Maze ransomware first appeared in 2019 and quickly gained attention for its aggressive targeting of high-profile organisations and its unusually sophisticated extortion methods.
It was operated by a cybercriminal group often referred to as the Maze operators, who are believed to have links to Russian-speaking threat actors, although their exact identities remain unconfirmed.
The group behind Maze became particularly known for introducing and popularising “double extortion” tactics. In addition to encrypting victim data, they also stole sensitive files before encryption and threatened to publish them publicly if the ransom was not paid. This approach significantly increased pressure on victims, as it introduced the risk of reputational damage alongside operational disruption.
Maze ransomware was active until around 2020, when the group reportedly ceased operations following internal agreements within the cybercriminal ecosystem. However, its methods did not disappear; instead, they were widely adopted by other ransomware groups and became a standard tactic in later campaigns. The impact of Maze was especially significant in sectors such as healthcare, manufacturing, and finance, where downtime and data exposure could have serious consequences.
Beyond financial gain, Maze operations were also notable for their publicity-driven approach, often targeting large organisations to maximise visibility and pressure for payment. Its combination of data encryption, data theft, and psychological coercion made it one of the most influential ransomware strains of its time.
Here is our list of the best Maze ransomware protection tools:
- ManageEngine Endpoint Central EDITOR’S CHOICE This Remote management package includes an anti-malware service with a ransomware spotter and blocker. Access the Anti-Ransomware add-on to defeat Maze and other ransomware strains. Available as a SaaS platform or a software download for Windows Server. Get a 30-day free trial.
- CrowdStrike Falcon Insight This XDR collects data from all around the network while also running a full anti-malware unit on each endpoint. Creates a corporate threat intelligence network that warns of lateral movements.
How does Maze ransomware get onto a network?
Hackers using Maze require a valid user account, and so the first phase of a Maze attack is spear phishing. In this technique, hackers research individuals working in an organization and then open up a conversation based on some interest that they have discovered that person pursues.
The initial mark might be a low-level employee. In this case, the hacker gets the impact to explain who is in charge of that department and possibly who works in the IT department. The hacker group eventually builds up an organizational chart through these social contacts and works out who has privileged access to the system. That person then becomes the primary target. It is the system-level accounts that the hackers want.
While some hacker team members are trying to trick employees, other members will be trying traditional ways into the system with frequently used passwords, manufacturer default passwords, or a password cracker to get key access points into the network. The group will also try to get a remote access Trojan onto a device with an infected .docx file as an email attachment. One way or another, the group can acquire a user account.
How does Maze infect a system?
Once Maze is onto a device, it will enter a research phase, using well-known system probing tools, such as smbtools.exe, Adfind, BloodHound, PingCastle, plus system monitoring discovery tools. It will scan for network vulnerabilities. The virus will look for open SMB access, network device configuration settings, and the opportunity to get into Active Directory instances.
Operating system tools that the Maze ransomware deploys include Link-Local Multicast Name Resolution (LLMNR) broadcasts and the NetBIOS Name Service (NBT-NS) to try to identify other computers and devices. It will also capture NT LAN Manager (NTLM) packets, which contain login credentials. It will also deploy Mimikatz on each infected endpoint to try to discover user credentials. On getting hold of a user account name, the Maze package will use various techniques to acquire the password.
The ransomware will spend several days exploring the system, mapping the network, and assembling as much as possible of the access rights structure. The virus acts in a very similar way to regular system monitoring and management tools. It attempts to get access to other endpoints on the network. If the system is a managed service provider, the virus will try to connect through to client systems and begin its research phase.
While examining each newly accessed endpoint, the virus scans for plain text files that might contain user account information. It will also try brute force password cracking to try to get into user and system accounts on the device. The system has time, and it will keep exploring, scouring different devices, and other scanning techniques to find user accounts.
Once Maze finds user credentials, it can move around the network more quickly, using SMB and RPC services to send files and software onto other devices and possibly the central servers of the system. The virus will also create its user accounts to get into the access rights management (ARM) service for the targeted network.
The main difficulty of combating Maze lies in its ability to move over to new devices. Once it is on another device, that extra module will infect all other devices on the network. So, if the ransomware program is discovered on one device and removed, that device can quickly be reinfected from another infected device.
How does a Maze ransomware attack occur?
Maze spreads very quickly around a network. Its ultimate aim is to encrypt all data files to demand a ransom. Part of the reason that the system delays triggering that encryption is that the hackers behind the software also want to steal that data. So, as it gets into a new endpoint, it scans for files, opens a connection to the internet, and then transfers those files out. The team later threatens to release the contents of those files to the public or the hacker community to motivate victims to pay the ransom.
Once all of the data has been stolen, the Maze encryption begins. Encryption is carried out with two ciphers, which are ChaCha20 and RSA. ChaCha20 is a variation on the Salsa20 cipher. RSA is an asymmetric encryption system that is widely used as part of the SSL security system. The Maze implementation of RSA uses a 2048-bit key. ChaCha20 uses a 256-bit key.
As each file is encrypted, Maze adds an extra extension onto the end of its name. This is random series of four to seven characters. When all files on the device have been encrypted, Maze changes the wallpaper of the computer’s Desktop to show the ransom demand.
The user is directed to a text file that the ransomware has copied onto the device. This is called DECRYPT-FILES.txt. It explains how to use a decryptor, which is also copied onto the device. This utility has a decryption meter and allows three files to be decrypted for free. Paying the ransom buys credits for the decryptor. The screen does not name a price.
While the ransom demand is showing on the screen of the targeted computer, Maze also plays an audio file, which is a looping voice message that acts as an alarm.
The DECRYPT-FIES.txt file explains that the victim has three days to contact the hackers, or they will publish a notification of the attack on their site. This would be damaging because it might cause partner businesses that perform a third-party risk analysis to withdraw from dealing with the victim company. If the victim doesn’t contact the group within seven days, the Maze group will release all of the stolen data.
The threat of data release is potent because this blocks off recovery strategies that businesses might have to avoid paying, such as wiping and restoring from backup. The group is very confident of their power and even offer live chat support if the system administrator is having difficulty using the descriptor.
The victim has to open the Maze website in a Tor browser to receive instructions on payment and then get the decryption key. The group also promises to delete all of the stolen data they hold once the payment has been made.
The Maze ransomware doesn’t have a fixed ransom – remember that the group works in partnership with other cybercrime syndicates and splits the payment, and each partner will have different income expectations. However, it is known that Maze ransoms are very high. Reported demands range from $6 million to $15 million.
Where is Maze from?
The hackers behind Maze are not one of the major groups; in fact, they do not have a separate name – they are known as Maze, the same as the ransomware. A routine within the encryption system checks on the local language of the machine, and it will not launch the encryption attack if that language is one of those of the former Soviet Union or Serbian.
The block on interference with computers used by Russians or the populations of states allied to Russia makes it more than likely that the Maze hacker group is based in Russia. The code of the Maze program suite is well ordered and adequately commented. This indicates that the creators of the system are professional programmers. The code is bug-free and works well.
The system includes several obfuscation techniques, and it is composed of several modules that support each other and exchange data. This indicates that the ransomware was developed by experienced system designers and run by project managers. Its development included comprehensive testing. So, Maze is not the product of amateurs, and it is the product of a well-managed group effort.
How to deal with Maze ransomware
One good piece of news about Maze is that on 1 November 2020, the group announced that it was ceasing attacks. However, there is no reason to believe them. The lack of reported attacks is also no indication that no attacks have occurred. If there has been a ceasefire, then no one can be confident that it will be permanent.
The threat of data disclosure means that it is challenging to ignore a Maze ransom demand. If your business is tied to a data privacy standard, such a HIPAA, PCI DSS, or GDPR, the fines and compensation that you would have to pay for that disclosure could end up costing more than the ransom. The Maze group has been very smart in their approach.
The only surefire way to survive a Maze attack is to prevent it from occurring in the first place. Fortunately, some excellent malware defense systems block Maze ransomware. The Maze group may come back with a modified version that avoids the detection systems set up to spot the original Maze. However, there are antimalware options available that are future-proof because they look for anomalous activity rather than specific file names. This is particularly useful for Maze, which acts more like an insider threat than a virus attack.
Consider the following security systems to defend against Maze ransomware.
Our methodology for selecting Maze ransomware protection tools
We reviewed the market for anti-ransomware systems that will block attacks by Maze and similar malware and we analyzed the options based on the following criteria:
- Anti-malware system that can detect all types of automated attacks
- Coordination with access rights management systems
- Protection for sensitive data and user account information on Windows
- File integrity monitoring to spot file encryption
- A system that blocks data exfiltration
- A free trial or a demo option to enable an assessment of the package before buying
- Value for money from a threat detection system that can block lateral movement and data theft at a reasonable price
The entry method for Maze is through phishing and it is hoped that businesses will already have anti-phishing systems in place. We looked for anti-malware services that will spot and block the later stages of a Maze ransomware attack.
1. ManageEngine Endpoint Central (FREE TRIAL)
ManageEngine Endpoint Central is a package of remote monitoring and management tools that is designed for use by IT departments. The bundle includes the Security Edition, which adds data loss prevention to the unified endpoint management bundle, which is called the UEM Edition. ManageEngine has created a new Anti-Ransomware unit, which will be an add-on to the Security Edition.
Key Features:
- Backup: Uses the Microsoft VSS shadow copy system
- Ransomware Detection: Watches the activities of executables
- Trusted Application Flagging: Cuts down detection time by ignoring well-known software packages
- Operates on Windows: The target for ransomware
- Central Monitoring Console: Scans all endpoints
Why do we recommend it?
The Anti-Ransomware is an extra feature for the Security edition of ManageEngine Endpoint Central. It is currently free under the Early Access program and it is also available under the free trial, but the service will eventually require a license fee. The ManageEngine Endpoint Central Security Edition is available as a SaaS package or for installation on Windows Server.
The Anti-Ransomware unit features a file backup system. This provides the preparation to recover from a ransomware attack. The tool includes a detection system that scans all running processes and checks on file statuses to spot ransomware.
If you are tracking an endpoint with a lot of software, you can speed up the executable scans by flagging known software as trusted. For example, if you have a spreadsheet program installed on a computer, you don’t need to worry about checking on that program. However, if malware hijacks that software to run a macro that launches a malicious process, that new process will be scrutinized.
If a file appears to have been changed without a valid user account accessing it, the process involved is killed and the file is automatically updated by restoring the backup. If a valid user makes a change, the new version of the file goes into the backup.
Who is it recommended for?
The Endpoint Central system will run on Windows Server or you can get it as a cloud-based SaaS package. Each monitored endpoint needs an agent installed on it and these are available for Windows, macOS, Linux, Chrome OS, iOS, Android, and tvOS. You have to sign up for the Security Edition to use the Anti-Ransomware unit. The Anti-Ransomware will only scan PCs running Windows.
Pros:
- Scans All Processes for Malicious Activities: Focuses on lesser-known software
- Automatically Shuts Down Suspicious, Unknown Software: Prevents users from installing software
- Allows Valid Software to Run Without Interference: No point in wasting time looking at trusted systems
- Automatically Restores Damaged Files: Uses Microsoft VSS
- Creates a Backup Every Time a File is Changed: Uses native Windows mechanisms
Cons:
- Only Protects Windows PCs: However, this is the target of most ransomware
You need to get the Security Edition of Endpoint Central to access the Anti-Ransomware and ManageEngine offers this for a 30-day free trial both on the cloud and on premises.
EDITOR'S CHOICE
ManageEngine Endpoint Central Security Edition is our top pick for a Maze ransomware protection system because it includes the ManageEngine Anti-Ransomware unit as an add-on. This system includes a backup system for data files and it will automatically restore any file that is altered without authorization and ransomware encryption will trigger that action. Simultaneously, the package scans all running processes and kills those that are not recognized as authorized software. This strategy defeats Maze and all other ransomware and malware.
Download: Get a 30-day FREE trial
Official Site: https://www.manageengine.com
OS: Windows Server or SaaS
2. CrowdStrike Falcon Insight
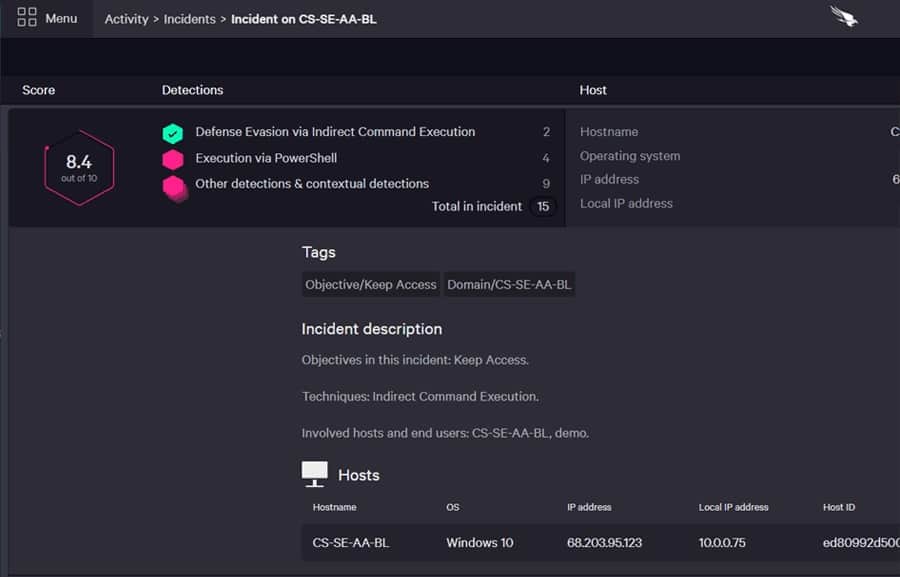
CrowdStrike Falcon Insight is a good choice for combating Maze ransomware. CrowdStrike has a research lab, and it knows all about Maze and how it operates, so blocking routines against the ransomware are built into this package.
Key Features:
- Hybrid Solution: On-device anti-malware and cloud-based threat hunting
- Antivirus Protection: Operates continuously on each endpoint
- Centralized Data Consolidation: Takes activity feeds from endpoint agents
- Cloud-Based Threat Hunting: Spots lateral movements
Why do we recommend it?
CrowdStrike Falcon Insight combines an antivirus package with a cloud-based XDR/SIEM. The on-device AV provides constant vigilance and will continue to work even if the connection to the cloud-based SIEM is lost. Such a disconnection is implemented by some ransomware and it can also be used as a defense mechanism to quarantine the device.
The Insight system offers coordinated coverage of all endpoints. This is very useful for Maze’s problem when it reinstalls its software on an endpoint that has been cleaned from another infected endpoint.
Insight sits in the cloud and receives reports from endpoint-resident modules. The monitoring software installed on each endpoint is called Falcon Prevent, which is available as a standalone product. This is a next-generation antivirus system that looks for abnormal behavior. It uploads reports to the Insight coordinator. Insight can send instant instructions to all endpoints as soon as an infection of Maze is spotted in one location. Thus, the removal can coincide on all devices throughout the network.
Insight manages threat response as well as detection. Remediation steps can include suspending user account, isolating devices from the network, and file locking for Active Directory. Insight works well against insider threats and intrusion as well as viruses.
Who is it recommended for?
With an Insight subscription, a business can get all data gathered by each individual AV unit, which is called Prevent, centralized in the cloud for a second tier of threat hunting. Protection gets expanded just by installing Prevent on another endpoint. Small businesses would find the price of Falcon Prevent too high.
Pros:
- Excels in Hybrid Environments: A mix of endpoint operating systems on a site
- Intuitive Cloud-Host Admin Console: Assesses all endpoints
- Can Track and Alert Anomalous Behavior Over Time: Uses machine learning
- On-Device Agent Provides Continuous Protection: Will carry on working if the device is disconnected from the network
Cons:
- Would Benefit from a Longer Trial Period: Only lasts 15 days
You can get a 15-day free trial of Falcon Prevent.




