One of the best ways of securing data is to render it unusable to anyone but its owners and other authorized users. And one of the best ways of doing that is with the help of data encryption tools
The two tools we are about to see, DriveCrypt and Endpoint Protector, are the most used ones on the market.
In this post, we will compare them, head-to-head, to help you decide the best one for you – in case you are in the market for one.
What is a data encryption tool?
A data encryption tool is a security tool that prevents unauthorized users from accessing data – primarily by “scrambling” it so it can’t be read without the proper key to unlock the encryption. And even if they do manage to bypass the security of such a tool, the tool renders any data on the compromised disk unusable.
The data encryption tools tackle unauthorized data usage by using access management controls like usernames and passwords to perform the encryption/decryption process. Meanwhile, data encryption is used to scramble the data so that even if a hacker were able to bypass the first obstacle, they still wouldn’t be able to read the data they had stolen from protected disks.
These encryption tools also protect the data in transit – instead of the data at rest on the disks. They can also save data when they are stored in network storage devices and USB storage devices.
DriveCrypt and Endpoint Protector are two tools that protect users’ data as such. First, however, we will look at their features as not all disk encryption tools come with the same features.
DriveCrypt – Product Highlights
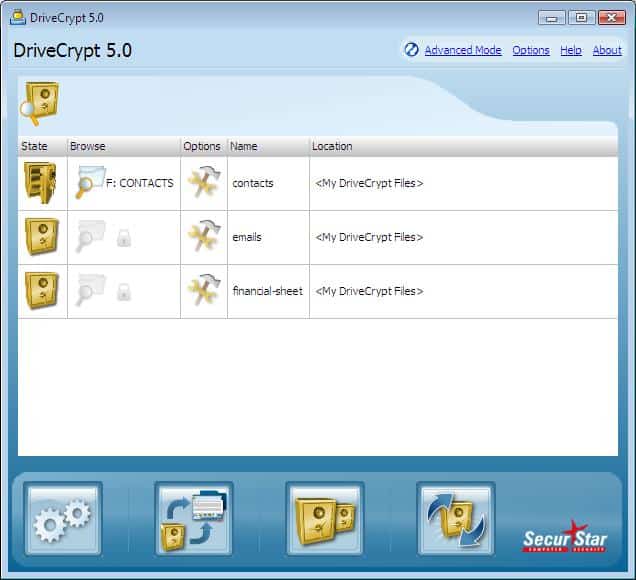
DriveCrypt is an easy-to-use data security tool that protects proprietary data on devices like laptops and desktops.
Key information
- DriveCrypt encrypts containers, partitions, and external devices like external disks and USB sticks.
- The tool uses 1344 Bit ultra-strong encryption – military-Strength disk encryption using reliable cryptographic algorithms.
- It can hide data in fake disks or music files – to pose another security barrier.
This tool works by encrypting data on a hard disk and automatically decrypting it before it is loaded into memory when an authorized user needs to access it. The data is also automatically re-encrypted when stored on – or written back onto – the hard disk. It is a transparent tool that means users do not require changing their working habits as they work on their computers. Applications, too, do not require re-configuration or special programming to access and store data.
As the data is caught “on the fly,” as it moves back and forth between the memory and the hard disk, there is no need for any manual intervention – like having to input passwords or ask the tool to encrypt/decrypt the data.
It is easy to install and deploy with minimal intervention or even user training required. This makes it the ideal data encryption tool for any type of organization – big or small. It can even be deployed in networks where there are a large number of users working remotely. It saves resources, too, as only individual files are decrypted at a time and not the entire disk.
Pros:
- Very easy to use – great for non-technical users
- Lightweight – uses little resources
- Ideal for smaller businesses
Cons:
- The interface could use improvement
- Not ideal for enterprises
DriveCrypt can be used to protect any type of data – business plans, client data, product prototype information, confidential memos, stock information, and anything else a business might deem top-secret data.
Finally, DriveCrypt can encrypt hard disks and even create virtual container files that store encrypted information.
Endpoint Protector – Product Highlights
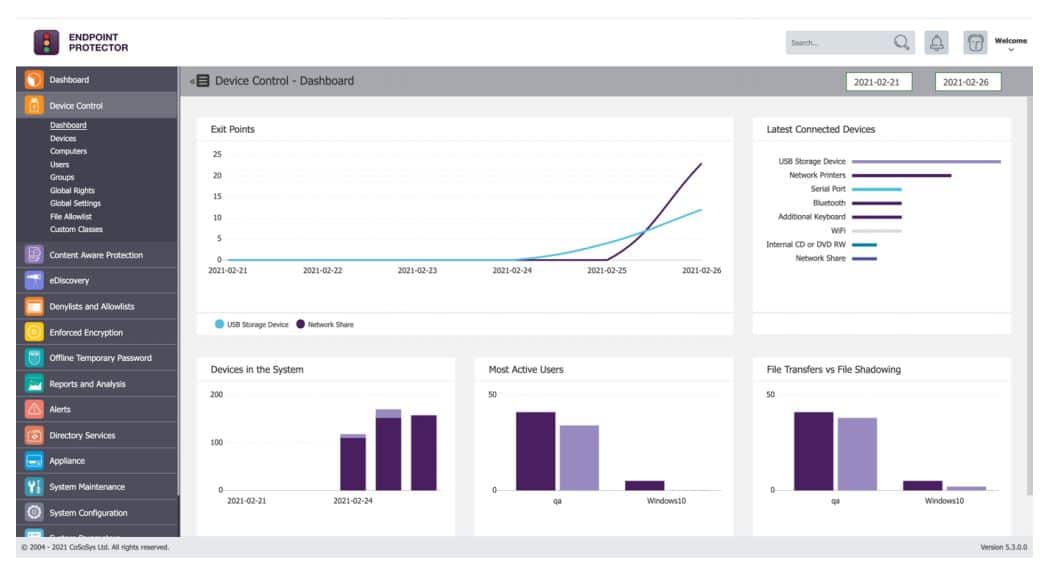
Endpoint Protector is another data encryption tool used “to protect high-value data from persistent security threats and challenges.” It is an easy-to-use, cross-platform encryption solution that offers data loss prevention (DLP) for large and small enterprises.
Key information
- Endpoint Protector is an advanced all-in-one DLP solution for Windows, macOS, and Linux.
- It is easy to set up and comes with predefined policies which allow for quick deployments.
- Available for deployment in cloud services like Amazon Web Services (AWS), Microsoft Azure, or Google Cloud Platform (GCP).
This tool comes with Enforced Encryption – which allows for the extension of Device Control policies and makes sure any data transferred to USB drives is automatically encrypted.
Once an administrator enables this Enforced Encryption function, any USB device connected to the Windows or macOS laptop or computer – where the tool has been installed – automatically starts to install the EasyLock encryption app and requires the user to create a password.
Once the installation of EasyLock is complete, the user can copy files to and from the USB drive where they are locked away inside the encrypted container of the device and can’t be accessed by anyone other than the owner – who has to know the password.
Network and security administrators can centrally manage encrypted devices – they can change users’ passwords, reset devices, and even send messages to them. In addition, they can use eDiscovery – a feature for scanning data at rest to discover, encrypt, and delete any sensitive data. They can trigger this feature for explicit content and context inspection through manual or automatic scans.
This means the administrators can scan for Personal Identifiable Information (PII) – like Social Security Numbers, financial information, and personal data – using eDiscovery and then automatically have it protected with Endpoint Protector.
And then, we have the Insider Threat Protection Prevent feature, which stops data loss or theft by monitoring activity related to device usage and file transfers. Administrators can track what sensitive data leaves an enterprise and plug that breach.
Pros:
- Custom security policies can be based on the user rather than the machine
- Automatically assesses risk based on vulnerabilities found on the endpoint
- Can alert to improper file access or insider threats (Acts as a DLP solution)
- Prevents data theft and BadUSB attacks through device control settings
Cons:
- Would like to see a trial version available for testing
Finally, Endpoint Protector can be used to comply with regulations like HIPAA and GDPR, thus ensuring the enterprise isn’t exposed to any liabilities or lawsuits.
DriveCrypt vs Endpoint Protector: Feature Comparison
| DriveCrypt | Endpoint Protector | |
|---|---|---|
| Who is it for? | Any business - big or small looking for DLP | Any company - big or small looking for DLP |
| Main use | Hard disk encryption | Enforcing USB drive encryption |
| Ease of use | Easy to use | Easy to use |
| Available | Cloud (SaaS), web-based, Windows - 32 and 64 bit Windows: Windows 10 Win 7 / Win 8.x Server (2003/2008/2012) | Cloud, SaaS, Web-based, Mac (Desktop), Windows (Desktop), Windows (On-Premise), Linux (On-Premise) |
| Features | Applications security and vulnerability protection | Data Loss Prevention, Encryption Software, Risk Alerts / Escalation, Compliance Management, Real-Time Reporting & Statistics |
| Unique features | Steganographic data camouflage | Encryption extends to the cloud and other devices |
| Modules | Hides data in fake disks or music files and encrypts containers, partitions, and external devices | Endpoint protector holds feature-rich modules within it. The four primary modules are: Device Control: To manage all devices, their permissions, policies, and settings. Content-Aware Protection: For inspecting and controlling data in motion. Enforced Encryption: For automatic USB encryption. eDiscovery: For scanning data at rest |
| Encryption technology | 1344 Bit Military Strength disk encryption | Government-approved 256bit AES CBC-mode encryption |
| Free Trial | 30 Days Free Trial | Demo |
DriveCrypt vs. Endpoint Protector
Let’s now go ahead and have a head-to-head comparison of the two products:
Who is this data encryption tool for?
DriveCrypt is for any type or size of enterprise as all of them – from a small company to a large international firm with thousands of users in the field – can effectively protect their valued digital assets using this disk encryption product.
The same goes for Endpoint Protector – it is the ideal data encryption tool for small and big businesses alike.
Mainly used for
DriveCrypt protects data that is stored in disks. It has a high-speed, seamless, and accurate “on the fly” disk encryption process that ensures information is protected at all times – without sacrificing user experience (UX).
This is in contrast with other products – that claim to also encrypt/decrypt data “on the fly” – do so to entire files and load them into memory; thus, creating bottlenecks and even posing security risks.
Endpoint Protector offers an advanced cross-platform DLP solution for macOS, Windows, and Linux computers and Thin Clients used with removable storage devices. It is used to stop unintentional data leaks, protect from malicious data theft, and get control of portable storage devices.
Security focus
DriveCrypt allows both the encryption of an entire hard disk partition and the creation of a virtual container file that stores all the encrypted information.
Furthermore, the DriveCrypt (Plus Pack edition) can create invisible disks inside that container or partition.
Administrators must define two passwords per container – the invisible disk password gives access to the working disk, which is hidden in the unused area of and “outer” disk. In contrast, another password provides access to the pre-setup DriveCrypt volume. This is because an administrator would want others to believe that the only data in the container or partition is stored.
This “fake” volume becomes useful when someone is forced to reveal a password – they’d simply show them this fake volume.
In contrast, administrators can use Endpoint Protector Device Control to restrict what can be connected to USB and other ports.
With Endpoint Protector being offered as a hardware or virtual appliance, it can be set up in minutes and start covering any type of connected device that has these ports – it automatically secures data copied on USB and other storage devices with an AES 256 bit encryption.
Administrators immediately start remotely monitoring USBs, and peripheral ports, from a simple web-based dashboard that, incidentally, has no UX impact on the protected devices. They can also set policies that cover – Windows, macOS, and Linux machines.
Moreover, the tool’s responsive management interface allows administrators to manage these policies and check statuses and reports from any device, a desktop, tablet, or mobile device.
Ease of use
The DriveCrypt data encryption tool requires minimal administration and user training. In addition, disk encryption is completely transparent, requiring no change in how users work on their computers.
When it comes to Endpoint Protector, too, predefined policies are available for quick, hassle-free deployments – seamless deployment with an intuitive interface and set-up process. It fits any company’s needs with multiple deployment options and integration capabilities. In addition, it is cross-platform, password-based, easy to use, and very efficient.
And so, we can say that both tools are easy to install, administer, and use.
Unique features
DriveCrypt uses particular steganography functionalities – it can hide sensitive information in music files. This way, only authorized users, who know what to look for, will be able to access the secret information, while anyone else will only find “harmless music” in storage.
With the HOT Disk option, DriveCrypt can also optionally automatically request users’ authentication data as soon as a USB device is inserted. When it is removed, all the data is automatically made inaccessible to unauthenticated users.
Endpoint Protector is a genuinely scalable tool that integrates well; it offers encryption for cloud storage, local folders, and even legacy storage devices like CDs and DVDs. A stand-alone version of this tool is also available for those looking for basic features – this means that this tool can be adopted into, and used in, almost any conceivable architecture.
Reports
Like the other versions, DriveCrypt Plus Pack Enterprise (DCPP Enterprise – another version of DriveCrypt) too provides centralized management and reporting. This reporting is a way of getting in-depth insight into the current encryption environment; this information is helpful for administrators and auditors.
Information such as drive status, assigned users, and login status can be easily obtained using these reports that can also be exported in common standard formats.
With Endpoint Protector, the reports and analysis monitor all users’ activity related to device use with a robust reporting and analysis tool. Logs and reports can also be exported. The tool’s responsive management interface allows managing policies and checking reports from any device, from desktop to tablet. Logs and reports can also be exported to SIEM solutions.
Security and encryption technology
DriveCrypt – uses 1344 Bit Military Strength disk encryption; it also uses the best and most proven cryptographic algorithms like AES, Blowfish, Tea 16 (and 32), Des and Triple Des, Misty 1, and Square.
Just to be 100 percent sure, DriveCrypt can be used to wipe free space on a disk to ensure that deleted files can never be recovered – even by special disk recovery tools.
And what’s more – if a user leaves the organization, the encrypted data on their PC can be quickly recovered and restored in a decrypted state by the administrator who uses a Master Password or a Local Administrator Password.
Endpoint Protector – uses US government-approved 256bit AES CBC-mode encryption. Their EasyLock USB Enforced Encryption application, combined with the Endpoint Protector tool, allows IT Administrators to extend their Device Control policy and make sure all confidential data transferred to USB storage devices is automatically encrypted.
Users can use a secure password to transfer confidential data safely. Moreover, additional valuable features allow administrators to remotely send messages to users, request a password change, or wipe any personal data in cases where a device is lost or stolen.
Support
DriveCrypt – they offer a FAQs page, ticket-raising capabilities, a support form, and downloadable manuals. In addition, they have a separate after-purchase page to register the tool.
Endpoint Protector – offers a technical support ticket portal, knowledge base for products and advice, a DLP testing tool, and consultancy services.
Prices
When it comes to DriveCrypt, there are three versions or packs to choose from – each with a selection of features and set prices:
DriveCrypt Disk Encryption is €39.95, DriveCrypt Plus Pack is €125.00, and the DriveCrypt Plus Pack Enterprise is €94.95 – all of which can be purchased from their sales page.
Endpoint Protector, on the other hand, requires clients to contact them so that they can “tailor a plan specifically for your needs”.
DriveCrypt vs. Endpoint Protector: The Verdict
Well, as we have seen, these two tools function as two different encryption tools. While they both help with DLP, DriveCrypt is the tool of choice for encrypting hard disk drives, while Endpoint Protector is used to making sure that data stored on USB drives cannot be deciphered – even if the device is stolen.
Therefore, it would make sense to have both tools in play when protecting data on a network – Endpoint Protector to keep the data safe on users’ devices and DriveCrypt to defend it when it is on the go.
But, if we must choose one, we would have to go with Endpoint Protector because of its features, including monitoring and controlling enterprise data at rest and while in motion.
Let us know what you think; leave us a comment below.




