CryptoLocker ransomware tore around the world in 2013 and 2014 in an eight-month cybercrime spree
Here is our list of the best tools to protect against ransomware attacks:
- ManageEngine Ransomware Protection Plus EDITOR’S CHOICE This all-in-one tool can protect your organization from ransomware like CryptoLocker. It defends your operations and reputation with its rich features. Start a 30-day free trial.
- ManageEngine DataSecurity Plus (FREE TRIAL) A protection service for sensitive data that includes file integrity monitoring that will spot the file renaming and encryption phase of ransomware. Available for Windows Server. Start a 30-day free trial.
- CrowdStrike Falcon Insight XDR This hybrid system includes on-device systems for activity scanning that identifies all types of threats, including malware, such as ransomware. It also has a central cloud-hosted threat hunting unit that spots lateral movement.
Although CryptoLocker ransomware is no longer a threat, it leaves a trail of variants and imitators in its wake, so it is still worth studying. The target of CryptoLocker was Windows computers.
The delivery mechanism of CryptoLocker ransomware was a Trojan. This was spread by a botnet called Gameover ZeuS. The ransomware put pressure on victims to hurry up and pay by placing a time limit on the availability of the decryption key.
CryptoLocker was first spread on September 5, 2013, and it was shut down in May 2014. During its period of operation, it attacked about 500,000 computers.
What is a botnet?
A botnet is a group of infected computers controlled from a central server over the internet. The active mechanism on the captured computer can open a connection and scan the remote server for instructions – that host is called the “command and control” (C&C) server.
The computers in the botnet are called “zombies.” They aren’t entirely controlled by the hackers and continue to operate as usual. In most cases, those companies don’t even realize that their devices are working for other people.
The purpose of a botnet is to spread a task between many computers. Some botnets control hundreds of thousands of private computers, and others control IoT devices, such as security cameras. Defense mechanisms in cybersecurity software can read the IP address of an attacker and block it. So, hackers invented botnets in which each computer just attacks a target once.
Typically, these legions of computers are used in DDoS attacks, where many computers simultaneously make a connection request to a web server, overwhelming it. They are also used for spam email campaigns.
Spam filters on most email systems divert emails from one IP address in bulk by sending those large mailouts from lots of different locations, but the botnet ducks that block.
Gameover ZeuS
The Gameover ZeuS botnet was created and controlled by Evgeniy Mikhailovich Bogachev, a Russian hacker. It included more than 1 million zombie computers. The system used peer-to-peer architecture for communication with the C&C server. This reduced the traffic traveling in and out of the server and made the C&C harder to trace.
The primary purpose of Gameover ZeuS was banking fraud. The mailing campaign for the CryptoLocker ransomware was a secondary task for the botnet. Not only did the C&C server issue instructions to send out a standard email, but it also generated fake domain names. Emails only need a valid source address if the sender needs a reply. However, the structure of ransomware attacks means that no response is necessary for the campaign to be successful.
In June 2014, an international alliance of law enforcement agencies shut down the Gameover ZeuS C&C servers in a planned exercise called Operation Tovar.
How does a CryptoLocker ransomware attack begin?
CryptoLocker had two methods of ingress. One was with a spam email that had a virus hidden in an attachment. The other was through illegal download sites, which supplied the virus installer bundled with the video inside a Zip file or making the video unusable but with an accompanying text file that instructed the recipient to download a codex plug-in. That plug-in was the installer for the Trojan.
The email purported to be from a shipping company with a delivery notice attached. There were two methods used to get the Trojan on the target computer. One was to make the file password-protected with a note in the email that included the password. Applying the password unlocked the file and released the installer.
It is difficult to work out why the hacker bothered with that password route because its other attachment method was just as effective. This was a Zip file, which seemed to contain a PDF. However, that was a fake extension because when the user unpacked it and clicked on the file to open it, the file ran as an executable and installed the ransomware by copying it down from the C&C server.
What Does CryptoLocker Do?
CryptoLocker starts its routines as soon as it is launched – it doesn’t delay. The system copies the program file to the %APPDATA% and %LOCALAPPDATA% directories. The installer adds a key to the computer’s registry to get the software to run on startup. It then launches the ransomware in two processes – the second is a persistence module that will relaunch the ransomware program if its process gets terminated.
As soon as the main program executes, it scans all accessible drives and lists them. It then visits each drive that includes non-executable files, records its directories, and then works through the list, encrypting them. The system uses RSA encryption with a 2048-bit key. The encryption process creates a new file. However, the process begins with a blank file with the original name and then deletes that. Overwriting the original makes it unrecoverable through the Recycle Bin or any other file recovery system.
Once a file has been encrypted, its original name is recorded in a text file and written to the registry in HKEY_CURRENT_USER/SoftwareCryptoLockerFiles.
The name of the encrypted file is altered to have an extra extension on the end of it. Different versions of CryptoLocker had other naming conventions for encrypted files. The added extension was either .encrypted, .cryptolocker, or a string of seven random characters.
Once all of the non-executable files in a directory had been encrypted, the program wrote a text file called DECRYPT_INSTRUCTION.txt or an HTML file called DECRYPT_INSTRUCTIONS.html. That included a list of the encrypted files. A later variant, called CBT-Locker, wrote out one file listing all encrypted files in the exercise for all directories and saved that to the directory where it started its work. This file was called !Decrypt-All-Files-[RANDOM 7 chars].TXT or !Decrypt-All-Files-[RANDOM 7 chars].BMP.
After encrypting all of the non-executable files in one directory, it would move onto the next until all files on a drive had been encrypted. It would then move on to the next drive accessible by the current user account and repeat the process. The activities of the CryptoLocker ransomware would extend to all of the drives that the active user account could access, which included mounted drives, shared drives, and cloud drives.
The ransomware could not replicate itself or move around the network. It did not include a utility to allow any hackers manual access to the infected computer.
Public key encryption
CryptoLocker ransomware used a public key cipher for its encryption. Public key encryption is also known as asymmetric encryption. This is because the encryption and decryption processes do not use the same key. That means that the decryption process is not just a matter of directly reversing the encryption. Instead, a complimentary formula is used to decode encrypted text.
It is impossible to work out the decryption key from the encryption key. Therefore, as long as the encryption creator keeps the decryption critical private, it doesn’t matter who knows the encryption key. Thus, the encryption key is public, and the decryption key is secret.
CryptoLocker uses the RSA public-key encryption system. RSA is very widely used because it is integrated into the authentication phase of the SSL system. SSL uses the Transport Layer Security protocol (TLS), which is centered on RSA encryption.
In the case of CryptoLocker, the virus contacts the C&C server, which sends the public key for encryption. As this key is of no use for decrypting files, it doesn’t matter if snoopers intercept the transmission of the key. It also doesn’t matter if the user knows the encryption key. So, the key is left within the ransom instructions as a reference that enables the C&C server to locate the correct decryption key to send once payment has been made. When it first acquired the encryption key, the ransomware stored it for reference on the victim’s computer in the registry key HKCUSoftware/CryptoLockerPublicKey.
CryptoLocker maintained a database of all of the encryption keys that it had ever used. However, it ceased to make the decryption key available to the victim after 72 hours had elapsed following an attack. This added a time element to the ransom, which motivated the user to hurry up and pay.
Cheekily, in November 2013, the hackers set up a service that was seemingly offered by data recovery consultants that offered to restore the files for those victims who had missed the 72-hour deadline and were no longer able to get the files decryption key. The recovery service was charged at a higher price than the original ransom.
During Operation Tovar, security analysts working with the authorities captured a copy of the encryption key database. Analysis of the database revealed that the CryptoLocker ransomware had made more than $3 million over its lifetime. Also, the analysts discovered that the process didn’t always return the correct decryption key in 25 percent of the cases where the victim paid the ransom. It was calculated that only 1.3 percent of victims paid the ransom.
The ransom process
On completing the encryption process, the ransomware altered the wallpaper of the Desktop on the target computer—this displayed instructions for payment. The price demanded was $400, which could be paid as 400 Euros or the Bitcoin equivalent. Those paying cash did so via MoneyPak.
The victim was warned that the decryption key would only be available for 72 hours, but this period was 100 hours in some variants.
Blocking CryptoLocker attacks
As the CryptoLocker ransomware tricks users into downloading and activating it, the most robust defense against this system is user awareness. Although CryptoLocker is no longer around, there are plenty of imitators still circulating, so it is essential to make sure that users are aware of the consequences of their actions. It is also vital to protect data on the systems, especially if you follow a data privacy standard.
Desktops running Windows were the targets of CryptoLocker ransomware. You need endpoint detection and response (EDR) systems installed on each device on your network to protect against ransomware attacks like CryptoLocker. Consider the following two security systems.
Our methodology for selecting a ransomware protection tool
We reviewed the market for ransomware protection systems that will block strains like CryptoLocker, and analyzed the options based on the following criteria:
- Scans for email attachments to identify malware
- Scanning and sandboxing for downloaded files
- File protection systems
- Activity monitoring with alerts for unusual actions
- Nice to have a wider protection purpose, such as data protection or general threat detection
- A free trial or a demo option that enables the package to be assessed before buying
- Value for money from a package that is offered at a fair price with respect to the services it delivers
With these selection criteria in mind, we sought out tools that have the flexibility to spot and shut down any type of ransomware.
1. ManageEngine Ransomware Protection Plus (FREE TRIAL)
ManageEngine Ransomware Protection Plus is an AI-driven ransomware protection tool that proactively scans your endpoints and reduces the chances of a ransomware attack. It also neutralizes these attacks and helps recover from the impact.
Key Features:
- Complete investigation: Investigates every incident and maps them to the root cause for further actions.
- Repeat offender defense: Detects programs that are tied to known ransomware.
- Prevents suspicious activities: Protects from activities like encrypting files and modifying critical system files.
- MITRE ATT&CK Mapping: Identifies tactics, techniques, and procedures on the VirusTotal community.
Why do we recommend it?
ManageEngine Ransomware Protection Plus is ideal for handling threats like CryptoLocker ransomware. This is because it scans the memory and processes, along with files, to detect all kinds of ransomware, including fileless ones. Its use of machine learning and behavioral analysis protects you from known and unknown ransomware attacks. Also, it continuously updates the signatures and scans for them to detect threats.
Once detected, it neutralizes the attacks by isolating the devices, killing the ransomware processes when configured in kill mode, and notifying the administrators. It also analyzes the incident and maps it to the root cause to make it easy for IT admins and security teams to take the next steps. Lastly, it connects with backup screenshots to bring the infected files to their pre-attack state.
Such comprehensive protection makes it a reliable choice for advanced attacks like CryptoLocker, and this is why we recommend ManageEngine Ransomware Protection Plus.
Who is it for?
It works best for organizations that handle sensitive data and operate in industries with extensive regulations, like the financial and insurance industries. Also, it is preferred for organizations that run a Windows-based environment.
Pros:
- Early detection: Identifies Indicators of Compromise (IoC) for early detection of patterns.
- Detailed reports: Generates detailed reports to better understand the nature and cause of an attack.
- Single click recovery: Rolls back infected systems with just a single click.
- Memory scanning: Continuously scans the memory to identify fileless ransomware.
Cons:
- Windows OS: Works best for a Windows environment only.
You can get started by registering for a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Ransomware Protection Plus is our first choice because it takes a multi-layer defense approach to safeguard your endpoints from the negative impact of any ransomware attack. Its ability to halt the spread of infected devices and processes acts as the first line of defense against a ransomware attack. Moreover, it can also connect with backup systems to recover data to its pre-attack state. The presence of such features make this tool our first choice for handling CryptoLocker ransomware.
Download: Start a 30-day FREE Trial
Official Site: https://www.manageengine.com/ransomware-protection/
OS: Windows
2. ManageEngine DataSecurity Plus (FREE TRIAL)
ManageEngine DataSecurity Plus is a sensitive data protector specifically designed for companies that need to comply with HIPAA, PCI DSS, and GDPR. The protection this service gives to files also makes it a good choice for blocking ransomware. It includes data discovery and categorization systems, which identify personally identifiable information (PII).
Key Features:
- Data Loss Prevention: Blocks data theft or corruption
- Email Scanning: Examines attachments for malware
- Application Allowlisting: Blocks all software from running on endpoints other than the packages listed by the administrator
- File Integrity Monitoring: Alerts when files are changed and also blocks ransomware activity
Why do we recommend it?
ManageEngine DataSecurity Plus is an on-premises package that is able to observe many endpoints on one network. The system includes a file integrity monitor, which will spot the initial actions of a typical ransomware attack, which is the renaming and encryption of files. At least a few files will be impacted before the system can spot and block the ransomware.
The service monitors emails and USB devices to block downloads and prevent data disclosure. It also has a file integrity monitor to guard against unauthorized changes. The service can be set up to implement actions on the identification of file tampering automatically.
Who is it recommended for?
Ideally, you should use this package in conjunction with a backup and recovery package so that the few files that have already been processed by the ransomware before the malware is stopped can be restored. The package’s central server will isolate the infected device to stop lateral movement.
Pros:
- Provides Detailed File Change Logs: As well as implementing automated responses and enables event analysis after the fact
- Platform Tracks Access Trends Over Time: Creates better malicious compliance reporting for GDPR, HIPAA, PCI DSS, and FISMA
- Integrations with Third-Party Tools: Help Desk solutions, notification platforms, and backup systems
Cons:
- Provided as Five Individual Modules: Only the free edition for the Data Leak Prevention unit is any good
The software for ManageEngine DataSecurity Plus protects Windows systems and installs on Windows Server, and is available for a 30-day free trial.
3. CrowdStrike Falcon Insight XDR
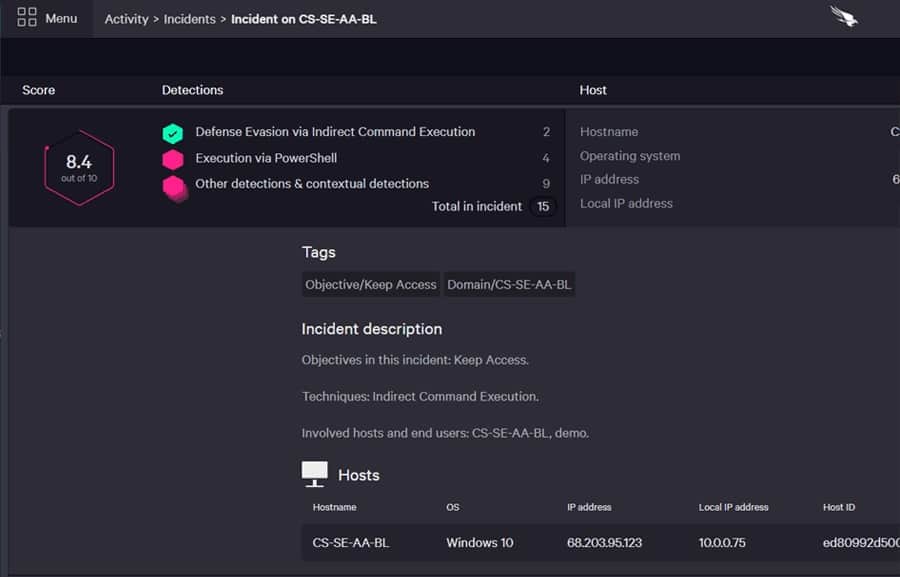
CrowdStrike Falcon Insight combines an EDR on each endpoint with a cloud-based coordinator. The on-site module is called Falcon Prevent.
Key Features:
- Dual Level Threat Hunting: A local unit for continuity and a central service for consistent, system-wide security scanning
- Local Unit is a Next-Generation AV: Scans the device for unusual activity
- Central Coordinator: Based on the cloud
- SIEM-Style Security Searches: Bases threat hunting on
Why do we recommend it?
CrowdStrike Falcon Insight is a suitable cybersecurity package for combatting ransomware, such as CryptoLocker. This is because it operates on two levels with a very strong local agent on each endpoint, which is a fully independent anti-virus system. A cloud service gathers reports from these endpoint units for threat hunting, creating a private threat intelligence network.
The endpoint agents operate independently, which means that they can maintain protection even if there is no connection to the internet. The cloud coordinator receives event log uploads from all endpoints on a network while links are available. The system analyzes this data based on threat intelligence gathered from all CrowdStrike customers. This system looks for abnormal behavior and so can identify zero-day attacks.
Insight includes response capabilities. It can isolate a computer from the network to stop a virus from spreading. The tool is also able to block communications with suspicious IP addresses and suspend user accounts.
Who is it recommended for?
This package is recommended for mid-sized to large organizations. The endpoint unit, called Falcon Prevent is available for purchase individually. The Insight option adds on a cloud-based SIEM to that. You can easily expand coverage by installing Falcon Prevent on another computer. However, the price of that system could be out of reach for small businesses.
Pros:
- Endpoint Unit is Autonomous: Will continue to run even if the computer is disconnected from the network
- Intuitive Admin Console: Guides set up and usage
- Informed by Threat Intelligence Feed: Gathered from the experiences of other clients of the CrowdStrike platform
- Historical Event Metrics Storage: For attack analysis
- Automated Responses: Shuts down attacks immediately without human intervention
Cons:
- No Endpoint Protection Software for Linux: Only Windows and macOS
CrowdStrike Falcon Insight XDR is available for a 15-day free trial.