Locky ransomware was first discovered in January 2016. It has since grown to be a family of ransomware systems
While the original Locky ransomware is no longer active, variants are still out there. There is also no guarantee that the original Locky won’t come back. So, there is every reason to research this malware and its variants and install protection measures to prevent it from getting on your system.
Here is our list of the best Locky ransomware prevention tools:
- ManageEngine DataSecurity Plus (FREE TRIAL) Focuses on data protection with robust file integrity monitoring, user activity tracking, and compliance reporting. Start a 30-day free trial.
- CrowdStrike Falcon Insight Provides comprehensive endpoint detection and response with advanced threat hunting and cloud-based coordination.
The Locky ransomware family attacks Windows systems. Attack campaigns carried out with Locky ransomware are opportunistic and not targeted. The code for the virus is attached to spam emails that are mailed out to lists of hundreds of thousands of email addresses at a time.
The strategy is a numbers game. A percent of the recipients will be interested in the generic text of the email, and a percentage of those people will open the attachment. A subgroup of that number will activate the macros that load the Locky ransomware.
Targets of Locky ransomware
Although Locky’s entry strategy is through mass mailouts, it is possible to tailor that target field by acquiring lists of emails in specific industries. The Healthcare sector has been a massive target for Locky. The Telecom and Transportation sectors are the next biggest targets.
Targeting businesses are more profitable than attacks on private individuals. Large organizations have more money to spare than individuals, and they also have more to lose. While many ransomware charges around $500 for remediation, Locky’s ransom was usually between $4,500 to $10,000, paid in Bitcoin. This is not the very high end of ransom demands; some ransomware demands sums in millions of dollars.
The Necurs botnet
Most email systems now apply spam filters automatically. These are blacklisting systems that spot high-volume mailings from one domain or email address. Spam filters divert identified emails to the Spam/Junk folder or outright block those emails from being downloaded into the client.
The makers of Locky got around this problem by creating a botnet. Both the hacker group and the botnet are called Necurs. A botnet is several private computers that have been infected with a virus. Each device in the botnet is called a “zombie.” The virus periodically opens a connection to a “command and control” server (C&C), which gives them instructions on what to do.
Necurs uses its botnet to send out emails. There are millions of computers in the botnet. Those computers can be big, corporate servers, and so Necurs has a large capacity. Spam filters blacklist source IP addresses and domain names that send out large numbers of emails. By spreading around the task of sending out the emails, Necurs avoids that filter. The source domains given in these emails are usually fake – they don’t need recipients to reply, just open the attachment.
How does Locky ransomware operate?
The same spam email, which is about an unpaid invoice, is sent out to hundreds of thousands of recipients. The email has a Word document as an attachment, and the message of the mail encourages the recipient to open it. The contents of the document are unintelligible – just a jumble of characters. A popup explains that the document has been encrypted and that pressing a button in the popup will decode it.
The button in the document popup activates the macros in the file. These act as a downloader that opens a connection to the C&C server and downloads an installer. With this, the Necurs group has an agent on that computer. The device can be used as part of the botnet or infected with Locky ransomware.
The Locky code isn’t copied over as a file. Instead, it is loaded directly into memory. The installer checks periodically for the running process, and if it can’t find it, it downloads the program and reruns it. This means that the Locky program doesn’t need to be resident on the computer to operate. This defeats one of the standard detection methods of antimalware. However, the installer itself needs to be stored on the computer so that an indicator can be identified. The installer also downloads some .txt and .bmp files for use in the ransom demand.
Locky doesn’t spread. It just starts encrypting files straight away on the computer that it is installed on. The encryption process changes each file name to have an ID made up of 16 characters and contains both numbers and letters. The encrypted file has a different extension. The first version of Locky used the .locky extension. Later version and variants used the following extensions for encrypted files:
- .zepto
- .odin
- .shit
- .thor
- .aesir
- .zzzzz
- .osiris
The last version of the ransomware emerged in December 2016, using the .osiris extension.
The Locky ransom demand
Locky encrypts files with two ciphers. These are AES encryption with a 128-bit key and RSA encryption with a 2048-bit key. The keys are generated on the Necurs server and sent to the Locky malware. They are also stored with a reference code.
The encryption only affects data files – files containing to identify an indicator text, images, video, or audio. It doesn’t encrypt executable files. This is important because it means you can still use the computer. The hackers want you to pay from that computer, so they don’t want to disable it. The ransomware changes the background of the infected computer’s Desktop to show the ransom demand. This note is also available in a text file copied to the computer.
The instructions tell the victim to install the Tor browser and use it to access the Necurs site. The note also includes a unique ID, referencing the hit and extracting the correct decryption key once the ransom has been paid. The victim has to type the attack ID and the Bitcoin code into a form on the Necurs site. A decryptor with the decryption key embedded in it is then sent by email.
Some ransomware, either through shoddy programming or intentionally, won’t deliver a method of restoring files. Fortunately, Locky does. Those who pay the ransom can regain access to all of their files.
Variants of Locky ransomware
There have been several updates to Locky that changed how the ransomware operated and can be identified by the different extensions used for encrypted files. Apart from programmatic changes made by the Necurs group, there have been two variants in circulation that Necurs didn’t necessarily produce.
PowerLocky
PowerLocky is a blend of two ransomware systems: Locky and PowerWare. This encryption-based extortion software is distributed as a .NET executable was written in PowerShell. It demands a ransom of 0.75 Bitcoin, which, at the time that the system was active in July 2016, was worth $500. Today that Bitcoin value converts to $29.600.
Like the original Locky, PowerLocky changes the names of all encrypted files and puts the .locky extension on them. The PowerLocky ransom note is an exact copy of that used by Locky.
Lukitus
Lukitus emerged in August 2017. The Necurs botnet also distributed this strain of Locky as an attachment to a mass email mailout. “Lukitus” is Finnish for “locking.” In the Lukitus campaign, the attachment was a .zip or .rar archive file, and the infecting code was written in JavaScipt or VBScript.
Infected files get the .lukitus extension. After completing its encryption task, the primary executable is removed.
How to protect against Locky ransomware
A heartening piece of news is that thanks to the efforts of Microsoft’s legal team, Locky is no longer a significant threat. Microsoft traced the C&C servers and threatened their hosts with legal action, causing them to remove those accounts in March 2020. Thus, even though the Necurs botnet malware is still resident on millions of computers, the IP addresses hard-coded into them for instructions polling no longer exist. By the time Microsoft plunged in the knife, Necurs had controlled more than 9 million zombie computers.
Despite this good news, you can’t be complacent about Necurs and Locky – they could quite easily return.
The best defense against Locky is to educate users against opening attachments in emails from people that they have never heard of. It is also essential to keep all of your software entirely up to date to shut down exploits and protect your system from all types of malware. You should also implement a backup strategy that copes and stores files from each endpoint separately to avoid cross-infection.
You can buy and install some excellent tools to block Locky and all other brands of ransomware. Here are two that we recommend.
Our methodology for selecting Locky ransomware prevention tools
We’ve broken down our analysis for you based on these key criteria:
- Endpoint Protection: Tools must offer robust protection for endpoints, including real-time detection and response.
- Data Integrity and Monitoring: Effective monitoring and protection of critical data against unauthorized changes or tampering.
- Threat Intelligence: Utilizes advanced threat intelligence to identify and mitigate ransomware threats.
- Automated Remediation: Ability to perform automated actions to isolate infected devices and prevent the spread of ransomware.
- Compliance and Reporting: Provides comprehensive reporting for compliance with standards such as HIPAA, PCI DSS, and GDPR.
1. ManageEngine DataSecurity Plus (FREE TRIAL)
ManageEngine DataSecurity Plus is a protection system for sensitive data. This is particularly useful for those businesses involved in the healthcare sector, which was a prime target of Locky. Companies following HIPAA need to ensure that all patient data is accessible for appropriate use, and does not get disclosed. The same rules apply to PCI DSS and GDPR. Action logging features in the package are suitable for standards compliance auditing.
Key Features:
- File Integrity Monitoring (FIM): Alerts when unauthorized changes occur in monitored files.
- User Activity Tracking: Monitors and logs user actions for compliance and security.
- Permissions Analysis: Analyzes file and folder permissions to ensure proper access control.
- Automated Responses: Implements automatic actions like shutting down endpoints or restoring files from backups.
Why do we recommend it?
As its name suggests, ManageEngine Data Security Plus is focused on data protection. The premise of this strategy is that data is the most important asset in your business, and any damage or loss is going to ruin your company. The system assumes that you have an AV to spot viruses.
DataSecurity Plus first scours the system and records all of the locations of data stores. It documents these and then scans each store, categorizing the data there. This enables the service to focus protection on sensitive data. The monitor then watches the files that contain that data and prevents them from being tampered with. The system also monitors emails and USB devices to prevent viruses from getting in, and data from getting out.
The file protection system is called a File Integrity Monitor (FIM). This raises an alert when an unauthorized change occurs in a monitored file. So, the first encryption attempt by Locky would trigger a notification.
The system can be set up to implement remediation actions automatically. Examples of those workflows are shutting down an infected endpoint, restoring files from backup, killing processes, and suspending user accounts.
This software installs on Windows Server and protects computers running the Windows operating system – the targets for Locky.
Who is it recommended for?
This system can protect against account takeover and insider threats as well as intrusion. It can also spot the actions of malware, although it doesn’t spend any time detecting the arrival of malicious code. Effectively, this is a last line of defense for data.
Pros:
- Detailed File Access Logs: Provides comprehensive records of file access to understand the context of changes.
- Trend Analysis: Tracks access trends over time for improved detection of malicious behavior.
- Compliance Reporting: Includes built-in reporting for HIPAA, PCI DSS, and GDPR compliance.
- Extensive Integrations: Can integrate with various helpdesk solutions, notification platforms, and backup systems.
Cons:
- Time-Consuming Setup: Requires significant time investment to fully explore and utilize all features and tools.
ManageEngine DataSecurity Plus is available for a 30-day free trial.
2. CrowdStrike Falcon Insight
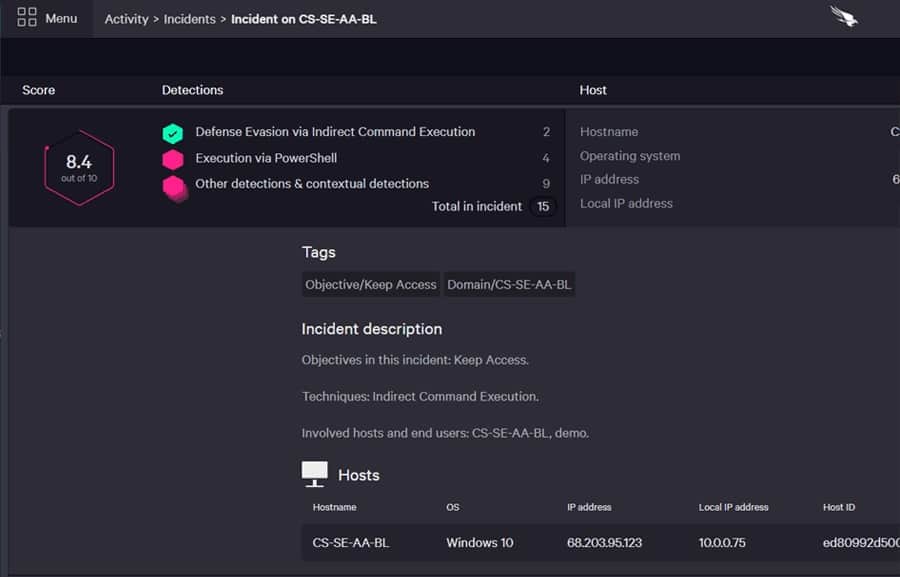
CrowdStrike Falcon Insight is a package of cybersecurity tools that includes both on-site and cloud elements. The on-site part of this system is an agent program that is installed on each endpoint. This is a complete endpoint detection and response service, and CrowdStrike also markets it as a standalone package called Falcon Prevent.
Key Features:
- Dual-System Design: Combines on-device antivirus with a cloud-based SIEM for comprehensive protection.
- Local Antivirus: Offers robust on-device security even when offline.
- Cloud-Based Coordination: Centralized threat intelligence and response instructions from the cloud.
- Advanced Threat Hunting: Uses dual-layer threat detection to identify anomalous actions rather than specific files.
- Automated Responses: Automatically isolates infected devices, suspends user accounts, and blocks malicious IPs/domains.
Why do we recommend it?
CrowdStrike Falcon Insight is a combination of an on-device antivirus package and a cloud-based SIEM. The AV is called Falcon Prevent and it is available as a standalone product. Each AV uploads activity data to the cloud server for threat hunting. That central unit sends back response instructions.
Falcon Prevent is sufficiently comprehensive that it can continue to protect a device even when isolated from the network and can’t contact the Insight controller in the cloud. The communication between Prevent and Insight uploads activity reports and downloads instructions. The Insight system analyzes activity reports according to the latest threat intelligence. The design looks for anomalous actions rather than specific files. This is the perfect detection method for Locky, which doesn’t drop an executable file on the targeted device. The endpoint agent also carries out that detection method, so Locky doesn’t get a look in.
Remediation actions include isolating the device from the network so infections can’t spread. The system can also command a shutdown of the device, wiping and a restore from backup. While Locky doesn’t rely on user accounts, other ransomware does. Falcon Insight can suspend suspicious user accounts and block access to blacklisted IP addresses and domains.
Falcon Insight is backed by CrowdStrike research labs and event records from other CrowdStrike customers. The coordinating system of Insight can pass threat intelligence to all devices on the network so that as soon as one endpoint is hit, all the others are on the alert.
Who is it recommended for?
The big advantage of this package is that its endpoint agent is able to keep detecting and protecting even if its host is disconnected from the network by a ransomware attack. Isolation can also be a protection strategy to prevent malware from spreading to other endpoints.
Pros:
- Hybrid Environment Support: Excels in mixed environments, including Windows, Linux, Cloud, and BYOD.
- User-Friendly Console: Intuitive cloud-based admin console for easy management and deployment.
- Behavioral Tracking: Tracks and alerts on anomalous behavior, improving over time with continuous monitoring.
- Lightweight Agents: Minimal system resource usage ensures smooth performance on endpoints.
Cons:
- Limited Trial Period: A longer trial period would be beneficial for thorough evaluation.





