File Integrity Monitoring (FIM) is the process of keeping an eye on your system and data files to detect any changes, authorized or unauthorized. Think of it like a security camera for your file systems. It alerts you when something has been modified, added, or deleted, which is especially critical when you’re trying to catch suspicious activity before it becomes a major problem.
Why does this matter? Well, when you are managing sensitive data or running systems that have to meet strict compliance standards like PCI DSS, HIPAA, or SOX, even the tiniest unauthorized tweak to a config file could spell trouble. FIM helps you spot those changes early before they lead to data loss, breaches, or compliance issues.
This article is for you if you manage IT security or compliance and want a simpler way to track file changes without constantly switching tools or questioning alerts. Perhaps you’re looking to deploy an FIM tool for the first time, or you’re ready to upgrade to something more powerful or cloud-ready. Either way, you’re in the right place.
Here’s what you will find: a carefully vetted list of the best FIM tools out there, based on actual research, user feedback, and hands-on experience. We’ll break down what each tool does best, where it might fall short, and what kinds of environments it fits. No fluff, just straight talk to help you make a wise, confident choice for your team.
Here is our list of the best file integrity monitoring tools:
- Fortra Tripwire Enterprise EDITOR’S CHOICE This on-premises package forms a central server for site-wide configuration controls and file integrity monitoring. The tool reaches across the network to operate on hosts across the business, providing a coordinated approach to security and compliance management. Runs on Windows or Linux. Access a free demo.
- ManageEngine ADAudit Plus (FREE TRIAL) A system security bundle that logs all user activities, linking each account to an actual person through the data in AD and protecting data. Runs on Windows Server. Start a 30-day free trial.
- ManageEngine EventLog Analyzer (FREE TRIAL) A suite of data security services that centers on log file management. This is available for Windows Server and Linux. Start a 30-day free trial.
- Site24x7 File and Directory Monitoring (FREE TRIAL) A Lightweight, Real-Time Security Asset for Modern IT Environments Get a 30-day free trial.
- Datadog Security and Compliance Monitoring Be among the first to trial this new security service from the cloud-based Datadog system monitoring platform.
- SolarWinds Security Event Manager A top SIEM system that integrates a file integrity manager to ensure that log files feeding event data into security assessments are not tampered with. Installs on Windows Server.
- Netwrix Auditor A package of access rights management and data protection service that includes a file integrity monitor. Installs on Windows Server.
- OSSEC A free, open-source host-based intrusion detection system (HIDS) that includes file integrity monitoring. Installs on Windows, Linux, Unix, or macOS.
- Samhain File Integrity A free, open-source file integrity monitor and HIDS. This system is written for Linux, Unix, and macOS and can run on Windows over Cygwin.
Key points to consider before choosing or purchasing a FIM tool
Here are the key points to consider before choosing or purchasing FIM tools:
- Compliance Support: Make sure the tool supports your compliance journey and helps you meet regulatory requirements such as PCI-DSS, HIPAA, or NIST.
- System Compatibility: Check that the software works with your OS, cloud, servers, and apps.
- Real-Time Alerts: Consider your need for instant alerts or regular scheduled scans.
- Easy Setup & Use: Look for tools that are quick to install and simple to manage.
- Clear Alerts & Reports: It should give useful alerts and easy-to-understand reports.
- Intelligent Change Detection: Effective FIM tools should be capable of distinguishing between safe and risky changes, so look for these features.
- Scalability: Ensure it can scale with your environment without compromising performance.
- Tool Integration: It should be able to integrate seamlessly with your other security tools, such as SIEM, EDR, or IAM.
- Cost and Licensing: Understand the pricing model and the features included.
- Vendor Support: Choose a tool that offers robust customer support and comprehensive documentation.
File integrity monitoring
File integrity monitoring (FIM) is the field of protecting files from tampering. Typically, there are two methods for protecting files. The first is to calculate a checksum on the properties of a file whenever it is written to by an authorized process. The second is to take a copy of the file and then repeatedly compare the live file to the backup.
Some systems will just alert you to any unauthorized change, in which case, you will need to have separate backup and restore procedures in place. Early APT incidents took years to discover, giving hackers free rein to exploit system resources and interfere with the operations of the business. File tampering is a telltale sign of malicious activity, so the notification of unauthorized changes to files at least gives you a heads up that something is going on as soon as the intruder starts trying to hide.
Systems that can restore files to their original state are preferable to those that just detect unauthorized change. The ability to see exactly which records an intruder changed lets your security software know exactly which accounts have been compromised and that speeds up the processes to throw that intruder out.
These tools help detect potential security breaches, data theft, and malware infections by providing real-time alerts whenever files are altered in ways that could signal a threat.
FIM tools work by establishing a baseline for the normal state of files and then monitoring for deviations. Whether it’s a change in file content, permissions, or metadata, FIM tools track alterations and immediately notify administrators of suspicious activities. This level of monitoring is particularly important in industries subject to stringent regulatory requirements, such as finance, healthcare, and government, where file integrity is critical to compliance and data security.
Log files record all actions on a system and SIEM systems exploit these data sources to identify malicious activity. Therefore, those log files are obvious targets for intruders who aim to hide their presence. Protecting files from tampering is now an essential part of cybersecurity. These files are the source material for security investigation and your entire system protection strategy will be useless if the records in those log files are not protected.
FIM Security requirements
Although, as explained, FIM is an important system protection strategy, you might be driven to investigate FIM systems because of a requirement imposed by a data security standard.
If your business has discovered that it is increasingly difficult to win business without complying with a specific security standard, you might be in the process of instituting all of the systems necessary for compliance.
FIM is a requirement of PCI-DSS and NERC-CIP and it is also considered a best practice for FISMA, SOX, HIPAA, and GLBA. If you are implementing one of these standards, you need to be sure that the FIM system that you choose complies with the requirements of that standard.
Choosing a file integrity monitoring tool
A full-featured system sounds like the best option. However, there are downsides to comprehensive security systems. If every log file on your system is copied, you will need a very large amount of disk space. Logfiles already require a lot of room to store and doubling the volume of log files makes that problem worse.
Although small networks don’t produce too much log traffic, larger systems can generate a very large amount. Processing those logs meaningfully requires a lot of processing power. The perfect security system with an active, live FIM would end up requiring more processing power and file space than the original system. Your business would end up spending more money on log file management than your core operations. So, clearly, the best FIM systems involve some sort of compromise.
In order to keep security services manageable, you need a FIM that is able to be smart. You need to find a system that can protect your files without taking over the entire purpose of your IT system. One key compromise is the choice over whether FIM actions are performed in real-time or periodically. Another strategy to look out for is a log management system that can identify which log messages are important and which are of little use for security purposes. Cutting down the volume of records that need to be protected makes FIM manageable.
The best File Integrity Monitoring tools
1. Fortra Tripwire Enterprise (GET DEMO)
Fortra Enterprise provides a security configuration management service that includes a file integrity monitor. While the Security Configuration Management service audits all of your software and operating systems for security loopholes, the FIM module focuses on data protection.
Key Features:
- Real-Time Monitoring: Actively scans hosts for setting changes, enhancing security vigilance.
- Integrated Policy Management: Seamlessly links with access rights systems like Active Directory.
- Comprehensive Compliance Logging: All user activities are logged, aiding in regulatory compliance.
- File Access Tracking: Monitors and records file interactions, ensuring data integrity.
- Security Policy Enforcement: Actively applies and maintains set security policies.
Why do we recommend it?
Fortra Tripwire Enterprise is a comprehensive solution to system protection that focuses on data protection. The package shuts down all of the configuration errors that can let hackers in and then it constantly scans hosts for signs of changes to those settings. It also controls file access and records changes to data so that they can be reversed.
The File Integrity Monitoring service begins with the definition of security policies. This requires an interface to your access rights managers, such as Active Directory. It enforces file access permissions for groups of users of specific data stores.
Once permissions have been set up, the system tracks file access events and records all actions that take place. This includes the time of changes and the user account that made them. The actual changes are also recorded so that they can be reversed if necessary.
All of the activities of users are logged for compliance reporting. The change detection extends to operating system and application settings, so the service maintains a secure environment and prevents hackers from easing their actions by manipulating system configurations.
Who is it recommended for?
This package acts as a vulnerability manager and configuration controller as well as a file integrity monitor. This means you only have one dashboard to visit in order to set up and enforce system security. As it protects data, this package is particularly suitable for businesses that have to follow data security standards, such as PCI DSS.
Pros:
- Flexible Deployment Options: Can be hosted on-premises or on cloud platforms like Azure or AWS.
- Extensive Vulnerability Scanning: Thoroughly examines enterprise systems to identify and mitigate risks.
- Effective Security Loophole Closure: Proactively addresses configuration errors to prevent hacker intrusions.
- Dynamic Secure Configuration Monitoring: Continually observes for alterations in security settings.
- Detailed File Access Logs: Tracks and records every file access and editing action for security.
Cons:
- Price Transparency: Lacks upfront pricing information, necessitating direct contact for quotes.
- Self-Hosted Complexity: May require additional resources for installation and management on public cloud accounts.
Fortra Tripwire Enterprise is a self-hosted package but it can be installed on a public cloud account, such as Azure or AWS. The on-premises version will run on Windows or Red Hat Enterprise Linux (RHEL). There isn’t a free trial available for the package but you can access a demo to learn more about the Tripwire system.
EDITOR'S CHOICE
Fortra Tripwire Enterprise is our top pick for a file integrity monitoring tool because it combines security measures for software and operating systems as well as protection monitoring for data. The tool acts as a vulnerability manager and will constantly monitor updated and secure configurations to ensure that system security settings don’t get loosened. Alongside the system configuration controls, the package provides access rights enforcement for files that contain sensitive data. The FIM will record all access events and any changes made to files. Thanks to the logs of the Tripwire system, any unauthorized or accidental changes can be reversed.
Download: Access FREE Demo
Official Site: https://www.tripwire.com/demo
OS: Windows, RHEL, or cloud
2. ManageEngine ADAudit Plus (FREE TRIAL)
ManageEngine ADAudit Plus provides data access controls and compliance logging with reference to the user accounts and permissions structure of Active Directory. The purpose of this system is to identify the actual person who accessed each resource, particularly sensitive data stores. The storage of these logs provides an audit trail for compliance auditing.
Key Features:
- In-Depth Compliance Reporting: Supports GDPR, GLBA, SOX, and other standards.
- Active User Behavior Analytics: Tracks and analyzes user interactions for security insights.
- Detailed File Change Tracking: Monitors modifications to enhance data protection.
- Active Directory Focus: Tailored for environments using Active Directory for access management.
Why do we recommend it?
ManageEngine ADAudit Plus is an activity tracking package that focuses on the protection of Active Directory records. The bundle implements user activity modeling to look for insider threats and this service is only worthwhile if the contents of AD are correct. This explains the importance of Active Directory protection in this package.
Important data files aren’t only those that you can see in a Windows Explorer file directory view. Database files and operating system temporary files can also give hackers access to sensitive data. By tracking activity on all files containing sensitive data, ADAudit Plus can be set to raise an alert if important files are accessed. The report will detail which account accessed the data and from where.
Changes to system files can indicate attempts to change authorizations, copy important system data for research or look for exploits. So, ADAudit Plus also tracks access to these files – logging those events as well as raising an alert.
File protection also extends to noting unexpected patterns of activity. For example, the activation of ransomware will start a sudden spike in file access activity. Catching the encryption access of ransomware and killing the process involved will save your business’s data. You will also need to have additional backup systems in place for full protection.
Who is it recommended for?
You would need to be using Active Directory for your access rights manager in order to benefit from this package. The tool is able to protect and exploit records in Azure AD as well as the various forms of on-premises Active Directory. This is particularly useful for large businesses.
Pros:
- Comprehensive User Activity Monitoring: Keeps a close eye on all user interactions within the system.
- Alerts for Abnormal Behavior: Quickly identify deviations from normal user patterns.
- Enhanced Data Access Surveillance: Vigilantly patrols access to sensitive data.
- Rigorous Compliance Reporting: Assists in meeting data security standards requirements.
Cons:
- Lacks Encryption for Sensitive Data: Does not provide encryption-based locks for protecting critical files.
- Active Directory Dependency: Primarily beneficial for organizations using Active Directory.
ManageEngine ADAudit Plus runs on Windows Server and it is available for a 30-day free trial.
3. ManageEngine EventLog Analyzer (FREE TRIAL)
ManageEngine EventLog Analyzer is a SIEM tool that protects its log files with file integrity monitoring. This protection extends to critical system files and folders. The tool will record all changes, such as deletion or alteration of records and even the alteration of file and folder access permissions. These changelogs identify the time of the change and the user account responsible for the alteration.
Key Features:
- Broad System Security: Offers extensive protection across various system components.
- Alert-Enabled FIM: Notifies administrators of file integrity issues in real-time.
- Detailed Data Access Logs: Tracks and records access to sensitive information.
Why do we recommend it?
ManageEngine EventLog Analyzer is a SIEM system that is very similar to the SolarWinds Security Event Manager. This package deploys extensive file integrity monitoring and those files that have been marked as containing sensitive data get any changes made to them logged, which means that those changes can be reversed.
The security service runs two levels of file integrity monitoring. It executes periodic checks on all files for changes and records what those changes were – it doesn’t offer any rollback option on these files. Critical files are subjected to live monitoring, so any changes to those files and folders generate alerts. These critical file changes are reported with before and after snapshots, so those changes can be reversed.
The FIM functions and auditing features of ManageEngine EventLog Analyzer help with compliance to PCI-DSS, SOX, HIPAA, and FISMA. Reports can be extracted into CSV files for further analysis or produced as PDF presentations.
The EventLog Analyzer isn’t just a file integrity monitor. Its functions offer a range of system protection measures, which include User and Entity Behavior Analytics (UEBA) to help you spot compromised accounts and endpoints that are being manipulated. The combination of functions in one package creates greater efficiency and enables the security service to provide several services with the same procedures, simultaneously optimizing the use of CPU, memory, and storage space.
The ManageEngine system is available in three editions. These are Free, Premium, and Distributed. The Free edition is limited to monitoring five log sources and it doesn’t include file integrity monitoring. The difference between the Premium and Distributed editions is that the Premium service covers one site, but the Distributed plan will monitor activities on many sites.
Who is it recommended for?
The need to protect files of sensitive data from tampering is an essential task for businesses that need to comply with data protection standards. Alterations to personally identifiable information are just as bad as its disclosure. Unauthorized changes to this data can cause terrible harm to the people to whom the data relates.
Pros:
- Versatile Edition Options: Available in free, premium, and distributed versions for different needs.
- Wide Platform Compatibility: Supports both Windows Server and Linux environments.
- Integrated Remediation Actions: Links detection of file changes to proactive security measures.
Cons:
- Complex Package Division: Different components can be challenging to understand and select.
- Intensive Resource Requirements: May demand significant system resources for optimal performance.
The software for the EventLog Analyzer installs on Windows Server or Linux and you can experience it on a 30-day free trial.
4. Site24x7 File and Directory Monitoring (FREE TRIAL)
Site24x7 FIM delivers reliable file change tracking without the performance hit. Its real value lies in context. It connects file activity to system health, so it is perfect for helping IT teams move from reactive fixes to proactive defense. It also works on Windows and Linux servers. It’s part of Site24x7’s broader infrastructure suite, including monitoring applications, networks, cloud resources, and more.
Key Features:
- Instant Alerts: Get notified right away when files are accessed, changed, deleted, or permissions shift.
- Storage Monitoring: Set limits and receive alerts when usage crosses thresholds.
- File Change Tracking: Catch unexpected edits or deletions that may indicate data loss.
- Error Log Alerts: Scan for error keywords and get notified when they appear.
- Inactivity Flags: Detect untouched or oddly modified files over time.
- Unified View: Track files, URLs, logs, ports, and cloud activity from one dashboard.
Why do we recommend it?
The power of Site24x7’s FIM lies in its integration. The FIM module is part of a unified cloud-based monitoring platform that also covers server health, network activity, application performance, user behavior, and cloud infrastructure. It also includes out-of-the-box support for AWS, Azure, and Google Cloud. So it is ideal for hybrid or multi-cloud environments.
We tested Site24x7 FIM on both Linux and Windows environments and were impressed by how fast and accurate it was. Any file changes triggered alerts in under 3 seconds. The weekly reports were also clear and actionable. These reports gave full visibility into changes by user, time, and file path.
The tool also stands out for its integration. It connects seamlessly with alerting systems like Slack or PagerDuty. We especially liked its ability to correlate file changes with system health metrics (something few tools do well).
Performance-wise, Site24x7 was efficient. Even during active monitoring, CPU load stayed under 5%. That’s crucial when deploying across multiple production systems.
Who is it recommended for?
Site24x7 FIM is ideal for different IT professionals. It comes with a single dashboard to monitor multiple platforms, so it is a strong fit for MSPs and IT admins managing hybrid environments. Security teams can also use it to track suspicious activity in sensitive directories or system files. Compliance officers may also benefit from its reliable file-level audit trails that support PCI DSS, HIPAA, or SOX requirements.
Pros:
- Instant Change Detection: Real-time alerts notify you immediately when monitored files are modified.
- Lightweight Agent: Minimal resource usage and quick deployment across systems.
- Centralized Monitoring: Unified dashboard displays file, system, and application health in one place.
- Hybrid-Friendly: Works seamlessly in both cloud and on-premises environments.
Cons:
- Noisy Alerts: Alert rules require fine-tuning to prevent unnecessary notifications.
The software for the Site24x7 FIM installs on Windows or Linux and you can experience it on a 30-day free trial.
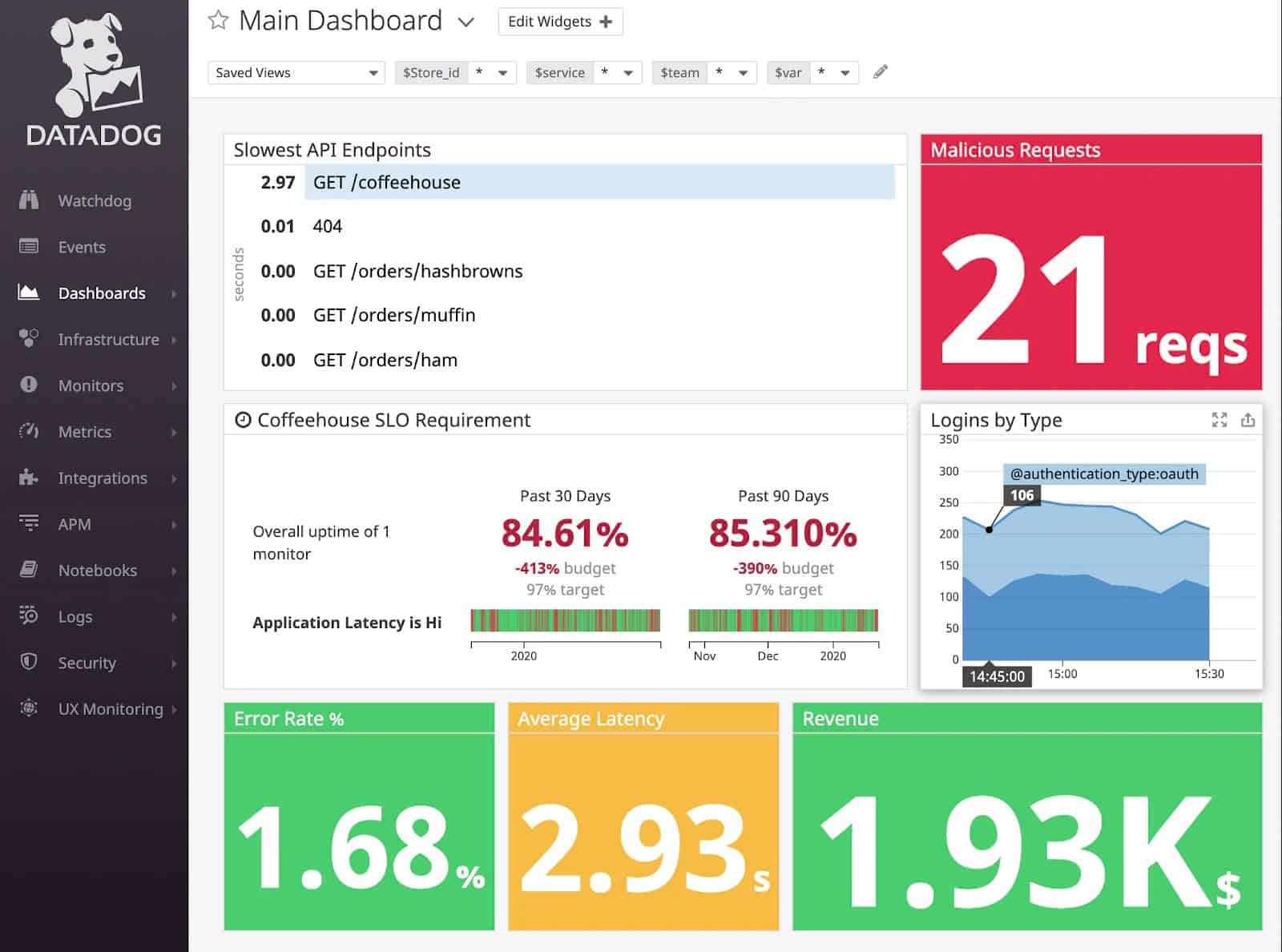
5. Datadog Security and Compliance Monitoring
Datadog is a cloud platform of monitoring tools for a wide range of systems including networks, servers, applications, and websites. The platform doesn’t have a security service, such as a SIEM system. However, there is a new security system that Datadog has just put together and it is currently under Beta release.
Key Features:
- Multi-Site File Monitoring: Offers comprehensive file tracking across various locations.
- Cloud-Focused FIM: Specializes in monitoring files on cloud platforms.
- Integrated Compliance Tools: Ensures adherence to regulatory standards within the SaaS framework.
- SaaS Model Efficiency: Streamlines operations by utilizing a cloud-based platform.
Why do we recommend it?
Datadog Cloud SIEM is a relatively new package from a platform that was originally focused on performance monitoring. This security scanning service is able to draw source data from cloud platforms as well as from multiple sites. The tool isn’t limited to monitoring one location, which makes it very powerful and identifies company-wide attacks.
You won’t see the Datadog Security and Compliance Monitoring explained on the main sales pages of the Datadog website. Instead, you need to request to be enrolled in the service. The security system is fully developed and includes sophisticated screens, showing recent security events.
This Datadog service is very similar to the SolarWinds Security Event Manager in that it combines log file collection with security detection.
The service applies detection rules to all incoming event messages and identifies records that require further investigation. Those events that could potentially indicate intrusion if combined with later events are put to one side for storage. The system then looks out for expected indicators to either strengthen or allay suspicion. Those stored records of potential threat indicators are protected by FIM. Thus, the processing load and storage demands of file integrity monitoring are greatly reduced.
Use this form to request special access to the Datadog Compliance Monitoring system.
Who is it recommended for?
The Datadog SIEM system is suitable for all types and sizes of businesses. The throughput-based price for the tool makes it an affordable prospect for small businesses. The SIEM’s ability to collect data from multiple sites plus cloud services makes it appealing to large and complex businesses that use hybrid environments.
Pros:
- Cloud-Based Simplicity: Eliminates the need for onsite software maintenance.
- Versatile File Integrity Monitoring: Effective for local, remote, and cloud file storage systems.
- Suspicious Activity Reporting: Keeps a log of all unusual activities for security analysis.
- Unified Monitoring Agent: Integrates seamlessly with other Datadog utilities for consistency.
Cons:
- Lack of On-Premises Option: May not be suitable for businesses requiring onsite deployment.
6. SolarWinds Security Event Manager
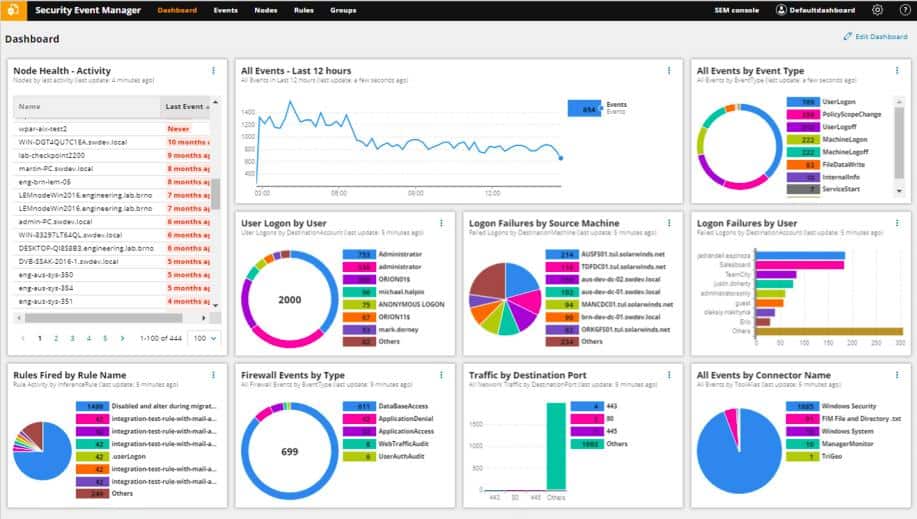
SolarWinds Security Event Manager is not primarily a FIM system. It is a SIEM service that exploits log messages to search for malicious activity. However, this service has file integrity monitoring integrated into it.
Key Features:
- Extensive Log Collection: Gathers Windows Events and Syslog records for comprehensive analysis.
- Log Message Consolidation: Centralizes log data, enhancing efficiency in security monitoring.
- Tamper-Proof Log Protection: Safeguards log files against unauthorized alterations.
- Integrated FIM for Logs: Monitors both live and archived log files for integrity.
- Compliance with Data Privacy Standards: Ensures adherence to various regulatory requirements.
Why do we recommend it?
SolarWinds Security Event Manager manages logs as well as providing security scans for threats. Log messages are drawn from all around the system so they can be pooled for searching and then stored in files. These files are important for re-searching and for compliance reporting and so they are protected against tampering.
The FIM strategy of the SolarWinds Security Event Manager creates efficiency. This is because the process integrates its own log file server. This is the system that collects log messages, sorts and filters them for relevance, and then stores them. So, it is able to identify which log messages are potentially important and which don’t really relate to security.
The Security Event Manager operates three functions simultaneously: it examines event records live as they arrive, it stores log messages for analysis, and for standards compliance, and it also works out which log records need to be protected against tampering.

SolarWinds Security Event Manager integrates FIM into its SIEM data collection processes. This early integration of file integrity management offers a solution to the problem of heavy processing power required for full, live log file protection. The system is able to identify key log records that require full protection, thus reducing the volume of data that needs to be duplicated for backup.
Who is it recommended for?
This package is important for any business because SIEMs are now considered to be essential for system security. However, this tool’s high volume processing capabilities are particularly suitable for use by large organizations. Businesses that need to implement compliance reporting need this service and need their log files to be protected.
Pros:
- Robust Log File Protection: Defends against unauthorized modifications, securing critical data logs.
- Comprehensive Log Management: Efficiently handles log files for security and compliance purposes.
- Full Administrative Control: On-premises installation offers complete management authority.
- Broad Compliance Coverage: Supports SOX, HIPAA, PCI DSS, and other regulatory standards.
- Efficient FIM Integration: Seamlessly combines file integrity monitoring within the SIEM process.
Cons:
- Limited FIM Scope: Focuses primarily on log file integrity, potentially overlooking other file types.
- Complexity for Smaller Organizations: May be overly extensive for smaller businesses’ needs.
The Security Event Manager is suitable for businesses that are enrolled in SOX, HIPAA, PCI DSS, NERC CIP, FISMA, and SANS Critical Security Controls programs. This is on-premises software that installs on Windows Server. SolarWinds offers the Security Event Manager on a 30-day free trial.
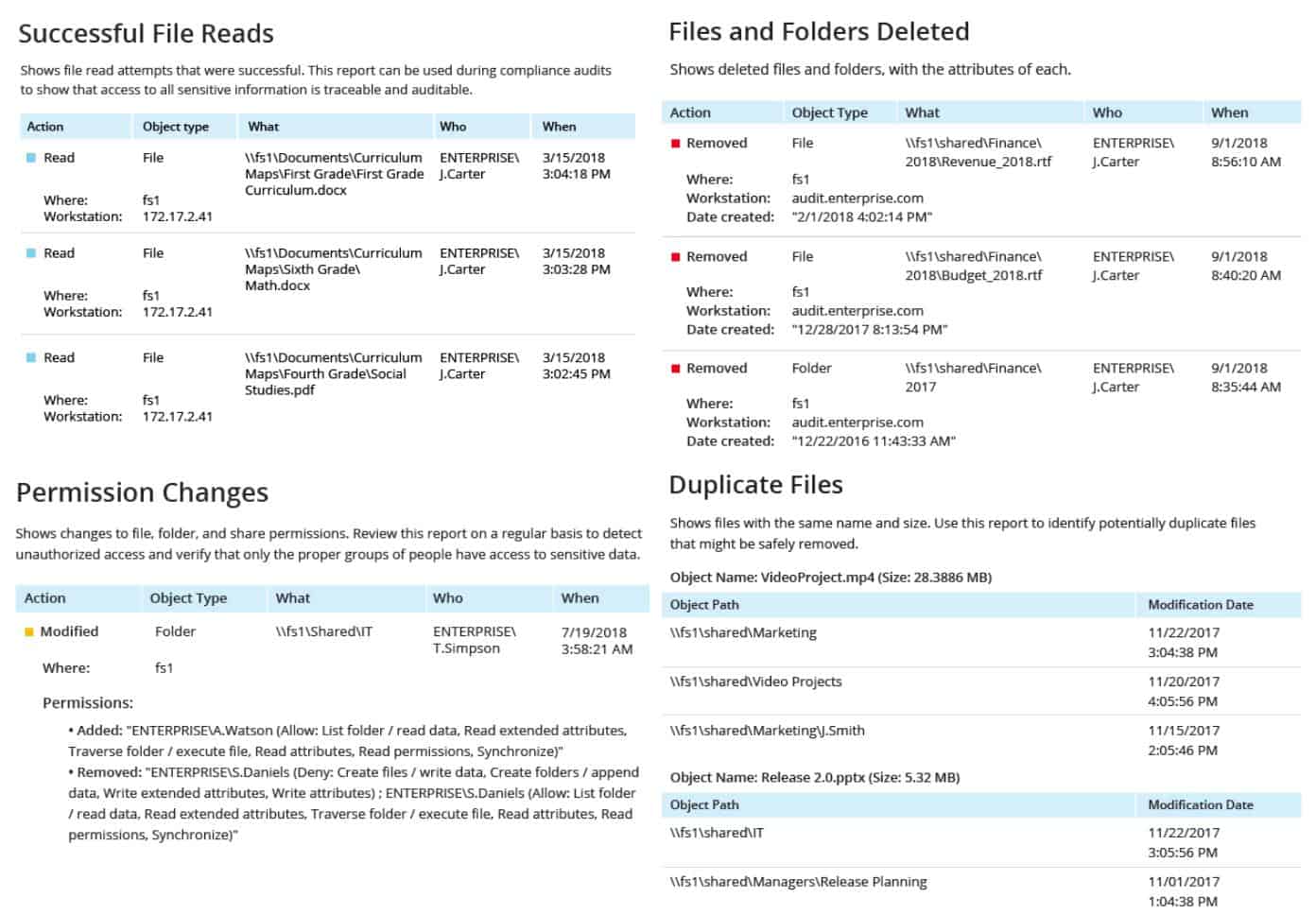
7. Netwrix Auditor
Netwrix Auditor for Windows File Servers includes a comprehensive file integrity monitor that logs the creation, modification, and deletion of files and folders. This tool is a good auditor for those who need to comply with PCI DSS, HIPAA, and FISMA.
Key Features:
- Detailed File Change Logs: Tracks creation, modifications, and deletions of files and folders.
- Enhanced Access Rights Management: Improves security through better control of user permissions.
- Full Compliance Reporting: Offers detailed reports to meet regulatory standards like PCI DSS and HIPAA.
Why do we recommend it?
Netwrix Auditor is a highly respected activity tracking service and it includes file access logging. It provides file integrity monitoring on Windows servers. The Netwrix unit that implements FIM is called the Netwrix Change Tracker. This focuses on changes to files that contain sensitive data and it lays down extra logs for inclusion in the Netwrix Auditor’s analysis function.
The Netwrix Auditor tool is purely and monitoring and reporting system. It doesn’t perform file backup and restore functions. However, for the sake of most security standards, you don’t need to protect those files, just report on access attempts and changes to data.
As well as reporting on changes to files and folders, the Netwrix Auditor service can be set up to report on file access. This monitoring service doesn’t apply to all files and folders – that would be an unwieldy system. Instead, it identifies stores of sensitive data and monitors those.
The file integrity monitoring service in Netwrix Auditor is part of a wider collection of security monitoring and reporting features. As well as observing changes to sensitive files, this tool will help you tighten up access rights by improving the granularity of the user groups that you maintain in Active Directory. By combining access rights management with file integrity monitoring and event audit reporting, Netwrix Auditor provides all of the data protection services that you need for standards compliance.
Who is it recommended for?
This tool is designed for use by large businesses that need to implement the recommendations of data protection standards, such as PCI DSS and HIPAA. Netwrix doesn’t publish its pricelist which might deter some IT managers that don’t like unexpected surprises when investigating new software purchases.
Pros:
- Comprehensive Compliance Support: Meets standards like PCI DSS, HIPAA, and FISMA.
- Sensitive Data Identification: Effectively pinpoints and monitors stores of critical data.
- On-Premises Security Assurance: Suitable for businesses preferring in-house server management.
Cons:
- Lacks Remediation Capabilities: Does not include direct processes for addressing security issues.
- No Backup or Recovery Functions: Absence of data backup solutions could be a drawback for some users.
Netwrix Auditor is delivered as on-premises software for installation on Windows Server. You can test this file integrity monitoring tool on a 20-day free trial.
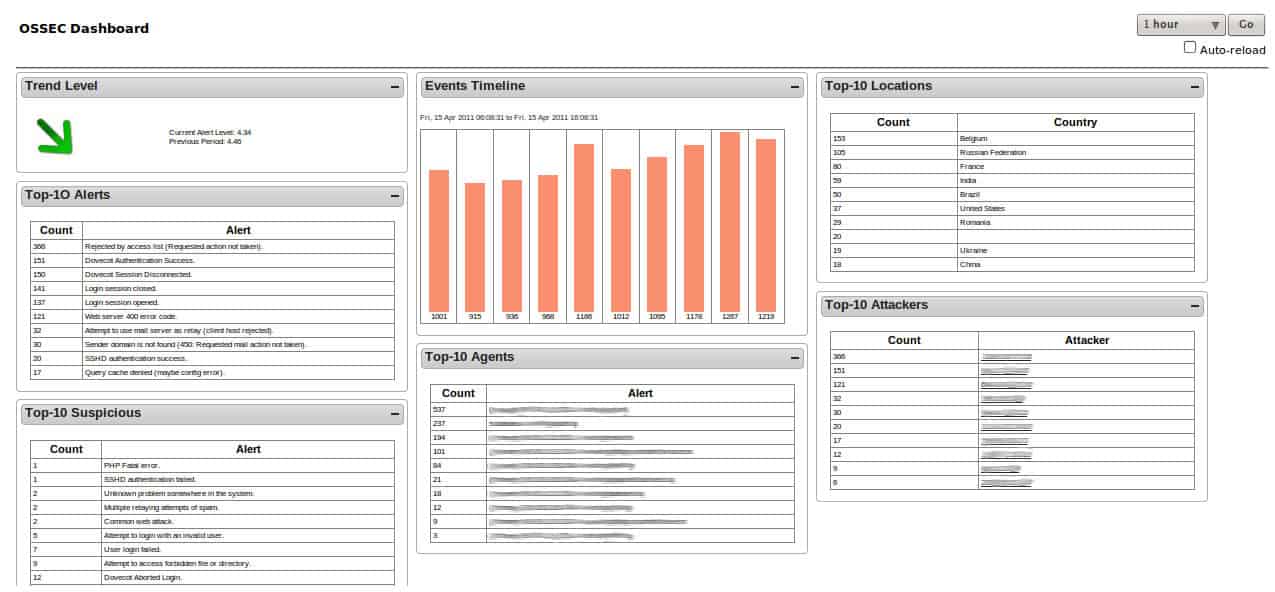
8. OSSEC
The OSSEC system is a seminal host-based intrusion detection system (HIDS). The software is actually owned by Trend Micro. However, it is free to use and it includes a file integrity monitor.
Key Features:
- Cost-Free Solution: Permanently free open-source HIDS with FIM capabilities.
- Efficient Resource Usage: Designed to minimize CPU and system demands.
- Log File Focused FIM: Concentrates on maintaining the integrity of crucial log files.
Why do we recommend it?
OSSEC is a highly respected free open-source host-based intrusion detection system. The tool has recently gone through some changes, shifting more emphasis towards its paid counterpart. Most users looking for a free SIEM solution will be drawn to the new OSSEC+ package, which is also free to use.
Host-based intrusion detection systems collect and analyze log files. The integrity of those files is crucial to the successful detection of interlopers because much of the real work of these systems occurs on historical records. The FIM tool built into OSSEC is called Syscheck.
Not every intrusion can be identified immediately, seemingly innocent acts only indicate malicious activities when they are identified in combination. Thus, the HIDS needs to keep records of activities and re-scan them as new log messages arrive.
Syscheck runs on a cycle, scanning files for changes every six hours. This strategy reduces the amount of demand the system places on your CPU. However, the trade-off for that system resource efficiency is a delay in detecting unauthorized file changes.
The OSSEC system’s server program installs on Linux, macOS, and Unix and there is an agent program for monitoring Windows systems. The server can also run on top of VMWare, which is probably a better option for those who don’t have any Linux servers on-site.
Who is it recommended for?
OSSEC is probably being aged out in favor of the new OSSEC+ and the paid Atomic OSSEC. This tool is very competent and, while time-consuming for small businesses to set up, will be a good option for SMEs as well as large businesses. If you follow the PCI DSS system, you will particularly need this tool.
Pros:
- Multi-Platform Compatibility: Runs on Linux, macOS, Unix, and Windows (via agent).
- Virtualization Support: Can operate over VMWare for flexible deployment options.
- Stealth Mode Operation: Enhances security by avoiding detection from potential intruders.
Cons:
- Windows Compatibility Issues: The main component doesn’t run natively on Windows, requiring additional setup.
9. Samhain File Integrity
Samhain is another free open-source HIDs. However, the file integrity monitoring service of this system gets equal billing – it is advertised as a file integrity monitor and host-based intrusion detection system.
Key Features:
- Universal FIM Capabilities: Monitors all file types, extending beyond just log files.
- Checksum-Based Assessments: Utilizes checksums for efficient file integrity checks.
- Perpetually Free Software: Open-source HIDS offering permanent, cost-free use.
Why do we recommend it?
Samhain File Integrity is an alternative to OSSEC and is also a HIDS. This package is a fast and lightweight service that works on external checks on files. You would need to implement a supplementary backup system if you want to restore files to their original form if Samhain detects a change.
The FIM in Samhain works on a checksum system. This calculates a value based on various attributes of the file and stores those sums in a table. The service periodically recalculates those sums and if the result comes out differently for a file, the system can tell that the contents of the file have changed. This is a good system from the aspect of confidentiality because it doesn’t need the FIM to get access to data. However, this also means that there are no data restore capabilities in the tool.
The HIDS part of Samhain relies on logfiles. The file integrity service isn’t limited to just monitoring the HIDs source log files – it will perform integrity checks on stores of files that hold sensitive data as well.
The system can be set to run continuously in memory or it can be launched periodically. The live running version will give instant notifications to system administrators whenever a file is changed.
Other security features in this package include rootkit detection and the identification of hidden or fake processes. The service will also scan for open ports. A nice feature of Samhain is that it has a “stealth mode” that enables it to run in secret. This helps it avoid detection by hackers who might try to kill detection systems so that they can remain hidden.
The Samhain software is available for Linux, Unix, and macOS. It is possible to run an agent program on Windows systems over a Cygwin interpreter. However, you will still need to have the main server system of Samhain running on another server that has Linux, Unix, or macOS as the operating system.
Who is it recommended for?
Samhain is a free tool and it is very easy to implement, so it will appeal to small businesses that don’t have system security experts on the payroll. Pairing this tool with a backup system provides excellent data protection for little money. The only problem is that it doesn’t work well on Windows.
Pros:
- High-Speed, Lightweight Service: Optimized for quick and efficient operation.
- Stealth Mode for Enhanced Security: Operates undetected to prevent disabling by attackers.
- Rootkit and Hidden Process Detection: Adds an extra layer of security against sophisticated threats.
Cons:
- Limited Windows Support: Requires additional setup to run effectively on Windows environments.
Our methodology for choosing FIM tools
The tools we selected here were selected based on a combination of real-world use cases, industry reputation, and core functionality expected from a modern FIM solution. We focused on tools that monitor file changes and also provide real-time alerts, intelligent change validation, compliance support, and integrations with broader security ecosystems such as SIEM or endpoint protection. These tools are widely adopted in both enterprise and mid-market environments, and each brings something unique to the table. We also considered scalability, ease of deployment, and the level of community or vendor support available, as these factors tend to matter a great deal to buyers and IT teams on the ground.
Other tools didn’t make the list not because they are not good enough, but because they either focused too narrowly (e.g., limited to Linux or Windows only). They lacked robust change validation features, or didn’t offer sufficient automation or integration to keep pace with today’s hybrid/cloud environments. We prioritized solutions that strike a balance between usability, security depth, and compliance readiness. Our goal is to provide a well-rounded shortlist that can serve various types of organizations, from those just beginning with FIM to those requiring advanced, enterprise-ready capabilities.
File integrity monitoring FAQs
What are file integrity monitoring tools?
File integrity monitoring tools control access to files containing sensitive data and log events that occur on them.
What does file integrity monitoring do?
File integrity monitoring tools are important for data privacy. They are intended to control access to files and also log all changes to the file, including moving or copying the file or changing its content.
What should I look for in file integrity monitoring tools?
When seeking a file integrity monitoring tool, look for a comprehensive data loss prevention package – FIM will help protect against insider threats and works well as part of a wider DLP service.
Can Splunk do file integrity monitoring?
Splunk doesn’t offer an integrated file integrity monitor. Some FIM tools are able to send log data to Splunk for integration into compliance reporting.