for each package. The patch manager is able to sort out patch dependencies and order their rollout.
The Atera menu of services includes the option to add-on integrations to endpoint detection and response software provided by Bitdefender, there is also an option to add on Acronis backup software.
Who is it recommended for?
Atera is constructed in two versions: one for IT departments and the other for managed service providers. The plans for each version have different modules, according to the needs of each business type. Atera is priced per technician, so the smallest business gets all of the features enjoyed by large companies but at an affordable rate.
Atera is offered in versions that are suitable for use by managed service providers and IT departments. MSPs need a multi-tenant architecture in their remote monitoring and management systems because they need to keep the data for each client completely separate. While IT departments benefit from remote management tools, they don’t need to create any sub-accounts. So, by offering two account structures, Atera is able to appeal to both markets. This system includes automated processes for software management and also facilitates manual remote access. The Atera package is also available with a ticketing system that enables managers to allocate work to support technicians and monitor progress.
Pros:
- A Cloud-Based System: Can be accessed from anywhere
- Ticketing System: Allows a distributed team to be centrally managed
- Network Discovery: For an extra charge
- Automated Software Management: License management and patching
Cons:
- The Network Discovery Service Costs Extra: Unusual for system monitoring packages
The Atera package is available in the plans: Pro, Growth, and Power for MSPs, and Professional, Expert, Master, and Enterprise for IT Departments. Pricing starts at $129 per technician. You can experience the Growth package with a 30-day free trial.
3. SuperOps RMM (FREE TRIAL)
SuperOps RMM is a SaaS package that includes four modules. These are Asset Management, Patch Management, Policy Management, and Alert Management.
Key Features:
- Remote Monitoring and Management: Professional services automation (PSA) also available
- Designed for MSPs: Multi-tenanted architecture
- Software Management: Patch manager
Why do we recommend it?
SuperOps RMM is a rival to Atera. This SaaS platform provides remote monitoring and management tools. This is one of two modules on the SuperOps platform, with the other being its PSA system. While the RMM package provides system monitoring and management tools, the PSA module includes MSP management tools.
Asset Management provides a discovery service for all of the network-connected assets on client sites. The service implements continuous monitoring of endpoints and network devices to watch over operations. The system tracks capacity utilization of resources and spots when possible shortages may be about to occur.
The Alert Manager is a notification system that is based on a series of performance thresholds and lets operators get on with other tasks, knowing that they will be notified if things turn bad. For example, a network device could have a threshold capacity of 75 percent placed on it. If throughput rises above that level, a technician will be notified to pay attention. In short, the thresholds are set to issue warnings of conditions that could cause performance issues if they deteriorate further. If a network is properly planned, capacity problems should be a rarity.
While network throughput is being tracked, the SuperOps system also receives regular status reports from device agents. This ensures that device failure can be dealt with quickly. The same capacity and status checks are reported on endpoints as well.
The Policy Management module helps support team managers ensure that they keep in line with the SLAs that the MSP has set up with its customers. These influence threshold levels to ensure that problems can be dealt with in the time specified by the support contract.
The Patch Management module is also an automated service. It looks through the software inventory that is maintained by the Asset Management system and checks routinely for the availability of patches and updates for those packages and systems.
Patches can be queued for automatic, unattended rollout at the next available maintenance window. The completion statuses of each patch application are shown in the SuperOps dashboard. All of the actions taken by the patch manager and the monitoring service are logged. Performance logs also allows for historic analysis of operations and responses.
Who is it recommended for?
This package is available as a standalone package or in a bundle together with the SuperOps PSA module. The plans for SuperOps are priced per technician, which makes this service accessible to businesses of all sizes. The RMM can be used by managed service providers and in-house IT support teams.
Pros:
- Automated System Discovery: Creates hardware inventory
- Automatic Monitoring with Alerts: Improves technician efficiency
- Partners with a PSA Module: Provides a ticketing system
Cons:
- Can’t Monitor Endpoints Running Linux or macOS: Only Windows
SuperOps offers four plans. All except for the Starter plan include both the PSA and RMM packages. The Starter plan is PSA-only. Of the three RMM plans, the lowest, Solo, is intended for independent technicians and is free to use for the first year. The two upper plans, Growth and Premium, are available for a 14-day free trial.
4. Acronis Cyber Protect Cloud (FREE TRIAL)
Acronis Cyber Protect Cloud is a package of system security tools that is aimed at Managed Service Providers (MSPs). An extension to this bundle of data protection services adds on software management – this is called Acronis Advanced Management. The main feature of this service is an automated patch manager.
Key Features:
- Vulnerability Scanning: Identifies system security weaknesses
- Software Inventory: Automated patching
- Ransomware Protection: Data backup
Why do we recommend it?
Acronis Cyber Protect Cloud is one of a list of device protection packages from Acronis. This bundle is a SaaS platform for use by businesses. This is a security bundle that emphasizes data security. The system protects each endpoint from malware and is particularly effective against ransomware because it includes a backup and recovery service.
The Acronis system includes an autodiscovery service to identify all hardware on a network and log it in an inventory. The Advanced Management service then scans each device for software and builds up a software inventory. The service then continuously scans both internally and externally for system vulnerabilities. It will automatically schedule patches when they become available.
This software management service runs alongside a data protection system that identifies insider threats and protects data from deletion or tampering through a constant backup system.
The package includes antivirus services to keep your software safe from unauthorized replacement. Advanced Management controls what software is allowed on each of your endpoints.
Who is it recommended for?
Acronis offers three editions for its Cyber Protect Cloud package. Higher plans don’t get all of the features of the cheaper plans. For example, patching is available in the two lower plans but not the top edition. The service is priced per endpoint, which makes it scaleable and suitable for any business.
Pros:
- Designed for MSPs: A multi-tenant architecture
- Automated Software Controls: Protection against unauthorized installations and ransomware
- Continuity Planning: Store profiles on the cloud to reinstall systems quickly
Cons:
- Doesn’t Include an Onboarding Tool: Does provide process automation scripting
The scripting system built into Acronis allows you to create task automation services for issues such as software deployment. The service is delivered from the cloud and installs its own agents on protected networks. You can try out Acronis Cyber Protect Cloud with a 30-day free trial.
5. ManageEngine Endpoint Central (FREE TRIAL)
ManageEngine Endpoint Central is a UEM tool designed to help administrators perform patching, deploy software, install operating systems, and provide remote control to devices. The platform supports Windows, Mac, and Linux operating systems making it an excellent choice for a diverse network.
Key Features:
- Fleet Onboarding: Automated software installation
- Software License Management: Creates an inventory
- Patch Management: Automated scanning
Why do we recommend it?
ManageEngine Endpoint Central discovery, registers, and monitors all endpoints on a system. It is also possible to enroll individual remote devices into the monitoring scheme. All endpoints that are logged in the system can also be managed remotely. Tools include software deployment, patching, endpoint security, configuration management, and USB device controls.
Endpoint Central stands out for being highly flexible and doesn’t put its users in a box when it comes to management. For example, not all administrators want endpoint security with their endpoint management. In addition, some platforms come with their security by default, which can clash with existing endpoint antivirus software. So instead, Endpoint Central offers optional endpoint protection through an endpoint security add-on. The add-on provides vulnerability assessments, app control, device control, and BitLocker control.
Visually the platform is very well designed and feels naturally intuitive to use. Additionally, the platform comes with numerous widgets that can be easily used to customize the look and feel of each screen. This is great for customizing dashboards for helpdesk teams or simply organizing what daily metrics are essential to you.
The platform also comes with a live device topology map. This populates with the latest devices and helps give sysadmins a visual look into how and where their managed devices communicate. This is particularly useful on more extensive, more complicated networks to help simplify how you see your devices.
The platform offers over 50 pre-configured desktop configuration options for management for administrators with specific desktop policies. Options like power settings, security policies, and USB device options can easily be set through the Endpoint Central GUI. I enjoy this option as group policy can cause many headaches, significantly when you’re modifying many local settings. Excellent addition to the many security features you don’t see in most management software is Data Loss Prevention (DLP).
With this tool, you can set up DLP through file mirroring, making it easy to monitor files for changes and immediately restore lost files from backup. You can even set policies to control how or where a file is shared. For example, for can set sensitive company information to be restricted from leaving the network or being copied to a device.
Overall, Endpoint Central provides a highly refined and streamlined endpoint management experience that’s tough to beat. While Endpoint Central focuses heavily on managing endpoints, integrations are available into other ManageEngine products for extended capabilities like behavioral analysis and infrastructure monitoring.
Who is it recommended for?
This package has a lot of deployment options. You can host it, either on one of your Windows Server hosts or on your AWS or Azure account. It is also available as a SaaS package. This bundle is intended for use by IT departments and there is a higher plan that includes mobile device management.
Pros:
- On Premises or Cloud Hosting: Can be installed on Windows, Azure, or AWS and is also available as a SaaS platform
- Manages Workstations: Can be running Windows, macOS, or Linux
- Mobile Device Management: For iOS, Android, and smart TVs
Cons:
- Reduced Features for Linux: More features for managing Windows and macOS
You can test out Endpoint Central and all of its features completely free through a 30-day trial.
6. BMC Helix Client Management
BMC Helix Client Management is an asset discovery and software management system for Service Desk teams. It works with endpoints running Windows, macOS, or Linux. This is a smaller package from BMC that can be expanded into a full-service management package for larger businesses, which is called BMC Helix ITSM.
Key Features:
- Device Discovery: Creates hardware and software inventories
- Operating System and Software Deployment: Set up device or role profiles
- Patch Management: Automated execution
Why do we recommend it?
BMC Helix Client Management provides an automated asset tracking system that discovers all of your endpoints and then protects them by managing their software inventories. This ITSM service will help to control the applications on your site, manage software licenses and identify unauthorized software. The tool can manage devices running Windows, macOS, and Linux.
This system explores your network and identifies each endpoint. It then populates a hardware inventory, which records details about each device. The tool will then scan each endpoint and identify all of the software installed on it. This phase is useful for software license management and it will also show you unauthorized software on fleet workstations.
The Helix package provides a software deployment system, which can also install operating systems. It is also possible to put together installer packages and make them available to users so that they can install the software at their convenience. The Client Management package also includes an automated patch manager.
This service will create a standard configuration for fleet devices and apply it, checking periodically if those security policies have been changed.
Who is it recommended for?
This is a tool for system administrators. It lets you create software deployment packages to onboard a new computer or reconfigure an existing device for a new user. It also includes a configuration manager to control device settings and a patch manager to keep software up to date.
Pros:
- Manages Devices: Hardware inventory creation and maintenance
- Scans for Software: Software inventory and license management
- Compliance Management: Security policy enforcement
Cons:
- No Price List: You have to contact the sales department
BMC doesn’t publish a price list but you can contact the company for a quote. BMC offers Helix Client Management on a 30-day free trial.
7. Scalefusion UEM Solution

Scalefusion UEM provides management tools for endpoints running Windows, macOS, Linux, Chrome OS, iOS, and Android. That list of operating systems shows that you can manage any device with the platform, even field equipment and retail signage.
Key Features:
- Scalable Subscriptions: Per-device pricing
- BYOD Options: Also fleet device management
- Deployment Options: Single and multi-app kiosk mode
Why do we recommend it?
The list of operating systems that Scalefusion can manage means that you can control just about any device with the package, even IoT devices and retail equipment. Scalefusion provides a Kiosk Mode, which can be deployed for use on devices that need only one or two applications, such as waiter input devices or customer help screens in stores.
The Scalefusion dashboard is hosted in the cloud- so system administrators aren’t restricted to managing devices on one site. The capabilities for managing mobile devices are more extensive than office desktops
The Scalefusion package provides different utilities to deal with different device types and ownership configurations. The facilities for managing mobile devices are more extensive than for office desktops because there are many more issues to deal with equipment that operates outside of the building.
Features that only apply to mobile devices include tracking, locking, and wiping. Another useful service is geofencing, which blocks some functions of a device if it is taken outside of an approved jurisdiction. An example of such a scenario would be if a digital nomad employee working for a European company decided to roam outside of the EU, where access to stored customer data should be prohibited.
Features that cover all types of devices include onboarding, patching, and application provisioning Software controls extend to customized applications that have been developed in-house as well as to packages that are bought off the shelf and require license management. All types of company-owned endpoints can be protected against unauthorized software installation, and there is even an option to separate personal and corporate apps and data on employee-owned devices under BYOD management.
Although Scalefusion can manage on-premises computers, it has to be said that the mobile device management services in the package are much more comprehensive. These extend to containerization for BYOD or user-owned devices while securing corporate data on them.
Who is it recommended for?
The range of plans with different lists of functions makes Scalefusion suitable for any type of business. However, companies that use a lot of mobile devices and permit BYOD will benefit the most from this solution. Retailers with point-of-sales equipment, engineers with field devices, consultants and artisans who are almost constantly out of this office are some of the business users who need this package the most.
Pros:
- Multiple Device Types: Manages desktops, retail POS devices, mobiles, laptops, and rugged devices
- Application Profiles: Supports user self-enrollment
- Kiosk Mode: For retail purposes
- Location Tracking: Includes remote wipe option for lost/stolen devices
Cons:
- BYOD Not in All Plans: The cheapest plan doesn’t provide BYOD management
There are four plan levels with higher plans offering more features for a higher monthly fee. In all cases, the editions can track desktops on multiple sites and mobile devices wherever they are in the world. You can get a 14-day free trial of any edition.
8. Trellix XDR Platform
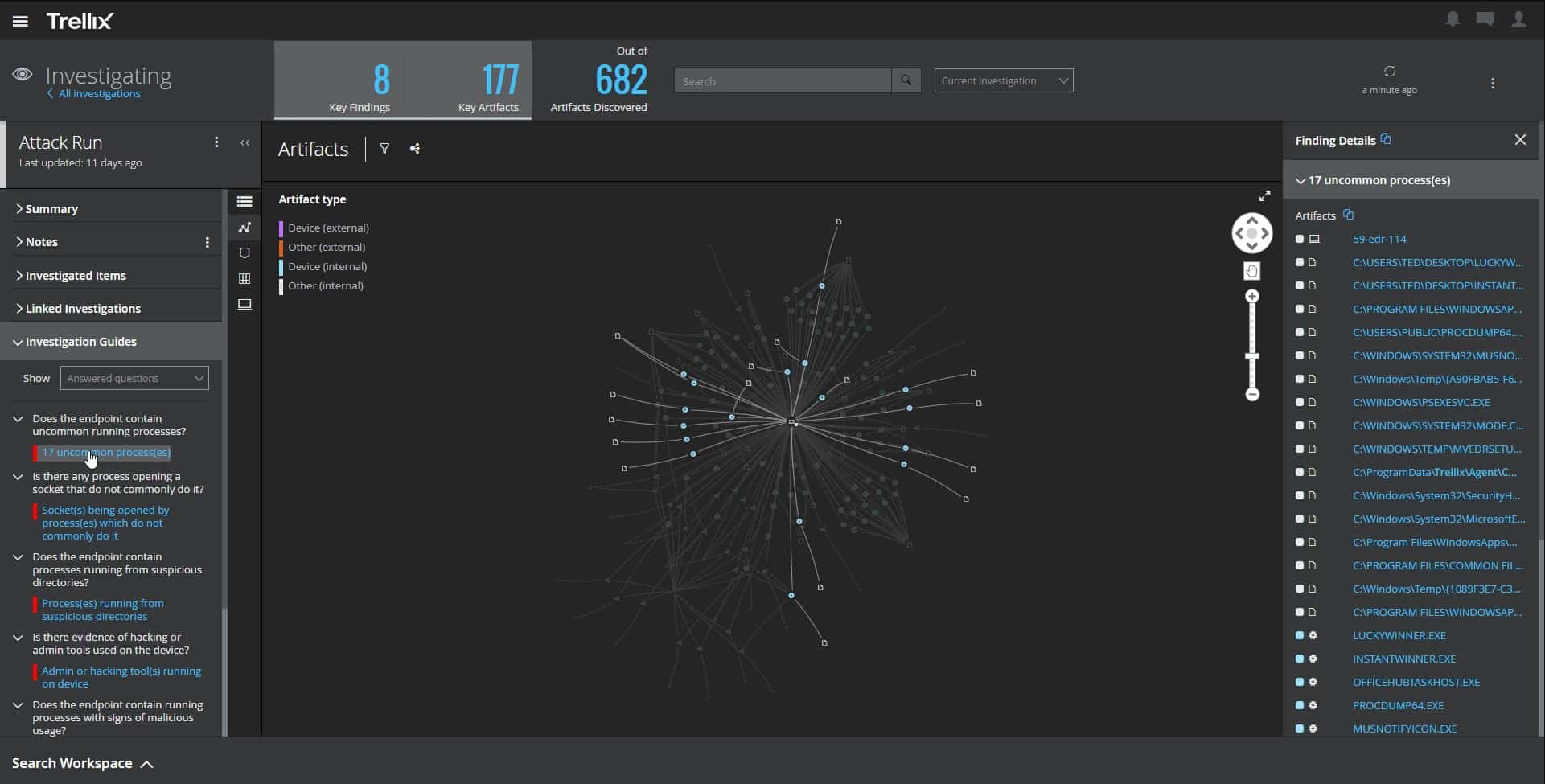
Trellix XDR Platform scans endpoints and networks to spot unusual behavior that could be generated by malicious intent. This isn’t so much an endpoint management package but an endpoint protection system. This system is based in the cloud but installs an agent on each endpoint for monitoring.
Key Features:
- Tracks Activity: Both endpoint and network monitoring
- Identifies Threat: Zones in on serious, irregular activity
- Automated Responses: Shuts down attacks
Why do we recommend it?
Trellix XDR is an important tool because it blocks all attacks on your endpoints. Unfortunately, hackers are highly skilled con artists with technical expertise and that means they are very good at tricking employees into disclosing their account credentials and downloading malware. So, you need constant scanning to spot and block all types of attacks.
The XDR system has an AI core that uses machine learning to work out what is normal behavior on that endpoint and for each user account that accesses the device. When activity changes, the Tellix service pays attention. This is the trigger for closer scrutiny and will result in confirmation or de-escalation.
A threat will trigger an alert in the Trellix dashboard and will also trip an automated response. Malware is killed and deleted, a suspicious user account gets suspended and traffic from a malicious external source will be blocked.
The Trellix system is a competent and reliable service that you just leave running in the background. You don’t need to be a cybersecurity expert to set this system up.
Who is it recommended for?
This package is suitable for any business. Looking at the price list for the XDR on AWS, it is pretty clear that small businesses will need to look for alternative endpoint protection systems, some of which are free. Mid-sized companies and large organizations will be attracted to this system-wide cybersecurity package.
Pros:
- Identifies and Shuts Down Threats: Follows playbooks
- Works on Hybrid Environments: Covers cloud platforms as well as endpoints
- Combines Endpoint Protection and Network Scanning: Also ingests cloud service logs
Cons:
- Pricey: Likely beyond budget range for smaller business settings
The best way to assess the Trellix XDR platform is to request a demo.
9. VMware Workspace One UEM
VMware Workspace One UEM aims to provide total visibility and control into physical and virtual endpoints no matter where they’re located. A big plus is that Workspace One integrates seamlessly with VMware products like Vmware Horizon, making it a solid choice for companies that heavily rely on VMware environments. In addition, workspace One helps sysadmin manage endpoints and build custom workspaces for specific departments or staff to work as efficiently as possible.
Key Features:
- Integrates with VMWare Hypervisor: Creates a desktop for each user
- Manage BYOD: ACcess through a portal
- Single Sign-On Environment: Ease of use
Why do we recommend it?
VMware Workspace ONE provides mobile device management, desktop management, or both depending on which plan you choose. This is a cloud-based system, so the console can be accessed from anywhere through a Web browser. The tool provides a range of solutions that cater to fleet divides and BYOD.
The platform takes an exciting approach to endpoint management by using Single Sign-On (SSO) to track and manage staff as they work in SaaS environments and transition back to on-premises tools. The tool does a great job of managing endpoints but also managing the connections and authentication to cloud-based tools. In addition, workspace One is compatible with the BYOD model and allows users to authenticate via an app to access corporate material on their own devices securely.
The web-based interface is built well and makes it easy to find and manage multiple devices and users, even when tested at an enterprise level. This usability extends to their mobile app as well, which is nice to see. Unfortunately, many platforms neglect their mobile app, making it tough to use or lacks features found on the web version. For example, corporate devices can automatically install company apps, lockdown devices upon terminations, and accept credentials from SSO or Active Directory through the VMware Tunnel VPN.
Administrators can also set up a form of identity access management through the workspace UEM, giving it more flexibility than similar UEMs when it comes to identity services. For example, rather than enforcing two-factor authentication on every connection, the network access control section can configure risk-based endpoint authentication for less tension between the user and the security policy.
Access control is very intricate and can take time to learn. There are numerous configurations allowing access by device, group, network configuration, or geographic location. I think more templated access rules could help flatten the learning curve with these features in particular.
Who is it recommended for?
VMware is a leader in virtualization and its endpoint management service can take advantage of that by providing containerized access to applications and data over the network or the internet. This is particularly useful for roaming and remote workers who might frequently switch devices and use their own equipment to access corporate data.
Pros:
- User-Friendly Experience: Creates a consistent environment per user
- Straightforward BYOD Enrollment Process: Set up accounts for users
- Great Mobile App Accessibility: Preserves corporate asset security
Cons:
- Password Sync Problems Over LDAP: Can trigger a false compromised alert
10. Microsoft Intune
Microsoft Intune works to bridge the gap between endpoint management in the cloud and on-premises by offering several tools and features that unify staff computers, phones, and virtual machines in a single place. Intune is considered a UEM form of management as it can control desktops and cellular devices across their entire lifecycle.
Key Features:
- Implements Microsegmentation: Manages zero-trust access
- Remote Monitoring: User satisfaction tracking
- Access Rights Management: Integrates with Active Directory
Why do we recommend it?
Microsoft Intune enables the management of desktops and mobile devices through one console. This package is resident on the Azure platform, so it can be accessed through a Web browser and manage devices on multiple sites. The computers of remote workers and the mobile devices of roaming staff can easily be included in the management system.
Intune does a great job of highlighting key insights and features on the interface side but still requires some invested time to learn where everything is. However, like Workspace One, the platform has a refined mobile app that brings the same level of detail from web access to your phone.
The platform utilizes zero trust security controls, which make it a highly secure environment by default. This can lead to more time spent configuring security policies, but it is pretty worth enhancing security. Intune uses continuous monitoring to assess each authentication attempt and analyze its risk assessment. Depending on the risk, you can choose to enforce step-up authentication or disable the account altogether. If you’re using Microsoft Azure, you’ll be able to natively integrate your authentication and identity management into the Intune platform.
Endpoint agents can monitor for unpatched systems, identify vulnerabilities, and alert to present threats. Data monitoring can also be set on mobile and desktop devices to monitor and restrict data flow from trusted zones to other locations.
An exciting feature in Intune is user satisfaction analytics. This measures user experience across your endpoint management software and can compare it to the baseline of similar companies in your industry. I can see MSPs and large enterprises using these metrics to improve performance and reduce the friction between device management and staff productivity.
Intune wouldn’t be my first choice for endpoint management software. Still, it is certainly worth a mention, especially if you’re already integrated into Microsoft products like Azure AD or Windows Autopilot.
Who is it recommended for?
The Intune system is a great option for businesses that operate a virtual office with workers who are geographically dispersed. Companies that implement a BYOD policy or manage a fleet of mobile devices would also be interested in this package. Integration with AD for access management is another big plus.
Pros:
- Good for Windows: Smooth integrations into supporting Microsoft products
- Remote Management: Easily configure patch and update settings
- Scales Well: Can support thousands of devices
Cons:
- Not Suitable for Linux Environments: Very focused on Windows products
Microsoft Intune is a service on the Azure platform and you can assess it with a one-month free trial.
11. Ivanti Unified Endpoint Manager
Ivanti Unified Endpoint Manager provides total visibility, patch management, and software distribution in a single platform. Ivanti offers two versions of their product, Endpoint Manager and Ivanti UEM. Endpoint manager offers options like remote control, patch management, software deployments, and provisioning. UEM extends those capabilities by adding data normalization, GPO replacement, user profile migrations, and extended asset discovery.
Key Features:
- Flexible Platform: Assemble your ideal package
- Mobile Device Management: Can manage BYOD as well as fleet devices
- System-Wide Scanning: Automatic inventory creation
Why do we recommend it?
Ivanti Unified Endpoint Manager provides software and OS management for desktops and mobile devices. This is a flexible cloud platform that provides modules that you select and slot together. This package has routines for managing corporate facilities on user-owned devices and different procedures for protecting fleet devices.
Visually the admin console is simple to navigate and offers customizable dashboards for daily reports and real-time insights. In addition, Ivanti seems to take a more minimalist approach on the dashboard monitoring end, which helps keep metrics clean and uncluttered.
Many parts of the Ivani UEM are modular, allowing you to add the feature you intend to use. This approach provides a feature-rich platform without overwhelming new users with options they’ll never use. In addition, the platform uses endpoint agents dubbed “Ivanti Neurons” to help automate deployments, detect endpoint problems, and personalize user workspaces.
Users can opt for their devices to be enrolled as a managed device on the mobile end, allowing you to implement a BYOD policy alongside managing your corporate devices. Additionally, the platform will enable you to manage iOS, Android, Windows, and Mac OS devices through numerous customizable policies.
From an end-user perspective, authentication is easy and provides a consistent way to log in to devices and services. Additionally, this design choice creates a shared experience across all devices that helps cut down on helpdesk tickets and makes getting to work less of a chore.
Devices that are lost or stolen can quickly be protected through the device security tab. Administrators can identify the lost device by name or last logged-in user and disable access in a few clicks. Additionally, users and devices can all be searched and filtered for in different ways, which is a nice feature, especially when you don’t have all the information you need to track down an asset.
Who is it recommended for?
Although this is a flexible and scaleable system, it is more appropriate for use by mid-sized and large organizations. Small businesses would probably find the systems utilities are a little more than they need. The ability to manage user-owned and fleet devices in different ways within one console is a big plus.
Pros:
- Endpoint Provisioning: Create a software profile
- A Wide Range of Customization Options: Provides the software integration feature
- Role Profiles: Set up an endpoint with a package of configurations, facilities, and software
Cons:
- Pricing Can be Complex: Requires calculations to total up the cost of all chosen features
Ivanti’s flexibility and experience working in the Fortune 100 space make it a solid choice for global enterprises looking to expand their endpoint management software. However, with that said, pricing for Ivanti can become excessive when add-ons are introduced and drive a wedge between their product and smaller enterprise organizations.
Are you currently managing your endpoints? If so, let us know what tools you’ve used, and consider checking out a free trial of any of our top choices.
Endpoint Management Software FAQs
What is endpoint management software?
Endpoint management can be expressed in a range of terms. The task is an asset management process because you need to meet the demand for hardware and software in a business by providing those assets, watching over their statuses, keeping them operational, and planning their retirement and replacement. This can also be expressed as monitoring and management – if multiple sites are being managed from one central location, then it is remote monitoring and management.
What is unified endpoint management solution?
Unified endpoint management (UEM) breaks down the silos between office computer management and the management of mobile fleets. The addition of mobile devices to the endpoint management system also opens up the possibility of BYOD management to support user-owned devices within the company network.
Is UEM same as MDM?
UEM includes MDM. Mobile device management (MDM) is part of the tasks needed to fully manage all of a business’s IT assets, the other part that you need to cover is endpoint management, which manages office-based IT assets. Unified endpoint management combines endpoint management and mobile device management. As well as centralizing the control of hardware for a business, this strategy also permits the creation of a toolset of software that can be provided to workers across devices.













