Configuring dozens or even hundreds of individual nodes is virtually impossible without the right tools.
Even straight-forward tasks like backing up router configurations become long, tedious affairs without the assistance of additional software when brought to scale.
From automation to network-wide monitoring, network configuration management software is designed exclusively with busy administrators in mind.
Here is our list of the best network configuration backup software:
- NinjaOne Endpoint Management EDITOR’S CHOICE Full remote fleet management package that includes configuration backup and monitoring. Start a 14-day free trial.
- ManageEngine Network Configuration Manager (FREE TRIAL) Full network configuration management tool that includes backup and policy enforcement. Download a 30-day free trial.
- Site24x7 Network Configuration Management (FREE TRIAL) Cloud-based protection system for network devices that includes firmware patching and configuration image storage with tamper blocking. Start a 30-day free trial.
- Domotz Cloud-based network and endpoint monitoring and management platform, includes a device configuration and backup service.
- LogicVein Net LineDancer Asset inventory system that includes configuration backups.
- Infoblox NetMRI Focused on security, this tool backs up device configurations while scanning for and rectifying compliance issues.
- SolarWinds Network Configuration Manager Stores images of device setups and prevents unauthorized alterations to configurations.
- LibreNMS with Oxidized Add-on Free network configuration management tool with a configuration management and backup system.
- BackBox Network manager with task automation, including inventory reporting and configuration backups.
- BMC TrueSight Automation for Networks Creates scripts that function as configuration backups allowing unauthorized changes to be rolled back.
- rConfig Free open-source configuration manager that includes a backup function.
What to look for in network configuration backup tools
When searching for configuration software, it’s good to take a look at a few different key things:
- Scalability – How well the product scales with size. Not all software is meant to be used on a massive sprawling multi-vendor network with thousands of nodes. A product that works beautifully with a dozen network assets may become a struggle to manage with a hundred. It’s important to pick the software that will work not just for the current size of your network, but for any potential increases in scale as well.
- Customization – Every network is different, and being able to tailor the application managing it is key to good configuration software. The best products will have some amount of inflexibility in order to meet their intended design goal, with enough flexibility in customization to fit a wide range of networks.
- Features – Some applications are designed only to be used as network configuration management software. Others take a more broad approach, functioning as more than just configuration repositories. Knowing what you want your software to do is critical to getting the most out of your selection.
- Product Support – The available documentation and support for any given product can range from overwhelmingly good to ‘play with it until things start working.’ This can be particularly true for free products. Make sure you can get up and running quickly with whatever you end up using.
- Presentation – Some configuration managers simply provide a text dump in a Command Line Interface (CLI), that may be entirely functional for some users. Others will have robust GUIs with complex topology visualizations, analytics laid out in graphs, and your own logo splayed across the back-end interface. The presentation of a configuration manager, from its aesthetic interface to ease of use, should play a part in your decision to use a given piece of software.
This is far from a comprehensive list of criteria, but it’s a good general list of things to start thinking about.
The best network configuration backup tools
The options available are almost as numerous as the nodes they will eventually be used for. It seems almost every vendor has their own proprietary network backup software and configuration manager, while a dizzying array of third-party developers feature their own programs with multi-vendor support. These can range from incredibly powerful to barely functional.
Our methodology for selecting network configuration backup tools
We reviewed the market for network configuration backup software and analyzed the options based on the following criteria:
- System that takes an image of each device’s settings and stores them
- Configuration manager that allows configurations to be standardized per device make and model
- Monitors all devices for configuration changes and automatically reapplies the stored image if any are detected
- Dashboard that enables a standardized image to be applied in bulk to many devices
- Onboarding function that allows new devices to be set up by applying a standard image
- Free trial for a cost-free assessment period or a free tool
- Repays its purchase price with improved efficiency or a free utility
This list aims to bring together a handful of the top choices, both free and paid, to help you find the right solution for your network.
1. NinjaOne Endpoint Management (FREE TRIAL)
NinjaOne is a platform of services for managed service providers. This suite is delivered from the cloud and is also suitable for use by IT departments for multi-site monitoring. The NinjaOne Endpoint Management module offers remote monitoring for networks, endpoints, and network devices. It includes a configuration backup and monitoring service.
Key Features:
- Backup and Restore: For endpoints running Windows or macOS
- Cloud Storage: Copy backups to the cloud
- Backup Strategies: Store a copy locally and another remotely
Why do we recommend it?
NinjaOne Endpoint Management is confusingly named because it also monitors and manages network devices. So, this tool includes configuration management for all of your equipment. You can store backups of each device’s configuration and set the tool to monitor for unauthorized changes and reapply the official settings.
The Endpoint Management service of NinjaOne also monitors networks. This is implemented efficiently because the SNMP system can be used to extract performance data from servers and desktops as well as network devices, such as switches and routers. The package installs an agent on each endpoint and can be used for a backup service as well.
Configuration backup takes an image of the device and stores it. Subsequent changes to those settings could indicate intruder attempts to cover their tracks and so need to be corrected immediately. The NinjaOne system includes automation that will quash tampering.
The stored OS image can be used to rapidly onboard a fleet of similar devices and this process also benefits from workflow automation.
As the NinjaOne platform is based in the cloud, its capabilities are not restricted by the boundaries of one network. You can use the tool to monitor endpoints on any network anywhere and also the computers in the homes of telecommuting employees.
NinjaOne has a multi-tenant architecture, which makes it ideal for use by MSPs.
Who is it recommended for?
NinjaOne is built in versions for IT departments and managed service providers. The Endpoint Management package is classified as an IT department tool. The equivalent to this package for use by MSPs is the NinjaOne RMM. This tool is based in the cloud, so it can be accessed from anywhere through a browser.
Pros:
- Network Monitoring: Device discovery and constant monitoring
- Device Status Monitoring: Uses SNMP
- Remote Monitoring and Management Package: Includes task automation
Cons:
- Doesn’t Provide Configuration Management: Monitors device status but not configurations
NinjaOne offers a range of utilities for remote management of IT systems and all of them are structured to make them suitable for use by MSPs. You can combine a Remote Monitoring and Management package with the NinjaOne Backup system to get a full system protection service. NinjaOne doesn’t publish its price list, so you need to contact the Sales Department to get a quote. Access a 14-day free trial of the NinjaOne platform.
EDITOR'S CHOICE
NinjaOne Endpoint Management is our top pick for a network configuration and backup solution because this endpoint-focused system can be adapted to backup network device configurations as well. This system provides servers and workstations with protection against accidental or intentional damage to data and its file-level backup and restore system also gives you insurance against ransomware attacks. So, adapting the process to take a backup of your network devices as well would give you a central store for all of your systems.
Download: Access a 14-day FREE Trial
Official Site: https://www.ninjaone.com/freetrialform
OS: Cloud-based
Related: NinjaOne Backup – Full Review
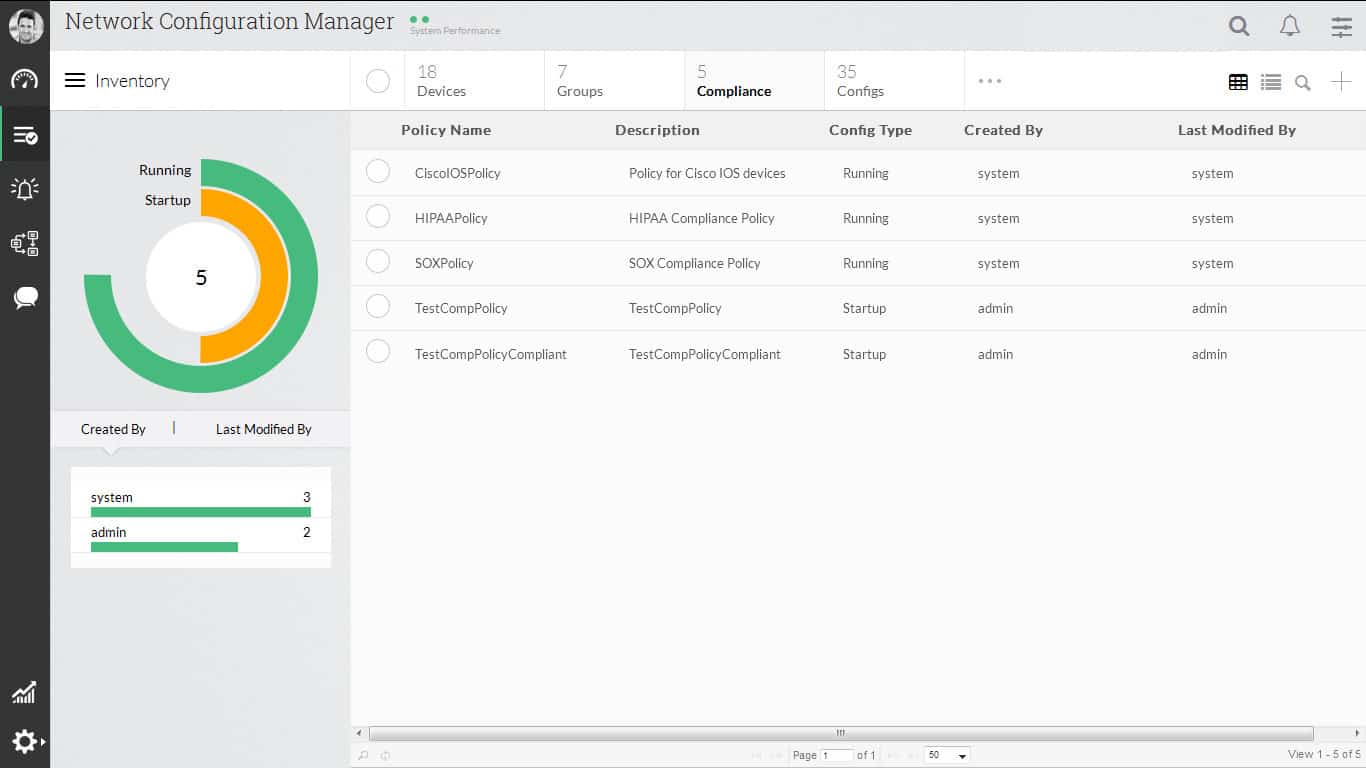
2. ManageEngine Network Configuration Manager (FREE TRIAL)
Coming from a large family of other ManageEngine products, ManageEngine’s Network Configuration Manager is one part of a larger networking suite distributed by ManageEngine.
Aimed squarely at being a configuration tool, ManageEngine’s Network Configuration Manager is a multi-vendor network configuration and change compliance product for a variety of network devices. Its sole purpose is to take control of the entire life cycle of a given networking device.
Key Features:
- Free Edition: Manages two devices
- Supports Configuration Tightening: Uses security policy templates
- Configuration Archiving: Takes an image of each device’s configuration
- Overwrites Unauthorized Changes: Restores the stored image
Why do we recommend it?
ManageEngine Network Configuration Manager supports the standardization of network device settings and it then stores images of those configurations. The tool performs a monitoring loop that checks each device for unauthorized changes, restoring the original configuration where necessary.
All the standard configuration features are found here, including configuration backup and deployment, change history, and configuration comparisons. Change tracking can be done in real-time to monitor network devices for unauthorized changes or potential complications in a configuration.
Standard automation tools are also featured here, including the automation of configuration tasks like regular network backups. Network Configuration Manager can also track user activity across devices, and routinely check for compliance with published policies and procedures. Lastly, it brings multi-vendor support along with it.
Similar to the BMC product listed above, ManageEngine’s Network Configuration Manager shines when paired with other tools in its developer’s suite. As a standalone product it achieves its intended design goal of being a straight-forward configuration manager, but lacks some depth when viewed apart from its overarching software suite.
Who is it recommended for?
This tool is almost identical to the SolarWinds Network Configuration Manager but with a few important differences. This system is offered in a Free edition that is limited to monitoring two devices, so very small businesses might try this. The system is delivered as a software package that will run on Windows Server, Linux, and AWS.
Pros:
- Device Discovery: Repeated network scanning
- Minimum Device Count for the Paid Version: 10
- On Premises: Windows Server and Linux
- Available on AWS: Get it from the AWS Marketplace
Cons:
- No Version for Linux: Also, there is no SaaS option
Access their 30-day free trial from their site.
3. Site24x7 Network Configuration Management (FREE TRIAL)
Site24x7 Network Configuration Management is part of a package of system monitoring management tools, and it is hosted in the cloud. The tool provides a range of security measures, such as a vulnerability scanner, a backup service, and a monitor against unauthorized changes. These functions are implemented to protect switches, routers, firewall appliances, and wireless access points.
Key Features:
- Part of a Cloud Platform: A component of a SaaS package
- Tightens Security: Recommends security policies for network device configurations
- Configuration Backup: Takes an image of each device’s configuration and stores it
Why do we recommend it?
Site24x7 Network Configuration Management provides an automated process to back up the configurations of network devices. The system takes an image of the configuration of each device and stores it in a secure encrypted locker. The tool then scans each network device, looking for changes in their settings. Changes indicate hacker activity and are wiped out immediately.
All Site24x7 plans include a network monitoring service that discovers all devices on the network and generates an inventory. The Network Configuration Management function works through that list of devices and checks each of them. The tool first performs a vulnerability scan, identifying whether the firmware on the device is out of date. If it is, the tool updates it.
The NCM takes an image of the configuration of each device and stores it in a secure locker. That image is available to be applied to a replacement device if the current piece of equipment breaks.
The Site24x7 system periodically checks on each device, comparing its current configuration with the image in storage. If there is a difference between the two, the Network Configuration Management service will apply the stored version, wiping out all of the unauthorized changes on the device.
Configuration images are stored in the cloud on the Site24x7 service. This provides a business continuity service, enabling you to set up new equipment, possibly in different offices, so your workers can get back on the job as quickly as possible.
Who is it recommended for?
Site24x7 has many different modules on its platform and offers plans that include all of them for one subscription fee. Those plans are all sized for the very smallest companies and most businesses need to pay for capacity expansions. The base package provides configuration management for one device. That is, except for the MSP edition, which covers five devices.
Pros:
- Firmware Vulnerability Management: Covers all aspects of network device security
- Scans for Unauthorized Configuration Changes: These could be implemented by an intruder
- Restores Stored Configuration: Wipes out unauthorized changes
Cons:
- No On-Premises Version: This is a cloud-based SaaS platform
The Site24x7 Network Configuration Management service can protect devices provided by SonicWall, Cisco, Citrix, Aruba, and other manufacturers. Per-unit pricing makes the 24×7 package very scaleable. Get access to the Site24x7 platform with a 30-day free trial.
4. Domotz

Domotz is a cloud platform that offers the ability to monitor and manage any network remotely. The system installs an agent on a device connected to each of the networks that you enroll in the service. Among the services in this package, you will find a configuration manager. This enables you to standardize device configurations to enforce your security policies.
Key Features:
- Cloud-Based Service: This is a SaaS package
- Automatic Device Discovery: Creates and maintains a network inventory
- Configuration Backup: Also provides a restore mechanism
Why do we recommend it?
Domotz is a rival to the NinjaOne system. It is a cloud platform of tools for remote monitoring and management systems that can be used by managed service providers or IT departments. The network configuration management tool in the package backs up network device configurations and then reapplies them when unauthorized changes are detected.
The Domotz service backs up your device configurations and then repeatedly scans the network, checking all device configurations for unauthorized changes. If changes are spotted, the tool raises an alert and automatically restores the authorized settings from the backup.
The network scans don’t just look at device configurations – they also check on the status of the components of each device. Domotz also spots rogue devices and identifies any changes to the network device profile. The system automatically compiles a network inventory and a topology map. It will also generate a software inventory for each endpoint on the network and conducts patch management.
Other tools in the Domotz package include analysis tests, such as Ping and TraceRoute. The tests can be run on-demand or on a schedule and the results can be stored for time-series analysis.
Who is it recommended for?
The target audience for Domotz is exactly the same as for NinjaOne. While NinjaOne gives its RMM package a different name for its service for IT departments, Domotz uses the same system for both markets but just provides a multi-tenanted architecture that MSPs can choose to deploy and IT departments can choose to ignore.
Pros:
- Maintains a Configuration Library: Applies backups for switches, access points, and firewalls
- Spots Rogue Devices: Regular network scans reveal all devices
- Version for Managed Service Providers: A multi-tenanted architecture
Cons:
- No Vulnerability Remediation Guidance: Doesn’t supply security policy templates
A very attractive feature of Domotz is that the package is charged at a flat fee per network, no matter how many devices are connected to it. The service is structured for sub-accounts, which makes it suitable for use by MSPs to monitor the sites of their clients. It is charged as a fixed fee per network, so the price doesn’t change according to the number of devices on the LAN. You can assess Domotz with a 14-day free trial.
5. LogicVein Net LineDancer
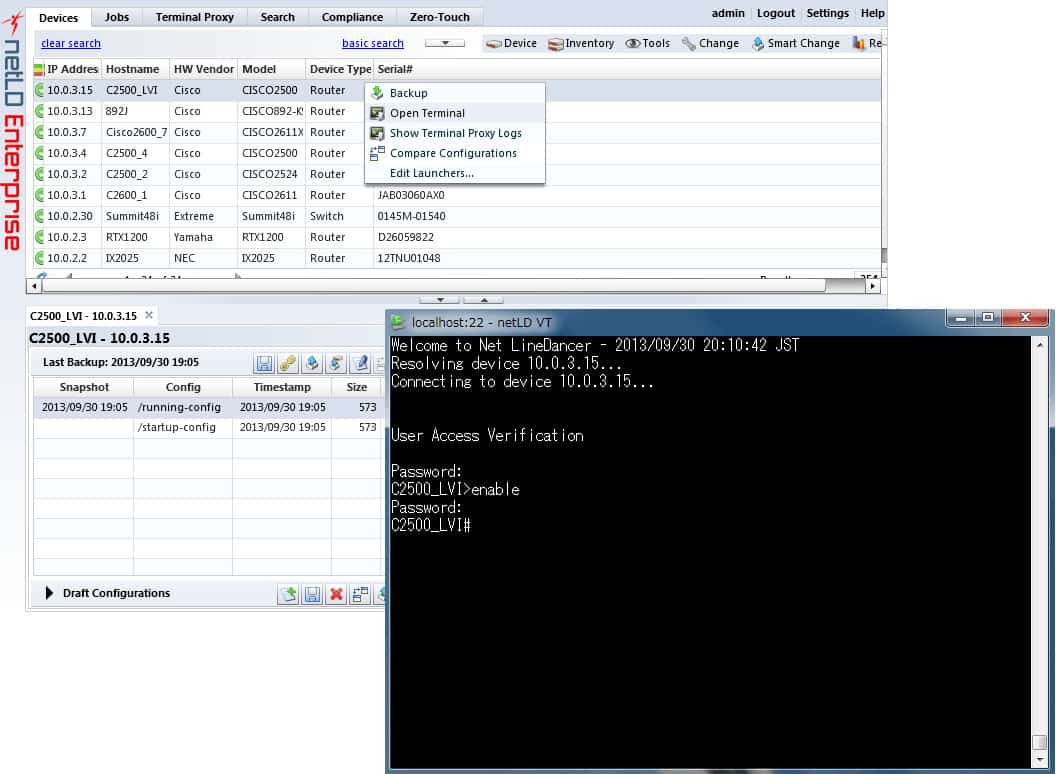
Aimed at large-scale networks with multi-tenancy address space, LogicVein’s Net LineDancer is largely dedicated to device configuration and hardware asset management. LogicVein produces Net LineDancer in two editions; NetLD Enterprise for IT departments and NetLD Managed Service Providers for use by MSPs. Both versions are identical but the MSP edition separates the data for each MSP client.
Key Features:
- Network Asset Management: Focused on network hardware
- Asset Discovery: Generates a network inventory
- Mass Updates: Issue a command from a central console and get it sent to all devices
Why do we recommend it?
LogicVein Net LineDancer stresses the necessity to coordinate the activities of network device configurations. The system has been around since the early 2000s, and its strategy has recently become more noticed as Zero Trust Architecture has emerged, which requires ACLs to coordinate traffic flows for security microsegmentation.
Net LineDancer can automatically generate hardware inventory reports with full asset reporting to help aid in asset management on network assets. This focus on large-scale asset management is a big part of Net LineDancer. Combining this with regular reporting and analytics can help administrators gain an edge on hardware life cycles and change management tracking. These tracking features are largely hardware-based.
Net LineDancer’s main strength comes in its ability to scale, thanks to its use of smart bridges to support multi-tenancy address configurations. Controlling subnets separated by address space using one centralized application is made easy with Net LineDancer.
Net LineDancer is mostly focused on providing administrators a straight-forward device configuration and hardware asset management platform to work with on large or complex networks.
Who is it recommended for?
You would particularly benefit from Net LineDancer if you are trying to implement microsegmentation. The tool is offered in two flavors; one for IT departments, called NetLD Enterprise, and NetLD Managed Service Providers for MSPs. The company now also produces ThirdEye, which is a full network monitoring system.
Pros:
- Suitable for Large Networks: Easily manages 100,000 devices
- Stores the Desired Configuration: Compares current configuration to the ideal and updates it if it is different
- Multi-Tenanted Architecture: Suitable for managed service providers
Cons:
- Software Package for Windows Server or Linux: Not a cloud-based SaaS platform
It features all the standard NMS features, including automated changes and real-time change detection that will work across the entire network. You can download a 30-day trial on their site.
6. Infoblox NetMRI
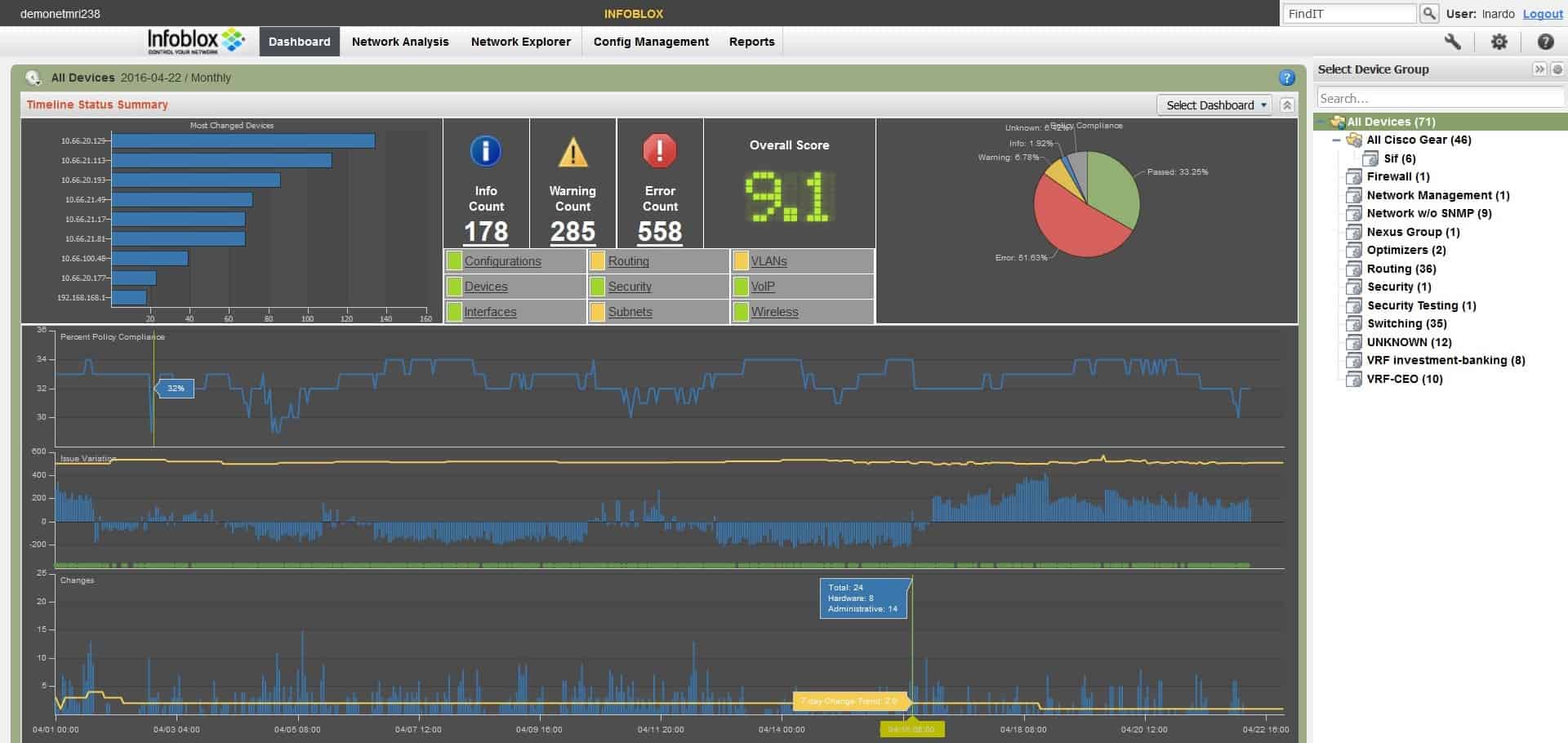
Made by Infoblox, NetMRI is a network configuration and analysis application with mobile integration. Designed to provide a high level of security to large-scale networks, NetMRI can be used for a wide range of network tasks, including automated compliance assessments and non-configuration data analysis.
Key Features:
- Automatic Discovery: Creates a network inventory
- Security Policy Implementation: Guides the creation of an ideal configuration
- Mass Apply: Rolls out designed configuration to all devices
Why do we recommend it?
Infoblox NetMRI is a network management package that includes a network device configuration management unit. The full package can be used for onboarding new devices and it maintains an inventory that tracks the lifecycle of each device, alerting when one has aged out of its depreciation calendar and should be replaced.
With several tools to aid in multi-vendor and virtual routing, NetMRI shines in complex networking environments. It’s able to scan connected assets for configuration and compliance issues proactively, helping to stop potential issues before they start.
NetMRI also supports mobile access, with a large portion of its monitoring and configuration controls available from the convenience of a mobile device. It can locate device locations, browse network inventory, and control connections all from a mobile platform.
As network management software, NetMRI also features all the standard configuration options. Automatic network detection and audits, configuration analysis, and configuration backup are all found in NetMRI. Its search and analysis suite also helps locate correlations between network problem areas to help diagnostics.
Change automation and configuration deployment, along with automatic network discovery and topology mapping round out NetMRI’s list of features.
Who is it recommended for?
This tool runs on top of VMware. It is a system that is designed for use by very large businesses with complicated networks. However, you can get it on a 60-day free trial, so it might also be a good idea for mid-sized businesses to take a look at it cost-free.
Pros:
- Change Tracking: Regularly scans each device for divergence from the standard configuration
- Wipes Out Changes: Reapplies the approved configuration where necessary
- Performance Analysis: Feedback on operations
Cons:
- Only Runs on VMware: You need to have ESXi, Workstation, or Fusion
NetMRI will lend its strengths to complicated networking environments with many connected nodes that need constant upkeep and analysis. You can download and evaluate NetMRI from their website.
7. SolarWinds Network Configuration Manager
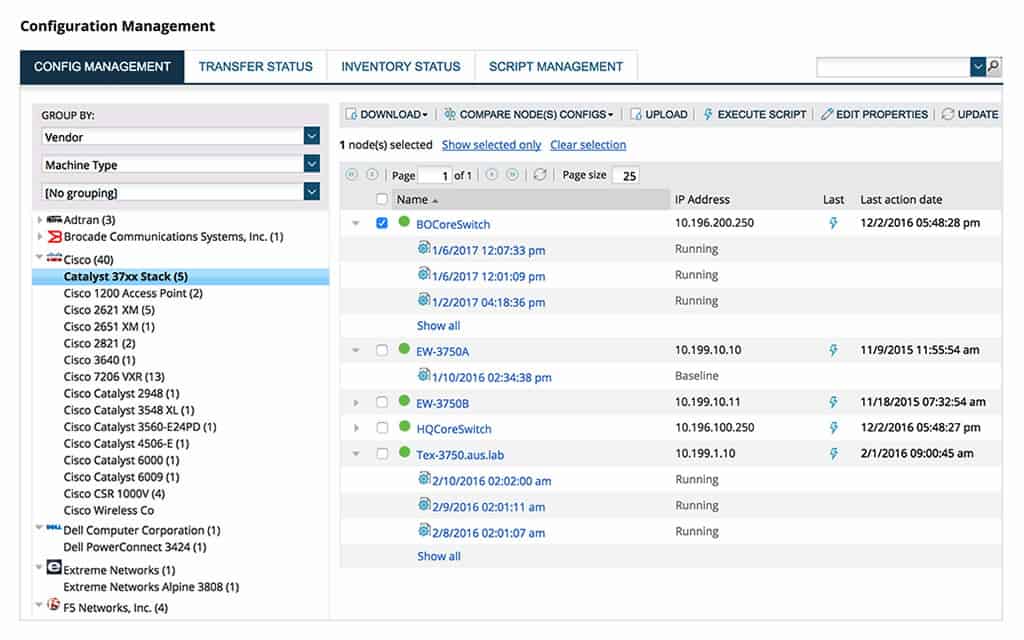
SolarWinds Network Configuration Manager aims to be the total package for network management. Not only does it include robust configuration options, it introduces useful asset management features that can be used to monitor hardware life cycle and other ITAM tenants.
Key Features:
- Device Discovery: Makes frequent network scans
- Copies Device Configurations: Takes an image
- Restores Official Configuration: Overwrites the device settings with the backed up image
Why do we recommend it?
SolarWinds Network Configuration Manager is a great combination of configuration analysis and protection services. You can use this tool to tighten up security by examining the settings and your network devices and improving security. You then apply those settings and take an image for backup. The tool will restore that official configuration if any change is detected.
Equipped with multi-vendor server monitoring, SolarWinds software is dynamic enough to fit into a wide range of networking environments, including those that have multiple hardware vendors in their ecosystem. A seamless change between managing Cisco, HP, and other devices from one centralized piece of software, with full administration access control to provide an easy security solution for hardware access. Automatic network discovery and asset mapping help actively monitor both network topology and hardware life cycles.
Automated configuration backup process and deployment makes restoring devices a simple, worry-free process, and network-wide vulnerability scanning helps to ensure devices are compliant with the National Vulnerability Database. Robust reporting and analysis help spot problem areas before they become an issue.

Full integration with both Cisco ASA and Nexus devices means SolarWinds Network Configuration Manager can make full use of the unique advantages those devices offer large networks.
SolarWinds Network Configuration Manager covers all aspects of device configuration management. After discovering and logging all devices, the software enables network managers to create one standard configuration per device type, make, and model, roll that out, backup the settings, and reinstall that image if any unauthorized configuration changes occur
Who is it recommended for?
Small businesses won’t need this tool because it is best suited to large organizations that have one or more large networks to manage and cannot keep track of every device manually. This software runs on Windows Server so if your site is all Linux, you won’t be able to run it.
Pros:
- Enables Device Standardization: Creates a backup for each make and model
- Fast Onboarding: Sets up a new device by applying a configuration image
- Compliance Management: PCI DSS, HIPAA, SOX, DISA, and FISMA
Cons:
- On Premises Only: No SaaS version
SolarWinds Network Configuration Manager provides an all-in-one NMS solution for networks of various sizes. It’s easy to use, has an intuitive GUI, and gives administrators the tools they need to manage even large-scale networks effectively. Visit their site to download a 30-day free trial.
8. LibreNMS with Oxidized Add-on
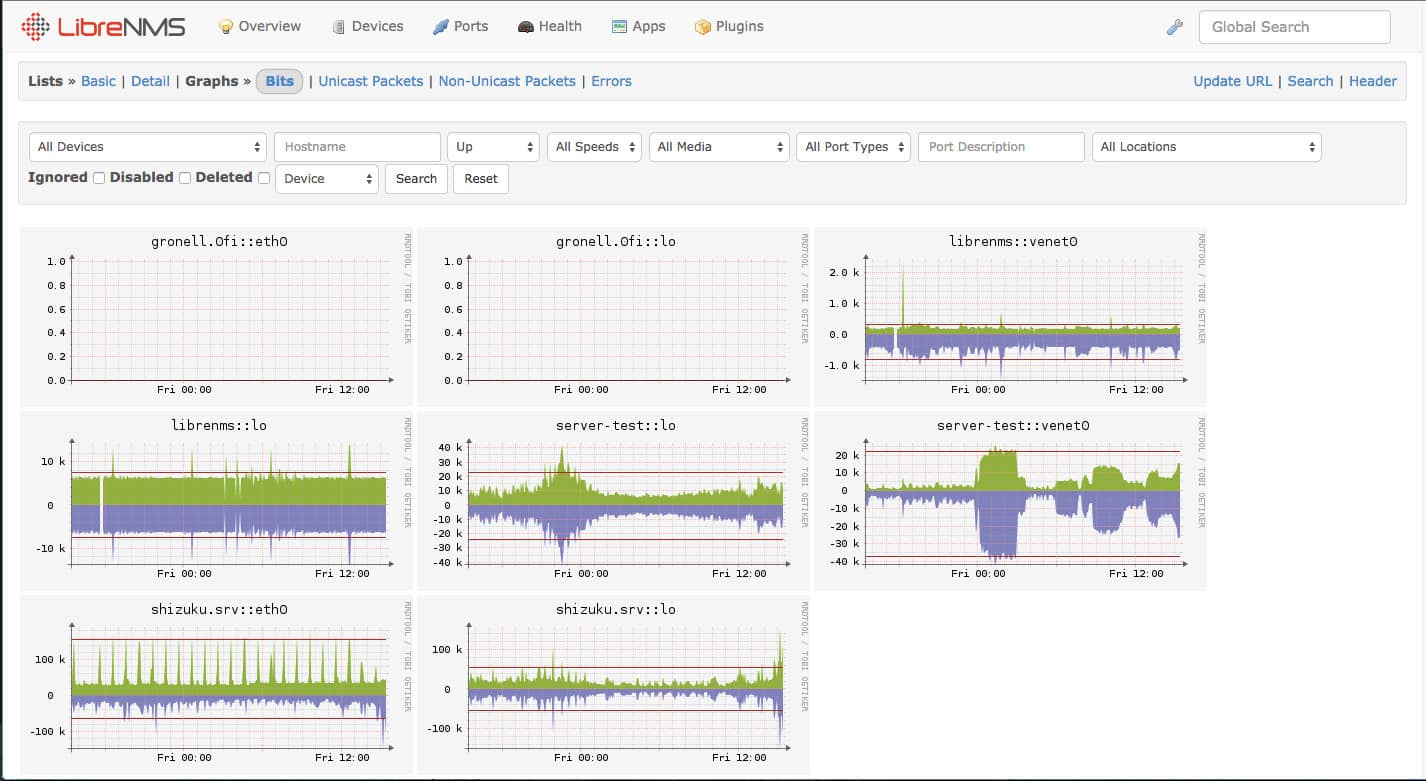
The first open-source solution on our list, LibreNMS is available via GitHub repository for downloading and editing. Don’t let the free nature of LibreNMS fool you, it’s a fully-featured NMS solution used by many organizations.
Key Features:
- Extension for Configuration Management: A free tool
- Device Discovery: Provided by LibreNMS
- Backs Up Device Configurations: Takes a snapshot of each device
Why do we recommend it?
LibreNMS is a great option for network managers that don’t want to pay for network monitoring software. However, it is a little time consuming to set up. The Oxidized add-on provides network device configuration management functions. If you have worked out how to get LibreNMS working you won’t have any difficulty installing the add-on.
We’ve listed Oxidized along with LibreNMS to provide an integrated configuration backup solution. LibreNMS is designed to be used alongside Oxidized with limited setup. This provides LibreNMS users a simple way to do both configuration backup and deployment.
LibreNMS as a standalone package that features automatic network discovery across a wide range of protocols, customizable alerts, data collection, automatic LibreNMS updates, and even an iPhone/Android app. There’s a wealth of customization available in LibreNMS, and that’s largely attributed to its open-source nature.
This functionality isn’t without its own downsides, however. LibreNMS can struggle at scale and has almost no support to speak of. It has enough documentation and is used widely enough to be able to find answers on your own, but it’s not for the faint of heart or those looking for a fast, ready out-of-the-box solution.
Still, for more experienced administrators or those not afraid to get their hands a little dirty, LibreNMS solutions offer a huge amount of flexibility. Another plus is that it’s entirely free and will always be open source. It can be paired with a huge number of open-source plugins to provide almost any functionality you may need for your network.
Who is it recommended for?
LibreNMS is a competent network management system but it doesn’t provide a professional support package, so large businesses won’t be interested in it. It is probably a good fit for a mid-sied business that wants to save money and has a fully qualified network manager on staff.
Pros:
- Free System: LibreNMS, Oxidized, and the extension that links them are all free to use
- Runs on Linux: Not available for Windows
- Options for Automatic Security Controls: Create your own script to compare configurations to the backup versions
Cons:
- Requires a Lot of Set Up: Not an off-the-peg tool
This potential for adaptability and no cost of entry earn it a place on this list. Find out more about integrating Oxidized into LibreNMS from the repository.
9. BackBox

Designed to automate tasks normally performed manually, BackBox offers a mostly one-dimensional approach to network management software. It’s a simple but effective tool that can provide all the functionality most users will need in a centralized network control solution.
Key Features:
- Automation Platform: Implements network management tasks
- Script Library: Includes tools to backup device configurations and reload them
- Compliance Management: Logs measures to enforce security
Why do we recommend it?
BackBox is a competent network monitoring and management tool. Its monitoring features compete well with all of the top network performance monitors because it includes network discovery and automatic topology mapping. The management system provides task automation and includes configuration backup and protection.
BackBox’s strong suit is in secure backup and configuration recovery. The BackBox software goes to extreme lengths to ensure each configuration backup is safely stored, verified for authenticity, and double-checked for errors. The attention-to-detail provided by BackBox’s ‘Five-Step Verification’ for each backup ensures corrupted or tampered configuration files never reach the end points on a network.
BackBox also provides real-time inventory reports on connected assets, as well as automatic network discovery. A visual topology map provides an easy-to-use method of exploring and configuring your network, giving you access to most of Backbox’s features directly through the topology map. It’s a creative way to make network management simple, but can understandably become limiting in very large networks.
Task automation gives administrators a good measure of control over their networks, including the ability to create complex task chains for BackBox to execute across multiple devices. Again, BackBox is largely designed around the idea of using automation to make network administrators’ lives easier, and in that regard, it succeeds.
Who is it recommended for?
This package is a good choice for network managers that like to implement a lot of task automation. The setup for these processes can be time-consuming but once it is in place, it will save you and your team a lot of time. It also provides security monitoring.
Pros:
- Device Discovery: Creates a network inventory
- Configuration Store: Apply easily to onboard a new device
- Configuration Restore: Manually restore an archived configuration or set up an automated process
Cons:
- Requires a Lot of Setup: You need to select, adapt, and schedule scripts to get automation
While it may not be the ideal scaling solution for every business, BackBox offers a strong suite of features across multiple vendors and devices. It’s both easy to use and surprisingly flexible, giving it an edge over some of its competitors. You can download a 14-day evaluation from their site.
10. BMC TrueSight Automation for Networks
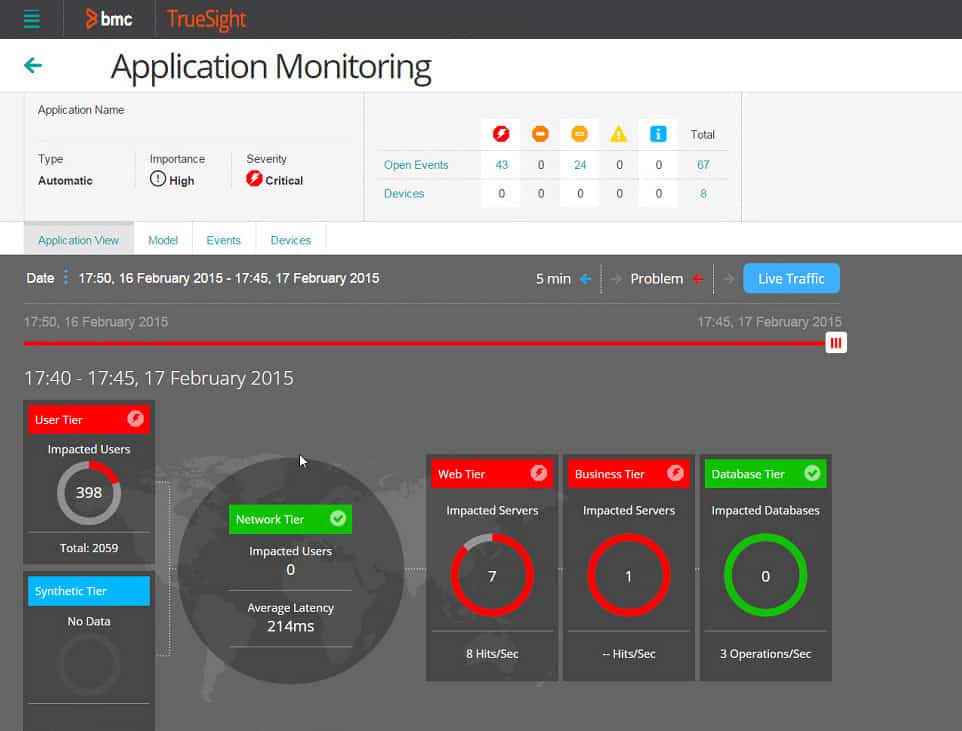
Made by BMC, TrueSight Automation for Networks looks to bring multiple tools together in the BMC product family and marry them with network management. If you’re already heavily invested in BMC solutions and products, it’s hard to argue against using Truesight in your network.
Key Features:
- Vulnerability Scanning: Assess network device security
- Patching: Firmware management
- Centralized Device Configuration: Define security policies and roll them out to devices
Why do we recommend it?
BMC TrueSight Automation for Networks is a task automation system that can be used for configuration backups and change detection. There are many other network administration tasks that can be automated with this package, such as firmware patching and software-linked configuration changes.
A large portion of Truesight’s power and flexibility comes from its ability to seamlessly integrate with other popular BMC products. As an example, Truesight can be set up to integrate with BMC’s change management tools in order to quickly and easily populate a CMDB with attached network assets. For administrators seeking a comprehensive way to combine their ITIL compliant asset management policies with their network, this kind of integration is a godsend. While most CMDB population software has some measure of network discovery built in, the ability to quickly and accurately generate a full network CMDB with a few clicks is on another level entirely.
That being said, these kinds of quality of life features are entirely dependent on using other BMC products. As a standalone piece of software, Truesight still offers a number of features that make it useful as a piece of network management software.
Scanless detection of potential vulnerabilities and templates for regulatory compliance to compare against ensure that big organizations are in accordance with various policies depending on region.
Configuration of both virtual and cloud-based environments give service-oriented networks a versatile option for configuration and administration from a single, centralized platform. Truesight also supports easy device importing from a variety of platforms, including Ciscoworks and HP Network Code Manager.
Rounding out Truesight’s feature list is the ability to auto-generate configuration scripts that can roll back a device’s configuration without the need for a full reboot (in some cases). This is a smart feature that lets administrators make small changes to a device without needing to remove an entire node just for diagnostics.
Who is it recommended for?
This package is very similar to BackBox and anyone looking for a network administration automation package should consider both of these systems side by side. Both of the packages are able to administer WANs and links to cloud platforms as well as wires and wireless systems on-site.
Pros:
- Onboarding: Store configurations in a library and apply one to a new device
- Change Tracking: Scans all network devices to identify configuration changes
- Automated Rollback: Restores authorized configurations if changes are detected
Cons:
- Cloud-Based Package: There is no on premises version
Overall, Truesight is a powerful network tool when combined with other products in its parent companies catalog, and still functions well as a standalone product. Learn more and contact their sales team from their site.
11. rConfig
The second open-source entry on this list, rConfig is a fairly basic network configuration manager with the potential for a lot of customization to fit the needs of small-to-medium-sized networks. As an open-source product, its code is freely available on the internet and getting started with rConfig costs you nothing.
Key Features:
- Free to Use: This is an open-source system
- Support Available: Paid plans with professional support included
- Device Backup: Copies an image of each device’s configuration
Why do we recommend it?
The rConfig is a free tool and has recently been updated to give its dashboard the same quality look and feel of pricey network management tools. This package isn’t as extensive as BackBox and BMC TrueSight, it focuses on configuration management. However, it provides task automation for compliance documentation, configuration backup, and device protection.
rConfig’s biggest strength is in its focused design and open-source nature. Its code repository is fairly well-documented and making changes to the base code is encouraged by the community’s developers. This allows administrators willing to get their hands dirty in rConfig’s code and the opportunity to customize tailor rConfig to fit their specific networking needs.
In terms of performance, rConfig works as a configuration manager ‘out of the box.’ It has bulk configuration deployment and configuration backups, along with a fast configuration compare and search feature to quickly locate differences between deployed or backed-up configurations. Its own built-in task scheduler provides a limited amount of automation in basic tasks.
Systems backups and built-in reporting flesh out rConfig’s list of features. For a small, free, and dedicated configuration platform, rConfig brings a lot to the table but will begin to struggle with larger networks due to its simplicity.
Who is it recommended for?
While many free tools can be less than competent, this recently revamped open-source tool is very impressive. It focuses on network configuration management and does it very well. It is suitable for businesses of all sizes, although large organizations probably would prefer a tool with professional support included.
Pros:
- Compliance Management: Defines security policies and enforces them through configurations
- Change Scanning: Spots device configuration changes
- Change History: Shows device configuration changes over time
Cons:
- Automated Rollback: Only available in the paid version
That being said, sometimes simple is good, and you should take a look at rConfig yourself to see if it has the features your network needs. Here are their installation guides and documentation.
Choosing Network Backup Software: SolarWinds Network Configuration Manager
SolarWinds Network Configuration Manager is one of the best backup tool on this list. No matter what vendors your network is dependent on, SolarWinds Network Configuration Manager has the potential to keep track of the device’s lifecycle. Device monitoring is supported with automatic network discovery to ensure every device on your network is being monitored.
Whether you’re part of an SME or a large organization, we recommend SolarWinds Network Configuration Manager because it is easy to use. The design is so intuitive that there is next to no learning curve once it has been deployed. In the long term, this means that devices stay maintained and minimizes the chance of devices failing due to poor maintenance.
Network Configuration & Backup FAQs
How often should automated network configuration backups happen?
Your configuration should be backed up whenever you make a change to the settings of a device. Automated systems should perform this backup automatically and restore the authorized settings whenever unauthorized changes are made.
Why do network engineers prefer NCM automation to manage network configuration and compliance?
Automation is always preferable for routine tasks because it removes the human failures of forgetfulness and accidental errors. Automated configuration management prevents accidental or malicious changes to device settings and it also makes the rollout of a standard configuration easier and faster.
What are the reasons to back up the configuration of a firewall?
Backing up the configuration helps you solidify complicated complications of settings so you don’t have to go through the whole exercise again in case of accidental change. Firewall settings are targeted by hackers, so an automated network configuration monitor can keep the system secure by reloading stored configurations whenever unexpected changes are detected.