Nectea began operations in 2018. The bot management system was evolved out of a queuing system, called TrafficDefender. The new bot manager has built up a client list that includes some big-name corporations, including Sony, Malwarebytes, Pets at Home, and ClearScore.
The system uses a multi-layered strategy to identify bot activity and has a false positive incidence of less than 0.001 percent. That’s important in the competitive world of eCommerce, where any slight inconvenience can cause a potential client to go elsewhere. Netacea targets the right traffic quickly and leaves real people to get on with their visit to your site.
Here is our list of the five best alternatives to Netacea:
- Cloudflare Bot Manager This bot protection system is part of a package of useful tools for website owners, which includes a CDN, a free SSL certificate, and DNS management. This is a cloud-based service.
- Radware Bot Manager A plug-in package that scans incoming packets for signs of DDoS attack or Application-level bot activity.
- DataDome A bot detection plug-in that is strong on fraud prevention and includes 15 separate tests.
- Reblaze Bot Management A fast proxy system that uses AI-based behavioral analysis and includes a content delivery network.
- Imperva Web Application Firewall A bot management system that can be hosted on-site as a physical or virtual appliance, on a private cloud, or a SaaS platform.
Netacea bot detection
The Netacea package is a traffic checker that scans for automatically generated activity. Humans behave in a particular way, which is often random but usually does fit into patterns of behavior. The producers of bots try to emulate human behavior but they can never get the randomness exactly right and Netcea has developed a system that can spot the difference between humans and pseudo-humans.
There are many different tasks that bots are created for. These include inventory hoarding, content scraping, and account fraud. As far as Netacea’s system is concerned, it doesn’t matter what the bot is trying to do; what’s important is how it does it. This makes the bot detection system universal. It can be applied to any type of website and it will identify any type of automated scam.
The Netacea bot detection service, called N/ Monitor works with an Intent Analytics engine. This is a form of machine learning, which is a discipline of Artificial Intelligence. The system tracks how a typical user on a Web page or feature behaves. There will be some variations in this pattern of behavior, but it is possible to identify a typical human move on a page. Once that baseline has been established, the Netacea service looks for deviations from that pattern. That outlier is probably a bot up to no good.
Machine learning takes time to establish a typical user behavior profile. However, Netacea has universal behavior patterns that have been derived from the implementations for exciting customers. As time passes, the Intent Analytics engine refines that behavior template so it becomes tailored to the behavior encountered on your site.
Some of the bots on your site might be there at your behest – a synthetic monitoring system is an example of this. In such cases, you will be able to approve the bot and so it won’t be included in the assessment the next time it runs through your site. This whitelisting will also cause the behavior profile to be recalculated.
Netacea bot response
As with any activity in life, there is no hard and fast rule to apply when identifying bot activity. There are gray areas, so the Netacea response package, called N/ Protector has three strategies.
A dead cert bot is automatically blocked. Each time Netacea identifies a bot, it records the source of that activity in terms of browser fingerprinting. So if that source tries again, it can be blocked immediately.
A suspected bot is flagged for further analysis. A challenge can be set up to outright ask if the visitor is a robot. Netacea human analysts will also look at outliers to decide whether that visitor is a bot.
That means bots are either identified:
- on a blacklist and blocked immediately
- as a bot through behavior analysis and blocked
- as a potential bot through behavior analysis and then challenged
This three-stage approach is the secret to the speed of a Netacea assessment.
Netacea deployment options
Netacea is unusual because it doesn’t hijack your traffic as a proxy server or require a call to an API, which are the two implementation strategies that most bot management systems use. Instead, the tool integrates into another system that you have subscribed to. It piggybacks onto another package.
Examples of services that can contain Netacea include content delivery networks, such as Amazon CloudFront, Cloudflare, and Netacea’s CDN, which is called Netacea Cloud. You can also get Netacea as part of Splunk or ElasticSearch.
Netacea prices
Netacea doesn’t publish its price list, so you have to fill out a form at the Netacea website to request a quote. You can access a demo to assess the service.
Netacea strengths and weaknesses
Netacea is an interesting bot management system that is attracting a lot of attention in the industry. We have identified several good and bad points about the service.
Pros:
- Three-phase detection strategy
- Blacklisting and whitelisting
- Integrates into other products
- AI-based detection
- Low false positive rate
Cons:
- No on-site package
Alternatives to Netacea
The market for bot management is very crowded at the moment and you can spend a lot of time assessing all of the different tools available. Netacea is not your only option. So, we have done the legwork for you to speed up your assessment program.
Our methodology for selecting an alternative to Netacea
We reviewed the market for bot management systems like Netacea and analyzed the tools based on the following criteria:
- AI-based behavior analytics
- DDoS attack detection
- Automated responses
- Blacklisting
- Fast detection process
- A free trial or a demo system for a no-obligation assessment opportunity
- Value for money, represented by a comprehensive bot detection system at a fair price
With these selection criteria in mind, we looked for systems that can identify and block bot activity
You can read more about each of these systems in the following sections.
1. Cloudflare Bot Manager
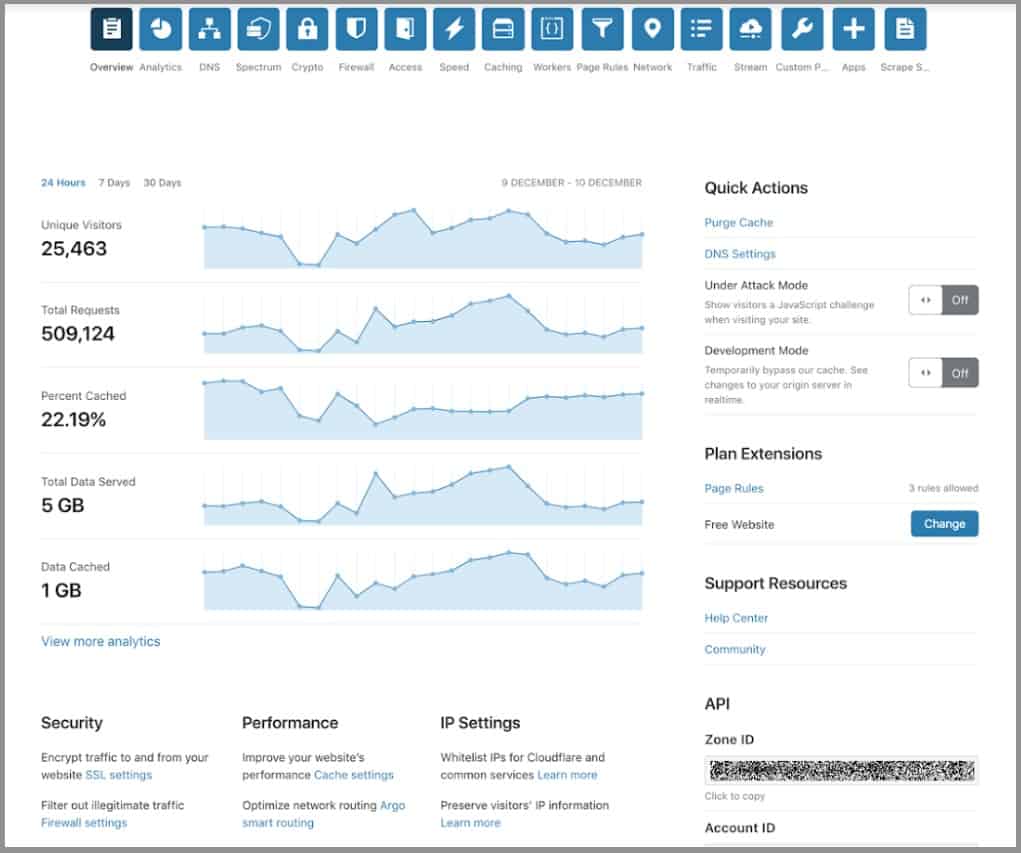
Cloudflare combines a bot manager, a content delivery network, DNS management, and a free SSL certificate in a package that is offered in free and paid plans. The system is a cloud-based edge service. Cloudflare is widely used and scans 28 million HTTP requests every second.
Key Features:
- Cloud-Based: Provides edge service through the cloud for scalability and reliability.
- Bot Identification: Detects and blocks malicious bots using advanced techniques.
- DDoS Protection: Offers robust protection against Distributed Denial of Service attacks.
- Blacklisting: Maintains a comprehensive, shared blacklist of known bot servers.
- Browser Fingerprinting: Uses detailed device information to accurately identify bots.
Why do we recommend it?
Cloudflare Bot Manager is a leading Web application protection system and can be bundled in with a Web application firewall or a content delivery network service from Cloudflare. The company built its reputation on DDoS protection and it also identifies bots used for credentials cracking, credit card stuffing, inventory hoarding, and content scraping.
The Bot Manager service can absorb DDoS attacks and also detect Application-layer bot activity, such as content scraping, inventory hoarding, and credentials stuffing. The tool tracks activity on the site and identifies bots by the difference to a baseline of standard human behavior. When the service detects bot activity, it stores the identity of that traffic source on a blacklist.
The blacklist is compiled across all Cloudflare customers, so it accumulates a comprehensive list of bot servers. A quick check to the blacklist can save a lot of time and make bot blocking a fast process. Identities are stored as fingerprints rather than just IP addresses. The browser fingerprinting system combines many identifiers from a device, including browser and operating system versions and a list of plug-ins.
Who is it recommended for?
Cloudflare Bot Manager is part of the Application Security & Performance package from Cloudflare. This is a WAF and it has four plan levels that target different business sizes. The first plan level is Free and is heavily marketed through partnership with Web hosting services.
Pros:
- Content Delivery Network: Enhances web performance by delivering content efficiently.
- Free SSL Certificate: Provides secure communications with a complimentary SSL certificate.
- DNS Service: Includes DNS management for streamlined website operations.
- Fast Web Page Delivery: Improves site speed with efficient content delivery.
- Free Version: Offers a no-cost plan with essential features, making it accessible to small businesses.
Cons:
- Lengthy Bot Detection: Full bot detection scans can cause significant delays for legitimate users.
The full package that includes the Bot Manager is called Cloudflare Application Services. It includes a content delivery network and a free SSL certificate. Cloudflare operates data centers in more than 200 locations around the world and it caches your site at a selection of three. This service makes the delivery of your site’s pages faster. It also provides a failover service because each of the cache servers can substitute for each other if one goes down. Bundle. The Cloudflare Application Service’s bundle is available in four plans and the entry-level package is Free.
EDITOR'S CHOICE
Cloudflare Bot Manager is our top choice for web application protection due to its robust capabilities and comprehensive service offerings. This cloud-based edge service combines bot management, a content delivery network (CDN), DNS management, and a free SSL certificate in both free and paid plans. It effectively scans 28 million HTTP requests every second, making it a reliable and efficient solution for securing web applications.
The Bot Manager excels in DDoS protection and bot identification, using advanced techniques such as browser fingerprinting to differentiate between legitimate users and malicious bots. Its ability to detect and block bots involved in activities like credential cracking, credit card stuffing, inventory hoarding, and content scraping sets it apart as a leading solution in the market.
Cloudflare’s extensive global network of data centers enhances the speed and reliability of web content delivery. The service’s caching and failover capabilities ensure that your website remains accessible and performs optimally even during server failures. The inclusion of a free SSL certificate further enhances the security of your web traffic.
Download: Download the Free Version
Official Site: https://www.cloudflare.com/products/bot-management/
OS: Cloud-Based
2. Radware Bot Manager
Radware Bot Manager operates as a plug-in to a Web server or it can be integrated as an add-on to the Radware CDN or Web application firewall. The service can protect websites, mobile apps, and APIs. It operates both at the packet level and across packets at the Application Layer. The dual focus allows it to block DDoS attacks and task automation attacks that manipulate features in Web applications. After performing its scans, the Radware module returns a pass or fail signal to the Web server.
Key Features:
- Plug-In Delivery: Integrates seamlessly as a plug-in to web servers.
- WAF and CDN Integration: Can be added to Radware’s Web Application Firewall or Content Delivery Network.
- DDoS Attack Blocking: Protects against Distributed Denial of Service attacks.
- AI-Based Behavior Analysis: Uses artificial intelligence to detect and analyze anomalous behavior.
Why do we recommend it?
Radware Bot Manager is able to spot customer fraud attempts, such as credit card fraud and inventory hoarding, as well as credential stuffing attacks. The package also provides DDoS protection. The system can protect mobile apps and APIs as well as websites. It can spot identify spoofing and replay attacks.
The application-level checks use AI to perform behavioral analysis and spot anomalous behavior. This flags specific visitor sessions for tracking and deeper investigation. The result of a bot being detected gets that source of traffic added to a blacklist. The Radware system scans its blacklist first before performing checks and that reference phase speeds up bot management.
The problem with the plug-in format of Radware Bot Manager is that it doesn’t protect your Web server from DDoS attacks – those large volumes of traffic still get to your server and can overwhelm its ability to process connection requests. Taking the service as part of the WAF or CDN services resolves that problem because both are hosted, so the Radware servers absorb all of the DDoS requests.
Who is it recommended for?
This package is sophisticated and is, therefore, quite expensive. So, it is suitable for large companies with big budgets. Companies that operate in eCommerce or rely on mobile apps for contact with customers particularly need this tool. The base plan processes up to 50 million requests per month but it is possible to go higher.
Pros:
- Effective Blacklisting: Maintains a comprehensive blacklist to quickly block known threats.
- Fight Back Option: Offers proactive measures against detected threats.
- Integration Flexibility: Can be integrated with Radware’s WAF and CDN for enhanced protection.
Cons:
- Traffic Queuing: The standard configuration may still require traffic to queue, impacting performance.
Another option for the Radware WAF is that it can be hosted on your servers as a virtual appliance. However, you are then back to the problem of managing the large volumes of traffic that arise from a DDoS attack. Radware Bot Manager is available for a 30-day free trial.
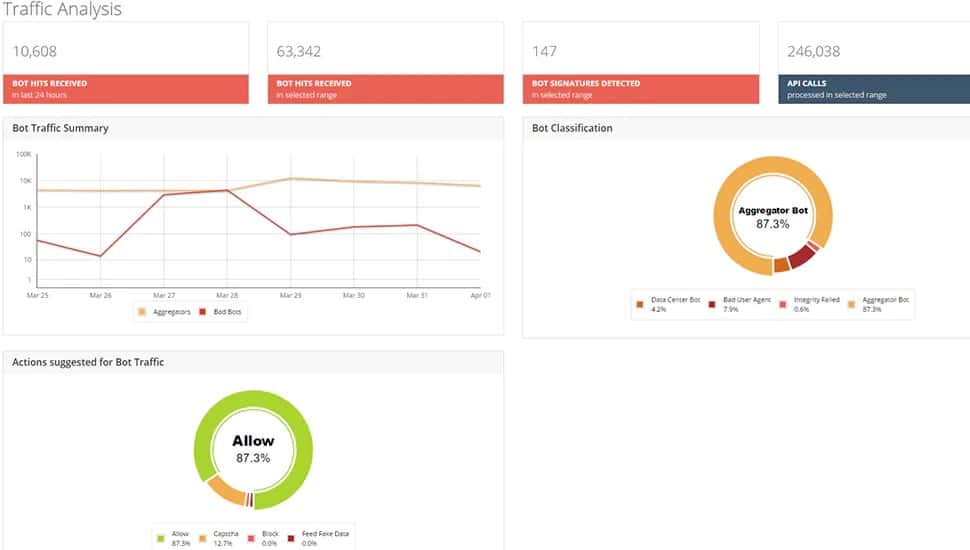
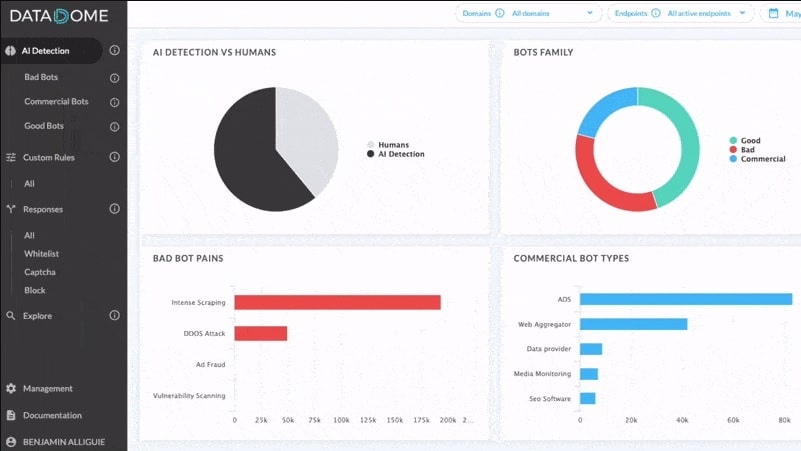
3. DataDome
DataDome operates as a function call that needs to be embedded into your Web assets, so while the processing part of the system is hosted in the cloud, you still need to manage traffic coming into your Web server, including DDoS floods. The system is suitable for protecting websites, mobile apps, and APIs.
Key Features:
- Plug-In Deployment: Requires embedding a function call into your web assets.
- Test Sequence Options: Provides customizable options over the test sequence for traffic assessment.
- DDoS Detection: Identifies and mitigates Distributed Denial of Service attacks.
- Application-Level Tests: Conducts detailed tests at the application layer to identify malicious activities.
Why do we recommend it?
DataDome provides a fast assessment of each request arriving at a Web server. The assessment process takes 2 milliseconds to complete and results in an allow or deny recommendation. The service protects websites, APIs, and mobile apps. It can detect DDoS attacks, probing, scraping, and account takeover attempts.
The DataDome dashboard offers a list of 15 scanning systems. There are also four templates available that act as preset combinations of tests to deploy in specific situations. The first test run by the system is usually a blacklist reference. It isn’t ever necessary to run all 15 checks and the average assessment from DataDome takes about 2 milliseconds.
The DataDome system will detect DDoS traffic and it also operates at the Application layer. The tool is very strong on fraud detection, which makes it a good choice for online stores. The system is also able to identify content scraping, scalping, inventory hoarding, and account takeover.
Who is it recommended for?
This service is designed for very large businesses that run websites, use APIs, and/or operate mobile apps. While the Radware system is expensive, Datadome costs even more – roughly double, so it is completely out of reach for all but the most successful eCommerce businesses.
Pros:
- Large Scale Protection: Ideal for large online stores needing comprehensive protection.
- Activity Reporting: Offers detailed activity reporting for monitoring and analysis.
- Strong Fraud Protection: Excels at detecting fraud, making it suitable for eCommerce.
Cons:
- High Cost: Expensive, making it less accessible for smaller businesses.
- Traffic Management Needed: Does not pre-filter packets, requiring additional traffic management for volume attacks.
As the DataDome system doesn’t pre-filter packets, you still have the issue of traffic management and volume attacks to deal with. Another factor that might put you off DataDome is its price – it is considerably more expensive than Cloudflare. You can evaluate DataDome with a 30-day free trial.
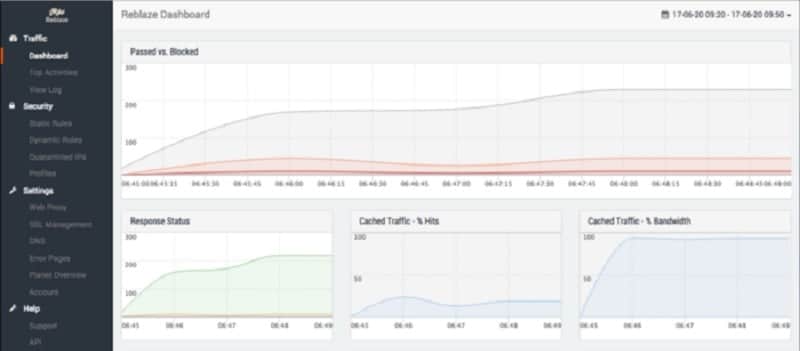
4. Reblaze Bot Management
Reblaze Bot Management is a proxy service that scans through your incoming Web traffic and weeds out the malicious activity before it hits your Web server. This is a great tool for speeding up your Web server performance because it lightens the load and on average, its checks take around 0.5 milliseconds to complete.
Key Features:
- DDoS Filtering: Blocks Distributed Denial of Service attacks before they reach your server.
- Content Delivery Network: Enhances performance with a global CDN.
- Traffic Analysis Reporting: Provides detailed reports on traffic activity and threats.
Why do we recommend it?
Reblaze Bot Management is a similar system to DataDome because it is a reference service that assesses and then passes or fails a submitted request. Reblaze beats DataDome on speed because it completes its tests in 0.5 milliseconds. The system performs a hybrid assessment of four stages, which include profiling and behavior analysis.
Reblaze will immediately filter out DDoS floods and its blacklist also takes care of a lot of malicious traffic very quickly. It has four phases of tests and its Application layer system uses AI-based behavior analysis to catch a long list of malicious activities. These include fraud attempts of all kinds, scalping and inventory hoarding, account takeover and account cracking, and click fraud.
The Reblaze package includes a CDN, which is hosted at a series of data centers around the globe. These interact with an account control module, which you install on a cloud account, such as AWS, GCP, or Azure. This, in turn, interfaces to your Web server. This architecture is a little complicated. However, it allows you to access your account dashboard on your chosen cloud server. The dashboard includes access to fine-tuning services, such as whitelisting. It also offers activity analysis that shows allowed traffic metrics as well as information about bots that were blocked.
Who is it recommended for?
The bot manager is offered as part of the Reblaze WAF and the Reblaze CDN. These deployment options are hosted and they filter traffic before they reach your Web server, which is an optimum strategy for dealing with DDoS attacks. This is a solution for large, Web-based businesses.
Pros:
- Very Fast Service: Completes checks in approximately 0.5 milliseconds, enhancing server performance.
- Comprehensive Fraud Detection: Protects against various forms of fraud and account-related threats.
- Content Protection: Safeguards your content from malicious activities.
Cons:
- No Published Pricing: Lacks a publicly available price list, making cost assessment difficult.
Reblaze is available for a 30-day free trial.
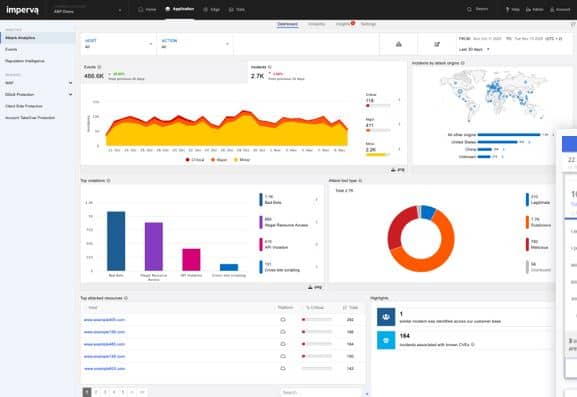
5. Imperva Web Application Firewall
Imperva Web Application Firewall is a prominent protection system for Web applications. The system has an integrated Bot Manager and its deployment in front of your Web server enables it to protect all of your operating code, including those services that are supplied and hosted by third-party vendors. The service is a good option for protecting mobile apps and APIs as well as websites. It takes the stance of assessing visitors and users before they are granted access and during their usage of the site or app.
Key Features:
- DDoS Protection: Shields your web applications from Distributed Denial of Service attacks.
- Integrated Security: Combines with a wider web application security framework, including bot management.
- DevOps Friendly: Suitable for development and operations teams, supporting secure deployment practices.
Why do we recommend it?
Imperva Web Application Firewall is a proxy service that operates as part of a Web application firewall. This package will block all malicious traffic from getting anywhere near your Web server and that includes bot activity. The service protects APIs as well as Web applications.
The Advanced Bot Protection module of the WAF includes a blacklisting strategy and AI-based behavior tracking. This service will automatically block DDoS attacks, account takeover and break-in attempts, content scraping, scalping, inventory hoarding, payment, and card fraud, and click fraud.
Advanced Bot Protection is also available as an add-on to the Imperva content delivery network service. The WAF is a good option to take as part of a wider system security strategy because it can interface directly with SIEM systems.
Who is it recommended for?
This system is designed for use by DevOps teams. That is for businesses that both develop and run Web systems. The service is in compliance with PCI DSS and it will provide activity logging for compliance reporting. This stored information on events can also be used for threat analysis.
Pros:
- Comprehensive Security Package: Includes a CDN, enhancing performance and security.
- Flexible Deployment: Available as SaaS or self-hosted, providing deployment flexibility.
- Fraud and Content Theft Prevention: Effectively blocks various forms of fraud and content theft.
Cons:
- Frequent reCAPTCHA Challenges: Utilizes reCAPTCHA often, which may disrupt user experience.
The Imperva WAF system is offered as Imperva Cloud WAF or you can choose to host it yourself with Imperva WAF Gateway, which is offered as a physical device or a virtual appliance. You can also host the WAF on an AWS account. Imperva’s WAF, CDN, and Advanced Bot Protection system are available as a bundle on a 30-day free trial.