Vulnerability scanning is an important cyber security process that identifies weaknesses in systems that could be exploited by malicious actors. Two of the most popular tools for vulnerability scanning are Nessus and OpenVAS. Both offer comprehensive features for scanning networks, identifying vulnerabilities, and helping administrators manage their security posture, but they come with different characteristics and trade-offs.
This guide implements a comparison between Nessus and OpenVAS, providing a detailed analysis to help you determine which tool best meets your needs. As well as being among the most widely-used vulnerability scanners, they are also two of the oldest. In fact, Nessus and OpenVAS have a lot in common.
Nessus was started as an open-source project and is now a property of Tenable, Inc., which has constructed a commercial product, using the open-source system as its core. This package is known for its extensive vulnerability database, user-friendly interface, and robust reporting capabilities. It is widely used in enterprise environments and by security professionals who require a reliable and powerful scanning solution.
On the other hand, OpenVAS (Open Vulnerability Assessment System) is an open-source alternative that offers many similar features to Nessus. While it is free to use, OpenVAS is often chosen by organizations looking for a cost-effective solution without the need for a commercial license. OpenVAS has grown into a popular choice for businesses and security teams with the resources to manage and configure it on their own. The tool was bought by Greenbone AG, which provides its own paid version alongside the free core system.
We will examine the important differences between Nessus and OpenVAS, considering their features and costs.
What are Vulnerability Scanners?
What do Nessus and OpenVAS do? Vulnerability scanners are a tool that network administrators use to scan networks for vulnerabilities. A vulnerability scanner can highlight known vulnerabilities and misconfigurations that leave a network at risk of a cyberattack or a data breach. Many companies use vulnerability scanning to identify gaps in network defenses and then fix the entry points before an attacker can exploit them.
Scanning for vulnerabilities is essential for enterprises because it’s the only way to know for certain what weaknesses exist. Regularly testing for vulnerabilities enables you to consistently eliminate security gaps and make your network more secure.
Both Nessus and OpenVAS provide a simple solution for vulnerability scanning. However, it’s important to note that the effectiveness of vulnerability scanning solutions varies from provider to provider, as some solutions are better than others at detecting known and unknown threats.
Nessus Product Highlights
Nessus (originally called The Nessus Project) was created by Renaud Daraison in 1998 and was originally an open-source remote security scanner. Several years later in 2005, Tenable Network Security changed Nessus over to a closed-source license. Today, Nessus is a vulnerability scanning platform used by over 27,000 organizations that can detect over 47,000 vulnerabilities.
Key Information
- The lowest false positive rate in the industry with six-sigma accuracy
- Offers users over 130,000 plugins
- Releases plugins within 24 hours of discovering a new vulnerability
- Over 50,000 Common Vulnerabilities and Exposures (CVE)
Many enterprises use Nessus because it has the lowest false positive rate on the market, successfully detecting legitimate threats without creating unnecessary notifications for a human user to address.
Pros:
- Offers a free vulnerability assessment tool
- Simple, easy to learn interface
- Little configuration needed, 450+ templates that support a range of devices and network types
- Offers a vast amount of community support and user-generated plugins
Cons:
- Can be expensive for some enterprise budgets
OpenVAS Product Highlights
OpenVAS is an open-source vulnerability scanner that started as a spin-off of Nessus called GNessUs. It took until 2006 for GNessUs to transform into the OpenVAS tool enterprises recognize today. By 2017, Greenbone changed the OpenVAS framework to Greenbone Vulnerability Management, and change the OpenVAS Scanner into a module.
Key Information
- Open-source
- Uses the Greenbone Community Feed to run over 50,000 vulnerability tests
- Developed and Maintained by Greenbone Networks
- Supports over 26,000 CVE’s
The platform’s use of the Greenbone Community Feed makes it a compelling low-cost solution for enterprises, with the potential to run over 50,000 vulnerability tests, providing protection against a vast range of threats.
Pros:
- Open source transparent tool
- Has a large dedicated community
- Leverages the latest CVEs and frameworks into its product
- Completely free
Cons:
- Enterprises will likely need experienced staff to fully extract value from the platform
Feature Comparison
| Feature | Nessus | OpenVAS |
|---|---|---|
| Vulnerability scanning | Supports over 50,000 CVE’s | Supports over 26,000 CVE’s |
| Web interface | Yes | Yes |
| Reports | Reports in HTML, CSV, XML | Reports in HTML, PDF, CSV |
| Scan Templates | Over 450 scan configuration templates | N/A |
| Plugins | Yes / 130,000 different plugins | Yes |
Nessus vs OpenVAS Head-to-Head
User Interface
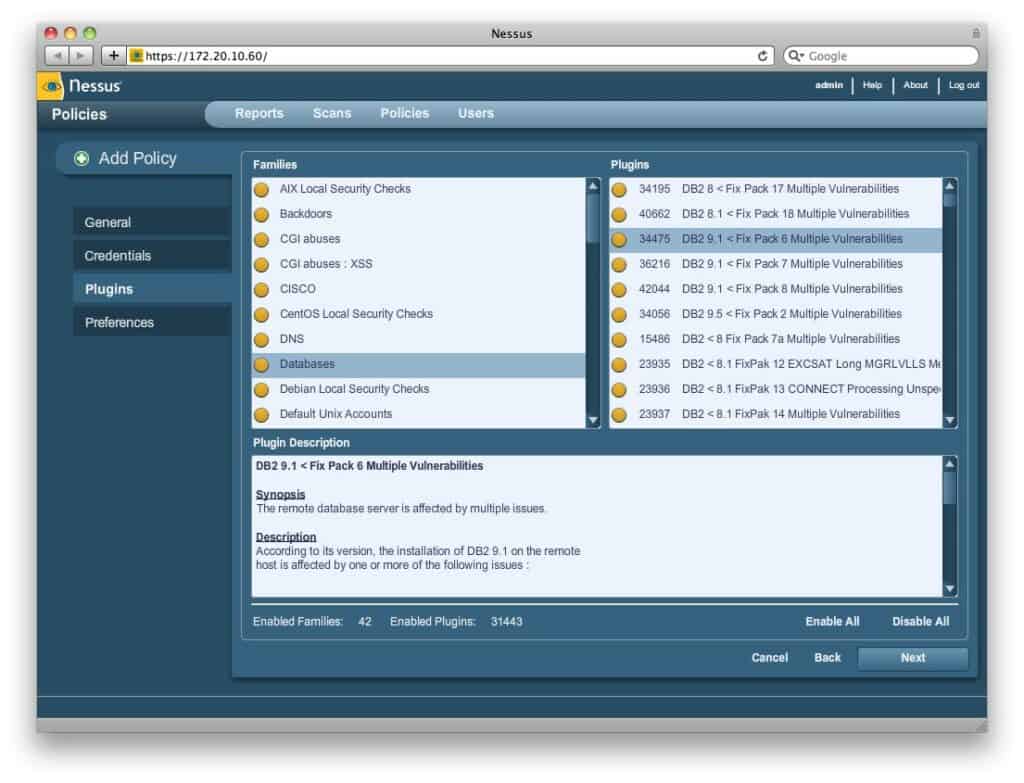
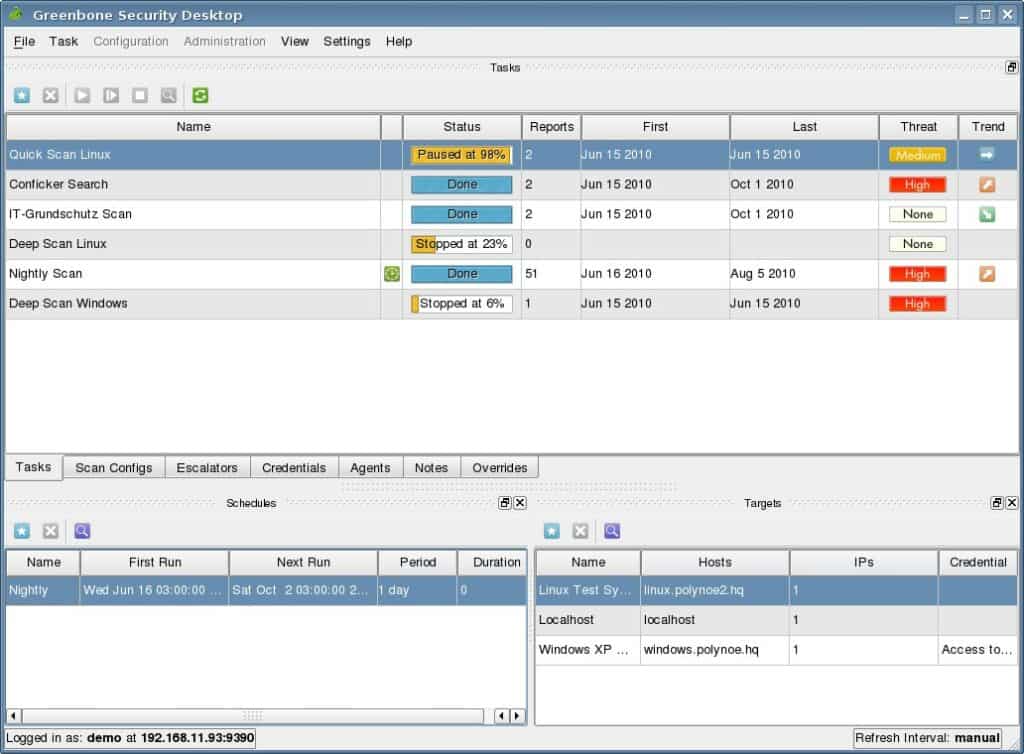
Both Nessus and OpenVAS come with web-based GUIs. While GUI preferences are usually a matter of personal preference there is a clear gap between the modern user interface offered by Nessus and the more dated look provided by OpenVAS. Functionally, they both provide a viable vulnerability scanning experience, but the production value of Nessus is head and shoulders above OpenVAS.
However, the OpenVAS GUI does provide dashboard views outfitted with clear charts that help you to make sense of network vulnerabilities according to severity. Both OpenVAS and Nessus have command line operations available for users that prefer to take a more classic approach.
Vulnerability Scanning Capabilities
The accuracy and depth of vulnerability scanning capabilities are two of the most important things to look out for when researching scanning tools. The best vulnerability scanners will minimize false positives and negatives, and detect legitimate weaknesses without creating flagging up irrelevant information.
When it comes to the metrics, Nessus covers a wider range of vulnerabilities than OpenVAS with support for over 50,000 CVEs compared to 26,000. Nessus is superior because it can detect more issues than OpenVAS.Nessus also has the advantage of delivering a lower false-positive rate. Six-sigma accuracy reduces the likelihood of missing vulnerabilities or incorrectly flagging anything up.
Unfortunately, false positives are something that OpenVAS has struggled with, as the user community has reported many issues when running scans. Based on the widespread CVE coverage and false positive rate, Nessus offers a more in-depth scanning experience.
Installation
When it comes to installation, Nessus is easier to install than OpenVAS. You can register for an activation code and then the company will send you a code you can use to register the program. The program itself can be downloaded directly from the company website on Windows, Linux, and Mac. Once you download it you can accept the license agreement and can continue the installation process through your web browser.
With OpenVAS, the process is a little more complicated. To install OpeNVAS you need to build it from source code. If you’re familiar with building software from source code this is no problem, but Nessus has the edge in terms of convenience.
Reports
Reporting is another area where Nessus delivers a solid experience. The user can create custom reports and export them in HTML, CSV, and XML formats. Nessus can automatically issue reports after a scan is finished, which helps to provide periodic updates.
OpenVAS also has its own reporting feature that allows you to create vulnerability assessment reports and combine multiple scans into one report with visual elements tables and pie charts. OpenVAS can export reports in HTML, PDF, and CSV. Nessus’ reporting feature may have the edge in terms of production value but OpenVAS’ reporting is still fundamentally strong.
Scan Templates
One of the areas where Nessus has a distinct advantage over OpenVAS is in templates. Nessus comes with over 450 configuration templates that assist the user to monitor their network.
Templates include Advanced Scan, Basic Network Scan, Host Discovery, Malware Scan, Offline Conflict Audit, WannaCry Ransomware, and more. The abundance of templates makes it easier for the user to configure their monitoring environment without setting up everything from scratch.
Plugins
While OpenVAS has some external tools users can incorporate, Nessus has over 130,000 different plugins. Plugins are written in Nexus Attack Scripting Language (NASL) and include information on vulnerabilities, remediation actions, and testing algorithms. The wide variety of Nessus plugins gives users more control over their monitoring experience than with OpenVAS.
OS Support
In terms of OS support, Nessus supports a wider variety of systems than OpenVAS. Nessus supports LinuxFreeBSD, Unix, Windows, and macOS. In comparison. OpenVAS runs on Unix and Linux systems and comes available by default with Kali.
Support
The level of support delivered by each provider differs considerably. OpenVAS has a Security Response Team that can help respond to security issues with the software or any associated modules. There is also a community forum where you can seek guidance from the wider-user community.
Nessus also offers a wide range of support options including 24/7/365 email, phone, portal, and chat technical support to assist the user with any problems (providing you purchase a package with advanced support). The diversity of Nessus’ support options gives it an advantage in this area.
Platform Support
The platform support provided by Nessus is also much more diverse than that of OpenVAS. Nessus supports a range of operating systems including Windows Server 2008, 2008 R2, 2012, 2012 R2, 2016, Windows 7, 8, 10, Debian/Kali Linux, Red Hat Enterprise Linux, CentOs, Oracle Linux, Free BSD, Fedora, SUSE Linux Enterprise, and Ubuntu.
OpenVAS comes with Kali Linux and supports many Linux OS’s but doesn’t support Windows users. The user also has to build binaries from the source code or seek assistance from the community.
Cost
As an open-source tool, OpenVAS is much more affordable than Nessus because it’s free, making it more suitable for smaller enterprises that don’t have the budget to pay for more expensive alternatives like Nessus. Nessus is free for home environments, but companies need to pay. We’ve listed the pricing options below:
Nessus Pro Pricing
| License | Pricing |
|---|---|
| 1 year | $2,790 |
| 1 year with Advanced support* | $3,190 |
| 2 year | $5,440 |
| 2 year + Advanced support* | $6,240 |
| 3 years | $7,951 |
| 3 years + Advanced support* | $9,151 |
*Advanced support provides enterprises with 24/7/365 phone, email, community, and chat support.
While the price is still competitive for a cybersecurity tool the low cost of OpenVAS makes it a choice that appeals more to the SMEs who have a lower budget to spend on the software but still want a reliable vulnerability scanning solution.
It’s worth noting that there is also a source edition of OpenVAS called the Greenbone Source Edition (GSE), but we’re not featuring this as part of the comparison for simplicity.
Nessus vs OpenVAS: The Verdict
Given the history behind Nessus and the later development of OpenVAS, it’s not surprising that these two vulnerability scanners are regularly compared with each other. While they each have their own strengths, Nessus stands out as the stronger product overall for enterprises that can afford the price tag.
The combination of a modern user interface, extensive plugins, templates, and diverse platform support, provides a superior monitoring experience to that of OpenVAS. One of the few advantages OpenVAS has over Nessus is its low cost.
As a result, OpenVAS is likely to be a better fit for those organizations that require a vulnerability scanning solution but can’t or don’t want to pay for a more expensive solution. For most enterprises that have the budget, Nessus is the natural choice of the two for an optimal vulnerability scanning experience.





Great insightful article. Thank you.