A Threat Intelligence Platform (TIP) aims to block repeat attackers and identify common intrusion vectors. This emerging technology is an advance on traditional anti-virus (AV) and firewall systems. A TIP will protect your IT equipment by applying AI-based learning strategies.
A number of replacement technologies have emerged in recent years to improve on the business protection afforded by traditional malware systems.
Anti-malware programs compare the code of new programs running on a computer to a database of previously detected malware signatures.
Here is our list of the best threat intelligence platforms:
- Atera EDITOR’S CHOICE This cloud-based monitoring and management platform includes strong threat intelligence capabilities, along with automated patching and automated endpoint upkeep. Get a 30-day free trial.
- ManageEngine Log360 (FREE TRIAL) Looks for threats in log file data from Windows Server or Linux and adds in threat intelligence from three sources. Start a 30-day free trial.
- ManageEngine Vulnerability Manager Plus (FREE TRIAL) A threat prevention system that looks for a list of known weaknesses in configurations of devices to block the possibility of intruders and malware threats getting in. Runs on Windows Server. Start a 30-day free trial.
- Datadog Threat Intelligence Turn-key threat intelligence feeds that are curated by select threat intelligence partners as a cloud-SIEM. Data feeds are continually updated on suspicious activity as it becomes known and available.
- Trellix Helix Combines a cloud-based SIEM threat detection console, AI learning methods, and a threat intelligence feed.
- N-able Threat Hunting A cloud-based service marketed to MSPs. This is a SIEM tool that enables MSPs to add security monitoring to their list of services.
- Heimdal Threat Hunting and Action Center Provides a private threat intelligence service by collecting activity data from other Heimdal cybersecurity products on site.
- AlienVault USM Anywhere Includes threat detection, incidence response, and threat intelligence sharing.
- LogRhythm NextGen SIEMs Includes the live monitoring of traffic data and the analysis of log file records.
Threat Intelligence Platforms Vs traditional Anti-virus Software
In the traditional anti-malware model, a central research lab investigates new threats to derive patterns that identify them. These malware detection characteristics are then distributed to all of the installed AV programs that the company has sold to clients. The local anti-malware system maintains a threat database that contains this list of attack signatures derived by the central lab.
The AV threat database model is no longer effective at protecting computers. This is because professional teams of hackers now engage in malware production lines with new threats appearing daily. As it takes time for research labs to notice a new virus and then identify its characteristics, the lead time for typical AV solutions is now too long to offer effective business protection.
Spotting a threat
A threat intelligence platform still includes a threat database. However, rather than relying on users reporting strange behavior to the headquarters of the AV producer, new cybersecurity systems aim to contain all of the research and threat remediations on each customer’s equipment. In effect, each TIP installation becomes a composite detection, analysis, and resolution bundle. It is no longer necessary to update the threat database from a central lab because each machine performs the researcher team’s work.
This distributed model of AV data gathering is much more efficient at combatting “zero-day” attacks. The “zero-day ” term refers to new viruses that have not yet been identified by the major AV labs in the world and against which, as yet, there is no effective defense. Each machine does not work alone, however. Information on discovered new threats is shared among the users of a specific brand of TIP.
The TIP uses detection procedures locally while still relying on a threat database, which is contributed by local analysis as well as frequent downloads from the software provider’s labs. Those downloads are derived from the discoveries made by the same TIP that is installed on other sites by other customers.
The best Threat Intelligence Platforms, Tools & Software Vendors
Although each TIP uses a similar set of strategies to detect malicious events, not all TIPs are equally effective. Some security vendors focus on one specific type of device and one specific operating system. They might also provide protection systems for other types of devices and operating systems, but without the same level of success that they achieved with their core product.
It isn’t easy to spot a good TIP and the claims, boasts, and obscure industry jargon used on the promotional websites of their producers makes searching for the right TIP a very tiring exercise.
Our methodology for selecting a threat intelligence platform
We reviewed the market for threat intelligence detection systems and analyzed tools based on the following criteria:
- Machine Learning for a baseline of normal activity
- Anomalous activity detection
- Threat intelligence feeds that adapt detection routines
- Alerts for suspicious activity to attract technicians
- Experience sharing and summaries of industry-wide threat notifications
- A demo or a free trial for a risk-free assessment opportunity
- Good value for money from a comprehensive threat intelligence feed at a fair price
Fortunately, we have done the legwork for you. With these selection criteria in mind, we identified network security services with threat intelligence feeds that we are happy to recommend.
1. Atera (FREE TRIAL)
Atera is a support platform built for managed service providers (MSPs). It is delivered from the cloud, so the MSP does not need to install any software on its premises and even does not need to run any major IT infrastructure. All it needs is a computer with an internet connection and a web browser. The monitored system does need special software installed on it, however. This is an agent program that gathers data and communicates with the Atera servers.
Key Features
- Designed for MSPs: Versions also available for IT departments
- Combines RMM and PSA: System monitoring and management plus a ticketing service
- Monitor Remote Systems: A cloud-based package
- Ticketing System: Automates task handling and team coordination for support operations.
- Endpoint Maintenance: Supports automated and scheduled system cleanup.
Why do we recommend it?
The Atera cloud platform of monitoring and management tools includes an automated patch manager. This scans all endpoints running Windows and macOS and notes the version numbers of all operating systems and software. It then looks at the latest versions available and installs patches to update outdated systems.
Being a remote service, Atera is able to monitor any client facility, including cloud-based AWS and Azure servers. The service includes an autodiscovery process, which logs all of the equipment connected to the network. For endpoints and servers, the monitoring system will scan all software, creating an inventory. This is an essential source of information for software license management and it is also an important threat protection service. Once the software inventory has been compiled, the operator can check what unauthorized software is installed on each device and then delete it.
The server monitor checks on processes as part of its regular tasks and this will highlight malicious software running. The operator is able to access the server remotely and kill unwanted processes.
Atera monitors access rights controllers on the client’s site, including Active Directory. The Live Manager tool in the Atera package gives access to Windows Event logs and provides a searchable source of possible security breaches.
One more threat protection service contained in the Atera package is its patch manager. This automatically updates operating systems and key application software when they become available. This important service ensures that any exploit remedies produced by software providers get installed as quickly as possible.
Who is it recommended for?
Atera is available in versions for IT departments and managed service providers. Both categories include four plans and all eight editions include patch management. The Atera system is cloud-based and it is priced per technician, so it is very scalable, catering to individual support technicians and large corporations alike.
Pros:
- Full Stack Observability: Networks, endpoints, and applications
- Patching and Maintenance Task Automation: Launched through a scheduler
- Subscription Price per User: Not per supported user or device
- Service Automation: Increases technician productivity.
- Remote Access Services: Includes licenses for Splashtop and AnyDesk.
Cons:
- Network Discovery Costs Extra: It isn’t included in any of the plans
Atera is charged for by subscription with the charge rate set per technician. Buyers can choose between a monthly payment plan or a yearly rate. The annual payment period works out cheaper. You can access a 30-day free trial to put Atera through its paces.
EDITOR'S CHOICE
Atera is our top choice for a threat intelligence platform because it brings monitoring, automation, and security management together in a single platform. Built as an all-in-one service for managed service providers, Atera delivers threat intelligence functions that strengthen organizational security. Its capacity to surface threats in real time, track endpoint condition, and automate security actions gives it an advantage over many competing platforms. Atera monitors systems continuously, helping businesses spot unusual behavior before it develops into a more serious security problem. Its use of artificial intelligence-driven automation supports earlier threat detection and faster responses, which helps reduce downtime and improve the efficiency of network operations. With one interface for managing endpoints, servers, and network devices, Atera helps organizations apply security controls and compliance requirements more consistently. The platform also delivers remote monitoring and management features that work closely with its threat intelligence functions. That combination improves both security and day-to-day operations, making it easier for teams to deal with security issues as they arise. Its scalability also makes it suitable for organizations ranging from small businesses to larger enterprises that need stronger network protection.
Download: STart a 30-day FREE Trial
Official Site: https://www.atera.com/signup/
OS: Cloud-based
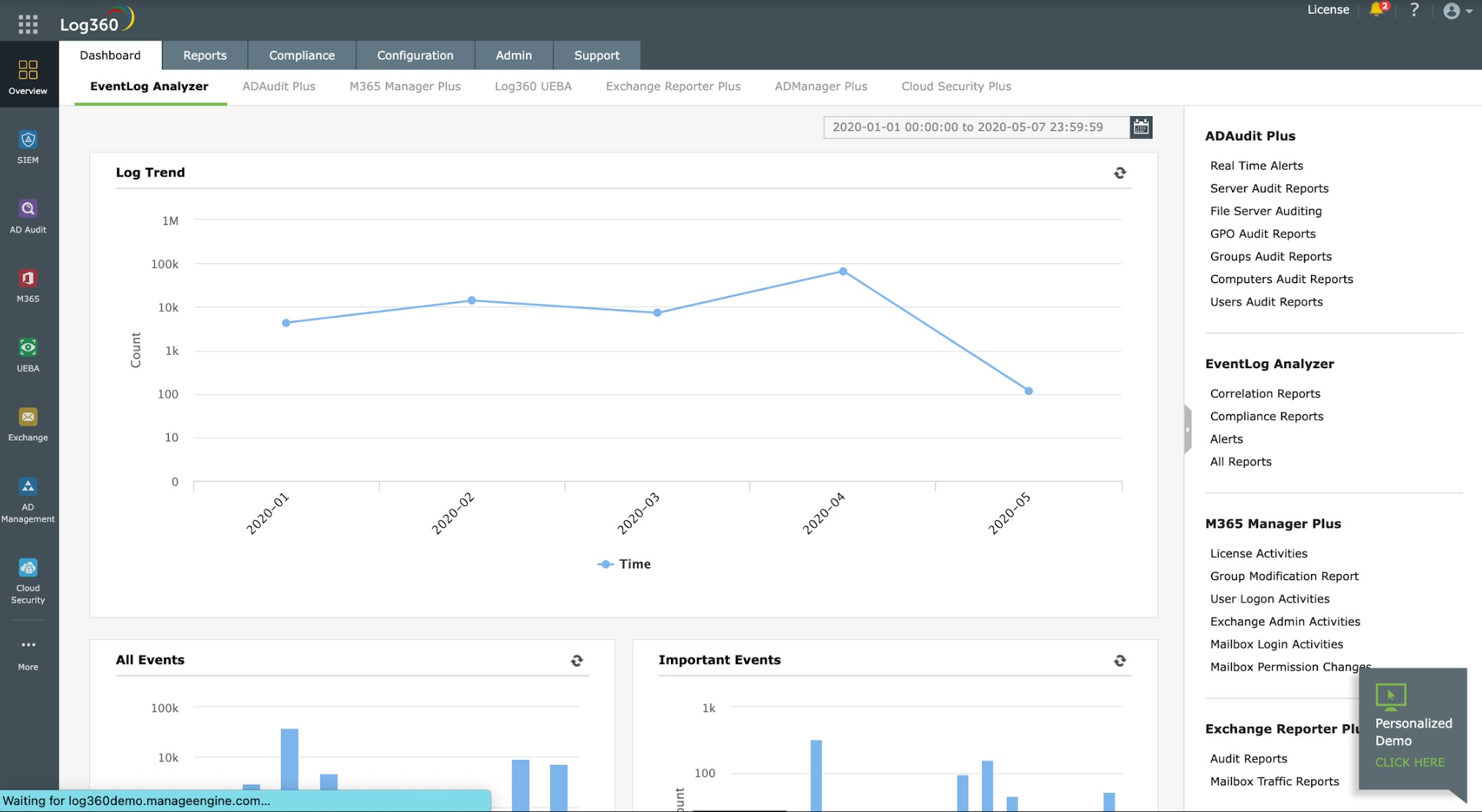
2. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 is a very comprehensive TIP that investigates all possible sources of log data to tighten up system security.
ManageEngine already offers a range of log management and analysis tools. However, the company decided to bundle them into a combined module that covers all possible file-based sources of system information. IT also integrates external sources of information such as STIX/TAXII-based feeds on blacklisted IP addresses.
Key Features
- Includes a Log Server: Log management and analysis
- Takes Threat Intelligence: Receptive to STIX/TAXII threat intelligence feeds
- Protects Active Directory: Hackers frequently target AD to create or hijack user accounts
Why do we recommend it?
ManageEngine Log360 is a bundle of ManageEngine monitoring systems. The threat intelligence core of the tool is supplied by EventLog Analyzer. This is a SIEM and it is informed by a threat intelligence feed. You can subscribe to a third-party threat intelligence feed to improve threat detection.
As well as controlling Event Logs, the tool integrates the information resident in Active Directory. This helps the detection engine of this tool to check on who has the rights to access the resources used in the activities that log messages record. The tool monitors changes in Active Directory to ensure that intruders aren’t able to grant themselves access rights.
The reach of this security tool extends out to the web because it also gathers audit reports from AWS, Azure, and Exchange Online.
You know that Exchange, Azure, Event Logs, and Active Directory are all Microsoft products. However, Log360 isn’t limited to monitoring Windows-based systems. It also gathers log messages raised on Linux and Unix systems, such as Syslog messages. The tool will examine all IIS and Apache Web Server messages and it covers messages generated by Oracle databases.
Your network hardware and perimeter security systems also have important information to share and so Log360 listens for log messages arising at firewalls, routers, and switches. If you have any other intrusion detection and protection systems installed, Log360 will integrate their findings in its threat intelligence summaries.
Log360 doesn’t create logs about logs, which you might end up overlooking. The system creates real-time threat intelligence alerts, so your team gets notified as soon as suspicious activity is detected. In addition to monitoring, the Log360 package regularly audits, summarizes, and reports on the security of your entire IT system.
Who is it recommended for?
This package is very big and it includes a file integrity monitor, user activity tracking, and Active Directory protection. Of course, all of these services bump up the price. It could be that you get a better deal by buying just the EventLog Analyzer and that tool has a Free edition for small businesses.
Pros:
- Great Dashboard Visualizations: Ideal for NOCs and MSPs
- Centralized Threat Hunting: Can integrate multiple threat data streams into the platform
- Cross-Platform Monitoring: Protects Windows, Linux, and Unix systems
Cons:
- On-Premises Software: Runs on Windows Server
You can install Log360 software on Windows and Windows Server. ManageEngine offers a 30-day free trial of the Professional Edition There is a Free Edition that is limited to collecting log data from just five sources. If you have different requirements you can discuss pricing for a package that suits your needs.
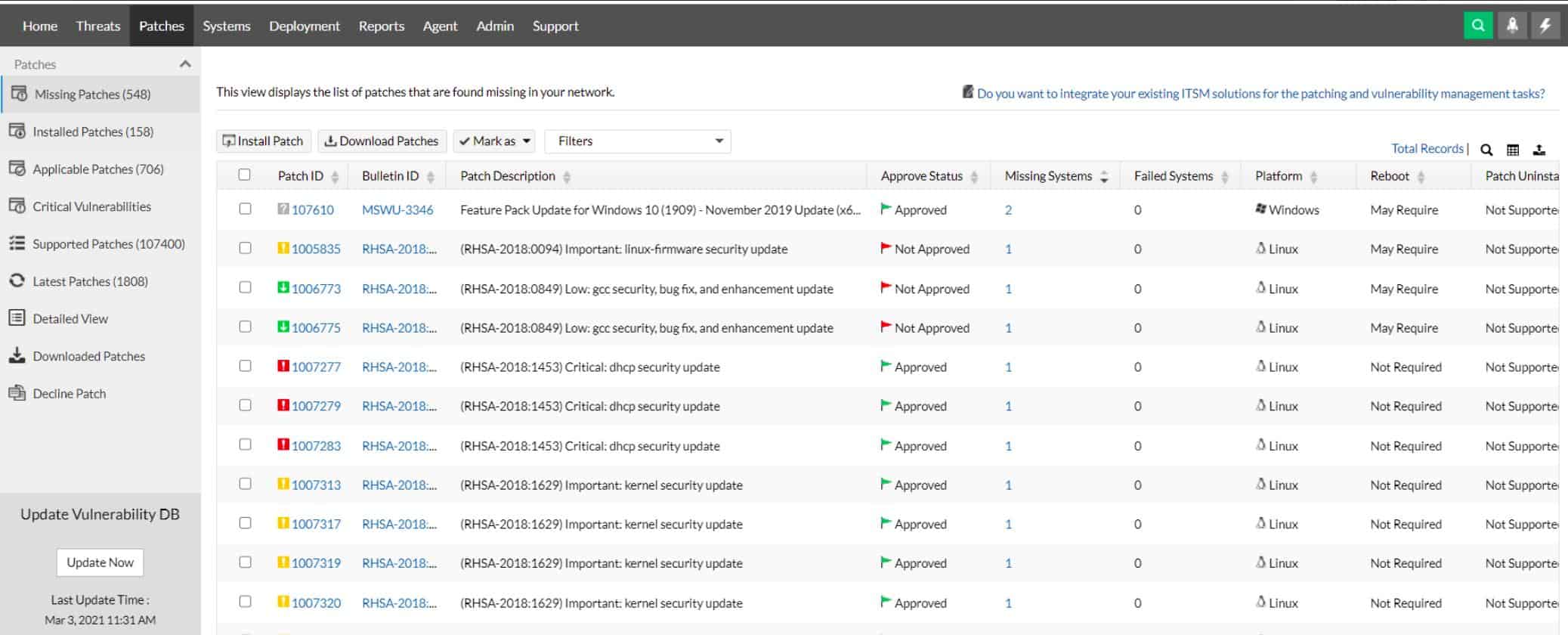
3. ManageEngine Vulnerability Manager Plus (FREE TRIAL)
Vulnerability Manager Plus uses a set list of known system weaknesses and scans through all of the software and the operating system on each endpoint. This tool is an on-premises software package and it reaches out to all of the endpoints in your enterprise across the network. The highest edition of this package is able to connect across the internet to check all of the endpoints on remote sites.
Key Features
- Checks for Known Weaknesses: Scans system configurations
- Implements Patching: Automatically called by the vulnerability manager
- Protects Multiple Platforms: Endpoints can be running Windows, macOS, and Linux
Why do we recommend it?
ManageEngine Vulnerability Manager Plus scans all endpoints on a network and identifies security weaknesses. The package works through a list of weaknesses that are known to be vulnerable to hacker attacks. These are called exploits and they are the tactics that hackers use to try to corrupt or break into a target.
The Vulnerability Manager Plus system is a collection of security systems that combine to form a platform that protects all endpoints on a network. The system looks at the versions of operating systems and software packages to identify whether there are updates available. Many updates are issues to address recently discovered security weaknesses, so it is important to install them. The ManageEngine software gathers the patches available for the discovered packages and schedules them for installation. The tool is able to order patches to account for dependencies and it is also possible to test patches before they are applied.
Vulnerability Manager Plus also identifies software that has been flagged for End of Life status. The news that software is about to be deprecated is important because your business needs to take steps to find replacements.
The vulnerability manager scans each device and spots configuration weaknesses that provide entry points to attackers. The system reports on methods to close off those misconfigurations. The system also pays particular attention to Web servers and internet-facing network devices because they can be the first contact point for external attacks. Issues such as closing unused points and restricting Ping services can help harden these devices.
The service will also assess user accounts and system privileges. Accounts with high access privileges are very big targets for intruders and so these need to be addressed, as do abandoned accounts.
Who is it recommended for?
Any business would benefit from this package of system hardening checks. The package is available in three plans and each has different utilities. There is a Free edition for SMBs that will scan up to 25 endpoints. The paid editions don’t have that limit. This software runs on Windows Server.
Pros:
- Multi-Site Scanning: Available in the top edition
- Protects Against Web-Based Attacks: Hardens web servers and network gateways
- Alerts to Out-of-Date software: Checks for patch availability
Cons:
- Not a SaaS Package: Downloads onto Windows Server
ManageEngine Vulnerability Manager Plus is an on-site package that runs on Windows Server. The system is offered for free to manage up to 25 endpoints. The Professional edition will manage a LAN of more than 25 devices and the Enterprise edition is designed to protect endpoints on multiple sites. You can get either of the paid versions on a 30-day free trial.
4. Datadog Threat Intelligence
Datadog Threat Intelligence is offered from the Datadog cloud SaaS platform that includes a range of subscription services for system monitoring. The system requires agents to be installed on the monitored networks and it can also include cloud resources with the activation of an integration.
The Datadog agents can also act as data gatherers for other Datadog services in combination. Those local agents upload log messages and other system data to the Datadog server where threat hunting takes place.
Key Features
- A Cloud-Based Threat Detection Module: A SIEM system
- Centralizes Security: Can operate for multiple sites
- Uses UEBA: Scans for insider threats
Why do we recommend it?
To get Datadog Threat Intelligence, you need to subscribe to the Cloud SIEM package. This includes a database of threat detection rules and a library of 600 integrations that enable agents to forward log messages to the threat hunter. The tool lists security signals to look for which is augmented by a threat intelligence feed.
The UEBA system in Datadog Threat Intelligence is a user and entity behavior analytics system. This is an AI-based system that uses machine learning to establish a baseline of normal activity. Deviations from that pattern identify activities that require further scrutiny.
The threat hunter looks for patterns of behavior, which are called Indicators of Compromise (IoCs). The IoC database is derived from the experiences of all of the clients of Datadog, creating a threat intelligence pool.
Datadog uses a method called SOAR to interact with packages supplied by other providers. This stands for security orchestration, automation, and response. It means that the agents can gather operating data from systems such as access rights managers, switches, and firewalls. In the other direction, the server can send instructions through to those key network devices to shut down intrusion or kill off malware.
The SOAR and UEBA features of Datadog Threat Intelligence mean that you don’t need to completely bin your entire current security protection setup. The Datadog system will sit on top of your existing services and add to their protective capabilities.
Datadog Threat Intelligence includes extra services that would be of interest to developers and DevOps departments. These include a code profiler and continuous testing systems for CI/CD pipelines.
Who is it recommended for?
The Cloud SIEM can monitor whichever system that the agents can collect log messages from. This includes cloud platforms, containers, and virtualizations, as well as servers and software. The tool is also able to send instructions out to other security systems in order to shut down the detected threats.
Pros:
- Integrates with Other Datadog Services: Add on cloud security posture management
- Web-Based Console: Accessed through any standard Web browser
- Log Message Processing: identifies events on all systems that can generate log messages
Cons:
- Protected Systems Require Constant Internet Availability: Datadog needs to communicate with an on-site agent
Datadog Threat Intelligence, like all Datadog units, is a subscription service. You pay a rate per month for each GB of log data processed by the service.
5. Trellix Helix
Trellix Helix is a cloud-based blended protection system for networks and endpoints. The tool includes a SIEM approach that monitors network activity and also manages and searches log files. The threat intelligence feeds provided by FireEyes completes this multi-faceted solution by providing an updated threat database for your monitoring system.
Key Features
- SaaS Package: Gathers event information from all the endpoints on a protected site
- Constantly Updated Threat Database: Shares threat information among all Helix clients
- Remediation Workflows: Set up your own playbooks
Why do we recommend it?
Trellix Helix is a SaaS package and it performs security monitoring for on-premises and cloud systems. The tool is a SIEM and it gathers log messages from all technologies. The package takes a threat intelligence feed to speed up threat hunting and responses can be automated through coordination with third-party security tools.
FireEyes is a prominent cybersecurity firm and it uses its expertise to provide threat intelligence services on a subscription basis. The format and depth of that intelligence depend on the plan selected by the customer. FireEyes offers industry-wide warnings over new threat vectors, which enable infrastructure managers to plan for defense. It also offers a threat intelligence feed, which translates directly into threat detection and resolution rules in Helix Security Platform.
The Helix package also includes “playbooks,” which are automated workflows that enact threat remediation once a problem has been detected. These solutions sometimes include advising on secure practices and housekeeping actions, as well as automated responses.
Who is it recommended for?
This package is comprehensive but it might be a little too much for small businesses. The Helix system is suitable for mid-sized and large organizations. It can centralize security monitoring for multi-site businesses in a SOC. Companies with hybrid environments would also be attracted to Helix.
Pros:
- Dark Theme Console: Won’t strain the eyes during long-term monitoring in NOCs
- Stores Records of Events: Useful for attack analysis
- Playbooks for Remediation Can Involve Instructions to Third-Party Security Tools: Such as firewalls and access rights managers
Cons:
- Malware that Disconnects Endpoints from the Network is an Unaccounted-For Threat: It disables the Helix security routines
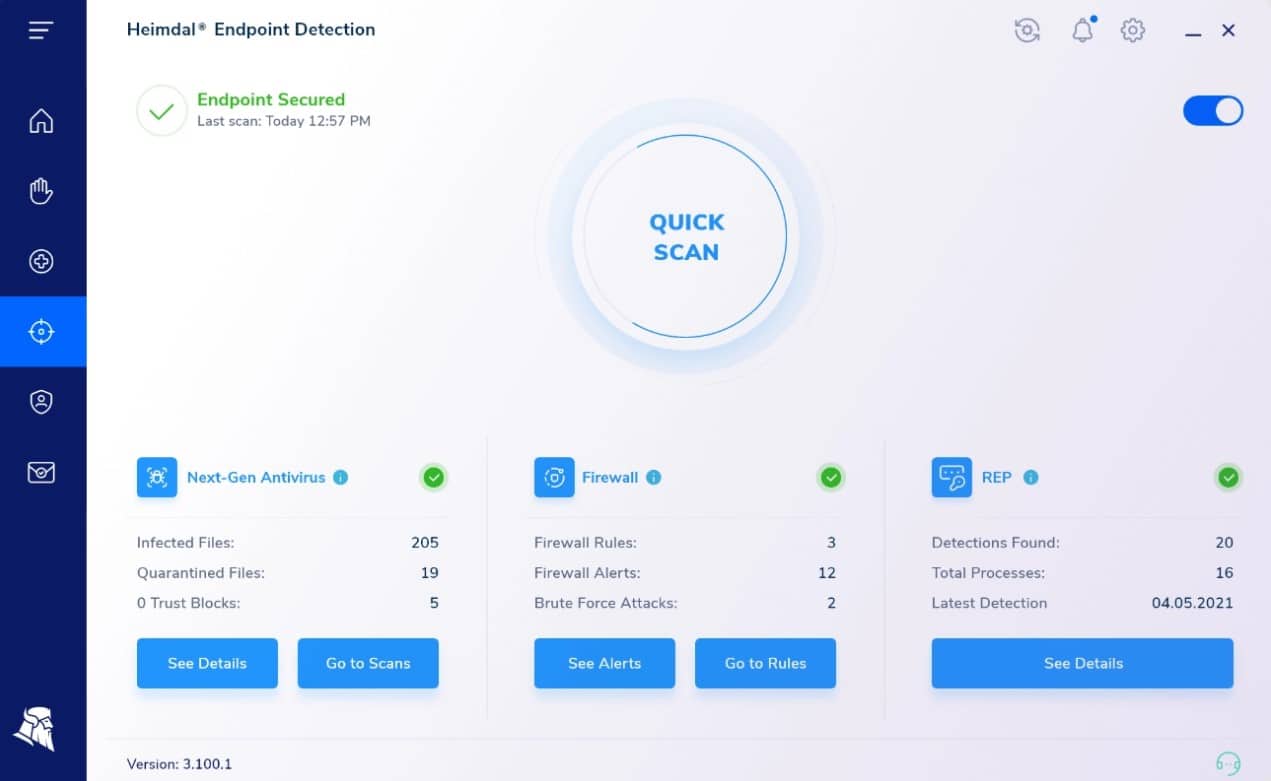
6. Heimdal Threat Hunting and Action Center
Heimdal Threat Hunting and Action Center is based in the cloud and it acts as a threat detection module as part of a suite of Heimdal cybersecurity systems. This module doesn’t act as a standalone product and it is specifically designed to consolidate activity reports from the Heimdal Next-Gen Anti-Virus system. This NGAV installs on Windows, macOS, and Linux. The NGAV system can also implement mobile device management (MDM) for devices running Android, and iOS.
Key Features:
- Gathers Data from a Site: Interacts with on-premises Heimdal products
- Centralized Activity Reports: Scans for threats from a unified data pool
- Implements Automated Responses: Activated through coordination between Heimdal units
- Includes Vulnerability Scanning: Examines system configuration and software statuses
Why do we recommend it?
Heimdal Threat Hunting and Action Center is a cloud-based system that adds value to on-premises Heimdal cybersecurity products. The system relies on the presence of Heimdal Next-Generation Anti-Virus, which installs on Windows, macOS, and Linux. The Threat Hunting system gathers activity records from this tool for threat detection.
The Threat Hunting & Action Center is only available in conjunction with the Heimdal NGAV plus two more Heimdal cyber security products. These can be any two of the Network Security, Email Security, Patching & Asset Management, and Endpoint Security packages from Heimdal.
The cloud service isn’t limited to reactive actions once a threat has been identified. The package will also scan devices, looking for vulnerabilities. It creates a risk score for each device and recommends system hardening requirements.
If a threat is detected on one device on the network, the service will send out warnings to all of the other endpoints. This blocks lateral movements by malware or intruders. These warnings constitute a corporate threat intelligence network. The coordinated responses are implemented by a unit called the XTP Engine. XTP stands for Extended Threat Protection
While unaffected devices are fortified against attack, the device that is already under threat receives defense instructions that help it to block the malicious activity. The cloud service will also provide reports on attacks and the actions taken to block them. This information is useful for system adjustments to guard against a repeat of the same attack strategy.
Who is it recommended for?
This solution is suitable for mid-sized businesses and it can provide a private threat intelligence feed, warning all devices on a network when one is attacked. The service requires the presence of three Heimdal products on site, one of which must be the Next-Generation Anti-Virus package.
Pros:
- Device Scanning: Protects computers and mobile devices
- Protection for Cloud System: Adds cloud-based threat detection to on-site cybersecurity tools
- A Cloud-Hosted Unit: A centralized private threat intelligence service
- Coordination for Several Heimdal Specialized Units: Flexible system-wide protection packages
Cons:
- Requires Three Other Heimdal Units: Not a standalone product
The Heimdal Threat Hunting & Action Center forms part of a package of tools that you choose from a list of Heimdal services and so it isn’t possible to get an out-of-the-box trial. Investigate the service by requesting a free demo.
7. N-able Threat Hunting

Threat Hunting is a product of N-able that provides software and services to support managed service providers. MSPs regularly offer network and IT infrastructure management services and so the addition of security monitoring is a natural extension of the regular activities of such MSPs.
Key Features
- An Endpoint Security Package: Gathers activity data from endpoints
- A SIEM Built for MSPs: Centralizes threat hunting in the cloud
- Log Management: Includes a log server
Why do we recommend it?
N-able Threat Hunting is a SaaS platform threat centralizes SOC services. The package includes a SIEM system and a threat intelligence feed. Monitored systems need collector agents installed on them to send log messages to a central pool for searches. The package provides automated responses.
This is a security information and event management (SIEM) system. A SIEM looks both at live activity on the monitored system and it also searches through system logs to detect traces of malicious activities. The service is able to monitor the on-site systems of the MSP’s clients and also any Azure or AWS server that the client uses.
The advantages of the N-able Threat Intelligence monitor lie in its ability to collect information from every point of the network and the devices connected to it. This gives a more comprehensive view of attacks than a single collection point. Threats are identified by patterns of behavior and also by reference to the central SolarWinds Threat Intelligence database, which is constantly updated. The threat intelligence database is compiled from records of events occurring all over the world. So it is able to spot immediately when hackers launch global attacks or try the same tricks against many different victims.
The alarm levels of the service can be adjusted by the MSP operator. The dashboard for the system includes visualizations for events, such as dials and charts, as well as live lists of checks and events. The service is delivered from the cloud and so is accessed through any web browser. N-able Threat Intelligence is a subscription service, so it is completely scalable and suitable for use by MSPs of all sizes.
Who is it recommended for?
The N-able brand of system monitoring and management tools is designed for use by managed service providers. The Threat Hunting package can also be used for an in-house security operations center. This is a particularly good solution for multi-site businesses. MSPs can become MSSPs with this package.
Pros:
- Good Income Stream for MSPs: Provides an extra service that they can sell to clients
- Protection for Hybrid Systems: Can scan cloud platforms as well as endpoints
- Different Alarm Levels: Distinguish between warnings and emergencies
Cons:
- Not Intended for IT Departments: Specifically marketed to MSPs
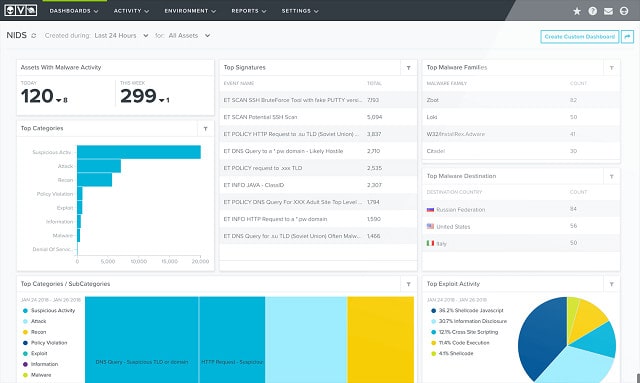
8. AlienVault USM Anywhere
AlienVault USM Anywhere is a product of AT&T Cybersecurity, which acquired the AlienVault brand in 2018. AlienVault USM Anywhere evolved from an open-source project called OSSIM, which stands for “open source security information management.” OSSIM is still available for free with AlienVault USM Anywhere running alongside as a commercial product.
Key Features
- Open Threat Exchange: Has free and paid editions
- Cloud-Based SIEM: Based on one of the longest-running SIEM systems in the world
- Threat Hunting with AI Processes: Looks for anomalous activities
Why do we recommend it?
AlienVault USM Anywhere is a SIEM service and a higher version of the OSSIM system. Both of these tools were acquired by AT&T Cybersecurity in 2019. The company has kept the integrity of both of these tools and capitalizes on the popularity of the free OSSIM system.
OSSIM is actually a misnomer because the system is a full SIEM, including both log message analysis monitoring with real-time network traffic examination. AlienVault USM Anywhere also includes both of these elements. AlienVault has a number of extra features that are not available in OSSIM, such as log consolidation, log file storage management and archiving. AlienVault USM Anywhere is a cloud-based subscription service that comes with full telephone and email support, while OSSIM is available for download and relies on community forums for support.
A key benefit that is available to the users of both the free and paid security products is access to the Open Threat Exchange (OTX). This is the world’s largest crowd-provided threat intelligence platform service in the world. Information made available on the OTX can be downloaded automatically into AlienVault USM Anywhere to supply an up-to-date threat database. This provides the detection rules and resolution workflows needed by the SIEM. Access to OTX is free for all.
Who is it recommended for?
Small businesses are going to prefer OSSIM to USM Anywhere. However, that free tool is a good trial for businesses that might choose to upgrade to the USM Anywhere system. There is a lot more automation in this paid package and many companies judge that it’s worth paying for.
Pros:
- A Free Version is Available: Look for OSSIM
- Provides Preventative Scanning: As well as live security monitoring
- Provides Orchestration and Automation for Threat Remediation: Interacts with third-party security tools
Cons:
- All Plans are Pricey: Many companies might choose the free OSSIM instead
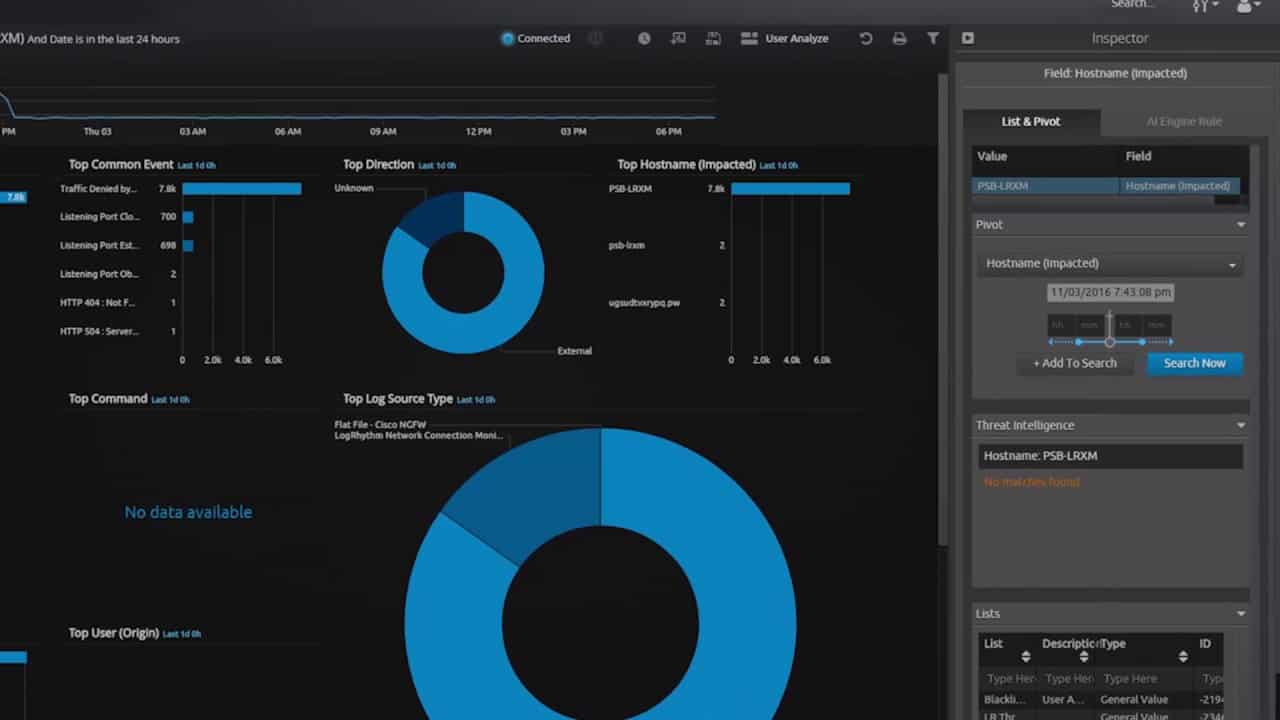
9. LogRhythm NextGen SIEM
LogRhythm terms its NextGen SIEM as a threat lifecycle management (TLM) framework. The platform serves two LogRhythm products, which are the Enterprise and XM ranges. Both of these products are available either as an appliance or as software. LogRhythm Enterprise is aimed at very large organizations, which LogRhythm XM serves small and middle-sized businesses.
Key Features
- Deployment Options: Buy it as a network appliance or install the software on Windows, Unix, or Linux
- A SIEM: Includes a log management
- Compliance Reporting: FISMA, GDPR, GLBA, HIPAA, ISO 27001, PCI DSS and many other standards
Why do we recommend it?
LogRhythm NextGen SIEM is a sophisticated SaaS package that provides threat hunting. The platform has some extra modules that can be added onto the core SIEM service. These include a User and Entity Behavior Analysis (UEBA) unit, a cloud platform scanner, and a Network Detection and Response (NDR) system.
SIEM stands for Security Event Information Management. This dense strategy combines two activities, Security Information Management (SIM), and Security Event Management (SEM). SEM monitors traffic in real-time, looking for attack patterns that are stored in a threat database. SIM also refers to the threat database but compares events recorded in log files to the patterns laid out in the threat detection rules.
The software for the NextGen SIEM can be installed on Windows, Linux, or Unix. It is also possible to keep your threat management system completely independent of your hardware by buying the system as an appliance that connects to your network.
Who is it recommended for?
This is a good package for a SOC and provides pretty much most of the security monitoring that the technicians will need. The system can monitor multiple sites and also cloud platforms, which makes it a good option for large organizations.
Pros:
- Guided Setup: Follow a series of wizards to channel log messages into the system
- Extensions Available: A network monitor and a UEBA are available to enhance the SIEM
- Leverages Artificial Intelligence: Machine learning for behavior analysis
Cons:
- No Free Trial: No price list either
Choosing a Threat Intelligence Platform Vendor
The cybersecurity sector is very vibrant at the moment. The growth in intrusion threats adding to the ever-present risk of malware has forced the industry to completely rethink its approach to system protection. This situation has resulted in major AV producers investing large amounts of money in innovative AI techniques and new strategies to combat hackers and cyber-terrorists.
New players in the market add extra pressure to the reputations of established cybersecurity providers and keep pushing the limits of cybersecurity technology. Threat intelligence platforms play an important role in the fight for cybersecurity alongside SIEMs and intrusion prevention systems.
Although new TIPs appear all of the time, we are confident that the recommended threat intelligence platforms on our list will stay at the head of the pack. This is because the companies that provide them have long-standing experience in the field and they have shown that they are prepared to innovate to keep ahead of threats.
Threat Intelligence Platforms FAQ
What is the difference between threat intelligence and threat hunting?
Threat hunting is the process of looking for indicators of compromise (IOCs). Threat intelligence is a list of IOCs to look out for. Some threat intelligence is built into most threat hunting modules – these are the fundamental events to look out for like excessive and rapid failed login attempts that indicate a brute force attack. Other threat intelligence is new information that identifies a new attack strategy that hackers have only just started to use. A threat intelligence feed passes on the news of a zero-day attack onto other subscribers, so that as soon as one user in the pool discovers that attack, all other customers know about it and their threat hunting module can look for it.
How do you describe the differences between threat intelligence and SIEM?
SIEM systems search through log messages for indicators of compromise (IOCs). Threat intelligence provides a list of IOCs to look out for. NextGen SIEMs include access to a live threat intelligence feed that provides up-to-the-minute IOCs.
Can threat Intelligence platforms stop malicious domains?
A threat intelligence platform includes a formatted list of potential attacks. This will include IP addresses and domains that are known to be used by malicious actors.