What Is Ransomware?
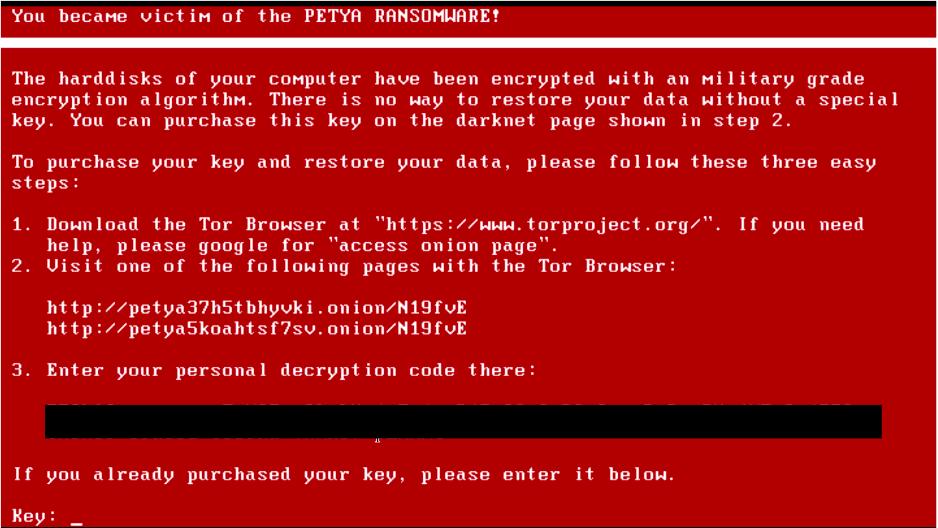
Ransomware is a form of malicious software designed to block access to a system or encrypt files until a ransom is paid. It can affect individuals, businesses, government organisations, and any connected network, often resulting in significant disruption and data loss. Typically, attackers demand payment in cryptocurrency in exchange for a decryption key that restores access to the affected data.
In most cases, infection occurs when users unintentionally download the malware through phishing emails, compromised websites, or infected software updates. Once inside a system, ransomware can spread across connected networks, encrypting files and locking users out of critical documents, applications, and databases. Victims are then presented with a ransom note containing payment instructions and a warning that data may be permanently lost if payment is not made within a specified timeframe.
There are several variations of ransomware, with the most common being Crypto ransomware and Locker ransomware. Crypto ransomware focuses on encrypting files and demanding payment for a decryption key, while Locker ransomware restricts access to the entire system or device, preventing users from interacting with their data altogether.
The impact of ransomware attacks can be severe, leading to financial loss, operational disruption, reputational damage, and potential regulatory consequences. For organisations, downtime can halt business operations entirely and significantly increase recovery costs. Reducing risk typically involves a combination of security measures, including firewalls, antivirus protection, regular system updates, and user awareness training to help prevent phishing-based attacks.
How To Prevent Ransomware Infection
Network security is best implemented in layers, and preventing ransomware is no different. The more of these security practices you have in place, the most you mitigate your risk of ransomware infection.
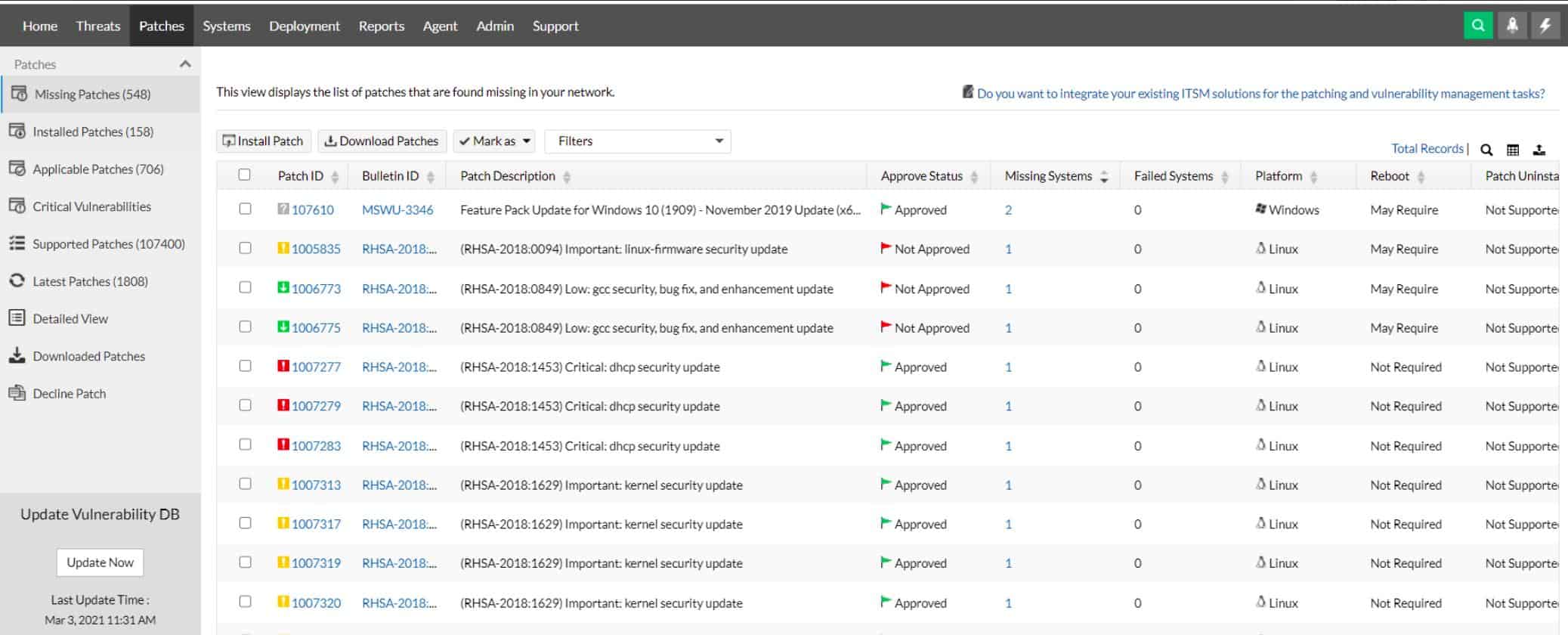
Patch And Update Your Devices
It’s easy to fall behind on patches and updates, but this lapse in security awareness can prove to be disastrous if not corrected. Ensure your servers, PCs, and network storage devices are patched and up to date at least once a month.
Keep an ear out for any recently discovered zero-days or emergency security patches that might need to be installed ahead of schedule. Keeping a strict patching schedule is an easy way to win half the battle when it comes to preventing ransomware. Larger organizations can benefit from automated patch deployment using several patch management tools.
Secure Your Ports And Services From Ransomware
One of the most popular attack vectors for ransomware has been vulnerable to remote desktop services. If devices on your network utilize the remote desktop protocol to gain access externally, you’ll want to ensure you’re using best practices.
Only allow remote desktop over a Virtual Private Network (VPN). In the past, it was enough to use remote desktop services with a nonstandard port and a strong password. Today, this is not enough to keep your network secure. Attackers are now using sophisticated port scanning tools to find services over non-standard ports and then running powerful brute force attacks to gain access.
Critical vulnerabilities such as BlueKeep are continuing to be discovered, leaving networks vulnerable to wormable ransomware attacks. If you must use remote desktop services, ensure that it is only accessible from inside a VPN, or from a list of whitelisted IP addresses. This will also help with your online privacy when using public networks.
Consider using nonstandard ports for specific services. While this isn’t foolproof, it does add an extra layer of obscurity that will cut down on bots that are probing networks looking for opportunities to cause trouble.
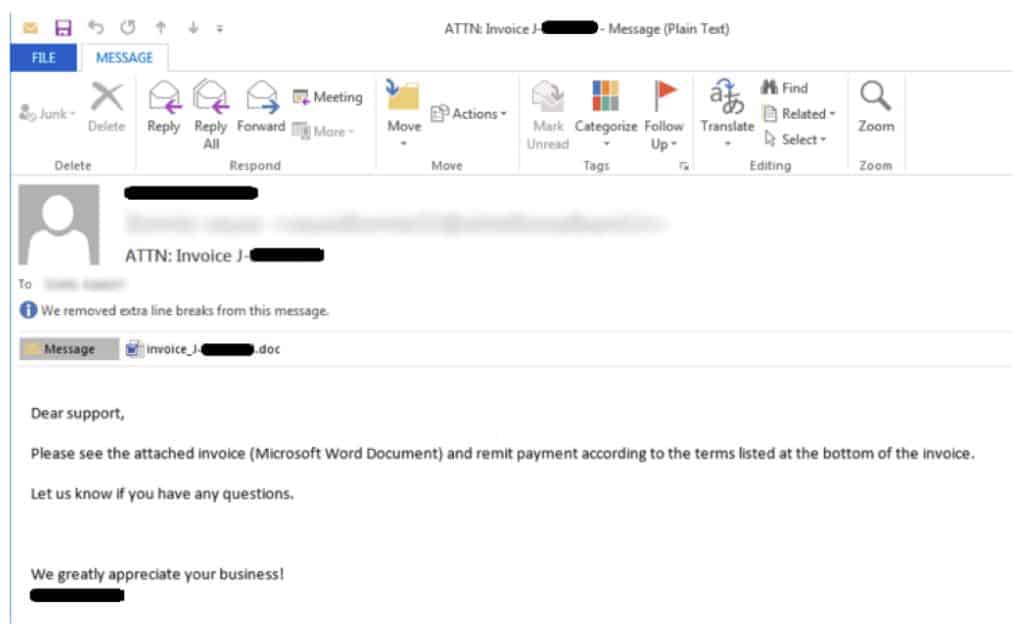
Stopping Ransomware In Your Email
Email is the number one attack vector when it comes to getting infected systems with ransomware. Oftentimes attackers will use well-crafted emails disguising their malware was an invoice, word document, or “encrypted” message.
The victim will click on the word document which usually prompts them to continue to a link to see the rest of the document. This link performs a drive-by download and begins the spread of ransomware.
There are dozens of different methods attackers could use to trick their victims into downloading and executing their ransomware. Email filtering is critical when it comes to weeding out some of the low hanging fruit.
A common way for ransomware to spread is through malicious macros embedded in word documents. Most enterprise firewalls now have preconfigured macro filtering which will not only scan a document but also analyze if it contains any malicious macros.
Denying all documents that contain macros and whitelisting only specific domains is a simple way to completely cut out an entire avenue of attack. Other products such as Vipre Email Security can detect and remove links that it finds are malicious before a user has a chance to click on it.
Other best practices such as running your email through a blacklist service, and restricting specific extensions such as .exe, .bat, and .jar, will also aid in fighting both ransomware and other viruses as well.
Another major part of email security is educating your team on best practices, and the identification of dangerous emails. We’ll touch more on education later.
Restricting Access To Prevent Ransomware
If ransomware does find itself on someone’s computer, there are a few restrictions you can put in place to help isolate and stop the execution and spread of ransomware if it does get downloaded on a PC in the network.
Ensure users do not have administrator privileges. When local users have unrestricted access to their PCs this gives the ransomware full rein to not only infect the local PC but begin probing outward and infecting other shares on the network.
Most ransomware will try to take specific actions before beginning file encryption. Locking down a user’s access to local shadow copies, software installations, and having a moderately strict UAC in place could be enough to stop the full execution of most ransomware.
Ensuring your network is segmented by security groups and subnets will also limit the scope of the damage if ransomware does manage to execute on a PC in your network.
Most ransomware takes advantage of these weak environments and doesn’t have the ability to perform privilege escalation. Having thorough local and domain restrictions in place could prevent the entire network from becoming compromised.
An often overlooked method of stopping ransomware is restricting what can run from the AppData and Temp folders. A large number of ransomware attacks leverage the AppData and Temp folders to infect a network. Under group policy you can and should restrict what types of files are allowed to run from these folders.
Blocking files likes .exe, .bat, and .js from running inside these folders can stop even the trickiest ransomware in its tracks, even if it does get past the firewall and local antivirus.
Restricting the AppData folder is a powerful move against the threat of ransomware, but does come with its inconveniences. You’ll often find yourself whitelisting legitimate applications such as LogMeIn or GoToMeeting, as there are a host of real programs that use the AppData folder.
All of these security policies can be pushed out via a login script, or group policy.
Prevent Ransomware Downtime With Backups
Even with the best network & device security practices in place, there will come a time where threats will slip through the cracks, and that might require files and programs to be recovered from a recent backup. Incremental backups should already be a core part of any business network to avoid downtime.
While solid backups won’t necessarily prevent the spread of ransomware, they will certainly give you peace of mind and act as an insurance policy if anything does go wrong. Just make sure you’re following best practices when it comes to backing up critical data on your network.
Make sure your backups are kept off-site or in cloud storage. In the event of a disaster, whether that be ransomware, an earthquake, or break-in, you’ll want copies of your files to be kept off-premises.
Having an off-premise backup solution gives you the flexibility to initiate a restore even if the entire office is down, or needs to be relocated. Off-site backups might take time to recover from depending on your internet speed, and the amount of data you have.
Off-site backups are an excellent solution especially when paired with a more readily available recovery method that is located on-site.
There are a number of online backup solutions you can choose from, here are a few of our favorites.
Keep incremental backups on hand for quick deployment. When you’re recovering from a disaster or ransomware attack you’re not just protecting your data, you’re saving the company from potential downtime.
Depending on the size of your organization, an hour of downtime could cost tens of thousands of dollars. Ransomware has crippled entire local governments that did not have a proper backup policy in place. Security software like StorageCraft’s ShadowProtect can take ‘snapshots’ of your network and recover to any point in time that you specify. Having the power to restore your network from an hour before a disaster, pays for itself on day one.
Keep your backs secured. There’s no point in investing your time and money into a backup solution if it gets compromised along with everything else during a ransomware attack. An external drive plugged into a server will get encrypted data just as fast as anything else on the network.
Backups should be performed ideally from a separate machine, isolated from all other traffic in the environment. This protects your backups but still gives you quick access to mount virtual drives on the fly.
The second component of this is ensuring your backups are encrypted and write-locked. This not only prevents accidental changes to backed up data but also stops ransomware from encrypting the backups if the isolated PC was somehow compromised.
The Best Ransomware Protection Software
Our methodology for selecting a ransomware protection tool
We reviewed the market for ransomware protection systems and analyzed tools based on the following criteria:
- Constant system security monitoring
- File protection
- Alerts that spot unusual activity surrounding file encryption
- A system that implements automated remediation to shut down encryption activity
- Protection for vital system files
- A free trial or a demo that provides an opportunity for a cost-free assessment
- Value for money from a package that provides security monitoring at a reasonable price
With these selection criteria in mind, we identified some useful systems that you should consider in order to protect your system against ransomware.
With all of these security policies and recovery measures in place, you’ll still want to rely on proactive real-time security software that can monitor your network and stop ransomware in its tracks. Here’s a quick summary of our top picks for ransomware protection.
- ThreatLocker EDITOR’S CHOICE This cloud-based system has a simple but effective solution to ransomware and malware protection because, by default, it blocks all software from running and then permits only systems that you specifically register in a whitelist to execute. The package is also available for integration with all the major RMM systems. Register for the free demo.
- ManageEngine Vulnerability Manager Plus (FREE TRIAL) Spot the exploits that ransomware uses to infect your system and fix them before any malware hits your system with this package of security tools. Runs on Windows Server. Start 30-day free trial.
- ManageEngine Log360 (FREE TRIAL) This large package of security tools provides activity logging and file integrity monitoring with automated responses to block unauthorized activity, such as file encryption. Runs on Windows Server. Start a 30-day free trial.
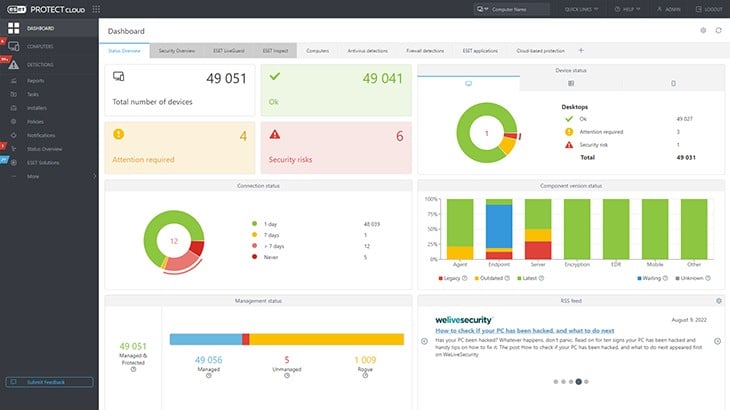
- ESET Protect (FREE TRIAL) This on-device anti-malware system can be upgraded into a company-wide XDR system and there is also a managed security service available. Runs on Windows, macOS, Linux, iOS, and Android. Start a 30-day free trial.
- CrowdStrike Falcon Prevent This device-based next-generation anti-virus protects from a range of malware types, including ransomware. Available for Windows, macOS, and Linux.
- SolarWinds Security Event Manager (FREE TRIAL) The best holistic ransomware prevention software for businesses. Feature reporting, auditing, and customizable alert templates.
- Malwarebytes Endpoint antivirus protection with built-in ransomware protection.
- Kaspersky Anti-Ransomware Tool Free standalone installer. Available for both home and business protection.
1. Threat Locker (ACCESS FREE DEMO)
ThreatLocker simplifies the strategy needed to deal with ransomware – it blocks all software from running. No matter what programs get onto your endpoints, they can’t run. The platform lets you set up an “allow list,” which is ThreatLocker’s name for a whitelist. Software on that list will be allowed to execute, so as long as you don’t whitelist ransomware, your endpoints are completely protected without the need to back up data.
Thanks to the block on execution, system managers don’t have to worry about users installing their own preferred software and any type of malware is disabled by the strategy. There is a possibility that malware will sneak onto your endpoints disguised as another, legitimate program. For example, a piece of ransomware can be made with the name word.exe on its containing file. However, ThreatLocker can tell the difference between a real program and a fake by looking at attributes of the executable file, such as size.
Key Features:
- Blocks all software by default
- Allows named software to run
- Controls resource access by permitted software
Why do we recommend it?
The ThreatLocker strategy of blocking all software from running by default prevents any chance of a ransomware of attack. There isn’t any way an unauthorized program can run on a device that is protected by ThreatLocker so there isn’t even any chance that an evasive process could be launched to somehow work around the execution block.
Endpoint software producers charge a fee for every installation, so license management is important. If you bought five licenses for a piece of software, you need to make surer that only five copies are installed on your site. With the Allowlisting feature of ThreatLocker, you can see how many endpoints have each piece of software. You install it yourself and you approve it on a per-device basis. So, other users who work on endpoints on which you didn’t install that package can’t have it. If they try to install it themselves, it won’t work, and if a piece of ransomware masquerades as that legal software, it won’t run.
The entire ThreatLocker platform has a range of components that enable you to focus your system security on protecting access to applications rather than to devices. This is a necessary move nowadays because many of the applications that businesses use are SaaS packages that are hosted on cloud servers. So, for businesses that entirely use SaaS applications, focusing security on local devices is useless. With the ThreatLocker system, you can secure access to any application anywhere.
Who is it recommended for?
The ThreatLocker package will appeal to all businesses that have networked endpoints – which is just about all businesses. The full package has a lot of other functions such as application access controls that operate on your hosted systems and cloud services. It also provides a USB access control system.
Pros:
- Suitable for hybrid networks
- Implements a Zero Trust Architecture (ZTA)
- Creates a virtual network
Cons:
- Doesn’t include a full access rights manager
The ThreatLocker approach to dealing with ransomware and managing distributed teams is difficult to understand. The best way to learn the ThreatLocker concepts is to access a demo of the system.
EDITOR'S CHOICE
ThreatLocker is our top pick for a ransomware prevention tool because it automatically blocks all software from executing. This simple strategy means that all malicious systems are immediately dealt with. This includes advanced persistent threat invasion strategies with systems such as remote access Trojans as well as ransomware and malware. You allow your authorized software to run by registering it in a whitelist. This approved list of systems is also useful for periodic malware removal scans – anything that isn’t on the list is deleted. Between scans, the block on all executables also prevents users from breaking your software licensing agreements by installing their own favorite utilities.
Download: Get FREE Demo
Official Site: https://portal.threatlocker.com/signup.aspx
OS: Cloud-based
2. ManageEngine Vulnerability Manager Plus (FREE TRIAL)
Head off disasters by closing down exploits with ManageEngine Vulnerability Manager Plus before ransomware producers discover them. This is a vulnerability scanner with a bundled-in patch manager and it can even spot zero-day weaknesses and close them.
You cannot predict what system weakness the next wave of ransomware will use to get into your system, so harden everything against any possible attack with this software package. The Vulnerability Manager Plus package runs on Windows Server but it reaches across your network to scan all of your devices running Windows, macOS, and Linux. The scanning cycle occurs every 90 minutes and it looks through the software inventory of each device, looking for unauthorized packages and software that has been flagged as end-of-life.
Key Features:
- Vulnerability scanning
- Patch management
- System hardening
- Web server risk assessment
Why do we recommend it?
ManageEngine Vulnerability Manager Plus is an on-premises package that tunes your IT system to make it less vulnerable to attack. The service looks for security weaknesses that would help intruders get in or malware, such as ransomware, to download and run. The package includes a patch manager.
All current and authorized software and OSs are scanned for risk. This involves checking their patch statuses and looking at their configurations. If patches are available, Vulnerability Manager Plus triggers the patch manager that is part of the bundle. Software and hardware misconfigurations and highlighted for action and the system can even generate scripts to realign device and software interactions to remove entry points for malware and intruders.
Web assets are particularly exposed to potential attacks and so the vulnerability risk assessment service in this ManageEngine system pays close attention to current assets, looking for the opportunities that hackers could use to infect websites or attack your services.
Who is it recommended for?
This package is suitable for all businesses. It protects endpoints running Windows, macOS, and Linux and it runs on Windows Server. ManageEngine provides a Free edition of Vulnerability Manager Plus, which has all of the functions of the paid system but is limited to protecting 25 computers.
Pros:
- Can spot security weaknesses even before they are publicized
- Includes systems to detect and close down exploits
- Provides an automated patch manager in the suite
- Logs all discoveries and actions for compliance reporting
Cons:
- Doesn’t extend to cloud platforms
ManageEngine provides a Free edition of Vulnerability Manager Plus, which is limited to protecting 25 devices. The paid versions are offered for a 30-day free trial.
3. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 provides a threat intelligence feed, which lists well-known hacker source addresses and recently used methods. This enables the SIEM to scan through log records and network activity to look for communications from those sources. In the meantime, a file integrity monitor looks for unexpected actions on files and you can specify that it alerts on any encryption action.
Key Features:
- IP address and domain blacklist
- Activity logging
- File integrity monitoring
- Anomalous behavior detection
Why do we recommend it?
ManageEngine Log360 has multiple methods to detect and block ransomware. The core of the package is a SIEM but it also includes a file integrity monitor, which would immediately spot ransomware actions. The tool includes a threat intelligence feed, which would earn the security system if a new ransomware rollout had begun.
The package includes user and entity behavior analytics (UEBA). This records all activity per user account and per device. Malware, such as ransomware can be spotted when activity on an endpoint suddenly changes.
The ManageEngine system includes a lot of different modules, which could be difficult to coordinate. However, a security orchestration, automation, and response (SOAR) unit in the bundle takes care of that problem. This provides a single interface where you specify actions to implement on the detection of a threat. These actions will involve several modules and also third-party tools.
When a ransomware encryption action is identified, your system will immediately suspend the user account involved and block all communication with whatever IP address has been identified as being involved in guiding the malware.
Who is it recommended for?
As it is a very large package, the tool has a high price tag. There isn’t a free edition for this tool, so there isn’t any way that small businesses could sneak in and get this system without paying the full price. ManageEngine produces an edition for LANs and another for WANs.
Pros:
- Sensitive data protection for standards compliance
- Automated responses
- Interaction with third-party tools
Cons:
- Too big for a small business to manage
ManageEngine Log360 is an on-premises package that runs on Windows Server. However, it is able to gather logs from other operating systems, network devices, and cloud platforms. It interfaces with third-party tools, such as firewalls and malware to gain further intelligence on system activity. You can examine Log360 with a 30-day free trial.
4. Eset Protect (FREE TRIAL)
ESET Protect is an anti-malware system that you install on each endpoint. The tool will protect mobile devices as well as your computers. Its software runs on Windows, macOS, Linux, iOS, and Android. Even the lowest package, ESET Protect Entry, comes with a cloud console that lets you see all of the activities on each device and across the enterprise.
Move up to higher editions for more features. In order of cost and complexity, the found plans of ESET Protect are Entry, Advanced, Complete, and Elite. With the Advanced package, you are moving into XDR territory. This service provides an extra layer of protection against ransomware and other malware because it performs threat detection on pooled data. Go up to the Complete plan to get a vulnerability scanner and patch manager. This seeks out the weaknesses in your system and dealing with those issues reduces the likelihood of being attacked by ransomware.
Key Features:
- Local protection unit for speedy response
- Cloud-based threat hunting
- Company-wide threat intelligence
Why do we recommend it?
ESET Protect is a range of editions that provides different combinations of on-premises and cloud elements. That endpoint unit continues protection even if the device is isolated from the network – that’s a service that you don’t get from cloud-based systems with thin on-site data collection agents.
ESET Protect Complete also gives you protection for cloud services. This includes your email system, which can also be protected if you host it on your site. The Elite plan adds on a coordinated response mechanism that can also involve third-party tools. All plans can be used in a multi-tenanted architecture for managed service providers.
ESET also offers an MDR, which stands for Managed Detection and Response. This gives you the service of the ESET Security Operations Center, where the company’s technicians will watch over the console for your ESET Protect implementation and take appropriate action where necessary. However, it is possible to set up automated responses, which reduces the need for cybersecurity expertise.
Who is it recommended for?
You need to have the ESET endpoint protection system installed on each of your computers and you also need at least two other on-premises ESET security tools in order to get the full XDR services of the ESET platform. The tool can spot ransomware actions and shut them down automatically.
Pros:
- Plan levels to suit all budgets
- Automated detection and response on the device
- A managed service option
Cons:
- Must have at least five endpoints
The first three plans are packages for a minimum of five devices and the Elite edition will cover a minimum of 26 devices. ESET Protect is available for a 30-day free trial.
5. CrowdStrike Falcon Prevent
CrowdStrike Falcon Prevent is a next-generation anti-virus system that installs on endpoints. The package is available for Windows, macOS, and Linux. The Falcon brand is a family of cybersecurity products that work in combination with Falcon Prevent. The Falcon Prevent system is the base product in the range and it acts as an endpoint agent for other Falcon systems, which are all cloud-based.
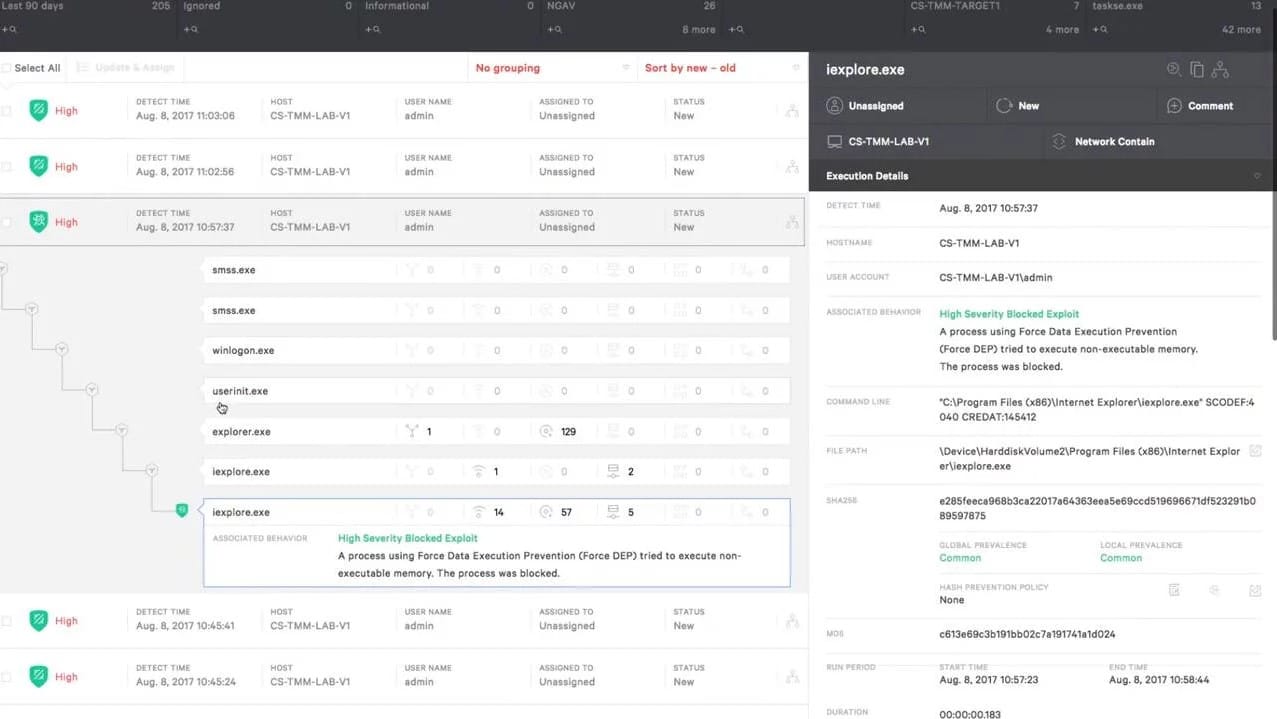
The Falcon Prevent system is able to detect a range of malware, including ransomware. The detection system in the tool is anomaly based. This means that the package establishes a baseline of normal activity per user on the device and then looks for activity that doesn’t fit into that pattern. This anomalous behavior is then flagged for further investigation.
Key Features
- Can spot fileless and malware-free attacks
- Looks for unusual activities
- Updated by the Falcon platform
- Continues working if the device is offline
Why do we recommend it?
CrowdStrike Falcon Prevent is an on-device package that provides a next-generation anti-virus service. This system will continue to function if the hosting device is disconnected from the network as part of a ransomware attack’s defense mechanism. However, it excels if it is able to communicate with the coordinating server on the CrowdStrike cloud platform.
Ransomware detection. The system gets Indicators of Attack (IoAs) from the Falcon platform and this guides threat detection. The tool will establish a baseline of normal activity and then look for different activity. Those unusual events are compared to IoAs.
Ransomware blocking. Unexpected downloads are blocked by isolating the file and drawing the user’s attention to the new file. Quarantine files can be released manually.
Ransomware response. If suspicious activity is identified, Prevent will kill its processes.
Ransomware remediation. The Prevent system cleans up after a confirmed attack by removing all files related to the blocked malware.
Who is it recommended for?
The high price tag of the CrowdStrike system will deter small businesses. However, for mid-sized and large organizations, this AV protection system is scaleable because if you buy one more computer, you just need to install the Prevent package on it to get it covered. The Prevent package can easily be enhanced by the CrowdStrike XDR.
Pros:
- Fast response, thanks to threat intelligence
- Flexible approach with anomaly detection that can block zero-day attacks
- Also identifies intruder activity
- Can link together suites of malware for detection and remediation
Cons:
- Only acts once ransomware is already installed and triggered
You can start with a 15-day free trial.
6. SolarWinds Security Event Manager
SolarWinds Security Event Manager (SEM) is a highly regarded security tool to prevent ransomware for medium to large-sized environments. Event Security Manager delivers enterprise-level network security at small business prices. Pricing starts at $2525 (£2019) but you can get a 30-day fully functional trial for free to make sure it’s the right fit for you.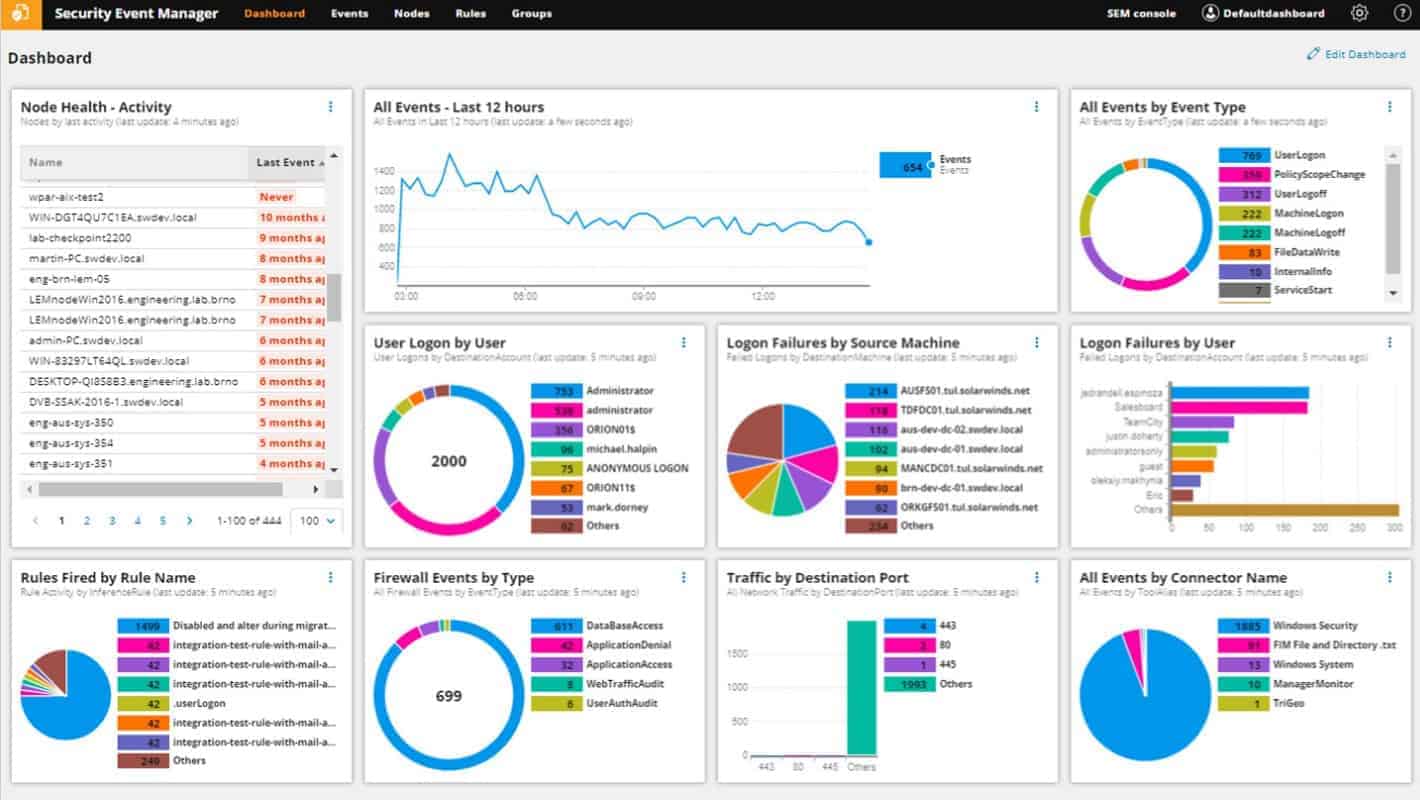
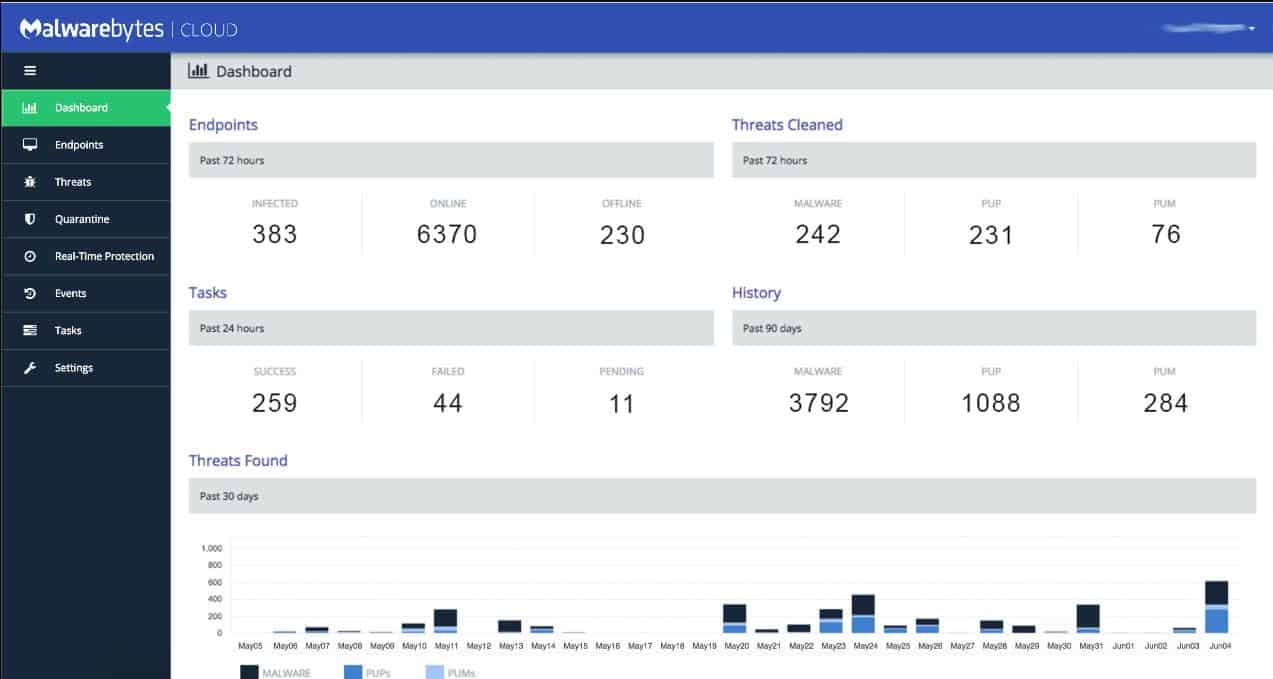
The dashboard of Security Event Manager monitors and alerts you to a number of security-related events on your network and works proactively to keep devices on the network secure and up to date. While this program has dozens of features that make it a powerful security tool, we’ll focus primarily on its anti-ransomware properties for this article.
Key Features
- File integrity monitoring
- System security monitoring through log analysis
- Threat detection
- Automated response
- Compliance reporting
Why do we recommend it?
SolarWinds Security Event Manager is a SIEM system that you host on your own server. This is a good service for ransomware blocking because it is right there on your site and not on a remote cloud server. In addition, this service can spot unusual file activity and attempts to move to other endpoints.
Community-backed intelligence and threat-based detection. Security Event Manager (SEM) leverages a number of sources to always have the latest information on evolving threats and the latest evolutions of ransomware. The SEM platform is constantly updated with real-time analytics, attack vectors, and malicious command and control servers to ensure nothing slips through the cracks.
Deep dive and perform forensic analysis with detailed logging. Easily sift and sort through your network logs to customize and improve ransomware threat-based detection. Compile logs from servers, applications, and other network storage devices with customizable search functions and visualization features.
Automatically detect and stop ransomware behavior. When an account becomes compromised it can be difficult to identify that account and disable its access. With SEM’s activity monitor, you can set predefined thresholds that can either alert you or take specific action against that account. Quickly identify and stop an account when it is behaving maliciously, changing file extensions, or attempting privilege escalation inside your network.
Who is it recommended for?
SolarWinds tools cater to large organizations. The threat detection service is fast and, being on your site, is harder for ransomware to evade by blocking internet connections. The tool can implement automated responses, such as blocking all communication with an infected endpoint to prevent the ransomware from moving.
Pros:
- Is easy to deploy – features numerous done-for-you templates, dashboards, and monitors
- Provides automated ransomware protection with artificial intelligence
- Over 700 pre-configured alerts, correlation rules, and detection templates provide instant insights upon install
- Threat response rules are easy to build and use intelligent reporting to reduce false positives
- Built-in reporting and dashboard features help you track issues and document performance over time
Cons:
- Feature dense – requires time to fully explore all features
Overall, SolarWinds Security Event Manager has hundreds of out-of-the-box correlation rules which can alert you to suspicious behaviors in real-time. You can also set up new rules with thanks to the normalization of log data. The dashboard gives you a command center for identifying potential network vulnerabilities.
SEM operates in a Windows environment and can be installed on Windows Server 2012-2016. SolarWinds offer a 30-day free trial for SEM.
7. Malwarebytes Anti Ransomware Software
Malwarebytes (MBAM) first found its way to market by providing quality consumer-grade malware protection for individual workstations. Fast forward a few years and Malwarebytes is now bringing that same level of quality ransomware protection to the business environment with its business-grade anti-malware program. While Malwarebytes offers an umbrella of network protection services, we’ll just focus on its ransomware defense capabilities.
In the early days of Malwarebytes ransomware prevention software was available as a beta standalone product. This technology is now a core feature built directly into Malwarebytes Premium which is available on Android, Windows, and Apple platforms. Malwarebytes Premium starts at $39.99 (£31.99) a year per device for consumers and $119.97 (£95.96) a year for 3 devices for small businesses. You can get a full breakdown of their business pricing here. Overall it’s an excellent internet security package.
Key Features
- Protects Windows, macOS, iOS, and Android
- Constant endpoint security monitoring
- AI-based threat detection
- Creates restore points for system rollback
Why do we recommend it?
Malwarebytes anti-ransomware software is available in three levels: Endpoint Protection, which provides anti-malware for each device, Endpoint Protection and Response, which includes AI threat prediction, and Managed Detection and Response, which provides the technicians to run your endpoint protection for you. This is a centralized system with an agent for each device.
Real-time ransomware prevention. MBAM monitors each endpoint live to detect ransomware activity. This includes recognizing remote code execution, malicious changes to the registry, and rouge encryption on the machine.
Ransomware detection and machine learning. Threat profiles built from machine learning help to proactively identify and stop ransomware before it can spread. This technology keeps you ahead of ransomware variants that traditionally avoid known malware fingerprinting.
Ransomware recovery options. Malwarebytes utilizes it’s Ransomware Rollback Technology to create a local cache of your systems and data files. This cache is protected and can be reactivated in the event ransomware does get through.
Who is it recommended for?
Malwarebytes produces solutions for small businesses, mid-sized businesses, and large businesses. This is a hybrid solution with the console and the threat detection system based in the cloud and agents for endpoints that upload activity data and receive response instructions. Agents are available for Windows and macOS.
Pros:
- Provides high-level insights of threats and asset heath from devices across the entire network
- Identifies both malicious processes and behavior
- Offers botnet protection as well as protection from browser-based threats
- Offers a free version
Cons:
- Would like to see a longer trial of the full product for testing
8. Kaspersky Anti Ransomware Tool
Kaspersky’s Anti Ransomware Tool (KART) has recently been revamped and made free to anyone who would like to try it. Their premium solutions offer both home and business users automatic patch management, software support, and 20+ other threat detection technologies. KART is currently priced at $39.00 (£31.99) for 3 home devices and $53.99 (£43.19) for 3 devices in a business environment. Kasperksy’s anti-ransomware tool is compatible with Windows OS environments.
Key Features
- Offered in free and paid versions
- Runs on Windows
- Blocks unauthorized encryption
Why do we recommend it?
The Kaspersky Anti Ransomware Tool is a free package for Windows. This system relies on Kaspersky’s excellent track record in spotting and combatting ransomware – many ransomware types were first discovered by this company. The free tool provides adequate protection and there is a paid endpoint protection system available that has more capabilities.
Blocking encryption at the source. Much like the other security tools, KART can detect and block both local remote executions of ransomware. It can detect when files encryption is being attempted and stop that process from finishing.
Works in conjunction with other tools. KART has the unique ability to run along with other antivirus software. While most antivirus tools will fight each other and cause problems, KART can seemingly run side-by-side other existing security endpoints.
Detects more than just ransomware. In addition to ransomware attacks, KART can detect illicit crypto-mining, adware infections, and risk-ware objects on endpoint PCs.
Who is it recommended for?
Kaspersky produces this free ransomware protection system for businesses and home users. The business version can be installed on up to 50 devices, so this is a good solution for small businesses. Larger companies will have to move up to the paid Endpoint Security Cloud. This protects devices running Windows, macOS, iOS, and Android and provides a central console on the cloud.
Pros:
- Completely free
- Simple installation – little configuration needed
- Great for small businesses and home user
Cons:
- Not the best option for enterprise networks
They offer a free download for home use.
See also: The Best Ransomware Protection Tools
Conclusion
It’s clear that the ransomware threat is here to stay, and is only getting more advanced as time goes on. The good news is that there are now more software tools and device security measures you can deploy right now to help keep your network safe.
All of the tools mentioned above are available as free trials, so try out a few and see which ransomware protection is right for you.
Have you experienced a ransomware attack before? Were you able to recover? Let a comment about your experience in the comment section below.
Protect Your Network Against Ransomware FAQ
How to prevent a WannaCry ransomware attack?
The first step to take in order to prevent WannaCry attacks is to upgrade your version of Windows or Windows Server. WannaCry doesn’t attack Windows 8, Windows 10, Windows Server 2008, Windows Server 2012, or Windows Server 2016. Make regular backups of your system so that everything can be restored as soon as an attack occurs.
Does encrypting your hard drive prevent ransomware?
No. Encrypting your hard drive is a valid security measure against data theft. However, encrypted data can be encrypted again. When your own encryption is underneath the ransomware encryption your data is rendered just as inaccessible as it would be if you hadn’t encrypted it.
Can ransomware spread through a network?
Yes. The traditional entry point of ransomware is through email attachments. However, the replication modules of a virus suite can explore and exploit known vulnerabilities to reach other devices that are accessible to the infected computer over the network.