NetWalker ransomware is a destructive strain of malware that first emerged in 2019 and has been used in attacks against organisations worldwide. It has been linked to a cybercriminal group that has targeted multiple sectors, including healthcare, education, and government, often resulting in significant operational disruption and financial impact.
Notably, NetWalker was developed and distributed using a ransomware-as-a-service (RaaS) model, making it one of the earlier examples of this approach. In this model, ransomware capabilities are effectively packaged and made available for use by other threat actors. The malware itself relies on strong encryption methods to lock critical files on infected systems, preventing access until a ransom demand is met.
Here is our list of the best tools to protect against NetWalker ransomware:
- ManageEngine DataSecurity Plus (FREE TRIAL) Focuses on protecting sensitive data with features like file integrity monitoring and data categorization, ensuring compliance with standards like HIPAA and PCI DSS. Start a 30-day free trial.
- CrowdStrike Falcon Insight Combines robust endpoint protection with cloud-based threat intelligence to prevent and respond to ransomware attacks. Its user-friendly console and lightweight agents make it efficient and effective.
NetWalker ransomware is also identified under several alternative names, including Mailto, KazKavKovKiz, and Kofer, and has been associated in some analyses with other ransomware families. Its operators are known to periodically adapt their techniques, contributing to its persistence as an evolving cybersecurity threat.
The group linked to NetWalker activity is often described by researchers as operating in a structured, conglomerate-like manner, with separate branches reportedly handling different ransomware strains as they are developed. Cybersecurity analysts frequently correlate similarities across multiple attacks to attribute activity to the same underlying actors. In some cases, tracking shared or reused code between different ransomware samples can also help map the evolution and relationships between variants.
This article examines how NetWalker has developed over time, the methods it uses to spread, and the impact it has had on organisations. It also outlines best practices for detection, prevention, and recovery, with the aim of helping organisations strengthen their resilience against similar ransomware threats.
Who produced NetWalker?
NetWalker, which some write as NetWalker, is a property of the group called Circus Spider. This is a division of Mummy Spider. The entire syndicate is based in Russia, and there are other partners in the organization that have produced well-known ransomware and different types of malware. Mummy Spider created a cybercrime network in 2014, using a Trojan called Emotet to infect many private computers. These infections can check in with a central Command and Control (C&C) server for instructions. The enormous army of infected computers is called a botnet.
The Mummy Spider expertise also created Trickbot, another botnet, through its Wizard Spider division. Another division, called Grim Spider, used the Trickbot system to distribute ransomware called Ryuk. So, this organization already had extensive ransomware creation experience when it set up Circus Spider to create and manage NetWalker in 2019.
The Mummy Spider conglomerate designs its malware not to attack computers based in Russia or any of the countries of the former Soviet Union. The organization is known to create extra income streams from its systems by making them available to other hacker teams for a fee. This is an Infrastructure-as-a-Service concept, and it enables other hacker teams to launch attacks without the upfront expense of developing a delivery mechanism.
Ransomware-as-a-Service
After developing NetWalker in August 2019 and running a few attacks from September 2019, the Circus Spider team decided to look for partners. In April 2020, the group made its attack software available in a Ransomware-as-a-Service model. This allows other hackers access to the software without having to distribute the code – the programs run on the Circus Spider server, and client hacker teams get access to the system through a user interface.
The Ransomware-as-a-Service concept mimics the Software-as-a-Service (SaaS) business model used by software producers to deliver cloud-based services. While SaaS providers hope to attract many customers, Circus Spider only wanted two.
The group put out a prospectus on the Dark Web and interviewed candidates. They were specifically looking for affiliates with network technology knowledge, an established pool of targets, proof of experience, and a unique attack strategy. The group would only deal with Russian-speaking associates.
Advertised features of the RaaS platform included a Tor chat panel for anonymous technical support, a multi-thread locker, a range of encryption options, automated ransom payment processing, an unlocking module, lateral infection, PowerShell routines to block AVs, and instant payouts.
The Circus Spider group’s package processed payments and paid out a share to the affiliate as soon as a ransom was received. A disclosure feature in the portal enables affiliates to see the logs of the attack events to ensure that they aren’t being cheated out of their share of ransom payments.
How does a NetWalker attack start?
The nature of NetWalker attack strategies has changed over time due to the involvement of other teams to identify targets. However, a sector that has been identified as rich in good marks is the Healthcare industry. The creators mainly targeted hospital employees with phishing emails related to the Covid-19 outbreak.
The installer for NetWalker is delivered as an attachment to an email. The attachment is usually a Word document, and it includes VBScript that triggers the installation process for the NetWalker ransomware.
Once the ransomware is installed on one endpoint on a network, it will send out an executable file to other devices. This program is called WTVConverter.exe. The ransomware executable hides as it runs by using a procedure that is known as process hollowing. It starts up explorer.exe, a legitimate process, but it starts that program in a suspended state. It then remaps the memory space allocated to that process to its code. So, the ransomware will appear as explorer.exe in the Task Manager.
Once the ransomware process runs, it moves the program file from its original location to the AppData\Roaming\ directory. It also sets up a registry key to run the program on startup.
The process for the ransomware will kill off specific other programs if they are running. This includes productivity suiter components that might have a file open, thus preventing it from being overwritten. The ransomware aims to encrypt all working files but to leave program files alone.
The NetWalker encryption process
The NetWalker encryptor has a preliminary phase once it has located files containing data. It transfers out files before starting the encryption. This is part of a worrying trend in ransomware that creates a double threat.
Businesses that have to comply with data privacy standards suffer heavy fines if data is disclosed. They can also be sued by the individuals whose information has been leaked. Organizations operating in the healthcare industry are particularly vulnerable to this type of threat because they have to comply with HIPAA to stay in business. This standard requires the protection of patient information.
The encryptor will also delete all shadow copies of Office documents. These are the autosave copies and not the backups you create. You should have a backup process to protect your data from incidences like a NetWalker ransomware attack. If you have security measures in place and save a copy off-site, you should be safe from NetWalker getting into your backup stores.
The encryptor changes the name to add on two extra extensions, the first of these is mailto, followed by an email address in square brackets. The email address is usually on the domain cock.li, although it isn’t always the same address. The second extra extension is a five-character string. This is the same on all encrypted files and forms part of the identifier for the attack.
The encryption process uses the Salsa20 cipher, which is widely used in ransomware.
The NetWalker ransom
When the encryption process finishes on a drive, the ransomware leaves a text file with the ransom demand. This directs the victim to contact one of two given email addresses for instructions. The first of these addresses is the one appended to each encrypted file’s name.
NetWalker ransomware gives victims a period of grace to pay. Once that period expires, the ransom increases and the countdown is reset. The system will release some of the data on the Circus Spider Dark Web website. This website is also the portal that victims need to access to pay the ransom. It also includes a bulletin of current victims and how long they have to pay.
If the victim still doesn’t pay, all of their data will be sold to another hacker group or published on the Circus Spider website. For those businesses following data privacy standards, the consequences of that disclosure could be disastrous. Not only will the company lose money through files, but they will also lose most of their customers who are obliged to only deal with suppliers that have standards accreditation. So, restoring from backup and ignoring the ransom demand is not an option.
Defending against NetWalker ransomware
The NetWalker system is not currently active. One of the associates of the team, a French Canadian, was arrested in January 2021. At the same time, the US and Bulgarian authorities completed a joint operation against the Circus Spider website. Taking down the site removed the threat of data disclosure, making restoring from a backup a viable option. However, the team is still active, so there is no guarantee that the NetWalker ransomware won’t come back.
The bottom line to defend against NetWalker and all ransomware is to educate your user community against clicking on links in emails or downloading attachments. You also need to buy security software.
Tools to protect against NetWalker ransomware
You need security systems that implement endpoint detection and response (EDR) and protect sensitive data to ensure privacy standards compliance. You probably won’t find the best protection from one tool that performs all protection tasks. However, with a combination of tools, you can both defend against ransomware and provide a second line of defense that ringfences the sensitive data that your organization holds.
Our methodology for selecting the best tools to protect against NetWalker ransomware:
We’ve broken down our analysis for you based on these key criteria:
- Ransomware Detection and Prevention: Tools must effectively detect and prevent ransomware attacks.
- Threat Intelligence: Integration of real-time threat intelligence to stay ahead of new ransomware variants.
- Endpoint Protection: Robust endpoint protection capabilities to safeguard all connected devices.
- Ease of Use: User-friendly interfaces and ease of deployment and management.
- Compliance Support: Ability to meet and support compliance with industry standards like HIPAA, PCI DSS, and GDPR.
Consider the following security systems to defend against NetWalker ransomware.
1. ManageEngine DataSecurity Plus (FREE TRIAL)
ManageEngine DataSecurity Plus focuses on protecting sensitive data. It is suitable for businesses that need to comply with PCI DSS, HIPAA, and GDPR. The software package is well-tailored to protect against the data theft aspects of the NetWalker ransomware and its encryption activities.
Key Features:
- Sensitive Data Discovery: Identifies and locates sensitive data across computers and cloud accounts.
- Data Categorization for Compliance: Categorizes data to ensure compliance with standards like GDPR, PCI DSS, and HIPAA.
- File Integrity Monitoring: Monitors file integrity to detect unauthorized changes or actions.
- Data Movement Tracking: Tracks and blocks unauthorized data movements to prevent data theft.
- Automated Responses: Enables automated actions such as killing processes, deleting files, and isolating devices from the network in response to threats.
Why do we recommend it?
ManageEngine DataSecurity Plus is a data loss prevention system and not an AV. This package scours all computers and cloud accounts for data and then identifies whether it is a protected type of data, according to a given standard. This system can adapt its processes for GDPR, PCI DSS, FISMA, and HIPAA.
The first task of DataSecurity Plus is to seek out all stores of sensitive data. It then scans all data files and categorizes the sensitivity of the information held within. This allows you to implement a strategy that adds protection to specific types of data. For example, healthcare businesses will need to protect patient information. This tool isn’t just about standards compliance. It will also cover intellectual property and trade secrets.
Once the files that need to be protected have been identified, DataSecurity Plus implements a file integrity monitor (FIM). This identifies unauthorized actions on files, and the encryption performed by ransomware falls into this category.
When a problem arises, DataSecurity Plus will raise an alert. It is also possible to specify that the system implements automated responses. These actions include killing processes, deleting program files, isolating the device from the network, and restoring files from backup storage.
Who is it recommended for?
This package supplements an AV rather than replaces it. This is because the tool doesn’t look for malware. Instead, it watches actions on the files that contain sensitive data and also tracks user activity surrounding that data. It will block any actions on protected data, such as file transfers.
Pros:
- Detailed File Access Monitoring: Offers comprehensive logs of file access to help sysadmins understand file changes in context.
- Access Trend Analysis: Tracks access patterns over time, improving the detection of malicious behavior.
- Built-In Compliance Reporting: Supports compliance with standards such as HIPAA, PCI DSS, and FISMA through built-in reporting tools.
- Integration Capabilities: Integrates with various helpdesk solutions, notification platforms, and backup systems for streamlined operations.
Cons:
- Learning Curve: Requires time to fully explore and understand all tools and features available.
DataSecurity Plus installs on Windows Server and protects endpoints running Windows. It is available for a 30-day free trial.
2. CrowdStrike Falcon Insight
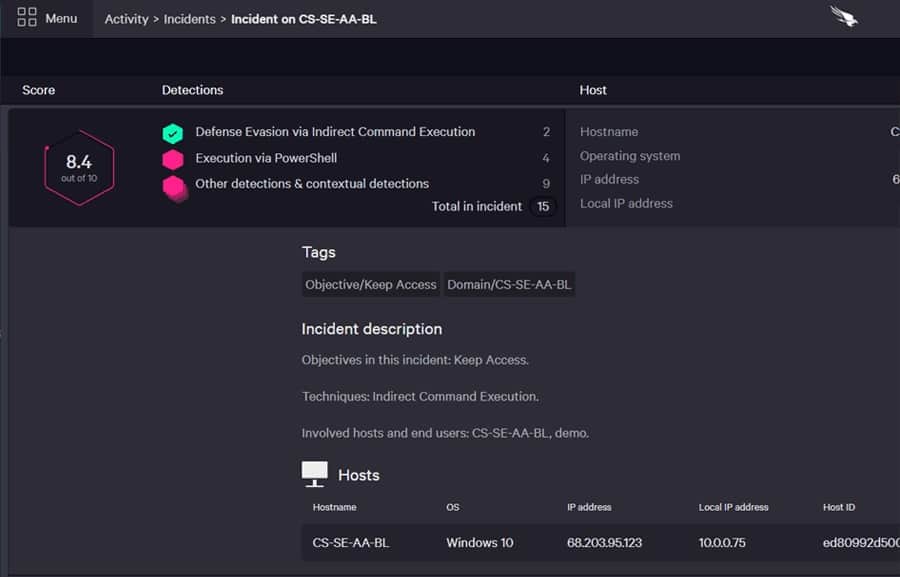
CrowdStrike Falcon Insight is an endpoint detection and response (EDR) system that includes device-resident software and a cloud-based coordinator. Having a significant part of this system on each endpoint ensures rapid responses and maintains protection even when the device is offline.
Key Features:
- Indicators of Compromise Detection: Identifies signs of potential security breaches on endpoints.
- On-Device Threat Hunting: Performs threat hunting directly on the device to quickly detect and respond to threats.
- Cloud-Based SIEM: Utilizes a cloud-based Security Information and Event Management system for centralized threat monitoring and management.
- Lateral Movement Blocking: Prevents the spread of malware within the network by blocking lateral movements.
- Threat Intelligence Updates: Provides continuous threat intelligence updates to keep endpoints protected against the latest threats.
Why do we recommend it?
CrowdStrike Falcon Insight is a cloud-based XDR, or SIEM. It collects logs from endpoint units, which are themselves independent antivirus packages. This service can isolate the device from the network to prevent data extraction or lateral movement and the AV keeps working while the computer is disconnected.
The cloud coordinator can process activity reports uploaded by all of the endpoint agents. It also receives threat intelligence feeds from CrowdStrike to keep up to date with the latest attack strategies. This information comes from CrowdStrike analysts and also from the attacks experienced by other CrowdStrike customers.
The cloud system updates each endpoint agent with the latest intel, and it also enables all agents to be warned if one device gets hit.
The endpoint agent is also available as a standalone product called CrowdStrike Falcon Prevent. This searches for suspicious activity rather than specific file names or processes. By this method, the service can spot and block malware that cybersecurity consultants have not yet identified. CrowdStrike runs a malware research lab that was one of the primary identifiers of the NetWalker ransomware. The system is fully equipped to deal with NetWalker through automated responses.
Who is it recommended for?
Insight is ideal for ransomware like NetWalker because its endpoint agent is a full AV. The cloud-based unit informs all other computers on the network while the unit on the infected computer deals with the malware by itself. This does mean that its price is a bit too high for small businesses.
Pros:
- Comprehensive Ransomware Prevention: Effectively prevents ransomware across various environments including Windows, Linux, Cloud, and BYOD.
- User-Friendly Admin Console: The intuitive cloud-based console simplifies setup and management, making it easy to use.
- Behavioral Monitoring: Tracks and alerts on anomalous behavior over time, improving accuracy and detection with prolonged use.
- Lightweight Agents: Uses minimal system resources, ensuring endpoint performance is not compromised.
Cons:
- Short Trial Period: The trial period could be longer to allow for more thorough evaluation.
You can get a 15-day free trial of Falcon Prevent.





