As your network grows, so does the time administrators spend managing policies across each device. From firewalls to switches and everything in between, this can take a considerable amount of time in an enterprise environment
Here is our list of the best Network Security Policy Management tools:
- ManageEngine Firewall Analyzer EDITOR’S CHOICE This tool helps you formulate a security policy, then implements it by interfacing to firewalls and prevents tampering with firewall rules. Available for Windows Server, Linux, or AWS. Access a 30-day free trial.
- Site24x7 Network Configuration Management (FREE TRIAL) Vulnerability scanning, configuration backup, and tamper prevention for network devices. Delivered from the cloud. Start a 30-day free trial.
- AWS Firewall Manager Offers NSPM for AWS environments.
- Netwrix Change Tracker Weaves NSPM with vulnerability management.
- Cisco Defense Orchestrator Solid option, especially for domains that rely heavily on Cisco hardware.
- SolarWinds Network Configuration Manager Provides robust security and configuration management across on-premises and hybrid cloud environments.
- Trellix ePolicy Orchestrator Offers over 150 integrations, does a good job consolidating multiple security tools into one dashboard.
- Indeni Focus on large-scale infrastructure management – includes features like licensing expiration alerts.
In the article, we’ll explore the best Network Security Policy Management (NSPM) tools sysadmins can use to cut down the time they spend managing their infrastructure and make life a little easier.
What does a Network Security Policy Management Tool do?
Network security policy management tools help administrators manage devices’ configuration and security settings across their network from a single dashboard. As you can imagine, software like this is potent, especially when networks support thousands of end-users.
NSPM tools can also provide a method for documenting policy changes, auditing network security, and automating policy changes. In some cases, administrators can deploy hardware and configure it through the NSPM tool remotely.
Why do you need an NSPM Tool?
Some network monitoring tools share a few characteristics of an NSPM but don’t indeed encompass all the features needed to be classified as one. For example, authentic NSPM tools must manage network and firewall configurations, provide an audit log of policy changes, and support frameworks that help meet compliance standards.
In addition to those features, look for products that make it easy to scale your management efforts quickly. For example, automated configuration management can save config files and push them out over the network to ensure all new devices are set up correctly.
Looks for software that supports intelligent alerting for your devices. For example, some NSPM tools can be configured to alert administrators when a policy or setting is changed. This not only helps protect you from misconfiguration but can also alert you of an account takeover or malicious insider activity.
Lastly, NSPM that supports auditing can help technicians cut down on their time troubleshooting issues. A single misconfiguration can cause a wave of helpdesk tickets, especially in a larger environment. By reviewing an audit log of recent changes, NOC technicians can quickly rule out that an internal shift triggered an issue.
With all that said, let’s take a look at our top 6 choices for the best network security policy management tools.
Best Network Security Policy Management Tools
Our methodology for selecting a network security management system
We reviewed the market for network security management tools and analyzed the options based on the following criteria:
- Assistance for the creation of security policies through wizards and templates
- Automatic implementation of security policies on network devices
- The ability to interface to devices produced by all the major brands
- Options for managing device security on remote sites
- Data protection standards compliance
- A free trial or a money-back guarantee that creates an opportunity to assess the tool without risk
- Value for money offered by strong security that will protect the business without costing the earth
Using this set of criteria, we looked for network device management systems that can help create strong security policies and implement them throughout the business. We particularly looked for systems that can extract activity data, providing logging and reporting for data protection and compliance reporting.
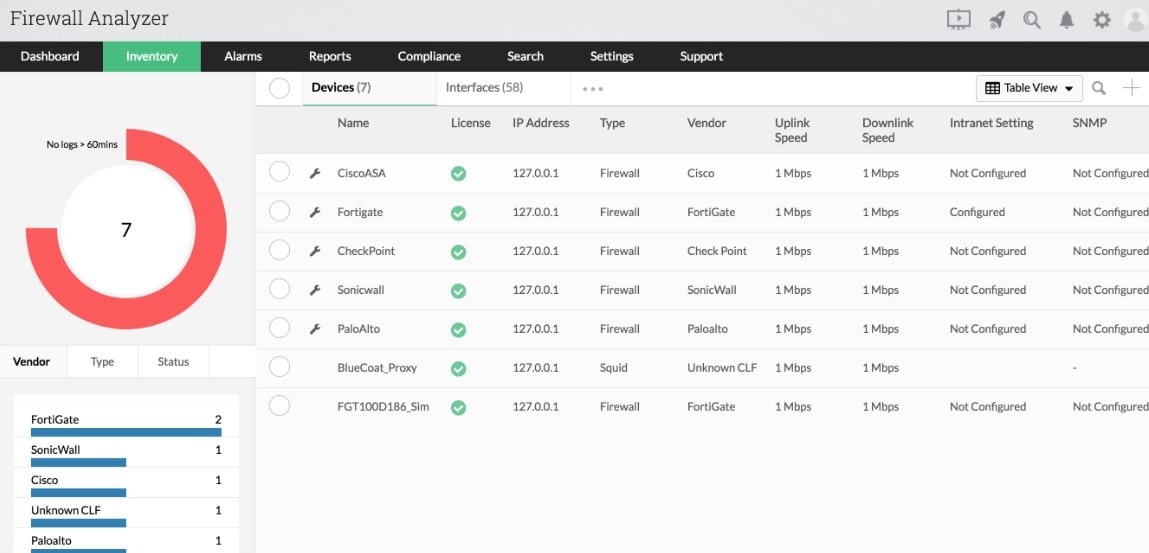
1. ManageEngine Firewall Analyzer (FREE TRIAL)
ManageEngine Firewall Analyzer is a tool that supports the creation of a network security policy. It then implements that policy by updating firewall settings and it follows on by supervising activities on the network and gathering status data from firewalls.
Key Features:
- Supports the Creation of Network Security Policies: Set up rules in the console
- Rolls Out Security Policies: Interprets policies into firewall rules
- Tailored to Standards Compliance: Follow data privacy standards
- Firewall Coordination: Adjusts endpoint, device, and network firewalls
Why do we recommend it?
ManageEngine Firewall Analyzer addresses the key security appliance on your network. This tool performs configuration protection through a backup and restore service that automatically detects unauthorized changes. It also provides a security policy implementor and a security event reporter. This is a software package for Windows Server, Linux, or AWS.
The tool interprets the network security policy into firewall settings. The system can interact with firewall provided by all of the major network and security tool producers, including Cisco, Fortinet, and Juniper Networks. The Firewall Analyzer then keeps tabs on those configurations, guarding against unauthorized changes. Should any occur, as well as noting the malicious event, the Firewall Analyzer restores the proper configuration.
While gathering data from firewalls, the Firewall Analyzer collects logs. The data it collates is then scoured for user activity. The system profiles each user identity, looking for insider threats and account takeover. The recording of network activity forms the basis for compliance reporting, following the PCI DSS, ISO 27001, SANS, NIST, and NERC CIP standards.
Who is it recommended for?
A small business that only has one firewall won’t need this tool. The Standard and Professional editions of the package will manage up to 60 devices and the Enterprise edition will manage 1,200 devices. Those numbers give you an idea of the sizes of networks that this tool is intended for.
Pros:
- Intrusion Detection: Scans traffic for anomalies
- Configuration Protection: Blocks unauthorized changes to firewall settings
- Performs User Behavior Analysis: Identifies insider threats and account takeovers
- Compliance Reporting: PCI DSS, ISO 27001, SANS, NIST, and NERC CIP
Cons:
- No SaaS Version: A software package for Windows Server and Linux or a service on AWS
ManageEngine Firewall Analyzer is available for installation on Windows Server and Linux or it can be added to an AWS account from the Marketplace. You can assess the Firewall Analyzer with a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Firewall Analyzer is our editor’s top pick for the best NSPM tool because administrators can easily create and implement a network security policy. All that they have to do is tweak the firewall settings, and the tool automatically oversees all activities and collects data from firewalls for further analysis. With this tool, organizations can also ensure compliance with the required standards and frameworks. Due to this ease of use, the ability to identify security threats, and compliance support, we highly recommend it.
Download: Get a 30-day FREE trial
Official Site: https://www.manageengine.com/products/firewall/
OS: Windows and Linux
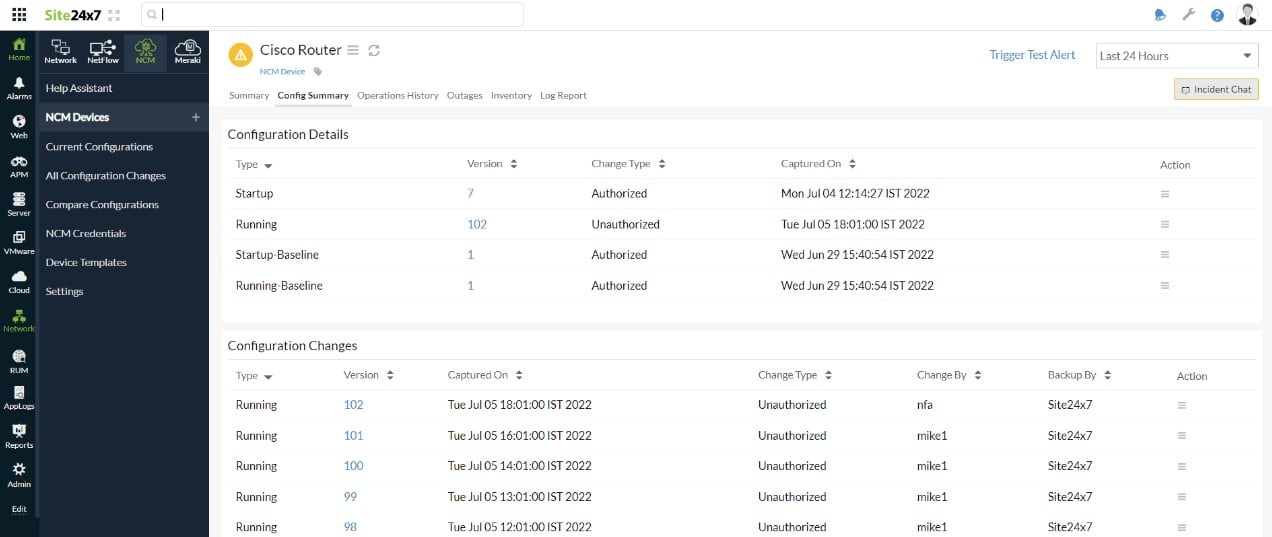
2. Site24x7 Network Configuration Management (FREE TRIAL)
The Site2x7 cloud platform provides system monitoring and management modules and the Site24x7 Network Configuration Management module is one of these. The platform includes a network discovery service, which supports the Network Configuration Management system by providing a list of devices to scan.
Key Features:
- Vulnerability Scanning: Looks for configuration changes
- Encrypted Backup Repository: Stored for security
- Reverses Unauthorized Changes: Restores the backed-up image
Why do we recommend it?
Site24x7 Network Configuration Management offers a cloud-based console that is accessed through a Web browser. In that screen, the network administrator can see a list of all devices. The Network Configuration Manager works down the list, scanning for available firmware updates and installing them automatically. The tool takes an image of each device’s configuration and then stores it on the Site24x7 cloud server.
The Site24x7 configuration backup service supports two security functions. The first of these is a defense against attack. If the settings of a device have been changed inexplicably, the Network Configuration Management system will restore the original. The other benefit is a business continuity service. If one or all devices need to be replaced, the new equipment can be set up quickly by applying the configuration images.
The Network Configuration Management system is fully automated, saving the valuable time of network managers and removing human error in configuration maintenance. The tool can protect switches, routers, hardware firewalls, and wireless access points.
Who is it recommended for?
This package is suitable for all sizes of businesses. Site24x7 produces many editions and nearly all of them include the Network Configuration Management feature. Plans are sized and priced for small businesses and larger companies pay supplements to get more capacity in each of the modules. Nearly all of the plans will cover just one device, but the MSP edition’s base package covers five.
Pros:
- Good for Multi-Vendor Environments: Communicates with devices from many different providers
- Watches Over Network Devices: Security protection for switches, routers, firewall appliances, and wireless APs
- Storage Included: A cloud repository for configuration images
Cons:
- Watch Out for Extra Costs: Base plans are sized for very small businesses
Site24x7 Network Configuration Management protects network devices from many suppliers, including Cisco Systems, SonicWall, Citrix, Dell, and Aruba. You can assess the Site24x7 platform by accessing a 30-day free trial.
3. AWS Firewall Manager
For organizations that invest heavily in AWS infrastructure, the AWS Firewall Manager can help push out policies to devices and automatically replicate updates across all other devices. While this tool doesn’t offer much outside of the AWS ecosystem, those who rely on AWS Organizations and other Amazon cloud-based services can use this product to provide NSPM.
Key Features:
- Security for AWS Systems: Hosted on AWS
- Create Global Policies: Cover all your accounts consistently
- Design Service-Specific Settings: Tailor the firewall options per service
Why do we recommend it?
AWS Firewall Manager is an interesting option for businesses that use cloud firewalls, particularly those provided by AWS. The system can manage third-party firewalls, so it isn’t limited to monitoring AWS firewalls, which are AWS WAF, AWS Network Firewall, AWS Shield, and Amazon Route 53 Resolver DNS Firewall.
AWS Firewall Manager supports nearly all AWS products and services and allows you to enable group rules, policies, and configuration changes in a single place. Once those policies are set, they can automatically be deployed across your entire infrastructure.
AWS Firewall manager does an excellent job at allowing you to push changes globally while still maintaining granular control over specific devices your wish to operate differently. For example, you can drive a global security policy change but easily make an exception for your development environment if needed.
One of the best features of this product is its autoconfiguration settings. Newly created resources and devices can automatically inherit your latest set of global configurations. You can also use this same methodology to meet compliance requirements quickly. For example, to meet US Department of Treasury’s Office of Foreign Assets Control (OFAC) regulations, you could deploy a rule to block embargoed countries across your environment.
Who is it recommended for?
The ability to implement a central list of security policies through many firewalls from many different providers sounds great but its capabilities are only ever going to be fully exploited by very large businesses. The pricing for this service is scaleable with a price per policy.
Pros:
- Autoconfiguration Across Multiple Accounts and Services: Handy for those who don’t have a plan
- Simple Integration into AWS Products: Part of the platform
- Apply Common Security Settings to All Services: Can quickly implement global policy changes
Cons:
- Limited to AWS Environments: You can’t extend its protection to your own site
4. Netwrix Change Tracker
Netwrix Change Tracker provides NSPM through a series of services and combines this offering with security options such as breach detection, file integrity monitoring, and vulnerability management. Additionally, the platform supports multiple deployments, including on-premises and hybrid cloud environments.
Key Features:
- System Hardening: Vulnerability scanning
- Configuration Change Blocking: Stores a backup of each device’s configuration
- Threat Intelligence: Warnings for hacker campaigns
Why do we recommend it?
Netwrix Change Tracker examines the configurations of all of your network devices, such as switches, routers, and firewalls. This tool is a worthy rival to the SolarWinds system because it isn’t limited to firewalls. The package goes further though, because it also checks on the configuration of endpoints.
Change Tracker aims to provide security through system integrity, with a significant part of policy and configuration management. Device configuration and files can be continuously monitored through the platform, allowing users to push out changes and recover to previous states. In addition, users can set automated planned change rules to revert to a golden image if unauthorized modifications are detected.
The platform help organizations minimize their risk of attack and meet compliance standards through continuous configuration monitoring paired with CIS-based recommendations. This combination lets businesses perform vulnerability mitigation while also managing their configuration policies.
The platform does a great job at assisting sysadmin to make informed policy changes by offering custom security recommendations based on best practices and compliance standards. These recommendations can also alert admins to configuration drift and failed policy updates.
Breach protection helps raise the alarm to unauthorized changes but only does so when it identities changes that are malicious. This is a great feature, as many systems can alert administrators to changes but fail to read the context behind the change.
Change Tracker accomplishes this by using behavioral analytics and baseline monitoring to provide a layer of threat intelligence behind config changes. Additionally, since breach activity is much different than a failed policy update, users can set custom automation and alerts to respond to breach incidents specifically.
Who is it recommended for?
This is a system-wide configuration management system that centralizes the enforcement of security policies across all equipment plus virtualizations and containers. The tool is more interesting to large businesses than small enterprises. It is particularly interesting for companies that need to comply with data security standards.
Pros:
- Combines NSPM with Proactive Security Features: Logging and auditing for compliance
- Leverages Machine Learning to Detect Breaches and Account Takeovers: Looks for illogical sequences of actions per account
- The Interface is Easy to Use: Well ordered and laid out
Cons:
- No Price List: Must contact the sales team for pricing and demo
5. Cisco Defense Orchestrator
Cisco Defense Orchestrator is designed to make managing Cisco firewalls easy across on-premises networks and cloud environments. Currently, the platform can manage security policies across multiple environments, including Cisco Adaptive Security Appliance (ASA), Cisco Firepower, Meraki MX, and Amazon Web Services (AWS).
Key Features:
- Cloud-Based System: Controls Cisco and AWS assets
- Device Onboarding: Use stored configurations
- Configuration Locks: Backup settings and overwrite unauthorized changes automatically
Why do we recommend it?
Cisco Defense Orchestrator is becoming more important because of the rise of microsegmentation. That strategy needs to be managed across switches and routers and this Cisco system can also extend security policies across WANs and hybrid networks that include cloud services. The service is controlled through a cloud-based console.
The product offers continuous scanning across each environment to monitor the supported devices for changes. Once a device is added to the inventory list, Defense Orchestrator highlights inconsistencies, misconfigurations, and other errors so you can quickly change them. A nice added feature is that the platform can also identify changes that can improve performance, allowing you to enhance your security and network performance in a single solution.
Like other NSPMs, Cisco Defense Orchestrator offers low-touch deployment of new devices. Since the platform automatically identifies new hardware, administrators don’t need to travel on-site or have firewalls shipped to them for configuration.
Firmware updates, image upgrades, and configuration changes can all be easily pushed out per device, per group, or globally. This flexibility is great for larger environments and allows MSPs to customize their settings in a way that can be tailored to each client.
On the backend, Cisco provides detailed insights and alerts based on changes identified across the environment. For instance, the tool can identify ransomware, DDoS attacks, insider threats, and even crypto mining within the network.
Who is it recommended for?
Cisco is a leader in networking technology and the use of device configurations to enforce security. However, its devices have their own command language which takes a long time to learn. This service interprets more natural language instructions into the complicated commands implemented in switches, routers, and firewalls.
Pros:
- Great Support for Environments that Heavily Use Cisco Hardware: The best configuration manager for Cisco customers
- Provides End-to-End Visibility: Offers remediation suggestions
- System Logging: Uptimes and see when changes were last made
Cons:
- The User Guide is Not Very Attractive: Typical Cisco help pages
6. SolarWinds Network Configuration Manager
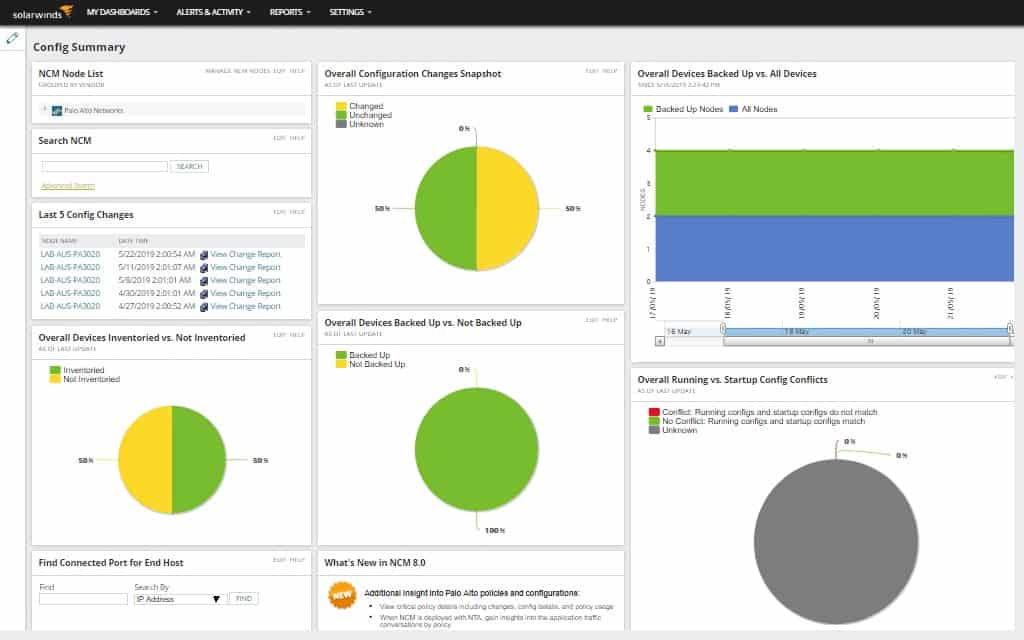
SolarWinds Network Configuration Manager (NCM) specializes in automating the configuration management of devices and gives sysadmin the power to push updates or roll back and restore devices to a particular state.
Key Features:
- Creates Standardized Device Settings: Access devices through the SolarWinds console
- Stores Configuration Images: Backups
- Continuous Network Device Polling: Monitors for unauthorized device settings changes
Why do we recommend it?
SolarWinds Network Configuration Manager is able to manage all of the settings of your routers and switches. That includes security measures such as access control lists and password encryption standards. This tool includes a compliance auditing feature but its best security package is its scans for unauthorized configuration changes.
Visually the platform is easy to navigate and makes excellent use of widgets to allow administrators to customize their view or build shared dashboards for network operation centers. I particularly like the bold use of color NCM uses to help key insights stand out over other events.
SolarWinds NCM can automatically crawl a network through auto-discover and build a live inventory list of all your managed devices. Information such as vendor, serial number, and firmware version is easily accessible from a single place. This feature can be used as a form of inventory management in conjunction with your NSPM strategy.
I like that that the platform aims to keep things simple without taking away any features or tools. For instance, if you think a configuration change has caused an issue, you can use NCM to view a side-by-side comparison of your set policy versus what a device has currently. Furthermore, these changes are automatically highlighted and can be reverted quickly.
This view also helps you read into the context of the change, which is just as important as fixing it. Understanding the nature of what was changed and why you can take the correct action to stop it from reoccurring. For example, changes can be made by malware, misinformed staff, insider threats, or simply a lousy policy update. These changes can be paired with alerts, allowing you to always stay on top of the most impactful changes across your network.
NCM helps you stay proactive by providing a simple framework for backing up configurations and maintaining a collection of configuration options to restore to. The platform supports hundreds of different vendor devices that can all be managed from a single place. You can quickly see devices with issues from the configuration management tab—understanding and pushing out changes to that device from a known-good backup file.
The platform offers automated configuration backup that takes snapshots periodically. You can use this to track changes and compare them to your “golden standard” image. This also comes in handy when a device inevitably needs to be replaced. Rather than sending a tech on-site, a staff member can simply plug the device into the network. NCM can automatically identify the device, catalog it, and allow you to push your saved config file to it.
Who is it recommended for?
This solution is suitable for large businesses that have many network devices to manage. Growing mid-sized companies would probably also be interested in this system. However, it is a little too expensive for small businesses that might have few network devices. This is a software package that runs on Windows Server.
Pros:
- Built for Medium to Enterprise-Sized Networks: Improves technician efficiency
- Automatic Discovery of New Devices: Provide templated health reports
- Configuration Management: Backup and restore
Cons:
- No SaaS Option: This is on-premises software for Windows Server
SolarWinds Network Configuration Manager starts at $1687.00 and is available through both subscription and perpetual licensing. In addition, you can test out NCM for yourself through a 30-day free trial.
7. Trellix ePolicy Orchestrator
Trellix ePolicy Orchestrator strives to provide a single web-based platform for all your security tools and configuration management options. Currently, the Trellix ePolicy Orchestrator supports on-premises environments, AWS cloud deployments, and even a SaaS version managed entirely by McAfee staff.
Key Features:
- For Hybrid Systems: On-premises and AWS protection
- Run it Yourself or Get Help: Managed security service option
- Communicates with Network Devices: Implements through firewalls
Why do we recommend it?
Trellix ePolicy Orchestrator focuses on endpoints rather than networks. It can also coordinate the activities of other Trellix products to tailor them to specific security policy rules that are defined in the ePolicy Orchestrator. Trellix is phasing out the on-premises option for this tool, encouraging users to migrate to the SaaS version.
Visually McAfee does a great job at providing a clean and clutter-free dashboard that is easy to use. Pre-configured reports easily display metrics like unresolved threats, software status, and recent configuration changes in a single place. In addition, devices can be added via auto-discovery or manually, giving your organization more control over how devices are collected. This option can be helpful, especially in a BYOD environment.
The NSPM works by embracing the native policy and security controls across each vendor and consolidates that access to a single dashboard. This allows you to control everything from Microsoft Defender policies to firewall NAT rules in a single place. This same technique is also used to provide infrastructure maintenance and management at scale.
The platform does an excellent job of highlighting key issues while suggesting recommendations and helping sysadmin improve their workflows. In addition, the platforms come with several pre-configured automated responses designed around specific compliance standards and general best practices.
This lets you get started quickly with the platform without spending hours building rules from scratch. While I am not a fan of McAfee endpoint antivirus, I have to say I was impressed by the quality and ease of use that ePolicy Orchestrator brought to the table.
Who is it recommended for?
Trellix is a tricky brand right now. The company was formed by a merger of McAfee FireEye with some divisions spun off into other companies. Now many of the McAfee tools are in transition. For example, the ePolicy Orchestrator has dropped its functions for network security policy management.
Pros:
- Attractive Tool: Great visualizations in the central dashboard
- Self-Populating Dashboard: Supports auto-discover as well as manual device collection
- Coordination with Third-Party Systems: Offers over 150 integrations into different platforms
Cons:
- No Free Trial: You can get a demo
8. Indeni
Indeni focuses on providing automated infrastructure management and security management for on-premises hardware and the cloud for AWS and Terraform environments. The platform is designed to help fix everything from configuration issues to non-compliance in a single platform.
Key Features:
- Security for Hybrid Systems: Protects on-premises, AWS, and Terraform systems
- Availability Checks: Alerts for lost devices
- Configuration Recommendations: Vulnerability assessments
Why do we recommend it?
Indeni is a compliance management system that automatically imposes controls through device configuration management. This system operates in a similar manner to a vulnerability scanner because it will assess the security of the configurations of each of your network devices, recommend changes, and then defend them against tampering.
Indeni can also detect systems and environments that are at risk of low availability. This is a good feature for managed service providers or data centers that support many additional customers. The platform can make suggestions that can improve your potential uptime and avoid any unnecessary downtime from a breach or misconfiguration. The platform also does an excellent job at making insights searchable and organizing historical data in a way that makes it simple to demonstrate compliance and review security issues.
Who is it recommended for?
This is a great tool for automatically translating compliance requirements into network device settings. So, it is a good service for network managers that are not fully qualified in cybersecurity strategies. The output that this tool generates for compliance reporting is outstanding.
Pros:
- Easy-to-Use Interface: Coordinates third-party tools
- Can Identity Non-Compliance: Scans all device security tools
- Supports High Availability: Great for MSPs and data centers
Cons:
- No Price List: You have to contact the sales department
Which Network Security Policy Management Tool is right for you?
We reviewed our top six choices for NSPM tools, but which is the best tool for you? We found SolarWinds Network Configuration Manager to provide the best onboarding experience, ease of use, and ability to automated configuration and security settings with the least amount of issues in almost all cases. In addition, unlike other NSPM tools, SolarWinds NCM supports a vast range of devices and multiple cloud and hybrid cloud configurations.
The one exception is for organizations that own minimal infrastructure and operate almost entirely in AWS. In that case, AWS Firewall Manager offers NSPM services seamlessly across all AWS accounts. The caveat is that AWS Firewall Manager is limited only to AWS.
Do you automate your security policies and configurations? If so, let us know what tools you use for the job in the comments below.
Network Security Policy Management FAQs
What is network security policy management?
Network security policies are the methods that you use to protect your IT system by hardening all of your network devices and implementing traffic filtering at firewalls and routers. The implementation of these security rules requires the coordination of the settings on many devices, therefore, the whole process is termed network security policy management. For example, you can set up access control lists to block certain types of traffic from moving between zones of trust on your network. The creation of zones of trust is also part of your network security policy.
What are the three types of security policies?
There are three types of security policies that can be implemented for an IT system:
- Program policies
- Issue-specific policies
- System-specific policies
How is security policy made and implemented?
Network security policies can be divided into two categories:
- Internal threat prevention
- External threat prevention
External threat prevention policies implement what is generally understood to be the responsibility of a firewall, which is to block connection requests from outside the network and only allow incoming traffic if it is in response to a request that originated from within the network. Some networks, such as those that include a Web server, need to allow incoming connection requests but only to a specific device or section of the network. In these instances, it is better to conceptually divide the network into zones of trust. Each zone is given a trust rating and then treated as a separate network for the purposes of network security policy management. This alters the definition of which traffic is external and which is internal.