Identity management sits at the core of modern cybersecurity strategy, ensuring that access to systems, applications, and data is granted only to verified and authorised users.
Here is our list of the best ID Management software:
- Rippling IT EDITOR’S CHOICE A comprehensive Identity and Access Management (IAM) platform that acts as the single source of truth for user access. It uses zero-trust protocols for security and automates onboarding and offboarding processes. Start a 14-day free trial.
- ManageEngine ADManager Plus (FREE TRIAL) An on-premises package that unifies the management of multiple AD implementations across applications, such as Microsoft 365 and Skype. Runs on Windows Server. Start a 30-day free trial.
- ManageEngine ADAudit Plus (FREE TRIAL) A data protection package that relates user activity to Active Directory records, providing behavior logging and compliance reporting. Installs on Windows Server. Start a 30-day free trial.
- LastPass A cloud-based password manager for teams that includes an online password vault.
- SolarWinds Access Rights Manager An interface to Active Directory that runs on Windows Server. Perfect for Sysadmins for customizing access rights and control in Windows and other applications.
- N-able Passportal A cloud-based service that combines password management with a document manager.
- CyberArk Privileged Access Security Consolidates and manages access rights and monitors access events.
- Passbolt An open-source password management system that is free for installation or available as a paid cloud service.
- Zoho Vault A cloud-based password manager that provides centralized control for existing local access rights managers.
As organisations expand their digital operations and adopt more cloud-based services, managing identities has become increasingly complex. Identity management software is used to strengthen security by controlling access permissions, protecting user credentials, and automating authentication workflows across multiple systems.
These platforms are essential for enforcing consistent access policies and reducing security gaps across an organisation’s infrastructure. Rather than relying on manual processes, they streamline identity-related tasks and help ensure secure access control at scale. Common capabilities include single sign-on (SSO), multi-factor authentication (MFA), automated user provisioning and deprovisioning, access governance, and identity synchronisation across applications.
Without strong identity controls, organisations face heightened risks such as data breaches, account compromise, and unauthorised access to sensitive systems. As attack methods become more advanced, maintaining strict and reliable identity verification processes is a key part of reducing overall security exposure.
In this guide, we will explore some of the best identity management software options available today. These solutions provide organizations with advanced features and capabilities to manage identities securely, ensure compliance, and enhance user experience. The right identity management software can significantly improve your organization’s overall security posture and simplify user access management.
Data breaches now don’t just damage a company’s reputation and cause it to lose its customers, but it lays the business open to crippling fines and expensive litigation. Fortunately, a number of IT infrastructure management tool providers have developed some very comprehensive identity management solutions and this guide lists the best of them.
The best identity management tools
Our methodology for selecting identity management systems
We reviewed the market for identity management packages and analyzed the options based on the following criteria:
- Auditing for Active Directory and other access rights management systems
- Recommendations to improve access controls through more granular user accounts
- User group management
- Failed login recording
- Insider threat detection
- A free trial or a demo system that creates an opportunity to test the package before buying
- Value for money from an identity management package that is offered at a reasonable price with respect to the utilities that it provides
You can read more about each of these solutions in the following sections.
1. Rippling IT (FREE TRIAL)
Rippling IT combines HR and IT systems to implement access controls through user identities. Essentially, every user’s identity is linked to the role within the organization. Accordingly, users can access only those apps and systems that are required for that role. This reduces the hassle of provisioning and deprovisioning, maintaining manual audit trails, and reducing unauthorized access.
Key Features:
- Centralized identity management.
- Prebuilt integrations with 600+ apps.
- Syncs devices and federated passwords.
- Supports custom alerts and automations.
Why do we recommend it?
We recommend Rippling IT because all user access can be managed through a single console. Besides keeping the process centralized, it also offers complete control to administrators over which users have access to what resources. This visibility reduces the chances of unauthorized access and insider threats.
Additionally, we like the focus on user experience. With just a few clicks, administrators can provision or deprovision access. This automation of user lifecycle management improves employee productivity without compromising on user experience. It also syncs devices and integrates with 600+ apps.
Who is it recommended for?
Rippling IT is well-suited for enterprises that want to use single sign-on to streamline and control access to apps and resources. This platform can also come in handy for organizations that have strict compliance requirements, especially SOC 2 compliance.
Pros:
- Easy to Use: Comes with an intuitive interface for easy IAM.
- Automation: Offers many workflows and automation to reduce manual effort.
- MFA: Helps implement multi-factor authentication through YubiKey, DUO, biometrics, or OTP.
- Wi-Fi/ VPN: Allows users to log into Wi-Fi and VPN using SSO.
Cons:
- Setup Complexity: Maybe complex to set up for some users.
Rippling’s price depends on your specific requirements. Start a 14-day free trial.
EDITOR'S CHOICE
Rippling IT is the editor’s choice for the best identity management software because of its comprehensive features and ease of use. With a few clicks, administrators can grant or revoke access to apps and resources based on the users’ roles and responsibilities. At the same time, it offers in-depth visibility into the access process.
What stood out for us is its Single Sign-On capabilities. With this single login, employees can access relevant resources, log into their Wi-Fi and VPN, use the appropriate SSH keys, access LDAP-based applications, and more. This results in improved user experience and productivity. These features help with compliance and audit. Due to these features, Rippling IT is our top pick for identity management software.
Download: 14-day FREE Trial
Official Site: https://www.rippling.com/paid-it-trial
OS: Apple and Windows
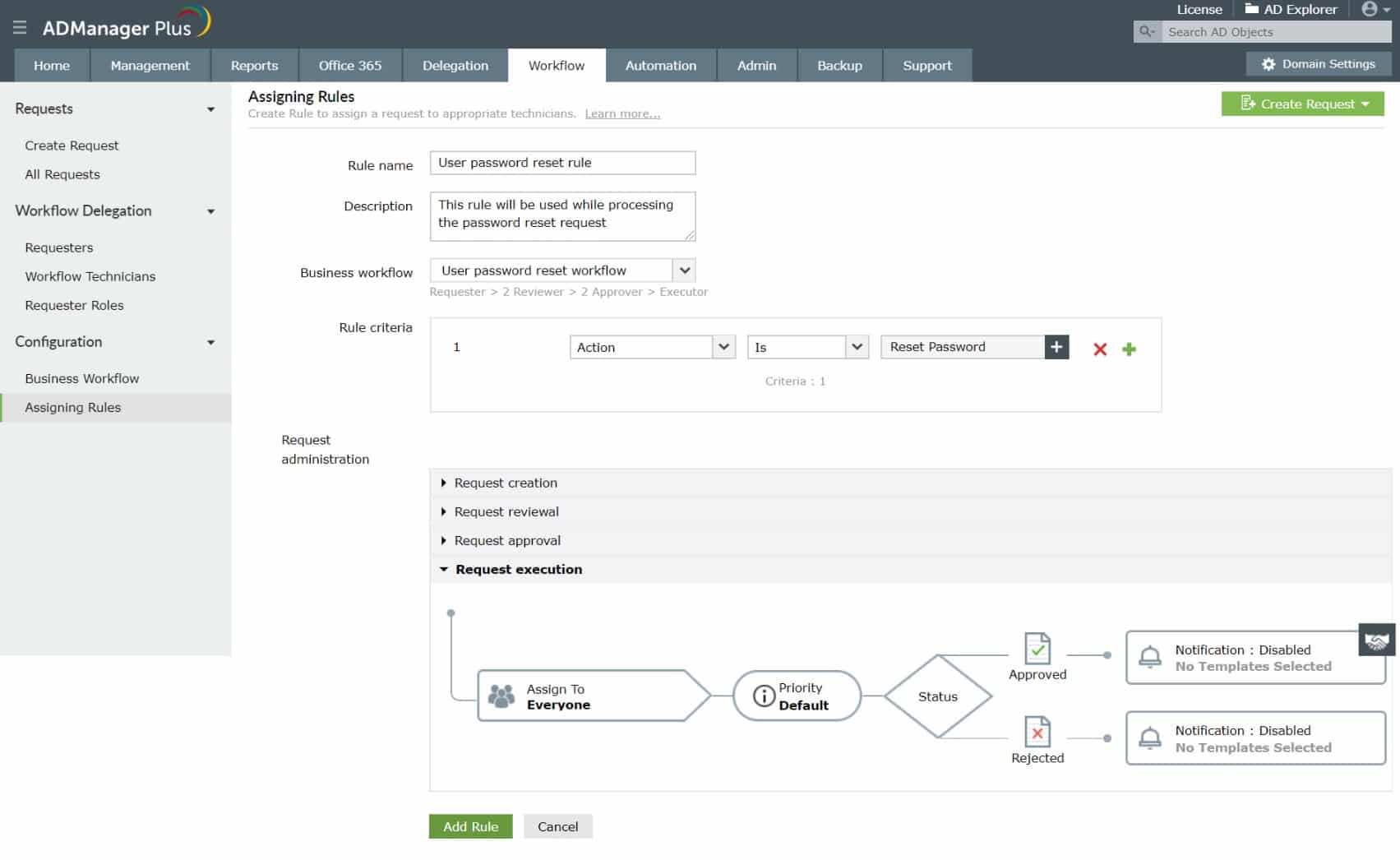
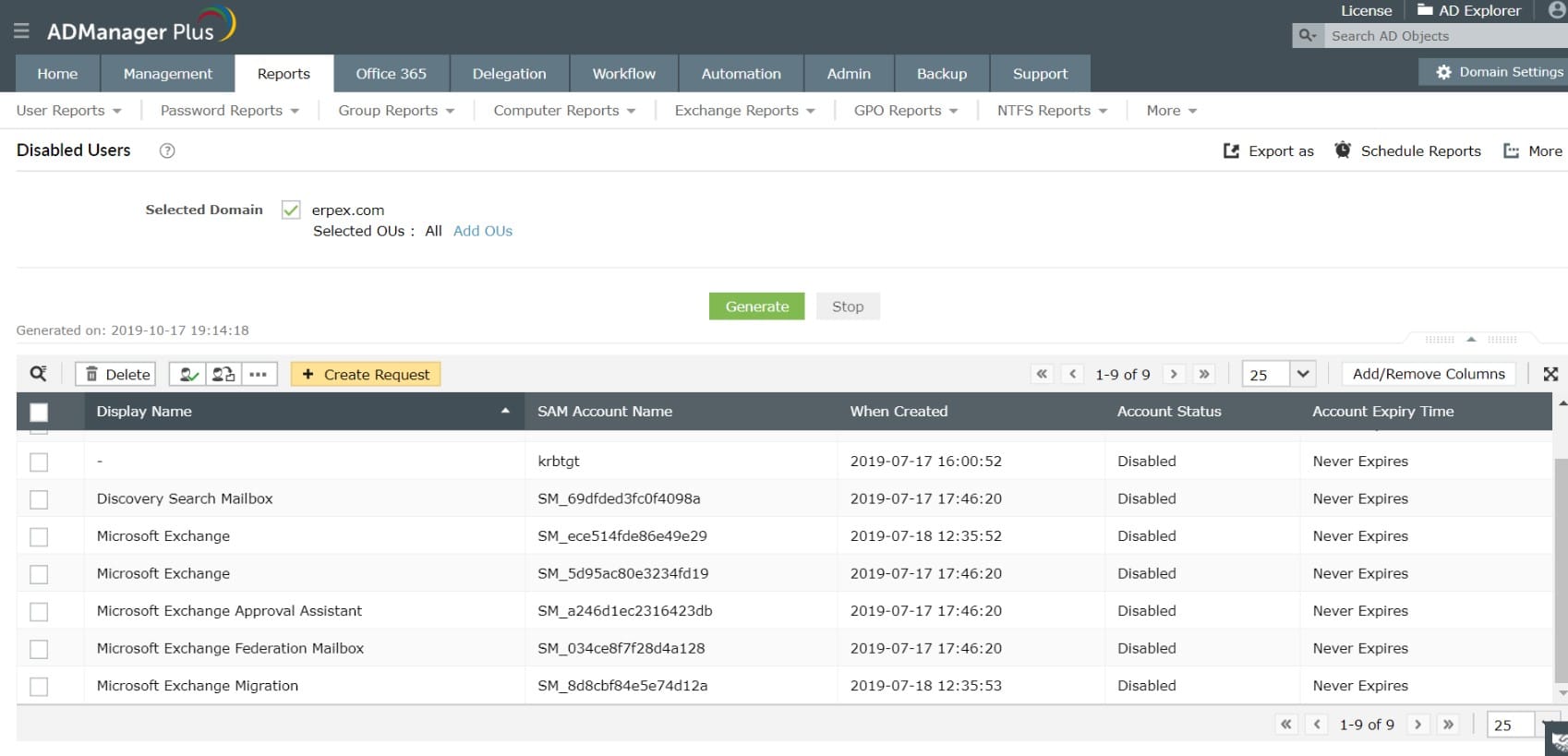
2. ManageEngine ADManager Plus (FREE TRIAL)
ManageEngine ADManager Plus provides a single console to manage multiple AD instances. These controlled AD systems can run access for your network and servers, for your NTFS storage, for Microsoft 365, Google Workspace, and Skype.
Key Features:
- Audits Active Directory
- Scans for abandoned accounts
- Coordinates AD instances
- Bulk account management
Why do we recommend it?
ManageEngine ADManager Plus is a coordinator of resource permissions and user accounts for Active Directory on-premises, Azure AD, Microsoft 365, and Google Workspace. The package lets you replicate accounts across all of your AD-based systems and provides bulk administration services. The tool can also be used to analyze accounts to tighten security.
Once you have ADManager Plus running, you don’t need to visit each AD instance. Instead, the ADManager Plus package does that for you. Every change you make in the Active Directory user accounts and device permissions in the ADManager Plus console gets rippled through to the actual underlying AD instances.
System management features in ADManager Plus save you time by implementing task automation. The service will scan all user accounts to detect abandoned accounts, enabling you to clear out dead accounts, which present a security weakness. You can also set up a password policy through the console, which will flow through to all instances.
The administrator tools in ADManager Plus include the ability to upload accounts in bulk. You can also create accounts en masse through the use of templates. The guided system will help you coordinate between accounts and user groups and then insert those objects into all of your AD implementations.
Who is it recommended for?
This system is available in three editions that suit all sizes of businesses. There is a Free edition that caters to small businesses and will manage 100 AD objects. The two paid versions are suitable for mid-sized and large organizations. The software package installs on Windows Server or you can run it on AWS or Azure in the cloud.
Pros:
- Bulk import, creation, adjustment, and deletion for user accounts
- Password policy implementation
- Centralized control of multiple AD instances
Cons:
- No hosted cloud version
There are three editions of ADManager Plus: Free, Standard, and Professional. The free version is limited to managing 100 AD objects. The software for ADManager Plus runs on Windows Server. Although ManageEngine doesn’t offer this system on its own cloud platform, ADManager Plus is available on the AWS Marketplace and the Azure Marketplace. You can get a 30-day free trial of either the Standard or Professional edition of ManageEngine ADManager Plus.
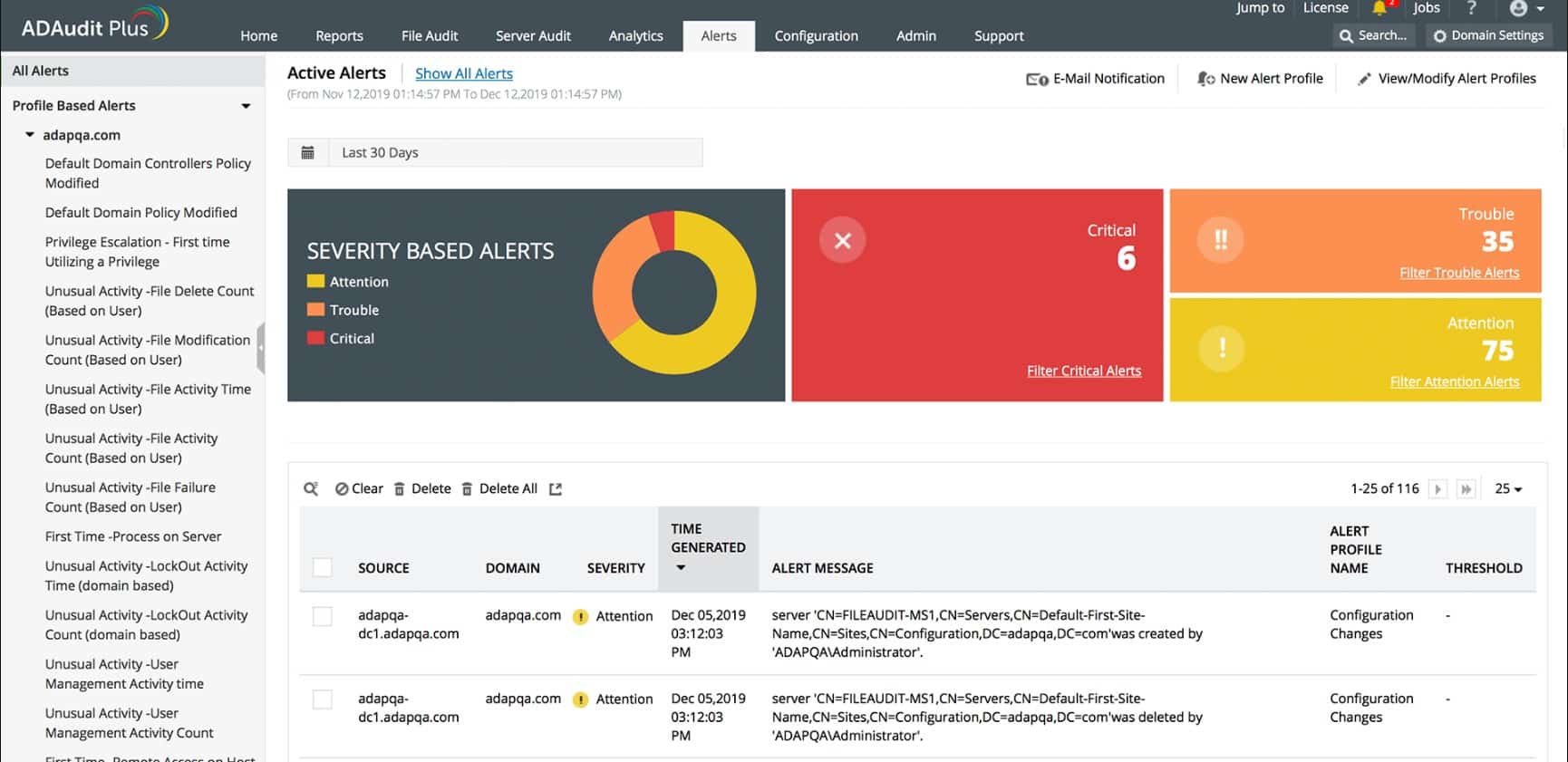
3. ManageEngine ADAudit Plus (FREE TRIAL)
ManageEngine ADAudit Plus is a data protection system that operates by recording each user account in Active Directory and then logging each action performed by each of those accounts. Therefore, this isn’t a system for auditing Active Directory, it is a system activity auditing service that is based on AD data.
Key Features:
- Tracks user activity
- File integrity monitoring
- Access controls on files
Why do we recommend it?
ManageEngine ADAudit Plus is a user behavior tracker that implements insider threat detection. As the whole system relies on Active Directory for user identification, the protection of AD domains is part of the package. The tool logs all changes made to objects in AD, identifying the user involved and enabling those changes to be reversed.
The main reason any company would use the ADAudit software is to enforce data privacy and implement a data security standard. This tool can enforce requirements and produce compliance reporting for GDPR, HIPAA, PCI DSS, GLBA, and SOX, among other standards.
The system is particularly concerned with the activities of users in relation to sensitive data. In order to effectively protect data, the package includes USB controls to prevent data copying and file integrity monitoring.
By employing user behavior analytics (UBA) the ADAudit Plus service protects against account takeover and insider threats. The package also protects Active Directory structures from unauthorized changes and blocks tampering with its own log files.
In addition to activity tracking, the ADAudit Plus system provides compliance reporting through a series of templates. The whole service will automatically adapt to the data privacy standard that you specify in the system settings.
Who is it recommended for?
This package is suitable for mid-sized and large organizations. A small business would probably be able to make human assessments of each user rather than relying on automated processes. Larger businesses can’t keep track of all of the users on the system and so need user activity tracking.
Pros:
- Behavior tracking and alerts for suspicious activity
- Data privacy controls and compliance reporting
- Tampering protection for AD instances and log files
Cons:
- No hosted cloud package
ManageEngine ADAudit Plus is an on-premises package that runs on Windows Server. You can also access it as a cloud-based service on the AWS and Azure platforms through their Marketplaces. The tool is offered in three editions: Free, Standard, and Professional. The Free system is free forever but is limited to monitoring 25 workstations. You can assess ADAudit Plus with a 30-day free trial.
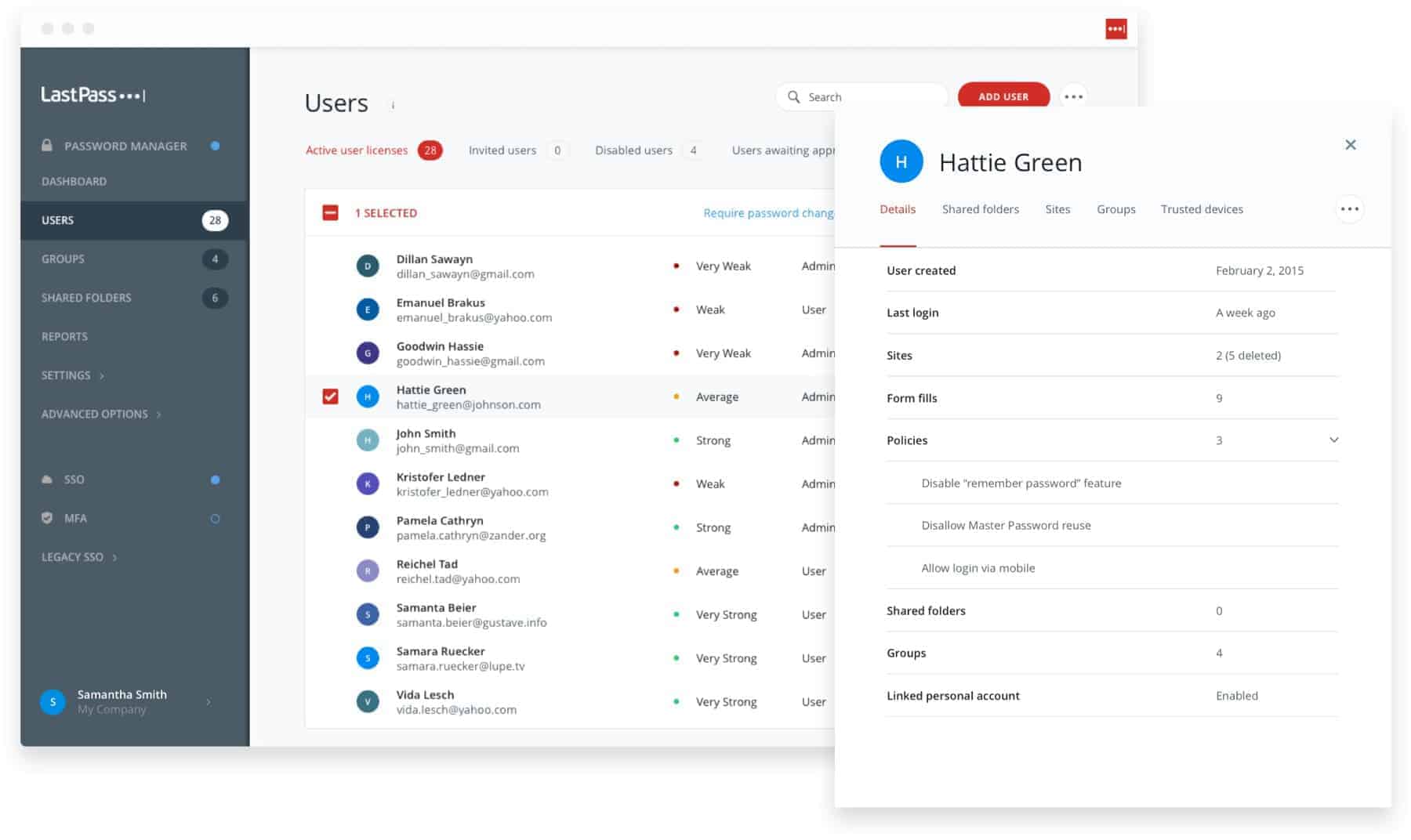
4. LastPass Enterprise
LastPass for businesses is available in four editions: Teams, Enterprise, MFA, and Identity. Of these, Enterprise is probably the best option for most businesses seeking an identity management solution. The only difference between the Enterprise and Identity plans lies in the multi-factor authentication methods available. The Enterprise system uses SMS and/or biometric methods, which are sufficiently comprehensive for most businesses.
Key Features:
- Distributed system
- Multi-factor authentication
- Password policy enforcement
Why do we recommend it?
LastPass Enterprise is a credentials locker. The tool centralizes the credentials for a team or for an entire organization and it will distribute those credentials without the user being able to see the password. This solves the problem of maintaining system security if a user leaves and reduces the risk of a rogue employee or technician stealing data or altering records.
The Enterprise service takes the role of a central controller that first scrapes access rights records from existing permissions systems then becomes the main point of access for the systems administrator. Changes made in the LastPass console get rolled out automatically to those local controllers.
LastPass will enforce password policies, including password rotation and complexity expectations. It is able to manage passwords and access rights at both the individual level and as groups. Onboarding can be automated and it enables a single-sign-on system to be implemented. Each user gets access to a personal password vault and can set the system to autofill password fields.
Who is it recommended for?
This package is a useful tool for all types of businesses. However, it is particularly important for technician teams that have privileged access. Three plans, of which, Enterprise is the highest, help this tool appeal to different sizes of businesses. Per-user pricing provides a scaleable subscription rate.
Pros:
- Sleek front end and admin console
- Tracks logins and login attempts through auditing features
- Supports safe password sharing and individual protected folders
- Access passwords from anywhere through secure cloud storage
Cons:
- Would like to see a longer trial period
This is a cloud-based service and charges are made by subscription, levied per user per month. You can learn more about the LastPass Enterprise by accessing it on a 14-day free trial.
5. SolarWinds Access Rights Manager
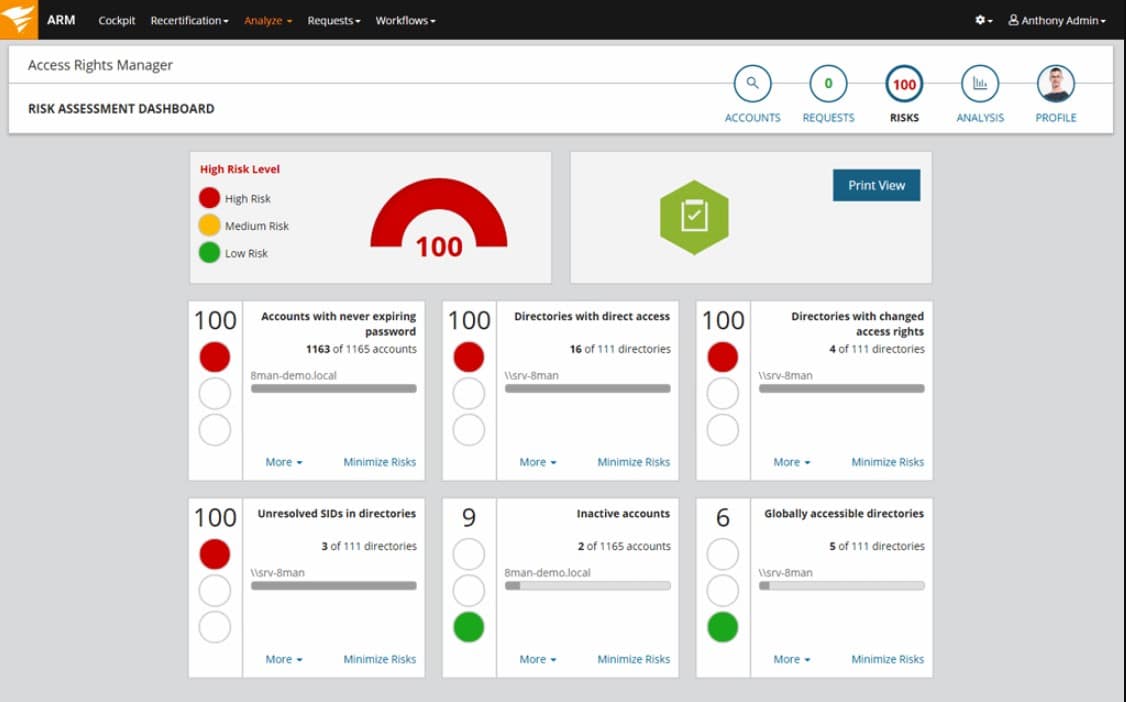
SolarWinds Access Rights Manager is an on-premises identity management solution that installs on Windows Server. It covers all Active Directory implementations, helping you to manage access rights and passwords for networks, devices, Microsoft Exchange, Windows File Share, and SharePoint.
Key Features:
- Manages multiple DCs
- Account remapping
- Identifies abandoned accounts
- Assists with replication
- Self-service password portal
Why do we recommend it?
SolarWinds Access Rights Manager is an on-premises software package that provides a frontend for Active Directory. The system is a replacement console for AD and you can manage several domains in that one dashboard. The tool enables administrators to analyze accounts, perform bulk actions, and replicate domains.
This tool contains automation processes through workflows. These will batch together the tasks you normally perform when onboarding a new user. It will also track group profiles and memberships and display relationships and inheritance in its dashboard.
A useful feature in the package is a self-service portal that enables existing users to manage their own passwords and solve access problems. All of the features are aimed at eliminating a lot of the routine work that fills the days of time-pressed systems administrators.

This permissions management system also includes analysis functions. The Manager includes auditing features and report formats that support the proof of data security standards compliance. The analysis and reporting utilities will also help you to improve your access rights policies and support the implementation of system refinements.
Who is it recommended for?
This is a solution for large organizations that have many AD domains. The service enables coordination between domains. It can manage on-premises Active Directory, Azure AD, and Microsoft 365 components, plus the on-premises version of Microsoft Exchange Server. The package can also be used for user behavior analytics for insider threat detection.
Pros:
- Provides a clear look into permission and file structures through automatic mapping and visualizations
- Preconfigured reports make it easy to demonstrate compliance
- Any compliance issues are outlined after the scan and paired with remediation actions
- Sysadmins can customize access rights and control in Windows and other applications
Cons:
- Access Rights Manager is an in-depth platform designed for sysadmin which may take time to fully learn
SolarWinds Access Rights Manager is available for a 30-day free trial.
See also: Best Access Rights Management Software
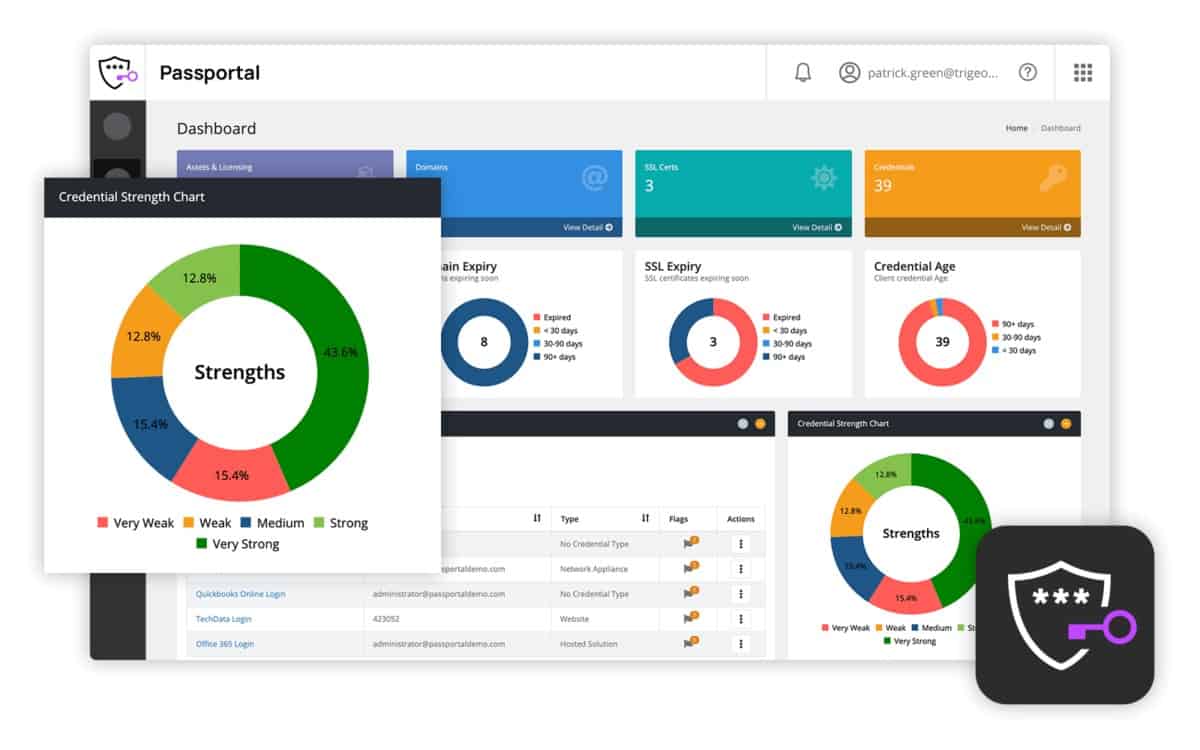
6. N-able Passportal
Passportal is a cloud-based subscription service aimed at managed service providers (MSPs). The base package includes a password manager and a document management system.
Key Features:
- Password storage
- Secure password distribution
- Designed for MSPs
Why do we recommend it?
N-able Passportal is a vault that will hold credentials, keys, and other sensitive information that needs to be protected. This system will distribute passwords unseen by users, so no one can learn what they are. The package is designed to support technician teams and transmission security means that one account can support teams in different locations.
The password manager in Passportal provides a centralized console for all of your access rights managers on-site or in the cloud. However, it is only able to interact with Microsoft-produced access rights systems. It will act as a controller for Active Directory implementations, covering networks, endpoint and server access, file systems, email and web server implementations. It will also manage Azure and Office 365 access rights managers.
The tool searches a client’s system to discover all AD-controlled systems. It then extracts records from the local Active Directory instances and runs password management from that point on. Any changes made in Passportal get updated in the relevant AD instance automatically.
Passportal will enforce safe password policies such as password rotation and password complexity requirements. It includes a password vault that is segmented per user and it will autofill password fields for the users.
Who is it recommended for?
N-able produces tools for managed service providers, so MSPs would be the most likely buyers of this system. The tool can segment its vault so that the passwords for access to the systems of different clients are kept separate. However, IT departments would also find this package useful for in-house password confidentiality.
Pros:
- Supports automatic Active Directory sync via LDAP
- Can run access audits to easily identify internal changes made during a period of time
- Supports compliance reporting to identify weak passwords and force changes base on policy
- Users generate their own encryption key, securing their cloud data from third parties, including Passportal
Cons:
- Smaller networks may not benefit from the MSP/enterprise-specific tools Passportal offers
The Passportal service is charged for on a subscription basis. There is no contract requirement and fees are invoiced month-to-month. You can access a demo system of Passportal for assessment.
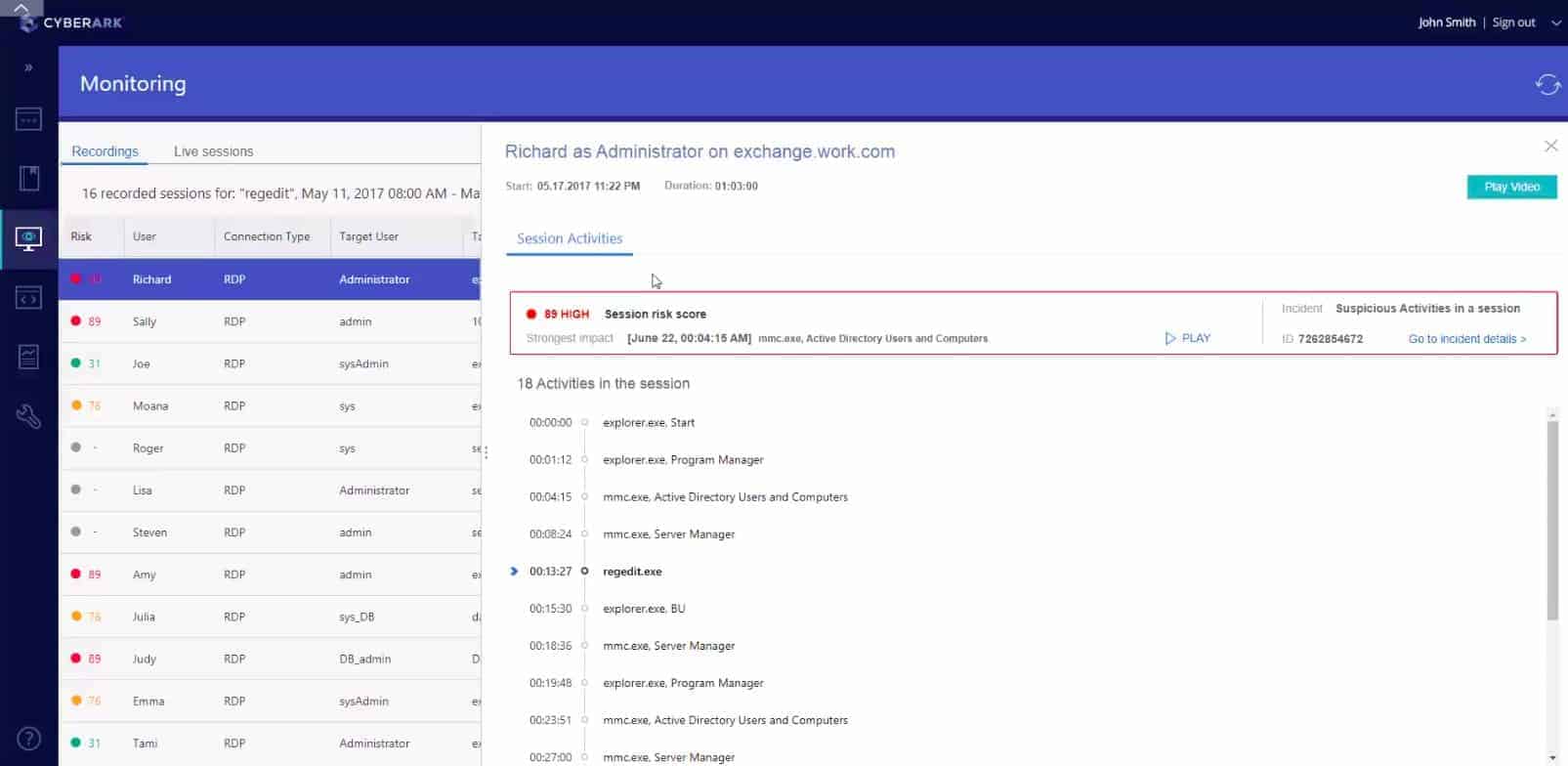
7. CyberArk Core Privileged Access Security
The software house CyberArk specializes in a range of system security measures and its Core Privileged Access Security system (PAS) is a package of its top sellers. The modules in this bundle are Enterprise Password Vault, Privileged Session Manager, and Privileged Threat Analytics. The system is available as on-premises or as a cloud service.
Key Features:
- Manages privileged accounts
- Automated ARM assembly
- Password vault
Why do we recommend it?
While many of the identity management software systems on this list enhance the security and management of Active Directory, CyberArk Core Privileged Access Security replaces AD. So, businesses who use this system won’t need any other IAM active on their site. The tool is aimed at managing access credentials used by technicians.
The PAS system starts off with an autodiscovery scan, locating all resources that require access management and identifying current users with access. This information is drawn into a standardized central database, which is protected by encryption. From that point on, the PAS dashboard becomes the management console for all access and password issues in the monitored enterprise.
The administrator sets up the system by entering the company password policies, activating utilities such as enforced password rotation and password strength requirements. Once these policies are in place, PAS will apply those standards automatically to the password creation screens for users. The audit features of the suite are perfect for data security standards compliance and a risk assessment module enables system managers to improve security procedures.
Who is it recommended for?
This system simplifies access rights management because you don’t need to juggle credential management through two ARMs. The service provides an access portal, which creates a double layer of system security because it directly blocks users from even getting to the login screens for the assets to which they do not have access rights.
Pros:
- Can manage access rights and alert to improper access by privileged users
- Autodiscovery quickly discovers resources to monitor
- Makes it easy to create and enforce custom credential polices
- Available as a SaaS or on-premise solution
Cons:
- Would like to see a full trial rather than a demo
- Pricing isn’t publically available, must contact their sales team
CyberArk Core Privileged Access Security is available in Standard and Advanced editions. The higher plan includes extra security procedures to protect servers and additional attack vector scanning. The system is available as on-premises software, as a self-hosted cloud system, or delivered as Software-as-a-Service from the CyberArk servers. The on-premises version installs on Windows Server. You can request a demo of the CyberArk suite.
8. Passbolt
Passbolt is an open-source software package that can be used for free on-premises. The software installs on Debian and CentOS Linux. It can be run on Windows on a virtualization platform. This password management system allows the organization, creation, alteration, and deletion of access rights at both individual and group levels. The creation of shared passwords is also possible.
Key Features:
- Manages Active Directory and LDAP
- Open source
- Disaster recovery
Why do we recommend it?
Passbolt is an independent access rights manager and it doesn’t rely on Active Directory for underlying access management services. This package operates a central password vault for technician access. Passwords are distributed without the user seeing them. The tool can manage general user accounts, not just privileged access.
The free version of the Passbolt is called Community. This is a standalone password manager and there is no professional support for it, though you can consult the extensive user community through a forum. There are two paid versions that are professionally supported. These versions are Business and Enterprise.
The Business edition is able to communicate with other access rights systems based on OpenLDAP and Active Directory. This edition includes a system auditing module, which is necessary for data security standards compliance. This version is also capable of implementing multi-factor authentication. The main feature of the Enterprise edition is that it can be customized by the development team behind Passbolt. It also includes the extra feature of disaster recovery procedures.
Who is it recommended for?
The Passbolt system is available in a free Community Edition, which is a good option for small businesses. The two paid editions are priced in packages of user accounts that increase in steps of 10. Those paid systems also implement single sign-on and offer a user access portal.
Pros:
- Free for on-premise installations
- Integrates with Active Directory via LDAP
- Great interface, includes a dark mode for long-term use
- Supports multi-factor authentication options
Cons:
- Would benefit from a longer 30-day trial
Passbolt Business edition is charged for on a subscription basis. The base price includes the management of five users and each extra user after that increases the price. As it is a bespoke package, the Enterprise version does not have a fixed price list. Passbolt Cloud is the Software-as-a-Service version of the password manager. It is available for a 14-day free trial.
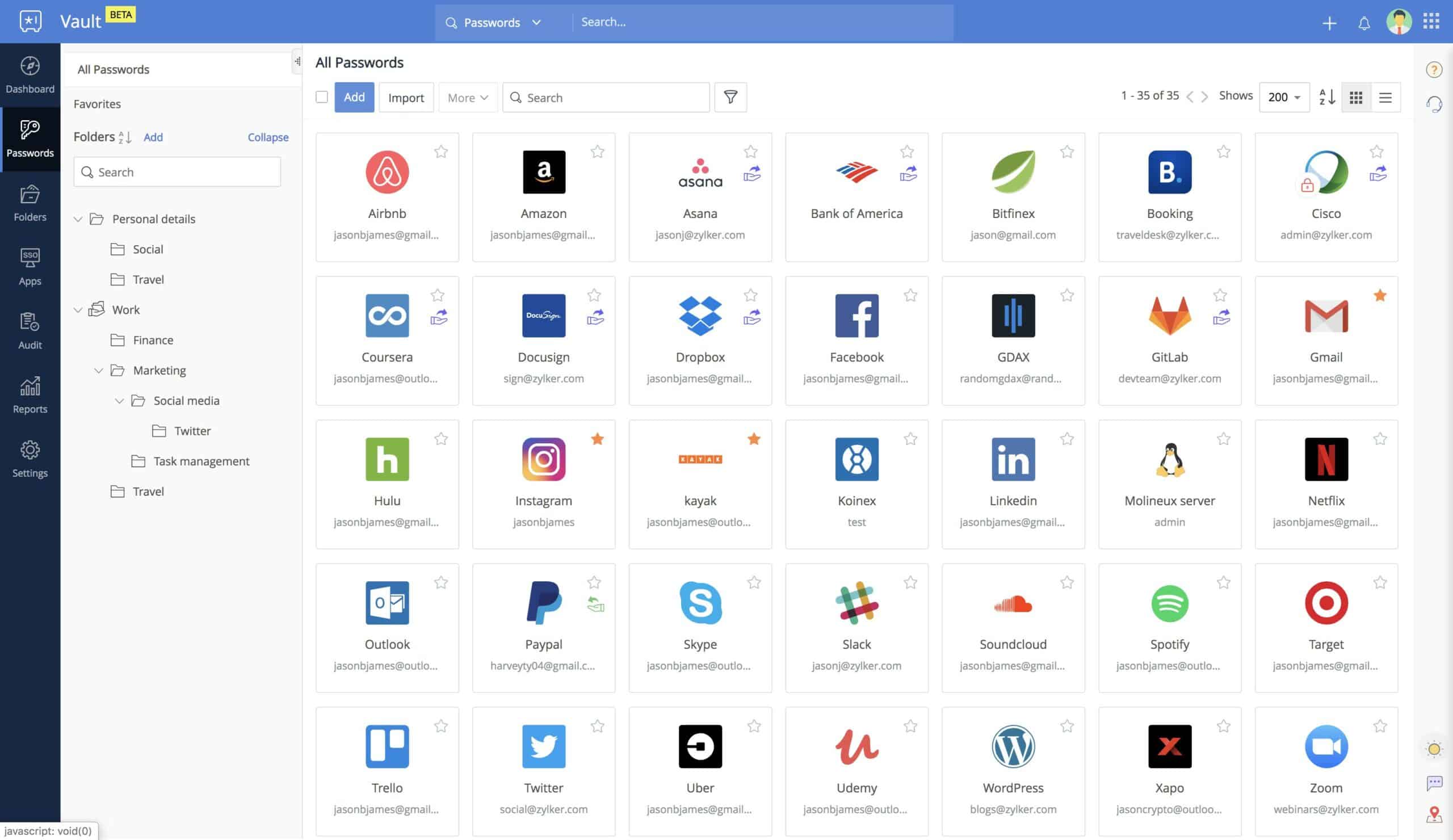
9. Zoho Vault
Zoho Vault is a cloud-based service that manages passwords for teams. The central element of the service is a secure encrypted password vault that is hosted on Zoho servers and protected by a 256-bit AES cipher. The console for the service acts as a central controller for on-premises or cloud-based access rights managers that already guard your systems. These include such as Active Directory, Office 365, Azure AD, and Google Cloud Platform.
Key Features:
- Online system
- Manages on-premises and cloud AD
- Fronts for multiple DCs
Why do we recommend it?
Zoho Vault is a cloud-based corporate password locker that can guard individual account credentials for regular access and also shared accounts for privileged access. Higher plans provide sophisticated access management tools, such as website password management and a single sign-on utility.
Once you have Zoho Vault active, you won’t need to visit all of your other access rights managers because changes made in the Zoho Vault system get replicated out to all of your other access control systems. Access rights can be managed by groups as well as by individual users. The password manager extends out to utilities for the users, including password field auto-filling and the ability for shared passwords to be created automatically on demand.
Who is it recommended for?
The four plans of this tool make it appealing to every type of organization. There is a free plan for individual use – that includes 2FA and other sophisticated tools, but it won’t provide the management of shared accounts for privileged access. Paid plans include team access management and are priced per user.
Pros:
- Organizes passwords by service, makes it easy for non-technical users
- Leverages cloud storage for credential access from anywhere
- Access control can be managed by single users or groups, great for larger environments
- Free for personal use
Cons:
- Would benefit from a longer 30-day trial
- Would like the ability to important passwords across multiple browsers
Zoho Vault is free for personal use and there are three paid versions for business: Standard, Professional, and Enterprise. All of these business plans are charged for by subscription with a fee levied per user per month. All paid versions are available for a 15-day free trial, with the site declaring that the Professional edition is the most popular.
Implement identity management
Identity management has become a much bigger field than just setting up user accounts. The multi-vendor environments that are common in modern business environments make access and password management even harder to coordinate.
One of the key features in all of the seven IdM packages in our list is that they enable all of the environment to be managed in a centralized console. That should unify the incompatible operating procedures and record formats implemented by the Windows and Linux standards for access rights controllers and password managers.
Centralizing and coordinating the existing systems will improve activity visibility and simplify working procedures. The unified base of your identity management solution then gives you a platform through which to automate user and resource management and improve security supervision.