ESET and CrowdStrike are two notable names in endpoint security, each originating from distinct backgrounds. ESET boasts a long-standing presence in cybersecurity, transforming one of the earliest antivirus solutions into a comprehensive endpoint security suite. In contrast, CrowdStrike, a newer player, started fresh by focusing on vulnerability scanning and intrusion detection, bypassing the traditional antivirus model.
Both ESET Endpoint Security and CrowdStrike Falcon aim to safeguard endpoints, such as computers and mobile devices, rather than focusing on network-level or gateway protections. This form of security serves as a critical last line of defense, complementing other layers of protection but not replacing network security measures.
The nature of cybersecurity threats has shifted significantly over the last decade. Hackers have increasingly targeted even modest corporate networks for malicious purposes, such as crypto mining, botnet operations, and identity cloaking. These threats turn compromised systems into tools for large-scale cyberattacks.
Organizations must prioritize protecting sensitive data stored within their infrastructure. Data breaches can lead to severe consequences, including legal penalties, loss of business credibility, and the erosion of customer trust. Compliance with data security standards is essential for maintaining partnerships and customer relationships, making endpoint security indispensable.
ESET Endpoint Security and CrowdStrike Falcon are both designed to combat tampering, data theft, and misuse when other security measures fail. Despite not ranking among the top five endpoint security vendors, alongside giants like McAfee, Symantec, Kaspersky, and Trend Micro, ESET and CrowdStrike stand out for their innovative approaches and reliable solutions. Their commitment to advancing endpoint protection makes them worthy of consideration for businesses aiming to strengthen their cybersecurity posture.
ESET Endpoint Security
ESET began trading in 1992. It is one of the oldest cybersecurity operations in the world. The company is based in Slovakia and its nationality has made it unable to achieve the same levels of brand recognition that its contemporaries in the USA, such as McAfee and Symantec have enjoyed. However, away from the spotlight, ESET has been one of the pioneers of cybersecurity since its inception. ESET currently has offices in 22 countries worldwide and R&D labs in 13 countries.
ESET terms its security product an “endpoint protection platform” (EPP). This refers to the construction of the Endpoint Security product as a series of modules rather than a single piece of software. That package needs to be installed on each device that is to be protected. ESET security software installs on Windows, Linux, Mac OS, iOS, Microsoft Azure servers, and VMWare virtualizations. However, the ESET Endpoint Protection name is only applied to the security software that the company produces for Windows, Mac OS, and Android. Solutions for other operating systems, however, also work on the EPP architecture and can be managed jointly from a common remote console.
The platform was designed to prevent the damage caused by ransomware, detect the operations of fileless malware, intrusion attempts and zero-day attacks. The company has adapted its original lab-based threat detection strategy to harness each installation of its software as a sensor. The first incidence of a new attack gets notified to the ESET server, which passes on the news to all of the other instances of ESET Endpoint Security running around the world.
The intelligence network is called ESET Live Grid. It is one of the three pillars of the ESET system. The next pillar is AI machine learning techniques that identify a baseline of regular activity on an endpoint and then monitor for anomalous behavior. The third pillar is the human expert pool of the company. This is the team that would have provided all threat intelligence under the old AV model.
The sensor tactic points to the existence of a threat signature database in the platform. Each instance is going to need to store all of the threat-protection tactics that it receives from the central information distribution point.
The ESET website explains the Endpoint Security strategy as a three-phase process: pre-execution, execution, and post-execution. The “execution” in these headings refer to the launch of an attack. So, pre-execution tasks include preparing backups and rollback points, system sweeps for suspicious activities and recognized malware files (which is a typical AV activity) and the identification of services that are likely to be targeted by malicious intruders.
The execution-phase tasks involve sandboxing newly installed software in a test environment/system emulator. The software also monitors known entry points and hiding places of malware and blocks their activity when it seems that the hidden malware has launched.
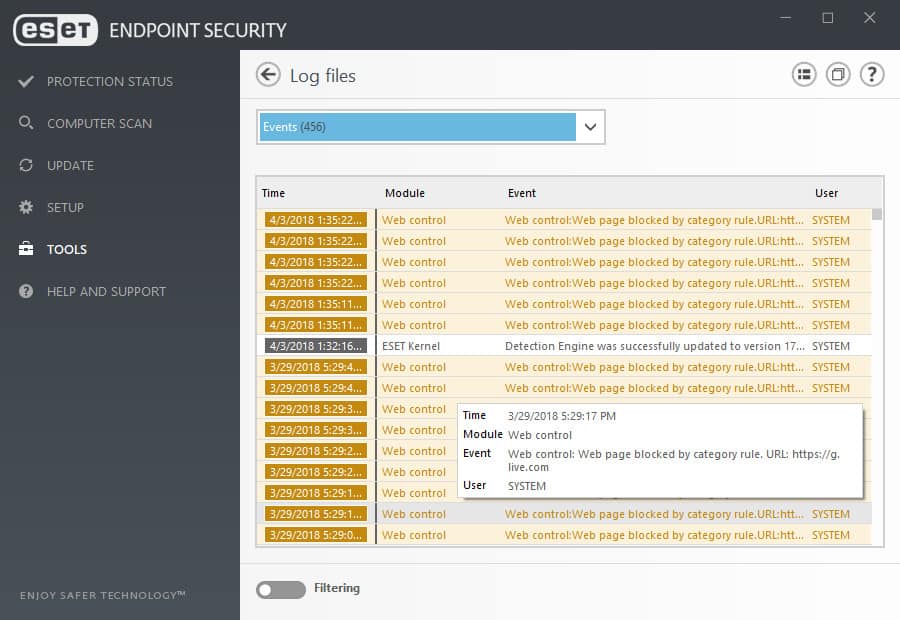
Post-execution activities involve restoring data, files, and software to their original states in case the malware wasn’t blocked quickly enough. This phase also includes the logging of attacks and the actions taken to block them plus the reporting of these events to the Live Grid system.
The ESET EPP includes eight protection systems:
- Machine learning – a feature of ESET technology since 1997.
- Advanced memory scanning – spots suspicious processes when the execute.
- Ransomware shield – specifically hunts for ransomware and blocks it before it causes harm.
- Exploit blocker – a vulnerability scanner.
- Network attack protection – what used to be called a firewall.
- DNA detections – a threat vector database.
- HIPS – a host-based intrusion prevention system that scans log files for records of malicious activities and protects those logs from tampering.
- UEFI scanner – monitors the Unified Extensible Firmware Interface (UEFI) for interference.
The console for the endpoint security system is an on-premises tool. It installs on Windows or Linux. The management dashboard enables the system administrator to see events on an individual endpoint of consolidated reports that describe the performance of the ESET software on all protected endpoints on the network.
Pros:
- Excellent dashboards – highly customizable with visual displays
- Leverages HIPS techniques to uncover threats by their behavior, not signature
- Can prevent bot attacks and identify threats by looking for C&C messages on the network
- Available as a cloud-based SaaS, or on-premise
Cons:
- Many features are tailored to medium to large-size networks, smaller networks may not use all features available
- The admin console is only available on-premise
CrowdStrike Falcon

CrowdStrike started up in business in 2011. The company initially worked as a cybersecurity consultancy and was involved in identifying and analyzing some of the famous advanced persistent threats that were uncovered in the United States during the early to mid-decade. CrowdStrike Falcon was developed in order to codify the expertise of the company’s cybersecurity consultants. Packages also include access to human expertise, which attracts more business to the company’s consultancy wing.
The CrowdStrike Falcon system is a hybrid on-premises/cloud-based solution. The actual protection work is carried out by an agent, which is the installed software. The cloud platform coordinates the activities of all endpoint agents, giving a systems administrator a console from which to monitor activity.
Falcon is an endpoint protection platform (EPP), much in the same way as the ESET system. The platform includes six modules:
- Falcon Prevent – Next-gen antivirus software.
- Falcon Intelligence – A threat intelligence engine.
- Falcon Insight – Endpoint detection and response.
- Falcon Overwatch – Threat hunting by human experts.
- Falcon Discover – A vulnerability scanner.
- Falcon Device Control – A monitoring system for USB memory sticks.
Customers don’t have to implement all of these modules because CrowdStrike markets Falcon in four editions:
- Falcon Pro – includes Falcon Prevent and Falcon Intelligence.
- Falcon Enterprise – includes Falcon Prevent, Falcon Intelligence, Falcon Insight, and Falcon Overwatch.
- Falcon Premium – includes Falcon Prevent, Falcon Intelligence, Falcon Insight, Falcon Overwatch, and Falcon Discover.
- Falcon Complete – A managed endpoint security service that includes the resources of all modules.
The base edition, Falcon Pro would probably be enough for many organizations. The deal includes what would traditionally be regarded as an anti-malware system and a firewall, which are the main elements of Falcon Prevent. The Falcon Intelligence module combats intrusion, which is harder to detect. An intrusion prevention system (IPS), such as Falcon Intelligence watches the activities on the protected device to detect suspicious behavior. The tool also includes automated remediation actions.
Threat strategies discovered by Falcon Intelligence get shared with the community through updates to the threat databases running as parts of other Falcon installs around the world. CrowdStrike analysts also use this intelligence to adjust the performance of the Falcon software.
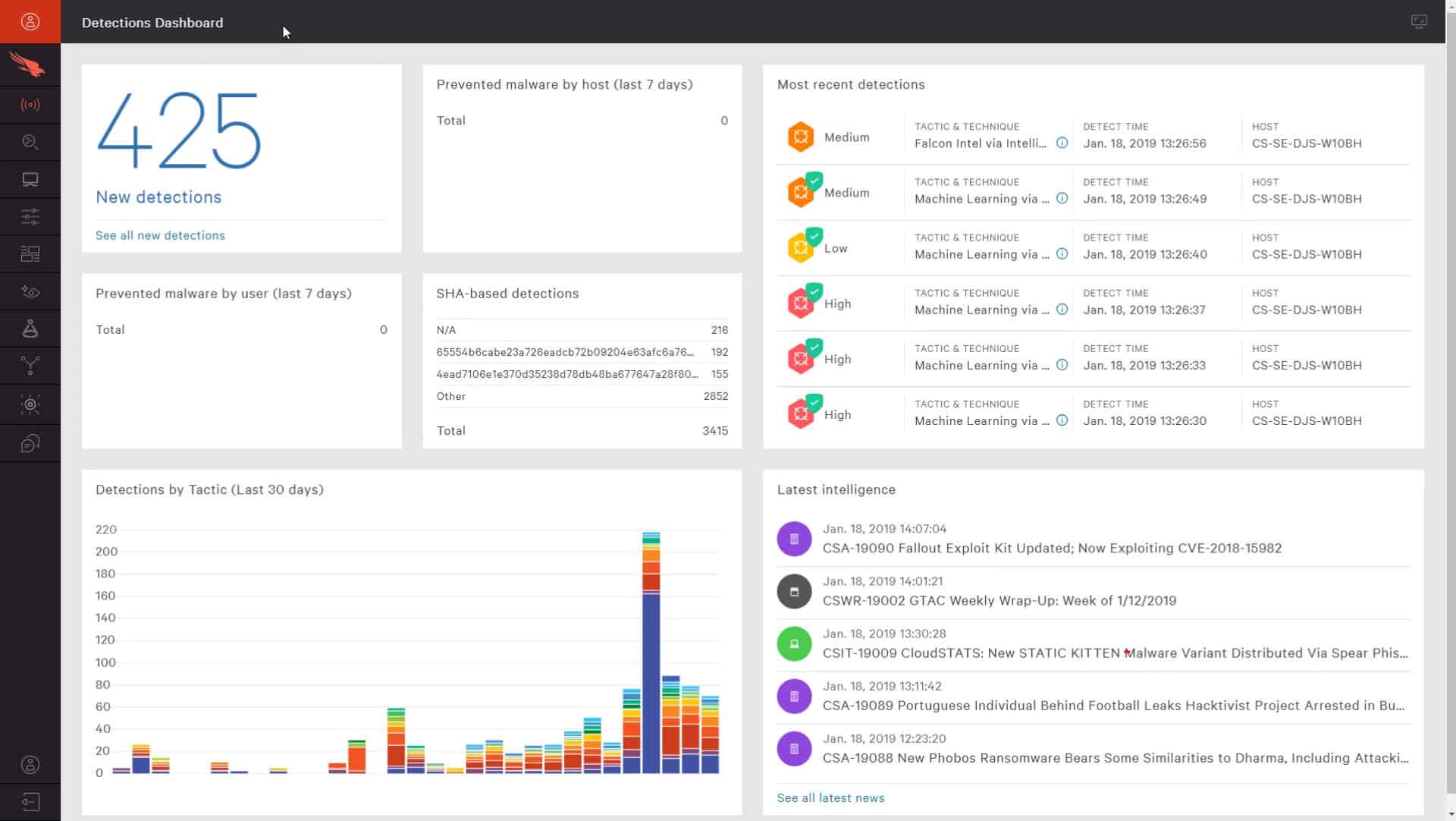
The Falcon Enterprise edition includes Falcon Prevent and Falcon Intelligence, plus Falcon Insight and Falcon Overwatch. Falcon Insight searches for evidence of advanced persistent threats (APTs). These intrusions are long-term unauthorized invasions of the system with the hacker setting up an account for regular access. Falcon Overwatch involves the human intervention of CrowdStrike analysts who look for intrusion evidence that the automated hunter might have missed.
The Falcon Premium edition adds on the Falcon Discover module. This is a vulnerability scanner. It will search the endpoint for security weak spots and tighten them up. The protection of log files is particularly important because these offer a rich source of system activity. Hackers aim for these files and remove records of their activities to hide their presence. Other factors, such as abandoned accounts and unprotected browsers get special attention to harden the security of the endpoint.
The Falcon Complete package is a managed service. Customers who opt for this edition of the CrowdStrike Falcon system don’t need to maintain a system security tram. The Falcon Complete service is ideal for companies that outsource all of their IT systems to managed service providers. This service deploys all of the Falcon modules.
One more module in the CrowdStrike Falcon family is the Falcon Device Control utility. This isn’t included in any of the standard editions of Falcon. It is a system to protect endpoints from infections carried by USB memory devices. The USB management software will block any memory stick from connection to the endpoint’s operating system unless an administrator has specifically approved that device.
Pros:
- Excels in hybrid environments (Windows, Linux, Cloud, BYOD, etc.)
- Intuitive admin console makes it easy to get started and is accessible in the cloud
- Can track and alert anomalous behavior over time, improves the longer it monitors the network
- Lightweight agents take up little system resources
Cons:
- Would benefit from a longer trial period
CrowdStrike Falcon is available to try on a 15-day free trial.
ESET Endpoint Security and CrowdStrike Falcon
Although CrowdStrike advertises itself as a cloud solution, almost all of the endpoint protection work is implemented through its agent software, which is installed on the protected device. This is exactly the same as the ESET approach. The two security systems also have a common strategy of spreading information about the threats that each installation encounters. This intelligence sharing is spread to all instances of each software package through threat database updates. In both cases, experts at the company HQ analyze threat information to find ways to improve the software.
The managed services and packages that include human expert intervention are unique to CrowdStrike in this comparison. These expert-driven services are only included in the higher editions of the software package with the lowest plan, CrowdStrike Pro having more in common with the AV and firewall strategy of ESET.
Another major difference between the two options is that the management console for ESET Endpoint Security has to be installed on-premises while the dashboard for CrowdStrike is accessed in the cloud.
CrowdStrike started off as a cybersecurity consultancy, selling the services of its human team. The software it markets can be seen as a draw to bring work into that team of experts, which is still on the CrowdStrike payroll. ESET has a team of experts, too. However, their lab-based threat detection work has been, to a large extent, replaced by the machine learning capabilities of the endpoint security.
Curiously, despite being a newer company with fewer obligations to long-serving staff, CrowdStrike has a much stronger human element in its services than ESET does.
Ultimately, you are going to need to try each of these systems out yourself in order to properly assess them. You can get a free trial of Falcon Pro. ESET offers a 30-day free trial of its business bundle, which includes file and mail server security alongside its Endpoint Security package. Once you have tested these two systems, leave a message in the Comments section below to share your opinions with the community.
ESET Endpoint Security vs CrowdStrike Falcon FAQs
Is CrowdStrike a Chinese company?
CrowdStrike Holdings, Inc. is a US company that is based in Austin, Texas. OF its three founders, two are from the USA and the other was born and raised in Russia before moving to the USA. The largest shareholders in the company are US investment funds.
What is ESET Endpoint security?
ESET Endpoint Security provides on-device security protection that implements anomaly detection to spot and block malware, intrusion, and insider threats. All of the endpoint units operating for a business upload activity reports to a central controller that scours those records for more threats – this central module acts as a SIEM and sends back instructions to endpoints to block any intrusions that it identifies.
What is CrowdStrike Falcon?
CrowdStrike Falcon is a cloud platform of cybersecurity modules that rely on an on-device unit, called Falcon Prevent, for local research and threat response. Falcon Prevent also operates as an independent antimalware service by searching for anomalous behavior. This strategy also detects intrusion and insider threats. The cloud-based XDR receives activity logs from Falcon Prevent and performs threat hunting. The XDR sends back response instructions to the instances of Falcon Prevent that are installed around the enterprise.