Active Directory (AD) is one of the most widely used directory services for managing users, groups, and resources in an enterprise network, and it is bundled with Windows Server. It provides administrators with the ability to control access to resources and apply security policies across the network. PowerShell, also integrated into Windows Server, is a powerful scripting tool that enables administrators to automate tasks and retrieve data efficiently.
One of the common tasks in AD management is exporting the members of an Active Directory group to a file for analysis or reporting. While the Active Directory Users and Computers (ADUC) management console provides a GUI for interacting with AD objects, it has limited capabilities when it comes to exporting group membership details.
In contrast, PowerShell offers a more flexible and efficient way to extract this data and save it to a CSV file, which can then be easily opened and manipulated in tools like Microsoft Excel.
Using Excel to view and analyze the exported data is a convenient approach, as it offers robust features for sorting, filtering, and analyzing large datasets. Importing a CSV file into Excel is quick and straightforward. Therefore, if you need to gather and organize information about the members of an AD group, knowing how to use PowerShell to export this data into a CSV file can save you time and provide much more flexibility than the ADUC console.
This guide is a quick read and gives you a way to export AD group members with PowerShell in four easy-to-follow steps.
Step One: Setting up
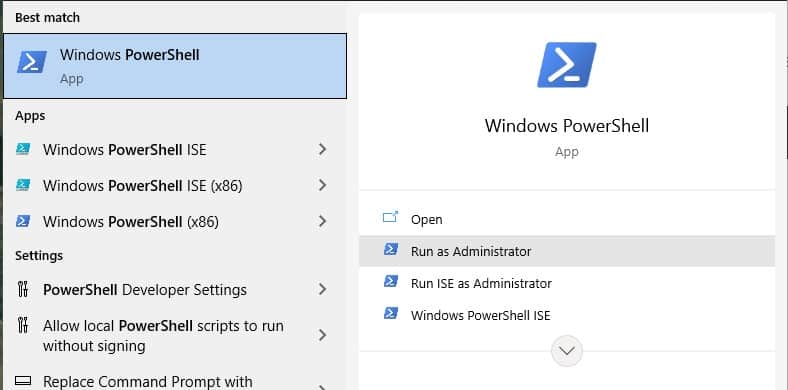
Type powershell into the Start search field and click on Run as Administrator.
Click on Yes in the User Account Control screen to continue.
In the PowerShell window, type:
Get-Module -ListavailableThis lists all PowerShell utilities. If you don’t see Active Directory near the top of the list, enter the following on Windows Server:
Install-WindowsFeature -Name RSAT-AD-PowerShellOn Windows 10, in PowerShell, run the following:
Get-WindowsCapability -Name RSAT* -Online | Add-WindowsCapability –OnlineThe installation process takes a long time. You will see a progress bar at the top of the screen in the form of a growing line of “o”.
Run the Get-Module query again to confirm that the Active Directory module is now available.
Step Two: Get the group name
You will need to know the name of the group that you are going to extract. If you’re not quite sure what it is called you can list all group names to jog your memory.
get-adgroup -filter * | sort name | select NameNote the name of the group that interests you.
Step Three: Look at the membership list
If you want to look at the list of group members, type:
Get-AdGroupMember -identity "group_name"Substitute the name of your group for group_name. This is not an essential step to extract the member list. However, it is a good confirmation that there are actually members in the group and it also checks that you spelled the group name correctly when you wrote it down.
Step Four: Perform the export
Now that all systems are go, you can launch the extract. In order to do this, you just have to pipe that last group member query into a file:
Get-AdGroupMember -identity "Group Name"| Export-csv -path C:\a_path\filename.csv -NoTypeInformationMake sure you substitute the real path and name for your export file.
Read this file into Excel to use its data searching facilities.
Use a third-party tool for Active Directory management
The above method is a great method for exporting AD group members with PowerShell in 4 steps. However, loading new user accounts into Active Directory is difficult with PowerShell.
SolarWinds Admin Bundle for Active Directory (3 FREE TOOLS)
A better solution for uploading user accounts is the Admin Bundle for Active Directory from SolarWinds.
This package of three Active Directory utilities is free to use. The other tools in the bundle assist in account removal. The Admin Bundle’s three components are:
- User Import Tool Create Active Directory user account entries in bulk by uploading them from a CSV file. The interface allows you to specify the columns that are contained in the file and map them to AD fields.
- Inactive User Account Removal Tool This utility will scan Active Directory and help you to remove users who have not logged in for a certain amount of time.
- Inactive Computer Account Removal Tool With this facility, you can identify defunct device entries and remove them.
ManageEngine Active Directory CSV Generator
The ManageEngine Active Directory CSV Generator is a free tool that lets you explore the contents of a domain controller by account attribute, such as user or group. Once you have selected a group, you can then export all related data into a CSV file.
The CSV Generator is one of a bundle of Free Active Directory Tools offered by ManageEngine. The full pack can be downloaded onto Windows Server.
Active Directory administration
A badly organized Active Directory database is harder to manage than a well-planned system and now you know how to export AD group members with PowerShell in 4 steps. Use free tools and system utilities to get a grip on the records in the AD system. Abandoned accounts and orphaned entries are particularly risky because they offer facilities to intrusion and so it is very important to ensure that all of the accounts that you have listed in Active Directory are still in use.