Cerber ransomware is offered as a service to other hackers. The creators of the malware have created a user portal for it. This enables others to sign up as an affiliate and launch a ransomware attack without copying over the code and hosting it.
Here is our list of the best endpoint protection and ransomware defense tools:
- Acronis Cyber Protect EDITOR’S CHOICE An effective combination of services for defending against ransomware, including threats like Cerber, by offering malware scanning and data backup. Start a 30-day free trial.
- ManageEngine Ransomware Protection Plus (FREE TRIAL) Uses machine learning and behavioral analysis strategies coupled with rollback and recovery to mitigate the effects of Cerber. Get a 30-day free trial.
- ManageEngine DataSecurity Plus (FREE TRIAL) A comprehensive tool for protecting sensitive data, particularly vital for businesses needing compliance with standards like GDPR and HIPAA, and equipped with effective ransomware defense mechanisms. Start a 30-day free trial.
- CrowdStrike Falcon Insight Delivers powerful endpoint detection and response capabilities, ideal for combating Cerber ransomware with its dual-level, cloud-enhanced protection.
- BitDefender GravityZone Offers a robust combination of on-device antivirus, an integrated firewall, and a backup system, making it a full-spectrum defense solution against malware and ransomware.
The Cerber strategy is called Ransomware-as-a-Service (RaaS). It relieves associate hackers from hosting the ransomware distributor, so they don’t have to worry about covering over connection records. In addition, the Cerber hackers take a 40 percent cut of the ransom that the associate gains by using the system.
There are many benefits for the associate when using a RaaS system, but why wouldn’t the Cerber group launch attacks with their software themselves and keep all of the ransom? The creators of Cerber decided that they didn’t want all of the workloads of seeking out marks and the trouble of trying to get access credentials.
By making their ransomware available to others, they can reap the rewards of the efforts of many other hard-working hackers. They remove the risk of those associates screwing them out of their cut by not allowing the code to leave their servers. The controllers of Cerber can log all of its activity and choose to withhold the decryption key if the associates don’t pay up.
About Cerber ransomware
Cerber ransomware first appeared in March 2016. This is quite a long time ago and makes it one of the oldest ransomware systems around. Little is known about the owners of Cerber – none of them have ever been arrested or even identified. However, the RaaS is advertised in Russian on Russian dark web forums, so it is reasonable to assume that the team behind Cerber is based in Russia.
Like a lot of Russian malware, Cerber won’t launch if it lands on a target in Russia or any of the former Soviet Union countries that didn’t join the EU – Armenia, Azerbaijan, Belarus, Georgia, Kazakhstan, Kyrgyzstan, Moldova, Tajikistan, Turkmenistan, Ukraine, and Uzbekistan. This is probably not out of nationalism but because the Russian authorities won’t arrest hackers as long as they don’t launch attacks within the country or its allied nations.
Cerber was very active in 2016 and 2017 and then seemed to disappear. However, you shouldn’t relax just yet because it came back again in January 2020. Cerber has been through many variants, and some earlier versions can be cracked with decryptors available for free. However, the latest version doesn’t have a simple solution.
The ransom demand for Cerber is relatively low compared to many ransomware systems. However, it is not very well organized given that so many different hackers launch Cerber attacks. This reduces the likelihood that the decryptor will be delivered to those who pay the ransom.
How does a Cerber attack start?
Cerber platform affiliates have options over how they get access to target systems. The split in specialty between the attack software and the controlling hacker means that the affiliate program is suitable for hackers with specialist skills in phishing or profiling. It is also ideal for those who are prepared to pay for lists of emails.
The main entry point for the Cerber ransomware is via an infected attachment to a phishing email. Other methods include a download disguised as a helpful program, malware disguised as media propagated through torrent systems, or direct manual transfers through stolen credentials.
Some hackers using the Cerber RaaS are very skilled con artists and will approach targets through social media and charm credentials. This is the type of operation that the creators of Cerber need but do not have the interest or time to implement themselves. This is why they are willing to make their attack software available to others.
What happens in a Cerber ransomware attack?
One good attribute of Cerber is that its attack implements as soon as the dropper has been downloaded onto a target computer. This means that it doesn’t have a stealth phase that spreads it around a network. There aren’t many attempts at lateral movement. The primary victim of an attack is the system onto which the malware is installed. So, the damage of Cerber can be quickly contained by identifying the presence of the software soon.
Cerber will encrypt files on the host computer and any network drives to which that computer is connected and shared drives. The executable for the encryption is saved on the Local App Data or App Data directory with a randomly selected name taken from the real applications installed on the device.
The Cerber ransomware will encrypt all working files, such as documents, text files, audio, video, and image files. It also encrypts database storage files. It doesn’t encrypt executables, so it will still be possible to use the computer after the attack. As each file is encrypted, its name is changed by the addition of an extra extension. The exact extension use by Cerber ransomware has changed over time with the development of new versions. After using .cerber, .cerber2, and .cerber3, the developers settled on a string of four random characters, such as .r4t5 or .dx56.
An AES cipher encrypts files with a 256-bit key. This key is generated on the victim’s computer and protected by RSA encryption with a 2048-bit key. AES encryption is an asymmetric cipher – the encryption and decryption keys are different. You cannot derive the decryption key if you know the encryption key, so it is unnecessary to keep the encryption key secret. The encryption key is called the public key, and the decryption key is the private key.
The Cerber ransom
After completing the file encryption process, the Cerber ransomware leaves several ransom notes. One of these is in HTA and is activated to display on the screen. There is also an audio file available, which speaks to the ransom demand.
The ransom, in 2016, was 1 Bitcoin. The victim had seven days to pay, and then the ransom doubled. The ransom note instructs the victim to install a Tor browser and gives the address of a generated page specific to that attack. The victim is then able to pay through that page. A successful transaction results in the victim being sent the private key for the RSA encryption. This unlocks the AES key, which can be used to decrypt all files.
Preventing Cerber ransomware attacks
The prime targets of Cerber ransomware are endpoints – specifically desktops and laptops rather than servers. This means that your primary defenses should focus on user education and endpoint protection. The malware gets onto devices because users are tricked into installing it. Thus, warning users about infected attachments or malicious links is a worthwhile exercise.
If your business is required to comply with a data privacy standard, the opportunities for data theft that are built into a Cerber attack and the ransomware means that this malware could seriously damage your business’s economic viability. Thus, if you need to comply with PCI DSS, HIPAA, or GDPR, you should also invest in sensitive data protection systems.
Cerber will delete all shadow copies of files – these are the autosave versions. However, it doesn’t travel across a network and infect other devices. So, this means that your backup stores are relatively safe. Another systemic weakness of Cerber is that data disclosure is not part of its master strategy. This means that as long as you run an intelligent backup system, you can afford to ignore the ransom demands and just restore encrypted files from your saved copies.
Be aware that Cerber isn’t the only ransomware that you need to plan protection against. Other systems will try to get onto your servers. In addition, some ransomware will delay activation while replication modules copy the encryption software across the network. Therefore, in order to fully protect backups, you need to combine malware scanning with each backup cycle.
Our methodology for selecting endpoint protection and ransomware defense tools
We’ve broken down our analysis for you based on these key criteria:
- Comprehensive Protection: The ability to cover all aspects of security from viruses to ransomware, including proactive monitoring and defense.
- Ease of Use: Tools that offer intuitive interfaces and straightforward management capabilities.
- Integration Capabilities: The ability to work seamlessly with existing IT environments and other security tools.
- Scalability: Solutions that can grow with the business, accommodating increasing data loads and more complex network environments.
- Backup and Recovery: Includes features that not only protect but allow for quick recovery in case of a security breach.
Here are four secure systems that you should consider installing:
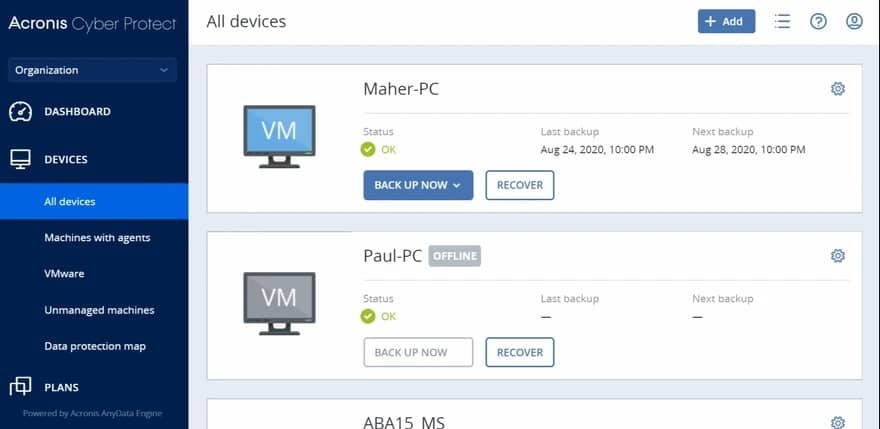
1. Acronis Cyber Protect (FREE TRIAL)
Acronis Cyber Protect offers an ideal combination of services for defending against Cerber and other ransomware. Built-in malware protection makes it difficult for ransomware to reach a target system, and if an attack does occur, administrators can restore all encrypted data from backup without paying a ransom.
Key Features:
- Real-Time Threat Detection: AI-powered ransomware detection helps prevent attacks before they can cause damage.
- Retroactive Malware Scanning: The system scans existing backup data using updated malware signatures to ensure previously stored files remain safe.
- Antivirus: Offers comprehensive malware and ransomware protection.
- Backup and Recovery: Provides robust backup solutions for both physical and virtual systems.
- Vulnerability Scanner: Includes tools to detect and patch vulnerabilities in software.
Why do we recommend it?
Acronis Cyber Protect is a combination of antivirus and backup and recovery. This is the ideal combination of systems to deal with ransomware. The system also assesses URLs to block access to infected or fake sites. Other units in the package are a vulnerability scanner and a patch manager.
The backup service covers physical and virtual systems, and it can perform complete backups of servers down to the bare metal. It will manage the backup of Windows Server and Linux. Backups can be made to other devices on-premises, to cloud storage systems, or both. You can choose your cloud platform to host the backup store, and Acronis offers a cloud backup storage service as an optional extra.
The vulnerability manager identifies software weaknesses and can patch out-of-date OSs and software. However, you also need full virus and intrusion defenses, so the threat detection system in the Acronis bundle is essential.
Who is it recommended for?
Acronis produces Cyber Protect in several editions, each of which caters to a different size and type of business. These range from a package for home offices up to a service for managed service providers. So, this system has a very wide market of potential customers.
Pros:
- Automated Recovery: Ensures data is restored quickly and accurately if a ransomware attack occurs, minimizing downtime and disruption.
- Comprehensive Protection: Combines antivirus, backup, and vulnerability management in one package.
- Flexible Backup Options: Supports on-premises and cloud storage, with full-server backups down to bare metal.
- Cross-Platform Compatibility: Available for both Windows and Mac, catering to a diverse set of users.
- User-Friendly: Balances ease of use with advanced features, suitable for various business sizes.
Cons:
- Complex Features: Some advanced features may require a steep learning curve to master effectively.
This is a cloud-based system that requires an agent program to be installed on your site. Acronis offers Cyber Protect a 30-day free trial.
EDITOR'S CHOICE
Acronis Cyber Protect is our first pick for a Cerber ransomware protection system because it combines powerful cybersecurity features with comprehensive data protection in a single solution. Cerber ransomware is known for its ability to encrypt files and demand ransom for their release, posing a significant threat to businesses. Acronis Cyber Protect offers multiple layers of defense against such threats: data backup, anti-malware, and real-time monitoring. Acronis Cyber Protect provides advanced anti-ransomware technology, which actively detects and blocks suspicious behavior, preventing ransomware from encrypting files in the first place. The solution utilizes machine learning and behavioral analysis to identify new and evolving ransomware threats, offering cutting-edge protection against Cerber and other ransomware variants. If an attack does occur, Acronis Cyber Protect ensures that businesses can quickly restore encrypted files from secure backups, minimizing downtime and data loss. This security package is incredibly easy to use, with a unified dashboard that allows IT teams to monitor and manage their entire security and backup strategy in one place. Its integration of backup and cybersecurity into a single platform reduces complexity and ensures that businesses have the tools they need to protect critical data from ransomware attacks, including Cerber.
Download: Start a 30-day FREE Trial
Official Site: https://www.acronis.com/en-us/products/cyber-protect/trial/
OS: Cloud-based
2. ManageEngine Ransomware Protection Plus (FREE TRIAL)
ManageEngine Ransomware Protection Plus has the right mix of features to detect and isolate Cerber ransomware infections before they spread across your entire network. It also checks file integrity and connects with backup systems to quickly restore infected data.
Key Features:
- Behavior-based detection: It checks for specific aspects like mass file encryption and abnormal registry changes to detect if a system has been infected by Cerber.
- Automatic isolation: Once it identifies the infected files, it automatically isolates them to prevent lateral spread.
- Quick recovery: Connects with the backup systems to bring files back to the pre-attack state.
- Root cause analysis: Identifies the vulnerabilities that caused the attack, so you can fix them right away.
Why do we recommend it?
We recommend ManageEngine Ransomware Protection Plus because its quick detection and neutralization reduce the damage. It also kills the ransomware processes and quarantines infected devices. This tool can also detect programs that display behavior tied to ransomware and neutralize them before they cause further damage.
This multi-pronged approach, from detection to recovery, can help organizations recover faster from a Cerber attack. Furthermore, it safeguards your devices from future attacks by identifying the IPs and URLs used and blocking them. It also reports them on the VirusTotal community to prevent future attacks.
Who is it recommended for?
It is highly recommended for medium to large organizations that have to manage thousands of endpoints. It can also come in handy for IT teams that want to quickly detect and neutralize these threats.
Pros:
- Prevents lateral spread
- Sends real-time alerts
- Supports recovery
- Uses behavioral analysis and not just signatures
- Integrates with other tools
Cons:
- Complex to set up
Ransomware Protection Plus has a free edition that supports up to 25 endpoints. The Enterprise edition is priced at $6.99 per endpoint per year. Get started by registering for a 30-day free trial.
3. ManageEngine DataSecurity Plus (FREE TRIAL)
ManageEngine DataSecurity Plus is designed to protect sensitive data. This is essential for businesses that need to comply with data protection standards, such as GDPR, HIPAA, and PCI DSS. In addition, the service includes a file integrity monitor that will spot and block file encryption as soon as it starts. So, his is an excellent service to protect against ransomware, including Cerber.
Key Features:
- Data Loss Prevention: Protects against data leaks and unauthorized access.
- Compliance Reporting: Facilitates adherence to standards like GDPR, HIPAA, and PCI DSS.
- File Integrity Monitoring: Detects and blocks unauthorized file changes to prevent ransomware attacks.
- Multi-Platform Coverage: Secures data across on-premises servers and cloud platforms.
Why do we recommend it?
ManageEngine DataSecurity Plus is a protection system for sensitive data but its file integrity monitoring and server activity monitoring services will spot any file name changes, which occur at the beginning of the ransomware encryption process. Blocking the process that performs that action and disconnecting the device from the network stops the ransomware.
The DataSecurity Plus system includes a data discovery service and a sensitive data classifier. It focuses defenses on sensitive data stores and logs all activities to provide an audit trail for compliance.
Who is it recommended for?
This system is a large package that is organized into four modules, which are all charged for individually. Not all businesses will need all of the modules, so it would be possible to reduce the cost of the protection system by identifying precisely which modules are needed. It will particularly appeal to businesses that manage sensitive data.
Pros:
- Detailed File Monitoring: Tracks file access comprehensively, enhancing security oversight.
- Trend Analysis: Identifies patterns in data access that may indicate malicious activity.
- Compliance Support: Offers robust reporting features for major regulatory requirements.
- Extensive Integration: Compatible with a variety of helpdesk and backup systems for streamlined operations.
Cons:
- Complex Setup: Involves a significant time commitment to fully leverage all available features and integrations.
This is an on-premises package that installs on Windows Server. DataSecurity Plus is available for a 30-day free trial.
4. CrowdStrike Falcon Insight
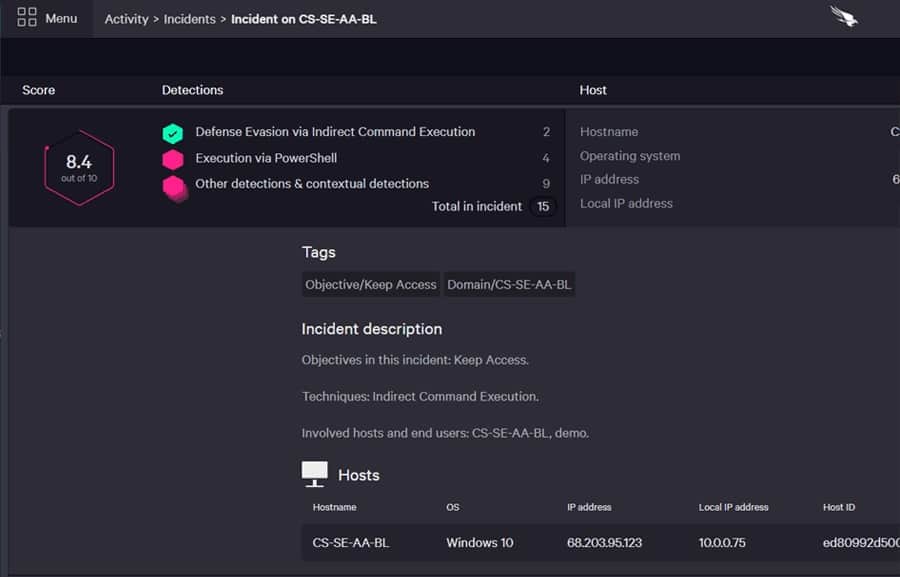
CrowdStrike Falcon Insight is an endpoint detection and response system (EDR). It focuses protection on endpoints, which is the perfect strategy for defense against Cerber ransomware.
Key Features:
- Dual-Level Defense: Combines local antivirus on endpoints with a cloud-based control system.
- Private Threat Intelligence: Offers tailored security insights to prevent lateral threats.
- Lateral Movement Blocking: Effectively stops the spread of threats across devices.
Why do we recommend it?
CrowdStrike Falcon Insight is a multi-level package that provides antivirus servers on each endpoint and a cloud-based SIEM that operates on data uploaded by the endpoint system. The endpoint unit will continue to operate if the device is disconnected from the network and the SIEM acts as a private threat intelligence system, preventing lateral movement.
Rather than just being an antivirus system, this package adds enterprise-wide defense coordination to the device-resident protection software. This system protection is provided by a cloud-based service that collects activity reports from each endpoint agent.
The endpoint defense software is available as a standalone package, called CrowdStrike Falcon Prevent. It is the cloud service that transforms many installations of Falcon prevent into Falcon Insight.
The cloud service works as a SIEM, searching through log data uploaded from the endpoints for indicators of compromise. This is a secondary defense because the endpoint agents are more than just data collectors; they have a complete defense system built into them. This double protection strategy enables CrowdStrike Falcon to offer complete system protection, and it can also cope with zero-day attacks.
Who is it recommended for?
The CrowdStrike system keeps vigil on each device and also warns all devices if one is attacked. Thus, ransomware is unable to spread throughout your organization and is contained on one device. Remediating that problem is a lot easier than having to restore every single endpoint.
Pros:
- Versatile Environment Compatibility: Performs exceptionally in mixed environments including Windows, Linux, Cloud, and BYOD setups.
- User-Friendly Administration: Features an intuitive admin console that is accessible via the cloud.
- Behavioral Tracking: Enhances security through continuous monitoring and anomaly detection.
- Efficient Resource Use: Operates with lightweight agents that minimize system resource usage.
Cons:
- Limited Trial Offering: Could be improved by providing a more extended trial period to better evaluate its full capabilities.
You can get a 15-day free trial of Falcon Prevent.
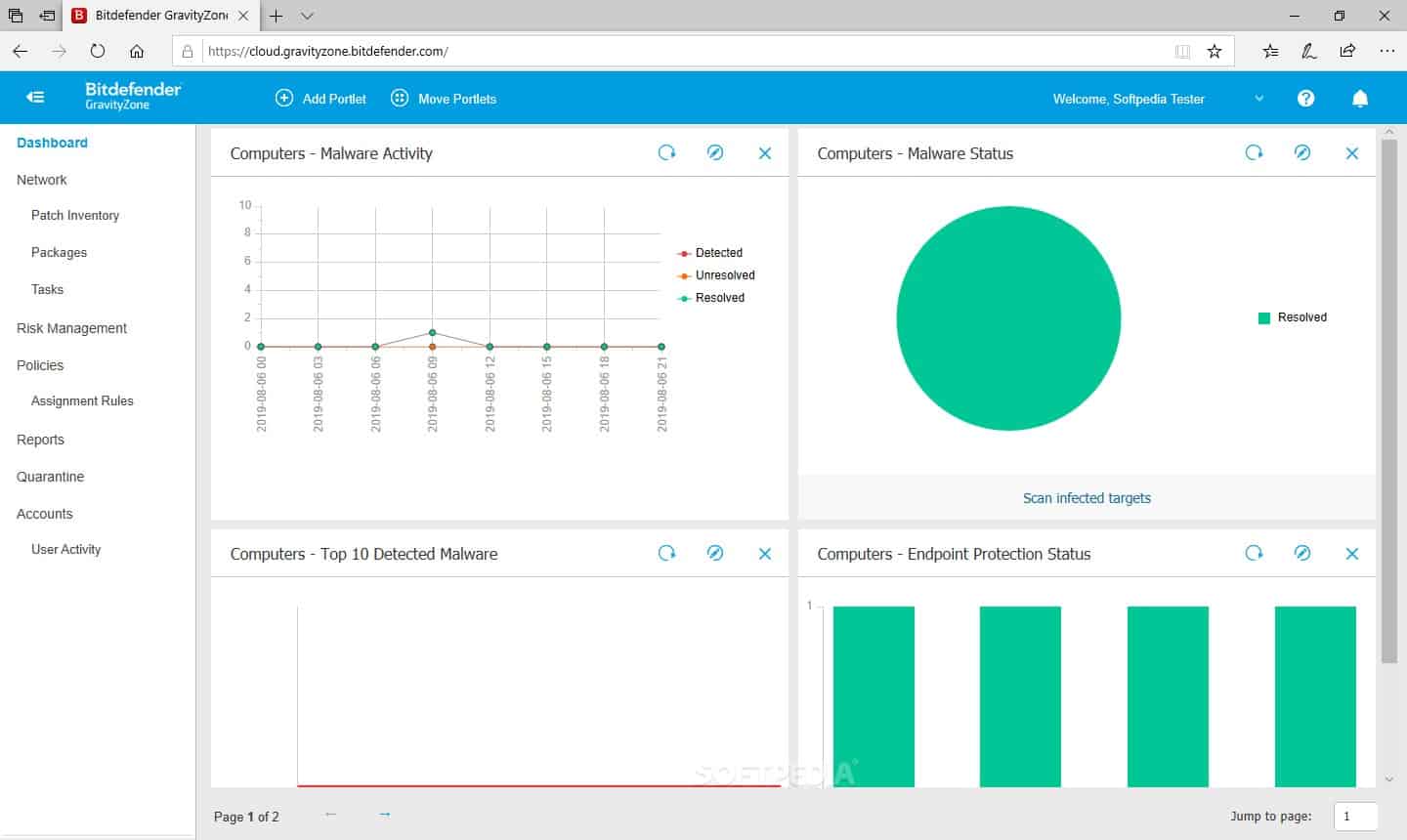
5. BitDefender GravityZone
BitDefender GravityZone covers all aspects of malware detection and protection and also includes a backup service.
Key Features:
- On-Device Antivirus: Provides robust malware protection directly on endpoints.
- Integrated Firewall: Enhances network security with a powerful firewall.
- Vulnerability Scanner and Patch Manager: Identifies and addresses software vulnerabilities to prevent exploits.
Why do we recommend it?
BitDefender GravityZone is an anti-virus system and firewall for endpoints that has special routines for ransomware detection and mitigation. The package includes a backup system for data files and that enables all data to be restored after detected ransomware has been shut down. Higher plans include allowlisting, which prevents all but approved software from activating.
The GravityZone service watches over all parts of your system, including endpoints, which are particularly vulnerable to Cerber ransomware attacks. The bundle of security services also includes a vulnerability scanner and a linked patch manager. These modules ensure that the ports, operating systems, and software packages are free from the exploits that will help malware get onto your system.
No matter how tight your security is, you can do little to prevent users from being duped into performing actions on behalf of con artists. So, you also need to make sure that you sweep for viruses at every point of your system. This is what GravityZone does. It protects all possible entry points, such as gateways and endpoints. Crucially, it also scans files for infection before uploading them to backup servers.
Who is it recommended for?
GravityZone is available in three editions with a Small Businesses service as the entry point. The higher plans have many more features. However, the ransomware is included in all three plans. That makes the ransomware protection and recovery services of this package accessible for all sizes of businesses.
Pros:
- Comprehensive Security Suite: Includes antivirus, firewall, and backup solutions in one package.
- Advanced Ransomware Protection: Features specialized routines for detecting and mitigating ransomware threats.
- Behavioral Analysis: Employs both signature-based detection and behavioral analysis to identify potential security threats.
- Data Encryption: Offers disk encryption to secure sensitive data on endpoints.
Cons:
- Lack of Documentation: Users may require more comprehensive guidance to fully utilize all features effectively.
Other essential elements of this security bundle are file integrity monitoring and automated responses. The software for BitDefender GravityZone runs as a virtual appliance, and it is available for a one-month free trial.