Effective IT asset management is crucial for organizations seeking to optimize their technology infrastructure, streamline operations, and ensure compliance. IT asset management (ITAM) refers to the practices, tools, and processes used to track and manage an organization’s IT assets throughout their lifecycle.
The assets that need to be tracked include hardware, software, network devices, and other technology components that support day-to-day business functions. By properly managing these assets, businesses can minimize risks, reduce costs, and improve operational efficiency.
In today’s digital landscape, IT asset management is more critical than ever. As organizations scale and adopt new technologies, the complexity of managing IT assets also increases. Without an efficient ITAM system in place, businesses may struggle to maintain visibility over their assets, leading to mismanagement, security vulnerabilities, and compliance issues. Additionally, inefficient asset management can result in unnecessary expenditures, as organizations may overlook unused or underutilized resources.
This comprehensive guide on IT asset management will explore the core principles of effective asset management, the benefits it brings, and how organizations can leverage ITAM tools to optimize their IT operations. We will discuss the key features and capabilities of ITAM solutions, such as asset tracking, software license management, and lifecycle management, as well as provide insights into the best practices that ensure effective asset governance.
Whether you’re an IT manager, network administrator, or business leader, understanding the importance of IT asset management is essential for driving cost savings, enhancing operational efficiency, and mitigating risks. By implementing the right tools and strategies, organizations can unlock the full potential of their technology infrastructure and stay ahead in a rapidly evolving digital world.
The International Association of Information Technology Asset Managers
The International Association of Information Technology Asset Managers (IAITAM) has been a leading force in the drive to nail down standard practices for IT asset management.
IAITAM defines an ITAM lifecycle, which includes the following stages:
- Request
- Procure
- Receive
- Stock
- Deploy/Monitor
- IMAC (Install-Move-Add-Change)
- Retire/Re-use
- Disposal
Some models insert a “Support” stage between Deploy/Monitor and IMAC. Other models truncate Receive, Stock, and Deploy/Monitor into one stage, called “Deployment.” In this guide, we will follow the IAITAM model.
Request, Procure, Receive, and Stock
The ITAM Request stage is an issue of company budgetary policy. This is a function of your regular accounting procedures and deals with how purchases are approved. If a departmental budget is set annually, then the IT manager has to decide whether new equipment is needed.
If serviced departments lead the purchase process by identifying a need for extra infrastructure, then a negotiation with the IT department needs to take place. The ITAM oversight in this stage is closely tied to your company’s IT service management policies.
The Procure stage is usually controlled by the IT department. It may be possible to fulfill the request from existing stock. This would be the case if there were staff who recently left, making computers and software licenses available for other users.
The need to reduce procurement costs also requires IT equipment buyers to research the market and establish the cheapest supplier for frequently requested hardware and software. It would also be a good idea to establish an account with suppliers who are willing to give discounts for regular purchasers.
The Receive stage is another area that is down to company policy. If you have many locations, you might want to centralize storage. However, that strategy would require an extra transport leg for final delivery. Your receiving strategy will depend on the size of your organization and the number and distance of all of its sites.
With the Stock phase you start to move away from the need for accountancy tools and into a requirement for inventory registers. The tools supporting this stage of the lifecycle are little different than those needed for standard asset management. The IT manager needs to ensure that there is as little of IT assets in stock as possible.
Experience may have taught you to keep some pieces of equipment spare in order to cover for failure of deployed equipment. Successfully agreeing support contracts for both hardware and software with service level agreements that provided rapid replacement would enable that safety stock can be reduced.
Maintenance contracts not only enable a reduction of stock, but they add a cost incentive to the policy of keeping spare capacity low. Although guarantees and support may be built-in to the purchase price of both hardware and software, they shouldn’t be regarded as “free.” The extension of support contacts usually incurs a fee, so you should account for that sum as part of the initial purchase price.
Keeping spare equipment and having unused software licenses incurs that support cost. So, by running down the maintenance contract without being used, that spare stock is costing you money.
Deploy/Monitor
If you are commencing an ITAM policy in an organization that is already operating, then the Deploy/Monitor phase will be vitally important to your implementation. Establishing an equipment inventory is the bedrock of IT asset management.
It is not uncommon for businesses to lose track of exactly what physical resources it has. Paid-for software licenses are easier to quantify. However, not everyone documents the number of copies of software that are in use within the organization.
Fortunately, there are system monitoring tools that can audit your existing system, making an inventory of hardware and a registry of all installed software. These tools make drawing up a starting point for your ITAM strategy a lot easier.
Performance monitoring has a second benefit for ITAM. It can help you spot excessive provision of services or overtaxed infrastructure. Network management tools can help you deploy traffic-shaping in order to get the best value out of your resources.
Contract values
An issue already mentioned in the Stock section above lies with maintenance contracts and support from suppliers. The measurement of SLA performance is more common on the side of the provider of a service rather than on the part of the customer. As with insurance policies, the benefit of an SLA in a support contract is only measurable in the customer’s accounts when things go wrong.
The supplier has a greater incentive for service delivery policies and SLA auditing than the buyer. Contract obligations need to be a consideration of a supplier’s system right back at the design phase. This creates a requirement for contact channels to be put in place and monitoring and team management software should be selected to guarantee performance. These monitoring systems should also include performance reporting.
Contract compliance data is rarely delivered to customers routinely. Instead, it acts as an insurance policy for the supplier as proof against complaints or potential claims from customers for SLA breaches.
Support performance becomes an issue for customer companies when they run in-house support departments. In this instance, the support department has performance obligations to business departments and in turn, needs to measure supplier support delivery to ensure their own compliance. In this example, Help Desk and MSP software needs to be provided to the IT department and should be accounted for as part of the total cost of ownership.
IMAC (Install-Move-Add-Change), Retire/Re-use and Disposal
The IMAC and Retire/Re-use stages of the asset lifecycle are closely linked to the Stock and Deploy/Monitor phases. Maintenance contracts are just as important for cost measurement in these phases.
IMAC stands for “install, move, add, change.” This phase guides you to adapt the layout of your network and the methods you use to deliver software to your staff and customers in order to optimize performance and reduce costs.
The Retire/Re-use stage is closely linked to IMAC. A result of utilization analysis is the retirement of some equipment or software, which can be reallocated. This analysis might also reveal that you have too many licenses for a particular software package or device type.
The Disposal phase is a function of standard accounting asset depreciation methods. These will give you a lifespan of each piece of equipment. This tells you when the service life of a device will expire. That piece of hardware can then be sold off to recover some money.
There are a number of strategies that you should use to reduce TOC in the IMAC and Retire/Re-use stages.
Reduce network infrastructure costs
An example of measures that should be taken in order to improve asset utilization is traffic-shaping.
During operations, you should monitor traffic levels on your entire network, on each device, and on each link. It is normal to experience a trend increase in activity, so your existing infrastructure will eventually become overwhelmed. Requests for new applications and the addition of new users will also put strain on your system.
Rather than planning network capacity for the maximum expected traffic volumes, it is more cost-effective to manage usage. All networks naturally experience peaks and troughs in demand. Traffic-shaping seeks to manage usage to switch tasks that are not time-sensitive to off-peak times.
At any one moment, your network carries traffic that needs to be delivered at the fastest possible speed, such as video streams and VoIP, and traffic that is not so urgent, such as email. All of these applications will be delivered in a timely manner, but some need to be delivered faster than others. Prioritizing traffic and queuing selective traffic slows down traffic where delays are un-noticeable. That means that you can spend less on your bandwidth provision.
Reallocate resources
Monitoring network traffic per link and trialing speeds between endpoints can help you detect bottlenecks. You need a network monitoring system that will alert you to specific devices becoming overloaded.
With the information that you gather on bottlenecks and link speeds, you can reconfigure the layout of your network, moving equipment from areas that show low traffic levels to increase the capacity in high traffic areas. This is an example of how an IT manager can prevent the cost of buying new equipment by altering the use of existing stock.
The introduction of virtualization is also a useful tool for software delivery. Virtual machines are easier to re-allocate because the movement of unused capacity towards areas of high demand can be performed automatically by VM software.
Avert hardware failure
Monitoring network devices and traffic levels on a network also enable an IT manager to head off potential problems in delivery caused by overuse. By installing network performance management software and setting performance threshold alerts, a network administrator can head off the strain on resources that would otherwise result in unacceptable performance impairment.
Tracking server performance also helps you to head off disaster. Keep an eye on CPU, RAM, and disk usage so that you can divert tasks to other servers or add on storage space before servers get overloaded. Similarly, monitoring usage can tell you where capacity has been over provided.
Reduce support costs
Self-service Help Desk functions and quick channels of communication can also reduce costs. Many Help Desk calls are for routine tasks that users could perform themselves, such as changing passwords. Other calls arise from a lack of training among the user community. That gap can be filled by a knowledge base that includes troubleshooting tips and usage guides.
The ability to track user activity and send them warning messages about potential problems also reduces the number of support calls – you tell them there’s a problem before they tell you.
IT asset management software and system tools
Accountancy tools are regularly used for asset and cost management. The extra equipment needs of IT asset management derive from the requirement for better information on equipment performance, location, and usage.
User Support
As mentioned above, effective user support is an essential part of IT asset management. IT staff can’t always test every usage case and interactions between installed applications before putting new services live within the business. This means there are always bound to be unaccounted for actions that will occur during normal operations. Enabling the user community to get in touch with the IT support staff quickly means that you can adjust the configuration of your equipment quickly if an unexpected hazard arises.
SolarWinds Service Desk is a typical service desk application that includes ticketing, a self-service portal, and a knowledge-base. This is an online service, so you don’t need to install any software on your own servers. This tool appeared in top spot of a recent market-wide report. The service was designed following ITIL standards and incorporates utilities and workflows that help you create, manage, and adapt IT systems. This makes it more than just a Help Desk system.
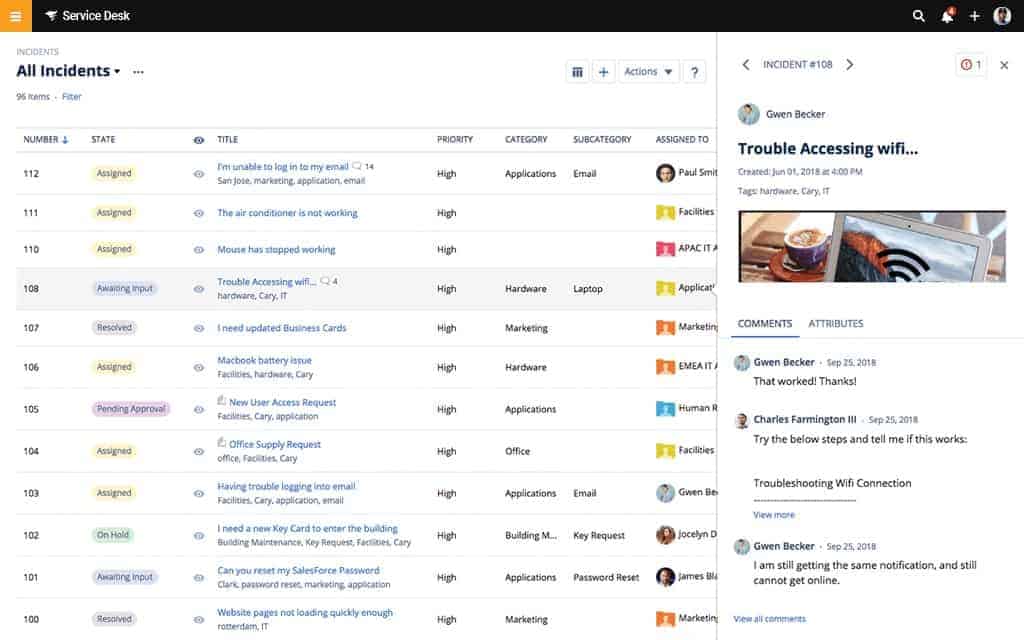
Many of the other software requirements for IT asset management are taken care of by SolarWinds Service Desk. It includes change management, release management, configuration management, service level management, and other essential IT asset management functions. The utility will constantly track equipment performance so you can be sure that all of your IT assets are operational and deployed effectively.
SolarWinds Service Desk is charged for on a per agent/per device basis, so it is suitable for businesses of all sizes. The service is packaged in three service levels. The entry-level package covers all help desk functions with more comprehensive IT asset management functions only available in the higher packages. You can get SolarWinds Service Desk on a 30-day free trial.
Device discovery and inventory
The key tool in an ITAM is the equipment inventory. You can’t track costs of your assets if you don’t know exactly what assets you have and where they are. Businesses that implement ITAM from their inception have a distinct advantage. Those that are already operating face problems.
Identifying equipment in stock is one problem and another is identifying equipment in use. The solution to tracking unused equipment is to create a policy of returning all equipment to a central physical storeroom.
Tracking equipment in use is an easy task if you have the right tool. Most network monitoring tools include an auto-discovery facility. This utility will detect all equipment attached to the network and create a log of them. The same mechanism that creates this inventory runs continually, updating the inventory automatically as equipment is added, moved, or removed. A tool that can generate a network map from the inventory will help you when you analyze equipment utilization.
The SolarWinds Network Topology Mapper is an example of a tool that creates an initial network inventory and topology map and then constantly monitors the network to keep those two information stores updated.

Equipment performance
Network performance monitors focus on the statuses of network devices. This category of system tool will alert you to problems with devices and allow you to set up warning thresholds so that you can get advanced warning of potential resource exhaustion. These tools also help you test end-to-end connection performance.
The SolarWinds Network Performance Monitor is a good tool for tracking the statuses of network devices. This tool integrates a network discovery facility and a network topology mapper. The NetPath utility in the tool shows you the performance of all of the links between two endpoints.
You will need a separate monitoring tool to watch over your servers. The SolarWinds Server & Application Monitor keeps a track on the statuses of your servers, enabling you to reduce load or add on resources when you see that CPU, memory, and storage are reaching their full capacity. This tool is also a useful input to traffic-shaping measures because it helps you to identify the software and services that are generating the most traffic.
Software management
As with your hardware, you need to compile an inventory of your software. You need to know how many instances of each package are in use and you need to know when updates are available for them and roll them out. Tools such as the Server and Application Monitor will do that for you.
If you deploy virtualization you will need a monitoring tool for that. Virtualization involves hardware, services, and applications, so it can be difficult to keep in good health by examining each element separately. The SolarWinds Virtualization Manager is a good example of a tool that can monitor VM implementations from one console.
User tracking
In order to work out which software is being used by the staff that it is allocated to, you could install user device tracking software that shows who is doing what and where – it provides device access tracking as well.
The information from a user device tracker also feeds into traffic analysis. You could look at the SolarWinds User Device Tracker. This tool has extra security features that enable you to detect rogue devices and prevent outsiders from using your resources.
Bandwidth monitoring
A bandwidth monitor will enable you to detect underutilized and overtaxed areas of your network infrastructure, enabling you to reuse resources effectively where they are needed.
A system such as the SolarWinds NetFlow Traffic Analyzer will help you detect overburdened links and reorganize your infrastructure. This tool can also help you implement traffic shaping to improve the quality of service that your network delivers to critical applications.
Asset tracking bundles
System monitoring and management tool providers tend to produce specialized tools for different types of assets. For example, you can get network monitoring systems, such as the SolarWinds Network Performance Monitor. However, to look at network traffic patterns, you need another package, called the NetFlow Traffic Analyzer. However, you can get both of these tools together with the Network Bandwidth Analyzer Pack.
The Network Automation Manager goes even wider, providing seven network monitoring and management modules. These are:
- Network Performance Monitor (NPM)
- Netflow Traffic Analyzer (NTA)
- User Device Tracker (UDT)
- VoIP & Network Quality Manager (VNQM)
- Network Configuration Manager (NCM)
- IP Address Manager (IPAM)
- SolarWinds High Availability
To get a bundle that manages software assets, you should consider the Hybrid Systems Monitoring pack. This bundle provides server and cloud platform tracking as well as application monitoring and management facilities. The modules in this package are:
- Server & Application Monitor (SAM)
- Virtualization Manager (VMAN)
- Log Analyzer (LA)
- Server Configuration Manager (SCM)
Outsourced asset management
All of the support and maintenance tasks of IT asset management can be outsourced to managed service providers (MSPs). An MSP can also assist with the capacity planning tasks of IT asset management by providing records of past resource usage. This information feeds into calculations of required infrastructure to match the needs of a natural increase in activity or expansion of service through the addition of new users, endpoints, and/or software.
The software tools required by an MSP are different from those required by an in-house IT Department. The main difference lies in the access procedures as all support activities will be carried out from a different location. The suite of tools needed for this off-site activity is called a “remote monitoring and management system,” or “RMM.”
Apart from the tools that technicians need to implement remote support and monitoring functions. The MSP needs team management, customer management, and contract management utilities. The package of software that supports these MSP management activities is referred to as “PSA,” which stands for “professional services automation.”
An example of an MSP software platform is the Atera system. This is a cloud-based service that includes both PSA and RMM packages. So, all of the IT asset management tasks of the MSP can be carried out through the Atera portal. As an online service, Atera is accessed through a standard web browser, which means that the MSP does not need to install any software on its own site or maintain any of its own hardware to support that software. You can evaluate Atera by registering for a free trial on their website.
Tooling for IT asset management
The key requirement of successful IT asset management is having the right tools for the job. We get into more detail on the best tools for ITAM in a related post. Many aspects of IT asset management are open to interpretation. Variables such as equipment lifetime and service level standards are all matters of policy. The decisions on policy are your key policy tool; the software, just supports your strategy.
Related: Best ITAM Tools




