Like most other ransomware brands, Dharma seems to come from Russia
Dharma ransomware, also known as Crysis, encompasses multiple variants and related strains that share core encryption techniques but differ in delivery methods, file extensions, and how ransom notes are presented.
Here is our list of the best ransomware protection tools:
- ManageEngine DataSecurity Plus (FREE TRIAL) Specializes in protecting sensitive data across various compliance frameworks, integrating data discovery with ransomware defense for comprehensive security coverage. Start a 30-day free trial.
- CrowdStrike Falcon Insight Delivers advanced endpoint protection with its cloud-assisted threat hunting and intelligence, making it a robust shield against sophisticated cyber threats.
- BitDefender GravityZone Equips businesses with a comprehensive suite of malware defense tools, including advanced EDR capabilities, to thwart threats like Dharma ransomware effectively.
First identified in 2016, Dharma encrypts files on victims’ systems and demands cryptocurrency payments for decryption. Its operators employ tactics to maximize impact and persistence, including encrypting files on local drives and accessible network shares, while deleting shadow copies to hinder recovery efforts.
Notable Dharma-Related Variants
Notable Dharma-Related Variants
- Crysis: The original strain, first detected in 2016, gained attention for targeting businesses through poorly secured Remote Desktop Protocol (RDP) ports.
- Dharma Variants: These often take their names from the file extensions they append to encrypted files, including .wallet, .onion, .gamma, .arena, and .cesar. More recent variants have used extensions such as .adobe, .arrow, .bip, and .cmb.
- Phobos: A closely related strain that shares much of Dharma’s codebase. It also targets RDP ports and uses similar encryption and ransom note methods, sometimes considered a direct offshoot of Dharma.
- XTBL: An earlier Crysis variant using the .xtbl extension, exhibiting operational similarities with both Crysis and Dharma.
Common Features Across Variants
- Delivery Methods: Unsecured RDP connections, phishing campaigns, and manual deployment once access is gained.
- File Extensions: Each variant uses unique extensions to differentiate campaigns and encrypted files.
- Ransom Notes: Typically left in files like info.txt or info.hta, detailing payment instructions and attacker contacts.
Security Recommendations
To mitigate the risks posed by Dharma and its variants:
- Secure RDP endpoints with strong passwords and two-factor authentication.
- Maintain regular offline backups of critical data.
- Use endpoint protection solutions capable of detecting and blocking ransomware activity.
For deeper analysis and updates on these ransomware strains, consult cybersecurity advisories from sources such as Broadcom and Fortinet.
Little is known about the hacker group behind Dharma. However, the code for a variant of Dharma was put up for sale in March 2020 on a Russian-language Dark Web site for $2,000. This was a meager price, given that the lowest ransom for the Dharma ransom was $1,500, with the average take per attack in December 2019 being $8,620. However, analysts confirm that it was the genuine code for the ransomware.
The code sale for the Dharma ransomware could mark the creators’ decision to stop using the system in favor of its successor, Phobos. However, the significant commonality between the two ransomware systems means that releasing the code for Dharma potentially exposed Phobos. Crysis, Dharma, and Phobos are all still operating simultaneously. However, it is not known whether they are all still controlled by the same people. It is also unclear whether the developers or a disgruntled associate made the code sale.
Dharma Ransomware-as-a-Service
Although it is difficult to tell the difference between the operating code of the three Crysis group members, there are distinguishing strategic differences. For example, Crysis uses an infected attachment on a phishing email. Dharma and Phobos use RDP to get onto targets, but there is a difference between them – Dharma is a Ransomware-as-a-Service platform, but Phobos is a developer-owned private attack package.
Ransomware-as-a-Service (RaaS) is inspired by the cloud package format, Software-as-a-Service (SaaS). In the RaaS scenario, the developers created a customer portal on its host for the Dharma software. In addition, the system presents Dharma as a toolkit. This is appealing to lone hackers or groups still learning the ropes and don’t have in-house programming skills.
The Dharma ransomware kit users have options – it isn’t a fixed service, but it offers variations on an attack. The way into a system is through the Remote Desktop Protocol (RDP). The Dharma system is a coordinator for a series of off-the-shelf system utilities. The benefit of using well-known legitimate software systems for an attack is that AV systems should ignore them as genuine activity. However, antimalware is trained to look for the coordinating program instead.
The fact that Dharma ransomware attacks aren’t all launched by the same people means that attacks can occur differently. For example, the renting hacker can manually enter into a system and copy over the installer, feed a known IP address into the portal and let the platform launch the attack, or load in a list of IP addresses and watch the service deliver the ransomware to many targets.
The benefit of splitting the duties of hacking with Dharma means that the developers cut out the laborious task of researching targets. The use of many attackers as associates also increases the turnover of the ransomware. The attacker and the Crysis group share the proceeds of an attack.
The Remote Desktop Protocol
Microsoft created the Remote Desktop Protocol (RDP) and it is integrated into Windows. This means that Dharma was specifically designed to attack computers that have the Windows operating system.
RDP is a communication protocol, and it enables someone to connect to a device and see its Desktop, so the remote computer can be used as though it is local. This is particularly useful for employees who are frequently out in the field, such as sales staff or consultants. However, it is also widely used to serve telecommuting workers.
The RDP protocol connects to TCP port 3389. Therefore, in operation, the administrator needs to activate RDP on the host computer. This starts up a receiving program that loops continually, monitoring for incoming connection requests with the port number 3389 on them.
There are security options available. The administrator can set up a password that needs to be entered by the remote user before access can proceed. Unfortunately, many administrators don’t bother with this feature. The user will still be prompted for a password but will get in by just pressing enter. This insecure setup is exactly what the Dharma ransomware is looking for.
The Dharma ransomware can easily be blocked just by setting a password for RDP access. However, password protection needs to be activated, but the password needs to be complex and not easy to guess.
Automated Dharma ransomware attacks will just drop the workflow if it encounters a password requirement. However, manually-driven attacks don’t have to stop there. The hacker can try a series of commonly used passwords or trick one of the target computer users into disclosing the password.
A Dharma ransomware attack
The variations on a Dharma ransomware attack mainly focus on the method of access. Once the installer for the ransomware is on the target computer, an attack proceeds in the same way.
The system uses Mimikatz, the Windows local user manager, NirSoft Remote Desktop PassView, LaZagne, and Hash Suite Tools Free Edition to try to identify user accounts and their passwords. It then uses the PC Hunter system diagnostics tool, GMER rootkit detector, and IOBit Unlocker to identify processes that possess files and kills them to make those files available for encryption. Finally, it uses Revo Uninstaller and IOBit Uninstaller to remove software that represents a threat to the ransomware.
All of these standard software packages are run by a PowerShell script. The ransomware bundle also includes PowerShell scripts that manage malware protection and persistence. They identify AV processes and kill them, and also unpack and then execute the ransomware.
The system uses the native Microsoft RDP client and Advance IP Scanner to identify and contact other computers on the network.
Unusually, in order to put all the software for Dharma ransomware in place, the RaaS platform shuts down the target computer and reboots it, bring up a screen locker with ClearLock, freezing out users and passing over control to the platform for the final phase of the attack. At this point, the hacker also has an opportunity to pause the attack and move about the victim’s system to explore files and steal data.
The platform unpacks the malware and tries to launch the encryption system with a discovered username and password. If that fails, the system prompts the hacker to relaunch the process manually with different target computer user credentials.
What is the Dharma encryption system?
Dharma the AES cipher with a 256-bit key to encrypt files. The key is created on the attacked computer. The ransomware also generates a unique ID for the attack. The ID and the AES key are then bundled with RSA encryption using a 1048-bit key. This protects the transmission of the key to the command-and-control server (C&C).
The system renames each file after it has been encrypted. This renaming process tags extra extensions onto the original file name. The format for this is:
.id[-].[<attacker’s e-mail>].dharma
That final .dharma extension can be different, depending on the variant that is in operation – there are about 200 variants in circulation.
Once all of the working files have been encrypted, the system generates two ransom notes. One is in plain text and is left on the hard drive; the second is in HTA format and is opened for display. This gives the victim instructions on how to proceed.
Instructions display the attack ID and tell the victim to use this in correspondence. The note also gives an email address to contact, which is the same email address tagged to the end of the name for each encrypted file.
The attacker sends the victim back a tool that generates a list of encrypted files and sends that back to the hacker. The victim then has to arrange payment. The affiliate submits the list of files through the RaaS portal, together with a Bitcoin payment, which represents a share of the ransom. With this, the RaaS returns a decryption tool with the decryption key for the RSA encryption. When the decryption tool runs on the victim’s computer, it will locate the encrypted AES key, decrypt it, and then read it in to perform the decryption of all files.
Protecting against Dharma ransomware
You can avoid paying the ransom if you have backup copies of all of your working files. However, it is also necessary to protect backup stores not to get broken into by hackers. An easy way to protect systems against a Dharma ransomware break-in is to password protect all RDP ports and institute secure VPN access for remote workers. However, there is always the danger that a Dharma ransomware affiliate could trick that password out of the user through phishing emails.
You must protect your user devices with endpoint detection and response systems that spot suspicious activity and isolate that endpoint before the ransomware can spread. It is also a good idea to get extra protection for sensitive data.
Our methodology for selecting ransomware protection
We reviewed the market for protection from ransomware such as Dharma and analyzed the options based on the following criteria:
- Account activity tracking to identify account takeover
- Anomaly detection to identify unusual activity
- Systems to suspend suspicious accounts
- Network threat detection to identify unauthorized activity
- A method to block incoming RDP connections
- A free trial or a demo that enables an assessment of the package before buying
- Value for money from a ransomware protection system that is offered at a reasonable price
Here are three system security packages that you should consider:
1. ManageEngine DataSecurity Plus (FREE TRIAL)
ManageEngine DataSecurity Plus protects sensitive data and should be deployed by businesses following GDPR, HIPAA, PCI DSS, or other data privacy standards.
Key Features:
- Ransomware Detection: Identifies ransomware encryption activities to prevent attacks.
- Process Interruption: Has the capability to block malicious processes in their tracks.
- Account Suspension: Suspends accounts exhibiting suspicious behaviors to mitigate threats.
- Endpoint Isolation: Can isolate devices to prevent the spread of security threats across the network.
Why do we recommend it?
ManageEngine DataSecurity Plus is a package of four units – each of which is available for purchase separately. As well as detecting insider threats and blocking data theft, this package can identify unusual activity in the communications between endpoints and kill processes when it detects changes to files, all of which blacks ransomware like Dharma.
This package includes a discovery module that identifies and categorizes sensitive data sources. It then protects all files with a file integrity monitor, which would spot the start of the encryption process and block Dharma or other ransomware systems.
Who is it recommended for?
The ManageEngine package is a little complicated because it is actually four separate modules that work together if bought as a suite. However, it is suitable for use by all sizes of businesses. The combination of ransomware protection, insider threat detection, and data loss prevention will appeal to businesses that store sensitive data.
Pros:
- Comprehensive File Monitoring: Offers detailed insights into file access patterns, aiding sysadmins in security management.
- Trend Analysis: Tracks access trends to enhance detection of malicious activities over time.
- Compliance Support: Includes built-in reporting features for major compliance standards like HIPAA and PCI DSS.
- Extensive Integrations: Seamlessly integrates with a variety of helpdesk, notification, and backup solutions.
Cons:
- Complex Setup: Navigating and utilizing all features requires a significant time investment to maximize the platform’s potential.
ManageEngine DataSecurity Plus runs on Windows Server, and it is available for a 30-day free trial.
2. CrowdStrike Falcon Insight
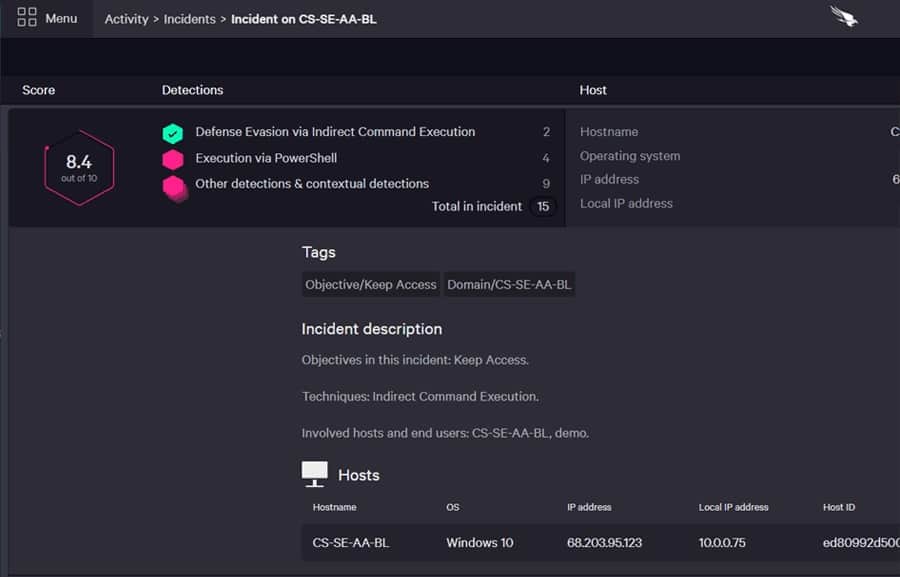
CrowdStrike Falcon Insight combines endpoint detection and response with cloud-based threat hunting and a threat intelligence feed. Each device has an agent installed on it. This software is also available as a standalone package, called Falcon Prevent. The EDR module scans for abnormal activity, so it would spot those PowerShell scripts that implement much of the setup involved in a Dharma ransomware attack.
Key Features:
- On-Device Security: Provides robust protection directly on each device, safeguarding against malware and breaches.
- Device Quarantine: Efficiently isolates compromised devices to prevent the spread of threats.
- Behavioral Anomalies Detection: Identifies unusual activities that may indicate a security threat.
- Global Threat Tracking: Enables tracking of threats across the entire enterprise, enhancing security.
- Immediate Threat Alerts: Sends alerts about potential threats in real-time, ensuring prompt response.
Why do we recommend it?
CrowdStrike Falcon Insight is a multi-layered system that implements threat hunting, informed by threat intelligence. The local, on-device agent is a fully functioning EDR that uploads activity reports to a cloud threat hunter while also providing its own investigations. That local unit gets guidance from the cloud platform but it can continue to function when isolated from the network.
The EDR can suspend user accounts, block communication with suspicious IP addresses and isolate the computer from the network. This combination of actions would shut down a Dharma attack. Once the threat is less immediate, the service can identify and remove Dharma components. Meanwhile, the threat intelligence system coordinates checks with all endpoints in the design and looks out for warnings of new malware, including other ransomware threats.
Who is it recommended for?
This system is designed for use by mid-sized and large organizations. The package joins together instances of Falcon Prevent, which is the on-device AV system. The system easily expands just by buying Falcon Prevent for another endpoint. Small businesses would find this package a little pricey.
Pros:
- Versatile Compatibility: Excels across various environments like Windows, Linux, and cloud-based systems.
- User-Friendly Dashboard: The intuitive administration console is easily accessible online, simplifying setup and management.
- Adaptive Alert System: Enhances its ability to detect anomalous behavior over time, offering improved monitoring the longer it’s in use.
- Efficient Operation: The agent’s lightweight design ensures minimal impact on system resources.
Cons:
- Trial Period: An extension of the trial period would provide additional value, allowing for a more thorough evaluation.
CrowdStrike Prevent is available for a 15-day free trial.
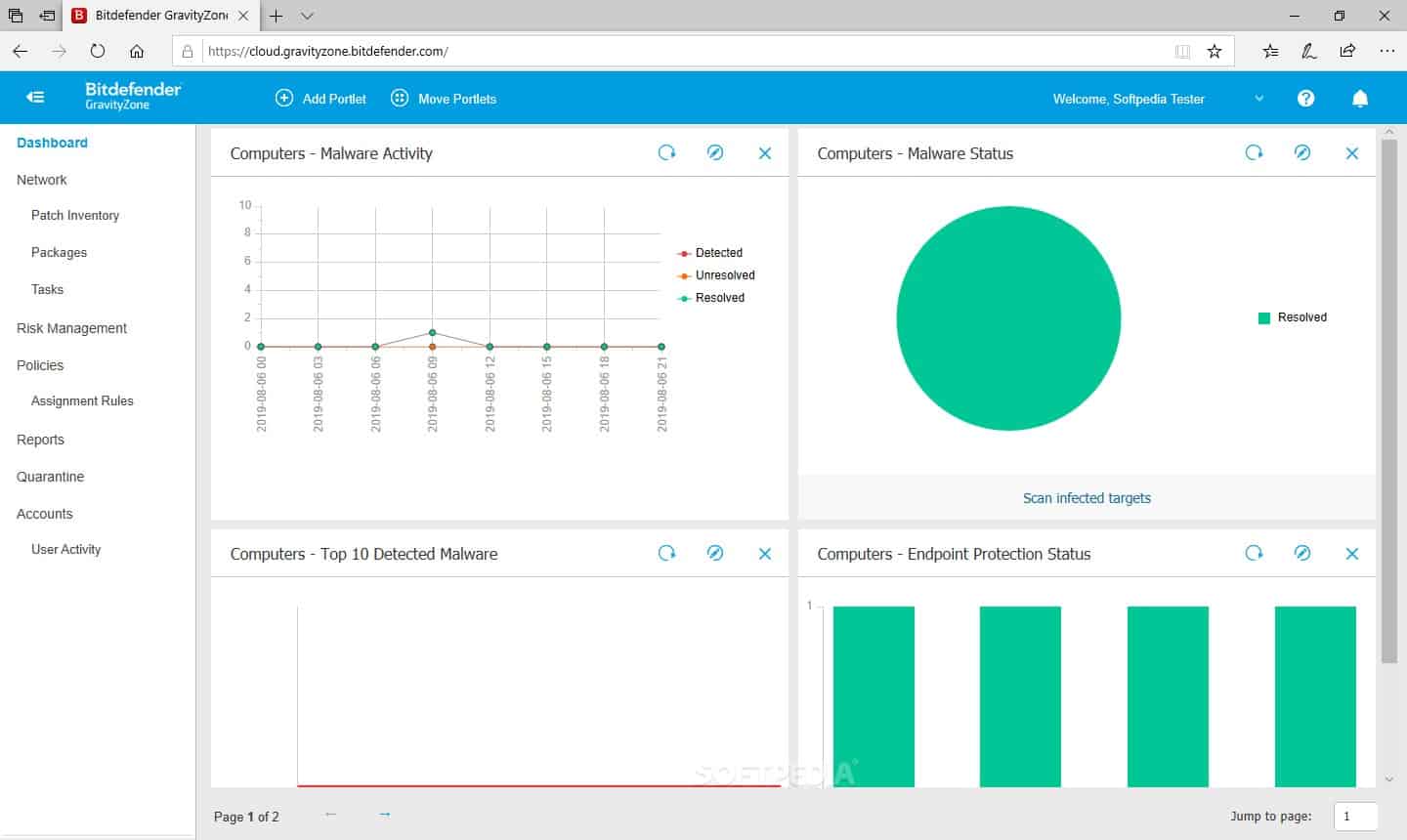
3. BitDefender GravityZone
BitDefender GravityZone includes a set of tools to guard your system against any kind of malware attack, including Dharma ransomware. The GravityZone bundle includes endpoint detection and response (EDR) to spot anomalous behavior and isolate the device before an infection can spread. It also includes vulnerability scanning, which will identify open or insecure ports. In addition, his service is linked to a patch manager, which keeps OSs and software up to date. There is also a configuration manager and a file integrity monitor in the package.
Key Features:
- Vulnerability Scanning: Identifies and reports system vulnerabilities to prevent exploits.
- Automated Updates: Keeps software and operating systems up-to-date with automatic patching.
- File Integrity Checks: Monitors file changes to ensure data integrity and spot tampering.
Why do we recommend it?
BitDefender GravityZone uses an entire armory of cybersecurity tools to battle ransomware. The package includes a backup service and a failsafe to enable data to be restored. Hopefully, the other services in the package should prevent any encryption from taking place. These steps include malware detection and file integrity monitoring.
Vital tools in the GravityZone system for guarding against Dharma ransomware are a backup manager and multi-point malware scanning. The GravityZone system scans all files several times over. As well as protecting them from unauthorized changes with the file integrity monitor, it will scan them for signs of infection before uploading them to the backup server.
Who is it recommended for?
This package is a good option for any size or type of business because its multiple functions provide good value for money. The bundle is not limited to blocking ransomware but addresses all possible threats to data, including accidental deletion or unauthorized alteration.
Pros:
- Intuitive Interface: Features a user-friendly UI that simplifies navigation and accelerates user proficiency.
- Advanced Threat Detection: Combines signature-based and behavioral analysis for comprehensive threat identification.
- Enhanced Data Security: Adds an extra layer of protection with disk encryption capabilities.
- Peripheral Control: Offers device management features, including the ability to secure USB ports.
Cons:
- Need for More Guides: A more extensive range of documentation would assist users in exploiting the platform’s full capabilities more swiftly.
BitDefender GravityZone runs on a hypervisor as a virtual appliance, and it is available for a one-month free trial.
Dharma Ransomware FAQs
Does Dharma ransomware steal data?
Dharma doesn’t steal data. However, one additional feature of this ransomware is that it provides access into the infected device to a controlling hacker for manual exploration, which could be used for data theft. Usually, Dharma encrypts files to make them inaccessible without moving them.
How does Dharma ransomware spread?
Dharma gains access by connection to a computer with the Remote Desktop Protocol on TCP port 3389. One way to block the Dharma system from gaining access is to shut down port 3389. Another way to stop it is to set up a password requirement for RDP access – the ransomware shuts down its attack processes if it is challenged for a password.
Is Dharma ransomware a service?
Dharma ransomware is a creation of an unidentified Russian hacker group and it is provided as a Ransomware-as-a-Service platform. This means that hackers who don’t have their own ransomware can launch an attack with Dharma by giving it a list of IP addresses to explore. When the victim pays the ransomware, the Dharma system processes the Bitcoin payment and withholds part of the payment as the fee for the service.