LookingGlass ScoutPrime is a comprehensive threat intelligence solution designed to help organizations detect, analyze, and mitigate cybersecurity risks. As cybersecurity threats continue to evolve and grow in sophistication, businesses require advanced tools to proactively monitor and safeguard their networks. ScoutPrime provides critical insights into emerging threats, enabling organizations to stay ahead of cybercriminals by identifying potential risks before they can cause harm.
Developed by LookingGlass Cyber Solutions, a recognized leader in cybersecurity, ScoutPrime integrates seamlessly into an organization’s existing infrastructure, providing continuous monitoring of external threat landscapes. This powerful platform offers real-time visibility into threats originating from both the public and the dark web, delivering actionable intelligence that can be used to bolster defensive strategies and respond to incidents promptly.
ScoutPrime’s well-designed interface allows cybersecurity teams to quickly assess and prioritize threats, providing detailed information on attack methods, targeted industries, and potential vulnerabilities. By leveraging this intelligence, businesses can make more informed decisions on how to secure their networks, adjust defenses, and ensure compliance with industry standards.
LookingGlass ScoutPrime stands out as a valuable resource for organizations seeking to enhance their cybersecurity posture. It is particularly beneficial for enterprises with complex networks or those operating in high-risk sectors such as finance, healthcare, and government.
In this review, we will explore the features, benefits, and capabilities of LookingGlass ScoutPrime, examining its effectiveness in detecting and mitigating cyber threats and providing insights into how it compares to other threat intelligence solutions available on the market.
About ScoutPrime
LookingGlass Cyber Solutions, Inc. was started up in 2009. None of the company’s founders are still with the business. The company is based in Reston, Virginia, and is funded by venture capital – it is still private. LookingGlass has two products, which are called ScoutPrime and ScoutThreat.
ScoutPrime specializes in collecting information from 88 intelligence sources and identifying the threats to their clients. These could be threats to the technology in use by a subscribing business, or it could be a specific attack that derives from disclosed credentials such as access accounts or email addresses.
How would you use ScoutPrime?
You register your corporate identities, such as your business name, locations, and domains. For complete risk analysis, it would probably also be necessary to register the identities of related operations, such as suppliers, major corporate customers, or service providers. For example, a challenge to one of your service providers could put your own business’s data privacy at risk if that service is responsible for processing or storing the data your business handles.
A security breach at one of the businesses you deal with could directly create a vulnerability with your own company. In such cases, you need to know about the exposure as quickly as possible and deal with the threat. For example, suppose it is discovered that a hacker team has stolen a list of your customer addresses from a cloud storage system. In that case, you need to know about that and report it to avoid losing standard privacy accreditation.
The businesses you rely on might not know that they have been attacked or might not be prepared to disclose that event. However, if an associated company tries to cover up a data leak related to your account, that disclosure will also be your responsibility.
ScoutPrime can detect security breaches even if the victimized company isn’t prepared to publicize them. That stolen data will end up being offered for sale on the Dark Web. However, to achieve a reasonable price, the sellers will release some information about the businesses that the data leak relates to. This is how ScoutPrime can find out about a data loss event before you do or even discover security weaknesses at other companies that have been covered up.
Who would use ScoutPrime?
Typically, you would expect your on-site analysts to look through the reports produced by ScoutPrime to identify security problems. However, if you don’t have a cybersecurity team on the payroll, you would probably need to find a managed cyber security service. In that case, you would subscribe to the ScoutPrime service for those service provider analysts to work on.
Not every business will have the budget or the complexity to warrant the expense of a ScoutPrime account. Small businesses would be less likely to take an interest in this service, and if your business doesn’t deal with private individuals, there is even less incentive to use this service. On the other hand, middle-sized to large corporations that regularly deal with public members, particularly those that process card payments or operate in the health sector, will be very likely to need a threat intelligence service such as the system provided by LookingGlass ScoutPrime.
ScoutPrime features
The ScoutPrime package offers a group of contributing elements that helps your business understand precisely what internet-facing assets you have. That also allows ScoutPrime to target its threat hunting. These are:
- Dynamic Internet Footprinting
- Risk Scoring and Prioritization
- Investigation Tools and Threat Hunting Support
- Threat Intelligence Management
- Real-Time Alerting
- Relationship Monitoring
- STIX and TAXII 2.0 Support
- Summary and Detail Reports
The modules of ScoutPrime all interact with each other – there are no silos in this system. The tool can also be integrated with different packages to automate threat protection.
Dynamic Internet Footprinting
Internet footprinting involves defining the identities of a company that needs to be protected. This will undoubtedly include the company’s name, its brands, and the names of its products or patented commercial assets.
The footprinting system is the basis for searches through threat intelligence monitors that scour through collected information drawn from many sources that list the current chatter and plots of the worldwide hacker community as communicated on the Dark Web or through any other channel.
Risk Scoring & Prioritization
ScoutPrime includes a risk assessment scoring methodology that is called the Threat Indicator Confidence (TIC) score. This assessment enables cyber security technicians and analysts to hone in on the most at-risk assets.
Naturally, these factors create constantly in flux rankings, so they need to be continuously watched. There are several other features in the ScoutPrime package that make risk management easier to achieve efficiently and cost-effectively.
Investigation Tools and Threat Hunting Support
The ScoutPrime dashboard includes investigative tools that enable your cybersecurity technicians to investigate further the sources of suspicious activities that are spotted once greater attention is paid to an asset that the threat intelligence feed has flagged as potentially vulnerable.
ScoutPrime aims to support onsite analysts, not replace them.
Threat Intelligence Management
This module is the core service of ScoutPrime; as the system’s name suggests, the package scouts for information that pertains to a subscribing company. It collects information on hacker activity from 88 different sources. That data is then converted into a standard format and stored in a searchable collection.
The threat intelligence system links together associated events and looks along paths to see where client assets are about to be targeted. This could simply be a signal about a sector that is currently being targeted, such as the health industry is the focus of a ransomware campaign or a particular type of attack on the rise, such as video hijacking or some other media type that is known to form a part of a client’s presentation.
As well as reporting on specific and general threats in the console for an account, the ScoutPrime will run through its TIC scores for all assets.
Focused Real-Time Alerting
No one is expected to sit and watch the ScoutPrime dashboard waiting for a new threat post to appear. Instead, you can set up a notification path to send out an email when further information arrives. In addition, it is possible to place branching rules on the notification requirements so that different technicians will receive a notification under other circumstances.
Relationship Monitoring
Assets listed individually would scatter the view of all of the commonalities between them. Specific systems work together, such as your Web server, load balancer, and ISP link. So, it makes sense to group those services as a potential target. Other examples of relationships would relate to associated businesses. For example, your billing system is linked to your clients, and your accounts payable is linked to suppliers.
By creating relationships, you simplify threat management.
STIX and TAXII 2.0 Support
STIX and TAXII are two platforms for sharing threat intelligence. This is important if your system has already been compromised. Getting that information out to others enables all at-risk associates to take action quickly.
Unlimited Reports
All of the information sent to a client account is a view on a central database, and that intelligence is available on an ongoing basis. Users can access that information at any time for their analysis and to create reports to share threat information with corporate stakeholders.
ScoutPrime deployment options
All of ScoutPrime’s services are delivered from its cloud platform, and there is no need to install any software on your site.
Through the use of APIs, plug-ins, and integrations, it is possible to get a digital feed sent straight through to your security systems. This lets your IT services harden their defenses proactively, search for evidence of an attack, and take remedial action.
ScoutPrime prices
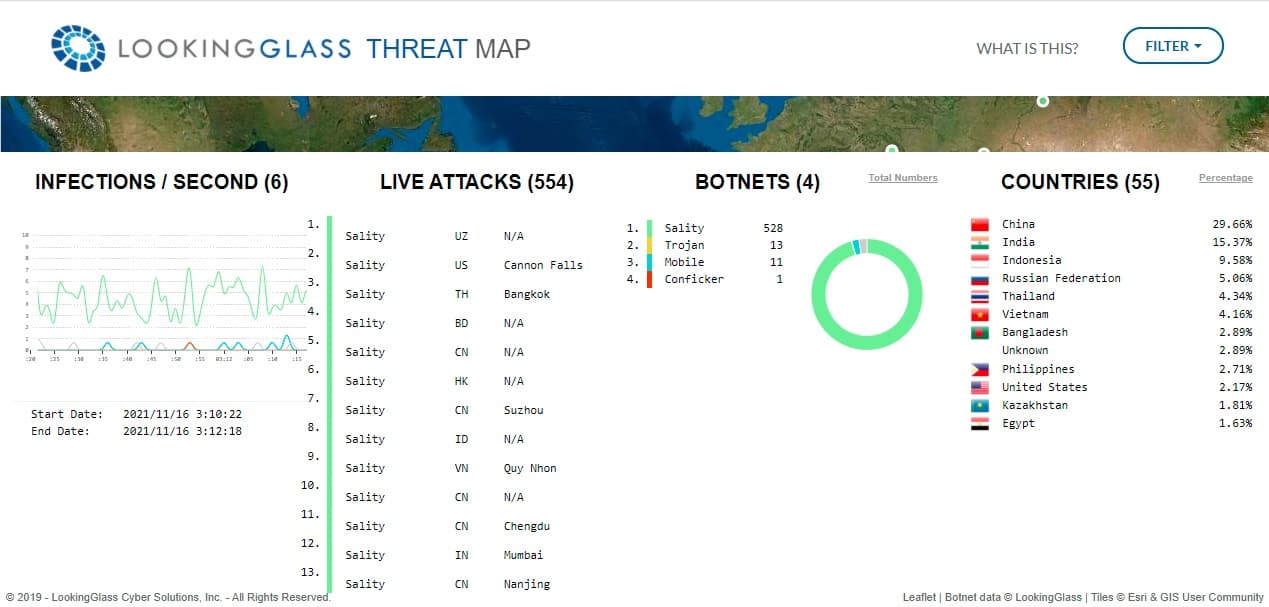
LookingGlass Cyber Solutions doesn’t publish a price list for its ScoutPrime system. Your buyer’s journey begins by requesting a demo. Take a look at the Live Threat Map that Looking Glass operates to get an idea of all of the hacker activity that is going on around the world 24/7.
ScoutPrime strengths and weaknesses
Scout Prime is a very specialized service, and it isn’t in the mainstream of cybersecurity products that most businesses would know to look for. However, it is the kind of service that a business’s experts would suggest subscribing to. Therefore, companies that don’t have any system security technicians or have never had a security audit would never know about the sector in which ScoutPrime operates.
We have identified the key points to note about ScoutPrime.
Pros:
- A consolidator that gathers 88 different sources of intel
- A guide through all of the information available out there to get pertinent warnings
- Alerts so technicians know when new data arrives
- A dashboard that includes analytical tools
- A reporting system
Cons:
- No associated system security software
- A managed service option would be helpful
Alternatives to LookingGlass ScoutPrime
ScoutPrime is an excellent service, and it offers inputs from many threat intelligence agencies. However, it is not the only provider in the market, and we have found some competitors that you should also consider.
Here is our list of the best alternatives to LookingGlass ScoutPrime:
- ManageEngine Vulnerability Manager Plus (FREE TRIAL) This software package for Windows Server is centered on a vulnerability scanner and a patch manager. The scanner runs across your hardware fleet every 90 minutes and looks for unauthorized and end-of-life software. It runs through devices running Windows, macOS, and Linux and notes the patch status of each OS and software package. This service feeds through to the automated patch manager that will update software. The tool also identifies misconfigurations that provide potential entry points for intruders and malware. There is a free version of this package that covers 25 computers. ManageEngine offers the paid versions of Vulnerability Manager Plus for a 30-day free trial.
- UnderDefense This service offers a flexible Security Operations Center solution that you can run yourself with advice from UnderDefense experts or pass over to the UnderDefense team entirely. Let UnderDefense set up all of your automated security systems or just let them do everything as an ongoing service. They will use a threat intelligence feed to protect your company without you needing to get involved. You can get your first month free when you sign up for the UnderDefense SOC service.
- CrowdStrike Falcon Intelligence The Falcon Intelligence system is a complete security package that includes on-premises and cloud-based elements. The security system is offered in packages, and there are several levels of threat intelligence included in each. The three strata of threat intelligence available from CrowdStrike are Intelligence Reports, which are human-readable, Tailored Intelligence, which is a close competitor to the ScoutPrime service, Snort/Yara Rules that automatically program your on-site defense systems for the latest threats; and an Assigned Intel Analyst to guide your team through threat intelligence information. You can register for a free trial.
- Rapid7 Threat Command this threat intelligence service offers live alerts and also direct implementation to block new threats. The service is part of a cloud platform of security protection options. This intel can feed into a vulnerability scanner called InsightVM or a SIEM service called InsightIDM. Check out the service by accessing a free threat report.
- Exabeam Threat Intelligence This service was built on SkyFormation, a well-respected threat intelligence service that Exabeam has now rebranded. The service gets a daily update into the cloud-based threat database, sorted, searched, and packaged, producing specific intel for clients. That threat intelligence feeds directly into the Exabeam Next-Gen SIEM service. Get a demo of the Exabeam system.
- Mandiant Threat Intelligence This threat Intelligence Feed is offered by one of the world’s leading cyber security research consultancies. Get it in report format and as a feed straight into your SIEM or XDR. Sign up for Threat Intelligence Free to gauge the system. In addition, you can get a full Managed Defense service from Mandiant that will include the intelligence feed and technicians to protect your system.