A common requirement in enterprise environments is controlling what users can access online, both for security and policy enforcement. DNS filtering addresses this need by restricting access to specific websites at the domain level, preventing pages from loading on organisational devices when they match defined rules or threat categories.
Here is our list of the best DNS filtering tools:
- ThreatLocker Web Control EDITOR’S CHOICE A flexible tool that controls and manages web access to improve your network’s security. It supports using policies to customize web access. Start a 30-day free trial.
- NordLayer Secure Web Gateway (ACCESS DEMO) The NordLayer platform offers tools to implement SD-WANs and SASE that protect multiple sites and remote workers by creating a secure virtual network over the internet. It includes a DNS filtering service in its SWG module. Get free demo.
- TitanHQ DNS Filtering This cloud-based service is part of a platform of security systems for online services, such as email systems. This tool operates as your global DNS service and blocks access to malicious sites and those that are not suitable for workplaces.
- Control D A configurable DNS filtering service that combines security, privacy, and content controls for individuals, families, and businesses.
- Twingate This cloud platform provides tools to implement Zero Trust Access or secure virtual networks and can integrate third-party DNS filtering services.
- DNSFilter This specialized platform offers per-user pricing and has an edition for managed service providers.
- NextDNS A hosted DNS-based firewall that provides out-of-the-box blocklists and lets administrators add their own banned sites for sinkholing.
- Cloudflare Secure Web Gateway This vast platform of internet security services includes a DNS filtering tool that can be combined with other edge services.
- Zscaler Cloud Firewall This growing platform provides internet and application security solutions and includes a DNS filtering unit.
At its core, DNS filtering works by inspecting domain name system requests and either allows, blocks, or redirects them based on security policies. This enables organisations to stop connections to known malicious domains before a website is ever reached, reducing exposure to threats such as phishing, malware distribution, and ransomware delivery.
In addition to blocking harmful content, DNS filtering provides valuable visibility into network activity. It helps administrators understand browsing behaviour, identify unusual traffic patterns, and reduce risks associated with users unintentionally visiting unsafe or compromised websites. It can also help defend against domain spoofing attempts that redirect users to fraudulent pages designed to steal sensitive data.
These capabilities can be applied across a wide range of environments, including desktops, laptops, mobile devices, and IoT endpoints, making DNS filtering a flexible control within broader security strategies.
This guide explores leading DNS filtering solutions available to organisations, focusing on tools that offer configurable filtering policies, real-time monitoring, detailed reporting, and integration with existing security infrastructure. Alongside blocking malicious domains, these platforms can also contribute to safer browsing experiences and help reduce malware-related risks to data integrity.
Because DNS filtering is highly scalable, it can be implemented effectively across organisations of all sizes, from small businesses to large enterprises, and adapted to different security and compliance requirements.
What is DNS filtering?
You probably already know that the Internet and the World Wide Web are not the same thing. The World Wide Web runs over the Internet. There are three technologies that define the World Wide Web: HTTPS for transport, HTML for data formatting, and the Domain Name System for addressing. The Internet is defined by the Internet Protocol, of which, the most important element is the definition of the IP address. DNS filtering interferes with the crossover points between the addressing systems for the World Wide Web and the Internet.
Web domains are user-friendly addresses for websites. However, they mean nothing to the routers on the Internet. Internet routers only recognize IP addresses. When a user enters a URL in the address bar of a Web browser, the first thing that browser has to do is find the corresponding IP address for that site.
A Web browser will look for the closest DNS Server, which is probably the one that you maintain on your network for hostnames. If you don’t have a network DNS server, the closest will be the one specified by your internet service provider (ISP). It is probable that your network DNS server only deals with local IP addresses and passes through the requests for external domains to the ISP DNS server.
The ISP can choose to block access to a specific site by not providing an IP address for a domain name. More frequently, the DNS will maintain a default domain mapping that goes to an error page. This process is DNS filtering. It is also known as “sink holing”. ISPs do this all the time – often at the direction of their governments. This is a quiet, secret way that Western governments control access to the Internet while hurling abuse at other countries, naming them repressive regimes for doing exactly the same thing.
So, when China controls access to YouTube, that’s a denial of human freedoms, when the UK government blocks access to a VPN review site, that’s responsible policing, and when a company blocks access to a porn site, that’s DNS filtering.
DNS filtering is an alternative way of banning websites within your business. Probably, the more usual method you know about is by implementing blocklists as part of firewall rules.
Commercial DNS filtering services
Your ISP probably doesn’t manage its own DNS server but forwards all requests to a specific DNS service. You can do that, too, skipping over the ISP and channeling all of your site’s DNS requests to a DNS filtering service. This is a better strategy than trying to assemble your own blacklist either in your firewall or by trying sinkholing in your own DNS server.
It is possible to implement DNS redirection within the network settings of each endpoint. So, you have a number of options over how to implement the new connection to the DNS service.
There isn’t any efficiency loss from nominating a DNS filtering service because your site’s browsers usually contact a remote DNS server to get the IP addresses for requested sites.
The Best DNS Filtering Tools
DNS filtering can be offered by businesses that specialize in that function, or it can be delivered as part of a platform of edge service.
Our methodology for selecting DNS filtering tools
We reviewed the market for DNS filtering systems and narrowed down the options based on the following criteria:
- Must be a remote, hosted, secure DNS server
- Should provide DNS-over-HTTPS or queries within a VPN for secure connections
- Should have a method to enable administrators to implement a custom blocklist
- Options to adapt DNS results according to IP address or group
- A cloud-based system that can cover remote workers and multiple sites
- A free trial, a money-back guarantee, or a demo to enable a risk-free assessment
- Value for money, represented by a price that matches the quality and extent of the service on offer
The following sections provide details on each of the packages that we selected.
1. ThreatLocker Web Control (FREE TRIAL)
ThreatLocker Web Control is a part of the ThreatLocker platform and offers an extensive web filtering solution to improve your organization’s network security. Using this tool, your administrators can apply granular controls and policies to determine who uses the web and for what. Specifically, it prevents any malware from downloading to your network’s devices.
Key features:
- Highly Flexible: Supports agent-based and agentless monitoring to suit different environments
- Prevent Phishing: Uses trusted sources like the UK Safer Internet Center to identify and block phishing sites
- Library Creation: Builds a library of prohibited sites and dynamically updates it
- Compliance: Supports compliance with frameworks like GDPR, HIPAA, and PCI DSS
- User Experience: Balances security with user experience for seamless adoption
Why do we recommend it?
One of the biggest takeaways for us is that ThreatLocker simplifies web content management and improves security – all without compromising on user experience. When users access a site that is blocked by your organization, they will be redirected to a company page showing their options if they still want to access that site. Its browser extension also makes it easy for users to request permission to use legitimate sites.
Another feature we love is the flexibility, as it supports both agent-based and agentless monitoring, which means you can also use DNS filtering for unmanaged devices. Such flexibility opens many options for organizations without requiring additional tools.
Who is it recommended for?
It is recommended for MSPs and IT administrators of medium to large enterprises. In particular, it is helpful for organizations that have BYOD policies and those that have to comply with stringent regulations.
Pros:
- Improves Security Posture: Reduces risk of malware by blocking suspicious sites
- Flexible Policies: Supports the implementation of custom policies at all levels
- Protects Unmanaged Devices: Extends security protection to unmanaged devices as well
- Compliance: Meets the compliance requirements for many organizations
Cons:
- Training: Requires training for creating policies
ThreatLocker offers custom pricing. Start a 30-day free trial.
EDITOR'S CHOICE
ThreatLocker Web Control wins the Editor’s Choice award for the best DNS filtering tool because it uses a flexible approach through agent-based and agentless monitoring to provide more options for organizations and cover a wide range of devices. Additionally, it focuses on user experience, ensuring that users don’t have to face a page with minimal information about why they cannot access a site. Requesting permissions for access is also simple. Due to these reasons, ThreatLocker is our top pick.
Download: Start a 30-day FREE Trial
Official Site: https://www.threatlocker.com/try-threatlocker
OS: Windows, macOS, Linux, Cloud/SaaS and Hybrid
2. NordLayer Secure Web Gateway (FREE DEMO)
Apps Available:
- PC
- Mac
- IOS
- Android
- Linux
Website: www.nordlayer.com
Money-back guarantee: 14 DAYS
Nordlayer Secure Web Gateway is part of a platform of edge services that was developed by Nord Security, the maker of NordVPN. The whole platform creates a secure private network to unite multiple sites, remote workers, and on-premises and cloud-based software. This is a zero-trust access service that integrates system access and application access controls into a single app. Users are admitted onto a protected network that includes its own DNS system.
Key Features:
- Secure networks: Creates SD-WAN and SASE configurations
- Secure Web Gateway: Examines incoming Web traffic
- DNS filtering: Provides more than 50 categories of Web content blocks that the administrator can choose to activate individually
- Custom DNS: The option to specify your own DNS
- Threat intelligence feed: Provides a list of infected and malicious sites that are automatically blocked
Why do we recommend it?
NordLayer Secure Web Gateway provides multiple layers of protection that include DNS filtering by category and a precise list of domains that will be locked because they are known to be infected or malicious. The blocklist comes from a threat intelligence feed and is constantly updated by research and the detection of threats by all NordLayer implementations.
The Secure Web Gateway operates from the NordLayer server. When an administrator sets up a NordLayer account, each user is given a system access app and the administrator console assigns an account to each with credentials. The administrator also allocates a list of allowed applications to each user. Access from a user to an application hub through the NordLayer server for authentication.
NordLayer Secure Web Gateway is part of a wider package of corporate protection systems that include internet security and application protection. The NordLayer service will automatically block traffic from domains that are known to be infected or host malware. In addition to this, the DNS filtering feature offers system administrators a list of more than 50 content categories that can be blocked. The full package creates a private space on the internet for companies that have multiple sites and remote users and use cloud services.
Who is it recommended for?
The package is suitable for businesses of all sizes and types. However, it is particularly appealing for companies that operate a virtual office strategy, for those that have many home-based workers, and for those that provide software from SaaS packages for their users. The system creates a secure network across the internet.
Pros:
- Constructs an internal network: The tool uses the internet as infrastructure for a private corporate network
- VPN-based: Connections are established as always-on access for remorse workers, and site-to-site systems for WANs
- Provides an authentication server: All user access attempts pass through the NordLayer server for authentication
- Creates a gateway to the outside internet: All traffic in and out of the private virtual network passes through the firewall and secure web gateway for inspection
- Dedicated IP address: A NordLayer subscription creates a unified identity for a business that really operates from many different locations
Cons:
- No self-hosting option: You can only get this package as a SaaS package
The NordLayer service is available in four plans. The lowest plan does not include the Secure Web Gateway with its DNS filtering feature. Prices are calculated per user per month, but you get a lower rate if you pay annually. The top plan has a requirement for a minimum of 50 users, but the lower three plans are available for teams of at least five members. There isn’t a free trial for NordLayer, but you can get access to a free demo.
3. TitanHQ DNS Filtering

TitanHQ DNS Filtering is a secure DNS service that limits access to websites, simply by not listing them. This strategy is able to block malicious sites that are used to impersonate legitimate websites or deliver malware. It can also be used to prevent employees from accessing sites that are not suitable for the workplace.
Key Features:
- Per-user pricing: Makes the package accessible to all sizes of businesses
- Custom policies: Add your own blacklist
- Adaptable controls: Change DNS rules for different user groups or sites
- AI assessments: Newly presented URLs are assessed
- Pre-scanned URLs: The package accumulates the research performed for other clients
Why do we recommend it?
TitanHQ DSN Filtering is easy to onboard and then provides sophisticated controls for those who invest time into tailoring the system. The package operates off-site, so you don’t need to host any software yourself. You just need to update the defaulter DNS system in the network settings of your endpoints.
TitanHQ offers a number of other security modules on its cloud platform. These include systems to protect emails systems from spam, malware, and phishing attempts. The company also offers an email encryption system and an email archiving package. The WebTitan service includes analytical tools that help administrators spot newly accessed websites that need to be blocked.
Who is it recommended for?
This package is suitable for any type or size of enterprise because its charge rate is levied per user. The system is hosted on the cloud, so you don’t need to investigate whether you have the right operating system to run it. TitanHQ provides a version of WebTitan for managed service providers.
Pros:
- Out-of-the-box controls: Apply standard blacklists immediately
- Integration with Active Directory: Adapt Web access controls according to user groups
- Individual activity controls: Bring Web access controls right down to the individual user level
- Activity reports: See how staff use the Web
- Threat detection: The TitanHQ constantly assesses new sites and blocks those that are malicious
Cons:
- A remote service: No private DNS option
TitanHQ DNS Filtering is a remote, cloud-based service and you sign up for it on the TitanHQ website.
4. Control D

Control D is a cloud-based DNS filtering platform built to give users more control over security, privacy, and web access. It blocks phishing sites, malware sources, and adult content in real time. Users can adjust filtering rules, restrict categories, and shape how internet access is handled. The service works across desktops, smartphones, and routers, which makes it flexible enough for home users as well as business environments.
Key Features:
- Customizable DNS Filtering: Lets users block website categories or individual domains to shape how internet access is handled.
- Real-time Protection: Blocks malicious sites, phishing attempts, and malware activity as it happens.
- Privacy-Focused: Helps keep user activity private while blocking trackers and ads.
Why do we recommend it?
We recommend Control D because it combines privacy protection, flexible filtering, and live threat blocking in one service. It is easy to set up, gives users strong control over what is allowed online, and works well for both personal use and wider policy enforcement in organizations. That makes it a practical choice for anyone who wants safer browsing without a complicated rollout.
The platform is built to keep user activity more private and secure. It adds protection against tracking systems and advertising networks, giving users tighter control over their data. Features such as whitelisting, blacklisting, and traffic monitoring provide more detailed control over DNS behavior. The result is a service that is straightforward to manage while still giving users meaningful control over security and privacy settings.
Who is it recommended for?
Control D is a good fit for individuals who want a safer and more private browsing experience, as well as for families and businesses that need to block harmful material or apply web usage rules. It is also well suited to users who want more adjustable DNS filtering to improve both protection and browsing efficiency.
Pros:
- Easy Setup: Simple to configure for both technical and non-technical users.
- Enhanced Security: Adds active protection against online threats.
- Granular Control: Gives users fine-grained filtering options for specific DNS requirements.
Cons:
- Limited Free Features: The trial version includes fewer capabilities than the paid plans.
Getting started with Control D is straightforward, and the service includes a 30-day free trial, so users can evaluate it before subscribing. Once registered, users receive setup guidance for configuring DNS on their devices or across the wider network.
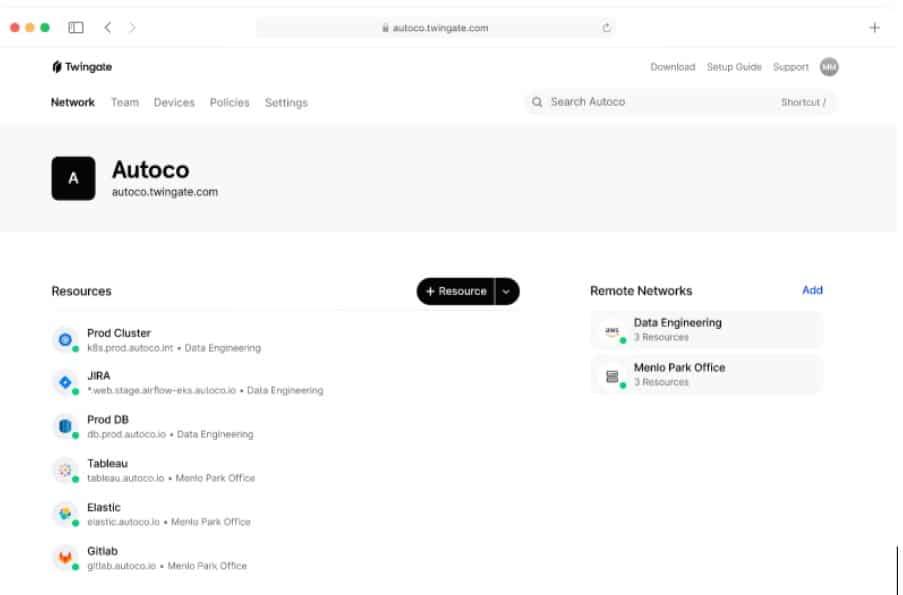
5. Twingate
Twingate is a Zero Trust Network Access system that can be used to secure connections to corporate SaaS accounts and can also provide secure access for IoT and BYOD. This package is run as a VPN hub with a gateway for traffic between the virtual network and the outside internet. The Twingate gateway can integrate a third-party DNS filtering service, such as NextDNS or DNSFilter.
Key Features:
- Combines network and application access: The user logs onto the network and gets access to a list of approved applications
- Hybrid network: Creates a seamless network with owned and internet infrastructure
- Access to hosted and SaaS applications: Treats all applications equally, no matter where they are hosted
- Connectivity for remote workers: Provides a VPN for remote access to the corporate network
Why do we recommend it?
Twingate is a similar system to Nordlayer because it is, essentially, a VPN service with integrated access rights management. This platform offers you the tools to create an SD-WAN or a SASE. The key difference between those two architectures is a cloud firewall, which Twingate offers with a secure Web gateway feature.
This package provides a single sign-on environment for corporate users. The user signs in to the Twingate app once and then access rights to all approved applications flow through. The administrator allocates applications to users, and access to any other system just isn’t possible. Users can’t break out of the controls of the Twingate system.
Who is it recommended for?
Twingate is a large platform of edge services, so it caters to a wide audience. The service offers a free plan, called Starter, which is, essentially, a team VPN package. Higher plans successively add on more features up to a complete virtual network with a secure gateway.
Pros:
- Expandable service: Connect in extra services from third parties, such as a DNS filtering package
- Device posture management: Checks each device for security risks before allowing it to connect
- Integrations for mobile device management: Connects to Jamf, Kanddji, and other tools
- Integration with other security tools: Crowdstrike and SentinelOne
Cons:
- DNS filtering is not native: Requires a third-party tool
Twingate isn’t an out-of-the-box system. It provides tools so that you can create your preferred security architecture. Therefore, you should examine all the facilities in the package closely and work out how you will slot your secure virtual network together. Fortunately, you can use a 14-day free trial to play with the services on the platform and try out all the possibilities.
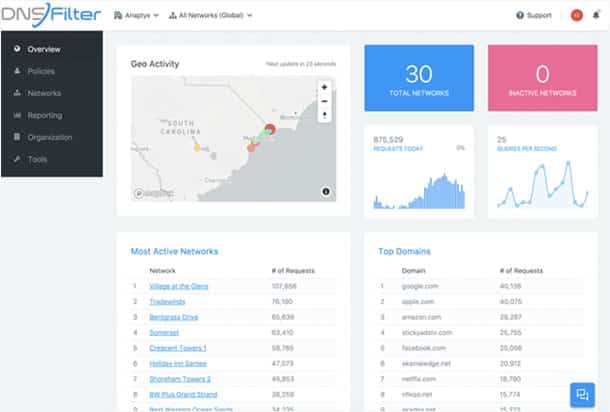
6. DNSFilter
DNSFilter is one of the external DNS filtering systems that can integrate with the Twingate platform. However, the tool works very well as a standalone service. This package allows connections over TLS/HTTPS for security and its blocklist is derived from a threat intelligence feed that is constantly updated. This blacklist is calculated through the use of AI that scans all the websites requested by the customers of the DNSFilter service and identifies malicious pages.
Key Features:
- Secure connections for DNS queries: Uses DNS-over-HTTPS
- Enables content filtering: The administrator can set up a keyword list for content to ban
- Can protect applications: Not just for browser communications
Why do we recommend it?
DNSFilter is a very advanced system. It provides a blacklist, allows content filtering, and it will automatically detect malware, phishing attempts, and botnet activity. You can specify the DNS server in your network’s settings on the DHCP server, in your firewall, or gateway. The tool uses Zapier to connect to more than 3,000 software systems, not just browsers.
The DNSFilter system is a good choice for protecting a dispersed team. Set up remote computers to use the DNSFilter system, and the highest plan also enables the DNS service for mobile devices running iOS or Android. The tool integrates with Active Directory and you can set up different DNS filtering policies for users and groups. The system also provides activity logs for analysis and compliance reporting.
Who is it recommended for?
This system is suitable for businesses of all sizes. It offers a subscription rate per user, which makes it scalable, and it will particularly appeal to businesses that operate a virtual office or have many remote workers. The DNS filtering process involves multiple stands that include administrator-specified blocks on domains, domain types, keywords, or content. There is also an edition for managed service providers.
Pros:
- Flexible filtering rules: Apply different rules to different groups or users
- Mobile device protection: Extend the service to your roaming and home-based users
- Can partner with Twingate: It also works well as a standalone service
Cons:
- Doesn’t provide a unified IP address for the entire organization: This isn’t like the virtual network options on the list
This system is easy to set up, although you will have to insert new network settings into each of the devices of remote users. Those devices can be computers running Windows or macOS or mobiles with iOS or Android. You can examine the DNSFilter system with a 14-day free trial.
7. NextDNS
NextDNS is a proxy service that implements DNS filtering. This platform has a Free edition, which will interest small businesses. The company explains its service as a cloud-based firewall. This system will block trackers and adverts, covering all applications that access the Web. The system is also available as a parental control system for homes.
Key Features:
- Automatic ad and tracker blocking: Covers all applications that access the Web
- A threat intelligence feed: Identifies infected and malicious websites
- Blocks adult content: Prevents employees from accessing inappropriate content
Why do we recommend it?
NextDNS is a good choice for both home use and for businesses. The service needs very little set up and almost no administration. It was designed for use by people who have almost no technical skills. This system is able to identify threats even when the domain involved is newly registered.
The tool will automatically block sites that are not suitable for work. These include social media sites, such as Facebook and Tinder. All activities are logged for analysis and the administrator is able to see activity summaries in the Web-based console.
Who is it recommended for?
The Free edition is marketed for home use. However, it could also be suitable for small businesses. The plan is limited to processing 300,000 DNS queries per month. The Pro edition is also billed for personal use, but it has no limit on traffic volume and costs 10 percent of the price of the Business and Education editions.
Pros:
- Secure connections: DNS-over-TLS and DNS-over-HTTPS
- Activity logging: Summaries shown in the console
- Also protects mobile devices: Set it up on Android or iOS
Cons:
- DNS filtering only: Doesn’t manage application access
The only difference between the three paid plans is that the Pro edition, which is a great deal cheaper than the other two, doesn’t come with professional support. There isn’t a free trial, but you can sign up for the Free edition to examine the system’s performance.
8. Cloudflare Secure Web Gateway
Cloudflare Secure Web Gateway is offered by one of the leading internet security providers in the world. Cloudflare runs a free DNS service that is available to anyone, you just need to specify 1.1.1.1 as the network DNS service. However, that system doesn’t provide DNS filtering. For that, you need to sign up for the Secure Web Gateway.
Key Features:
- Operates as a firewall: Automatically blocks malware, phishing, and malicious URLs
- Customizable rules: Add in your own blacklist
- Threat intelligence feed: A comprehensive list of malicious sites
Why do we recommend it?
Cloudflare Secure Web Gateway is a very fast and competent DNS filtering service. This package is delivered from the Cloudflare server and can be combined with other Cloudflare products, such as DDoS protection and WAN optimization. There is also a SASE package available.
Cloudflare is a well-known and widely-used platform. The Secure Web Gateway is just one of the products available from the provider. The DNS filter offers categories of websites that the administrator can activate for blocking. It can also implement selective filtering per endpoint or port.
Who is it recommended for?
Cloudflare offers a Free plan for the Secure Web Gateway that has almost all the features of the paid plans. Paying subscribers can opt for a month-to-month service or sign up for a yearly contract. The service can be combined with other Cloudflare products.
Pros:
- Site categories: Presents a list of website types to block
- Selective rules: Write different rules per endpoint or protocol
- Network-level policies: Create different defense strategies per site
Cons:
- A large platform: Cloudflare has a lot of services that you can add on
The Free plan of Cloudflare Secure Web Gateway is almost as good as the paid version, except that it is limited to protecting three sites. You can get remote browser isolation (RBI) with the contract plan and that hosts the browser on the Cloudflare server, giving the user a remote view on it. Sign up for the Free plan to get started.
9. Zscaler Cloud Firewall
Zscaler Cloud Firewall is an edge platform that includes a DNS filtering service. This package implements a secure DNS service that enables filtering thanks to category controls, a threat intelligence feed, and custom policies created by the administrator.
Key Features:
- DNS tunneling: Creates a secure channel for SNS queries
- Intrusion prevention system: Scans incoming packets for signs of suspicious activity
- SSL offloading: External communications are terminated and decrypted by the firewall
Why do we recommend it?
Zscaler Cloud Firewall is one option on the Zscaler platform. It can be combined with SD-WAN or SASE configurations and offers traffic management features, such as DDoS protection and WAN optimization. The system can also be combined with application access controls in a zero trust access strategy.
Zscaler offers many tools for connection security that expand into application protection and user authentication. By tightening up network access through secure internet links, formed by VPNs, the system reduces all points of entry to the Cloud Firewall. This makes the Cloud Firewall package an essential element in any virtual WAN strategy.
Who is it recommended for?
Zscaler is a platform of tools for large businesses. The company no longer publishes its prices, which is a factor that will deter small businesses from inquiring. The platform offers a range of strategies that can be assembled from building blocks in different configurations.
Pros:
- Preset filters: Removes standard malicious threats
- Anomaly detection: Scans site code for identifiers of known malicious content
- A hybrid solution: Protects on-premises and cloud-based assets
Cons:
- No price list: This will deter small businesses
Zscaler doesn’t offer a free trial. However, you can request a demo to investigate how you could use all the tools on the Zscaler platform.