As Industrial IoT (IIoT) takes center stage, there’s a greater focus on securing operational technologies like sensors, generators, industrial robots, Remote Processing Units (RPUs), and more. Organizations are increasingly looking for streamlined Operational Technology (OT) security platforms that can support multiple device types while providing real-time threat detection and compliance. For security teams and industrial operators, selecting the right OT security vendor is driven by these key challenges.
- When you have outdated systems that were never designed with cybersecurity in mind.
- OT networks without real-time monitoring, which can make it easy for threats to move laterally across your Industrial Control Systems (ICS).
- Frequent production halts, safety hazard issues, and regulatory violations.
- Lack of clear incident response procedures.
- Your external vendors and contractors need network access.
The OT security solution you choose must address these pain points, so your organization can enjoy uninterrupted operations.
In this article, we leverage our deep cybersecurity expertise to help you select the best OT security platforms that can safeguard your industrial environments from cyber threats.
Here’s our shortlist of the seven best OT security vendors:
- Forcepoint EDITOR’S CHOICE A cloud-based system that plans and then implements a secure overlay network, integrating underlying infrastructure into a universal addressing, security management, and monitoring system.
- Nozomi Networks Guardian Sensors Discovers and monitors industrial control systems, operation technology, and IoT devices.
- SigaGuard Monitors electrical signals rather than packets for wider monitoring abilities.
- Honeywell Assigns risk scores for easy threat prioritization.
- Kaspersky Industrial CyberSecurity Provides holistic monitoring and end-user education.
- Darktrace Leverages artificial intelligence to secure any protocol or technology.
- Dragos Can be used as a managed service and features 21+ partnerships.
With the stakes so high, OT Security vendors not only have to stop attacks but also have a set of automated procedures to isolate other systems and ensure any damage done can be quickly stopped and reversed.
If you need to know more, explore our vendor highlight section just below, or skip to our detailed vendor reviews.
OT Security vendors highlights
Top Feature
Seamless IT/OT Integration: Integrates IT and OT environments for unified security management
Price
Negotiated price
Target Market
Organizations managing critical infrastructure that require continuous monitoring, network segmentation, and protection against cyber threats targeting OT systems
Free Trial Length
30-day free trial
Additional Benefits:
- Integrates IT and OT environments for unified security
- Inspects and validates data at the byte level
- Integrates with SIEM platforms for centralized monitoring
Features:
- Deep Packet Inspection and OT-specific segmentation
- Lateral movement restriction via strict access controls
- Cloud sandboxing for threat isolation
- Fingerprinting and behavioral threat detection
- SIEM integration
Top Feature
Nozomi Networks Guardian Sensors provide AI-driven threat detection combined with asset visibility and risk analysis.
Price
Negotiated price
Target Market
Energy and utilities, oil and gas, manufacturing, and transportation sectors that rely on ICS and need asset visibility and network security
Free Trial Length
Free demo available upon request
Read more ▼
Top Feature
Out-of-band cybersecurity solution for Operational Technology (OT) environments
Price
Negotiated price
Target Market
Critical infrastructure sectors that need physics-based monitoring to detect process deviations and cybersecurity threats
Free Trial Length
Free demo available upon request
Read more ▼
Top Feature
Comprehensive and customizable cybersecurity solution for OT/ICS networks
Price
Negotiated price
Target Market
Manufacturing, energy, oil and gas, chemicals, and critical infrastructure operators that require end-to-end OT cybersecurity solutions, including threat detection, compliance management, and asset protection
Free Trial Length
No trial or demo disclosed - contact vendor for options
Read more ▼
Top Feature
Native Extended Detection and Response (XDR) platform for critical infrastructure protection
Price
Negotiated price
Target Market
Critical infrastructure sectors that require endpoint security, anomaly detection, and industrial network protection against cyber threats
Free Trial Length
Demo available upon request
Read more ▼
Top Feature
Self-learning AI for unified IT/OT threat detection
Price
Negotiated price
Target Market
Organizations in manufacturing, energy, utilities, and transportation sectors requiring unified visibility and proactive protection across IT and OT infrastructures
Free Trial Length
30-day free trial
Read more ▼
Top Feature
Intelligence-driven threat detection with expert-authored response playbooks
Price
Negotiated pricing
Target Market
Energy, manufacturing, water utilities, and transportation sectors requiring specialized OT threat detection and incident response
Free Trial Length
Demo available upon request
Read more ▼
How is OT Security Different From IT Security?
IT Security heavily focuses on securing information systems, databases, and user access through networks using internet protocol. Traditionally businesses have allowed information in and out of their network through the placement of firewalls that are sometimes paired with a proactive system such as a SIEM.
OT Security is primarily used to secure industrial systems and networks from cyberattacks or internal threats from rogue employees. This industrial IoT usually includes ICS and SCADA networks that may now have internet-facing access to remotely monitor or control physical systems on the plant floor. In the past industrial systems operated primarily on an intranet and did not have connectivity to the outside world.
While IT and OT security may seem similar, they are significantly different. One of the biggest differences is that OT Security covers networks and devices that used to be part of a closed system, and never accessible to the outside world. In IT Security a breach may result in the loss of information, whereas a breach of an industrial system may cause a pipe to burst, or a centrifuge to spin out of control.
As these physical devices become internet-accessible both IT and OT security need to be applied harmoniously in a way that secures the industrial network and ensures no unauthorized changes can be made either internally, or externally.
What Are Some Features Of OT Security?
OT Security has many layers, but most often starts with analyzing the industrial networks’ traffic. From a network perspective, these systems are isolated from everything else, lowering the total volume of network traffic that needs to be inspected and analyzed.
With less traffic, baselines can be created faster and monitors can be set to alert to suspicious activity or changes. Many OT Security vendors use a combination of behavioral analytics and baseline analysis to alert and sometimes even deploy automation to rectify an issue.
For example, these two technologies can detect if specific employees are accessing machines in a way they shouldn’t, or attempting to modify controls they are not authorized to change. If these actions are detected an alert can be sent immediately to a supervisor and their account can be temporarily locked until a more thorough look is taken into the situation.
Much of this automation and monitoring is designed to alert to an attack that may be in its early stages, giving you a chance to stop it before it is completely underway. In addition to this monitoring, many OT Security solutions come with tailored access control solutions that cater to ICS and SCADA systems.
These security features can monitor and directly communicate with industrial control systems allowing for in-depth access control, policy-based rulesets, and reports for auditing. Many of these OT Security vendors have scalable solutions that can secure a few dozen, to a few thousand sensors and industrial machines.
If you’re looking for OT Security vendors it’s important to look for solutions that can be implemented without causing downtime or risking non-compliance. Managing the jump from a closed industrial system to an internet connection one requires a vendor or tool that has the ability to provide IT and OT security convergence seamlessly.
Key Points to Consider Before Purchasing an OT Security Platform
Go beyond the feature lists when looking for the right OT security platform that meets your organization’s environment. Some factors to consider are:
- Threat detection and response speed: Look for solutions with automated threat mitigation that minimize the need for manual intervention.
- Compatibility with legacy systems: Make sure your platform integrates your infrastructure without disrupting operations.
- Network segmentation and access control: Select OT security platforms that offer granular segmentation to isolate threats before they spread across your ICS.
- Real-time monitoring and incident reporting: A good OT security platform should provide real-time dashboards, historical data analysis, and alerts on suspicious activity
- Regulatory compliance: If your industry is subject to strict regulations, choose a platform that meets these compliance requirements. Built-in reporting and audit trails are good-to-have features.
- Vendor support and SLA agreements: It’s a bonus if your vendor offers 24/7 support, clear SLAs, and dedicated security teams that can assist during critical events.
How to Calculate the ROI of OT Security Platforms
Investing in an OT security platform can deliver a strong return if you accurately assess the costs versus the benefits. Below is a structured approach to help you calculate the financial and operational impact of deploying an OT security solution.
Step 1: Establish Your Metrics
Before evaluating different platforms, assess your current risks and costs. Some key metrics include:
- Frequency of cybersecurity incidents in your OT environment.
- Average production downtime per security event and its financial impact.
- Incident response costs, including forensic analysis, recovery, and staff time.
- Regulatory penalties incurred due to compliance failures.
- Equipment replacement costs due to cyber-induced damage or wear from excessive downtime.
- Operational inefficiencies caused by security gaps, such as manual threat monitoring.
Step 2: Know the Cost of the New Platform
Next, calculate the total cost of ownership for the new OT security solution. This includes:
- Software licensing and subscription fees.
- Deployment and configuration costs, including hiring consultants if needed.
- Training costs for IT and OT teams.
- Ongoing maintenance and support fees.
- Hardware costs (if the platform requires additional sensors or appliances).
Step 3: Calculate the Benefits
Estimate how much the new platform will save your organization. Use the following metrics.
- Reducing downtime caused by cyber incidents.
- Lowering incident response costs with automated detection and mitigation.
- Minimizing regulatory fines by maintaining compliance.
- Preventing equipment damage from cyberattacks, extending asset lifecycles.
- Improving operational efficiency, reducing manual security tasks.
Step 4: Put the Numbers Together
Once you have the data, calculate the estimated ROI using this formula:
Annual Savings = (Reduced Downtime * Revenue Lost per Hour) + (Reduced Incident Response Costs) + (Avoided Compliance Fines) + (Security Tool Consolidation Savings) + (Extended Equipment Lifespan Savings)
Total Investment = Sum of costs from Step 2.
ROI (%) = ((Annual Savings – Total Investment) / Total Investment) * 100%
Use Our OT Security ROI Calculator
Enter the relevant numbers in our calculator to get the ROI.
OT Security ROI Calculator
The Best OT Security vendors
Let’s now take a look at some of the best OT security vendors and see exactly how their solutions can help secure IoT and industrial systems.
1. Forcepoint EDITOR’S CHOICE
Best For: Securing ICS and OT environments
Relevant For: Organizations managing critical infrastructure that require continuous monitoring, network segmentation, and protection against cyber threats targeting OT systems
Price: Negotiated price.
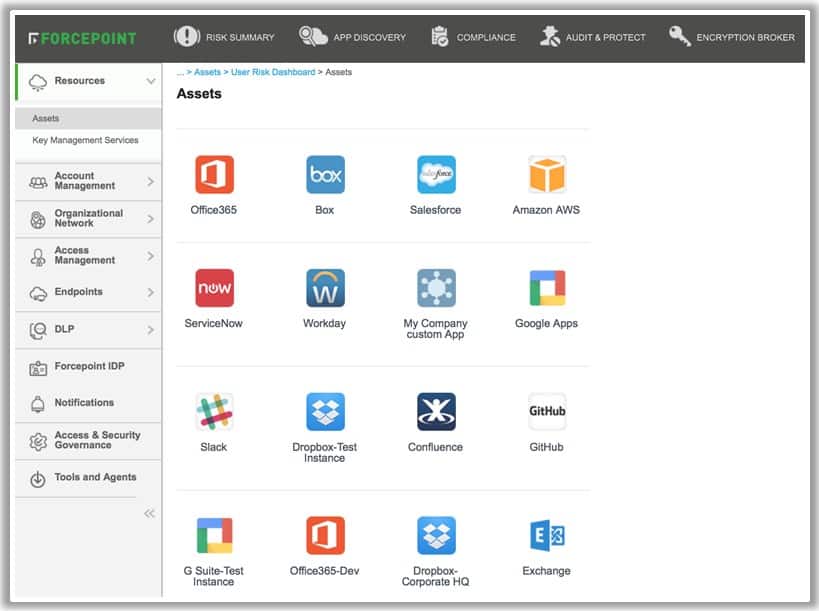
Forcepoint offers a suite of security services that encompass OT security as well as user, data, and edge protection. Within this suite, Forcepoint offers specialized security for critical infrastructure and IoT environments.
Forcepoint’s Key Features:
- Seamless IT/OT Integration: Integrates IT and OT environments for unified security management.
- Byte-Level Content Inspection: Inspects and validates data at the byte level to ensure security and integrity.
- SIEM Integration: Easily integrates with SIEM platforms for comprehensive security monitoring.
Unique Buying Proposition
Forcepoint OT Security delivers advanced threat protection tailored for industrial networks, ensuring both cybersecurity and operational continuity. Its ability to monitor network traffic in real time, detect anomalies, and enforce zero-trust security policies makes it a strong choice for businesses seeking to safeguard legacy and modern OT assets without disrupting critical processes.
Feature-in-Focus: Industrial-Grade Network Segmentation
Forcepoint’s platform provides Deep Packet Inspection (DPI) and micro-segmentation capabilities designed specifically for industrial networks. It restricts lateral movement and enforces strict access controls to minimize the risk of cyber threats spreading across OT environments.
Why do we recommend it?
Forcepoint is a network security package that can implement a range of strategies that include SASE and ZTA. What these acronyms mean is that you can control access to devices and applications through network device settings and you can also construct virtual secure networks across the internet, including industrial machinery.
The critical infrastructure service enables companies to enable OT security quickly whether the environment is already networked, or in a transitional stage. The service works to map out and create network boundaries and plan how cloud and remote access controls will work for your critical systems.
Through Forcepoint’s Data Guard, you can connect older devices and industrial machines to your private network to enable information sharing and the creation of insights that weren’t otherwise possible. Data Guard uses byte-level content inspection and data validation to ensure data is secure and untampered while in transit.
Data pulled from lower-level network devices can be aggregated into a single environment for security monitoring and management. If your organization already uses a SIEM platform, this data can be pulled quickly into the system for auditing and alert purposes. Forcepoint allows you to bring both IT and OT security together in a way that gives you a single pane of glass to view all of your physical and digital assets.
The methodology behind the technology involves creating layers of security and separating the IT network from operation controls without impacting productivity or limiting operators from doing their jobs.

Who is it recommended for?
This isn’t specifically an OT system, which means that you can construct shop floor security controls into your entire business system. Integrate multiple sites and cloud services into a single virtual network and gain central control over industrial systems remotely. The flexibility of this system makes it suitable for any business.
Pros:
- User-Friendly Interface: The interface is intuitive and easy to navigate.
- Advanced Threat Detection: Combines fingerprinting and behavioral analysis to effectively identify threats.
- Threat Containment: Utilizes a cloud-based sandbox to isolate and contain threats.
- Robust SIEM Integration: Offers strong integration capabilities with existing SIEM platforms for enhanced monitoring.
Cons:
- Pricing Information: Requires contacting sales for detailed pricing information.
Pricing for Forcepoint’s Infrastructure OT Security services is not available on its site. You can schedule a demo or request pricing on its website.
EDITOR'S CHOICE
Forcepoint is our top pick for an OT security vendor because it offers ways to plan and implement the implementation of hybrid networks that include traditional office systems with IoT and industrial devices. Create your network across sites through internet links but ignore the underlying medium and apply consistent security measures across environments. Wrap your entire business IT system with a defined boundary and patrol it with edge services. The package provides ongoing performance and security monitoring with alerts.
OS: Cloud-based
2. Nozomi Networks Guardian Sensors
Best For: Network visibility and risk assessment
Relevant For: Energy and utilities, oil and gas, manufacturing, and transportation sectors that rely on ICS and need asset visibility and network security
Price: Negotiated price
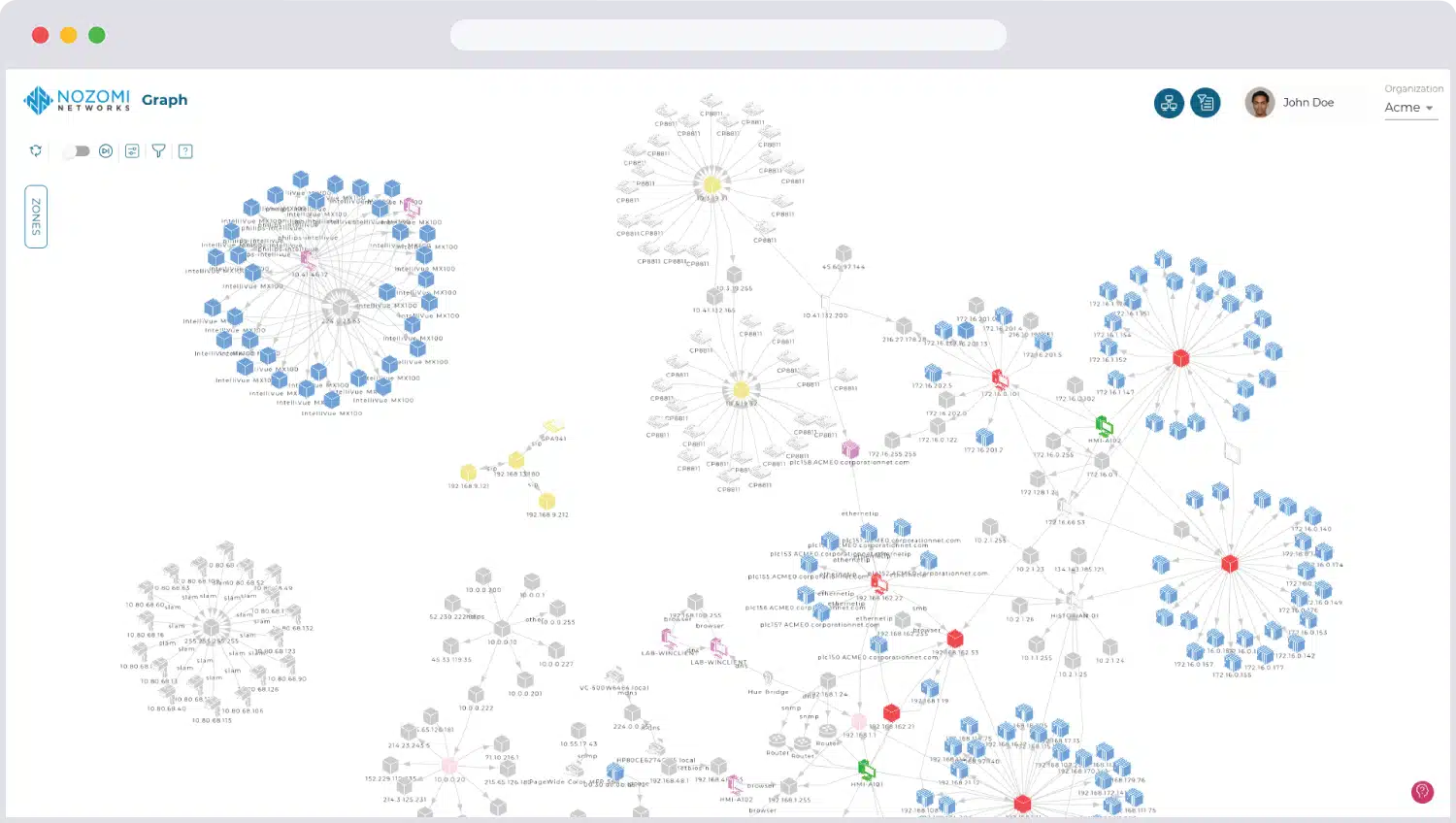
Nozomi Networks Guardian Sensors is an industrial network performance monitor. It is able to detect industrial devices, called industrial control systems (ICSs) and operation technology (OT) systems as well as IoT devices. While ICSs and OT are found on the shop floor in the form of networked machine controllers and programmable systems, IoT devices can be anywhere around the premises, such as security cameras. Some IoT devices that need to be monitored can even be offsite.
Nozomi Networks Guardian Sensors’ Key Features:
- Device Discovery: Automatically identifies and catalogs industrial and IoT devices.
- Asset Inventory Creation: Builds a comprehensive inventory of all networked devices.
- Monitors Cloud and Virtual Systems: Extends monitoring capabilities to cloud and virtual environments.
Unique Buying Proposition
Nozomi Networks Guardian Sensors provide AI-driven threat detection combined with asset visibility and risk analysis. It can integrate both IT and OT environments to proactively manage vulnerabilities and prevent cyber threats.
Feature-in-Focus: AI-Powered Anomaly Detection
This OT platform uses machine learning to analyze network behavior and detect deviations that could indicate cyber threats or operational risks. Its continuous monitoring of traffic patterns and device communications provides early warnings for potential attacks, misconfigurations, or equipment failures.
Why do we recommend it?
Nozomi Networks Guardian Sensors are collectors for environmental conditions that protect industrial control systems, IoT devices, OT equipment, and other It systems. These sensors are available both as physical devices and virtual appliances. While providing readings, the system also maps and scans each device, providing patch management and configuration control.
The Nozomi system scours an industrial network and discovers all of the intelligent devices that are connected to it. The system can also scan wireless systems and identify IoT devices. Each encountered device is queried for its attributes and the information gathered in this process is entered into a device inventory.
The monitor is able to compose a network topology map based on the network inventory and connection details relayed by each device. Each successive performance status checks constantly update both the inventory and the topology map.
Performance monitoring looks at traffic throughput and protocol activity. The system can then identify unexpected or abnormal behavior and that causes the Nozomi service to generate an alert. This notification of a problem draws the attention of system technicians to implement troubleshooting investigations.
While polling for status reports from all devices, the Nozomi system also performs vulnerability scanning. Issues that are discovered during both status and vulnerability scans are color-coded by severity in the Nozomi console and prioritized for resolution.

Who is it recommended for?
Any industrial or flow processing system can benefit from this system. The package includes sensors for operations activity and environmental risk as well as software for asset management and configuration protection. You can also use this system to spot traffic anomalies that could represent an attack.
Pros:
- Comprehensive Device Discovery: Effectively discovers and documents all connected industrial and IoT devices.
- Dynamic Network Mapping: Creates and continuously updates a detailed network topology map.
- Real-Time Performance Monitoring: Monitors live traffic and protocol activity to detect anomalies.
- Vulnerability Management: Performs continuous vulnerability scans and prioritizes issues for resolution.
- Error Prioritization: Color-codes and ranks discovered errors by severity for efficient troubleshooting.
Cons:
- No On-Premises Option: Available only as a cloud-based service.
The Nozomi Network Guardian Sensors system is a cloud-based SaaS package. You can get a demo of the Nozomi system to assess it for yourself.
3. SigaGuard
Best For: Deep Process-Level Anomaly Detection
Relevant For: Critical infrastructure sectors that need physics-based monitoring to detect process deviations and cybersecurity threats
Price: Negotiated price
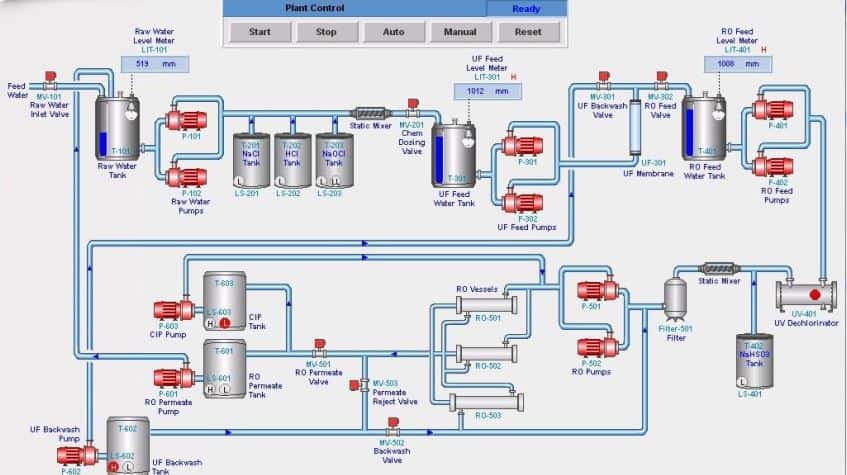
SigaGuard creates visibility into IoT networks and IT devices using accurate real-time sensors combined with a centralized monitoring and security platform. SIGA not only uses this information to provide OT security, but to reduce the need for human intervention by automating security responses.
SigaGuard’s Key Features:
- Sensors Supported by 10+ Integrations: Compatible with sensors from leading industrial companies.
- Electrical Signal Monitoring: Monitors raw electrical signals for accurate and secure process visibility.
- Regulatory Reporting: Generates detailed reports to meet regulatory compliance requirements.
Unique Buying Proposition
SigaGuard offers a unique approach to OT security, as it focuses on electrical signal monitoring at the physical layer. Unlike traditional cybersecurity tools that analyze network traffic, SigaGuard detects anomalies by directly monitoring raw electrical signals from industrial equipment for the early detection of both cyber and operational failures.
Feature-in-Focus: Physics-Based Anomaly Detection
It continuously monitors electrical signals from sensors and controllers to detect abnormal behavior, equipment malfunctions, and cyber-physical attacks. This method provides an additional layer of security and identifies threats even if they bypass conventional network-based defenses.
Why do we recommend it?
SigaGuard is a network TAP. It is a Physical Layer system that recreates packets and then compares the results to the data that arrives at the console. This is an important protection against the hacker strategy that inverts sensor results in the receiving software to con an operator into making inappropriate interventions.
SIGA is flexible and can be used in any industry such as energy, manufacturing, water treatment, or building management. The platform is designed to cover OT security as well as provide real-time business intelligence, reporting, and asset management all in as a single service.
Rather than using packet inspection, SIGA monitors raw electrical signals in the physical process to help support visibility into devices and pair that information with security insights for a deeper understanding of how the industrial side of your network is operating.
Currently, SIGA uses ICS and sensor technology that is supported by Honeywell, Siemens, GE, Schneider, and six other companies. These sensors can help close the gap between OT and IT by networking them through an alert control system. This system monitors for abnormal fluctuations or suspicious events that may signal a cyber attack is underway.
Alerts can create tickets for a security team, or deploy automated responses. In addition to real-time alerts, regulatory reporting and asset performance insights can be saved or sent out automatically depending on your needs.
Who is it recommended for?
This system is useful for critical infrastructure, such as pipelines or pressure systems that can be seriously damaged if sensor readings are corrupted either through connection errors or malicious actions. This package can be used by in-house security operations teams or managed security service providers.
Pros:
- Automation Across Infrastructure: Automates security responses and monitoring for complex critical infrastructure.
- Regulatory Monitoring: Provides comprehensive regulatory compliance and reporting capabilities.
- Enterprise Integration: Supports integrations with major industrial systems and sensors.
Cons:
- Industrial IoT Focus: Primarily designed for industrial IoT networks, making it less suitable for other environments.
You can view a demo of SIGA in action upon request.
4. Honeywell Forge Cybersecurity
Best For: Industrial Cybersecurity and Risk Management
Relevant For: Manufacturing, energy, oil and gas, chemicals, and critical infrastructure operators that require end-to-end OT cybersecurity solutions, including threat detection, compliance management, and asset protection
Price: Negotiated price
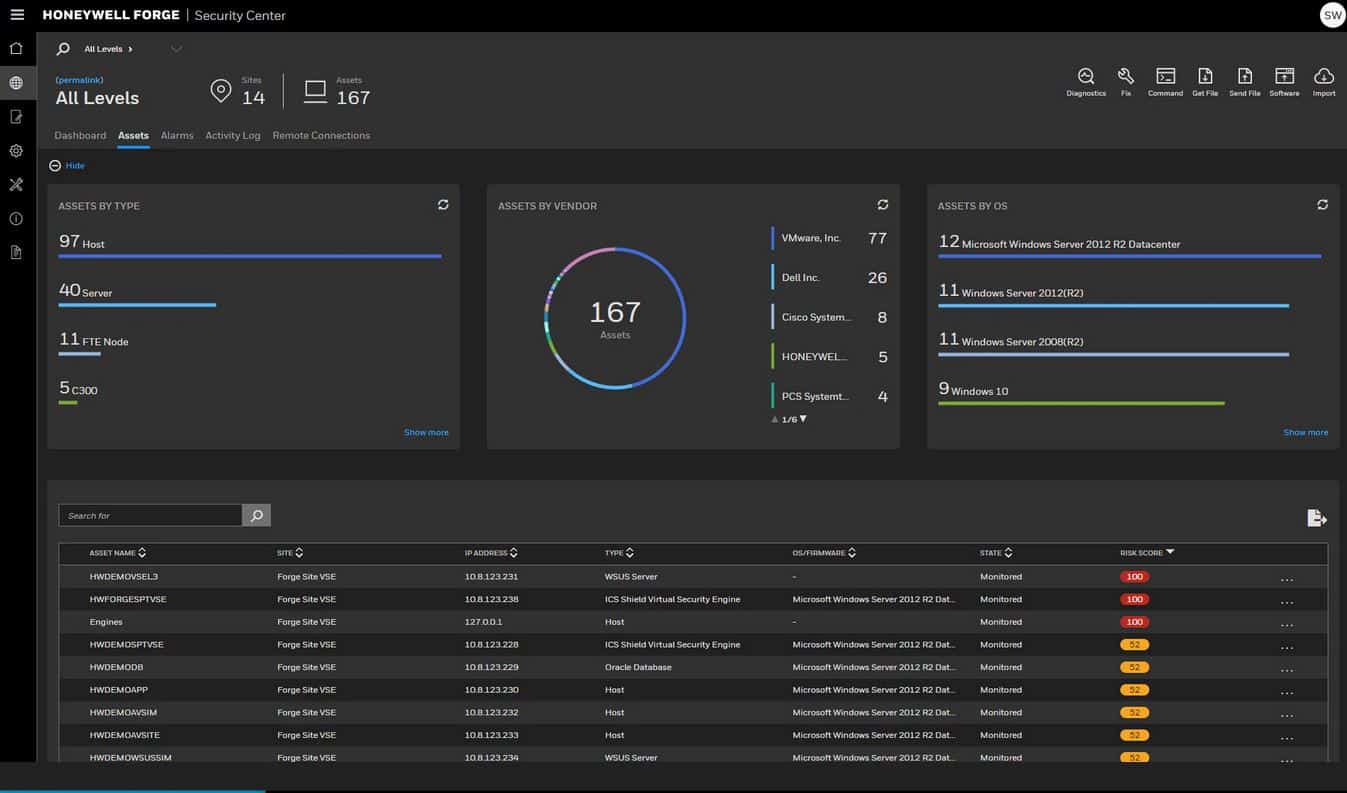
Honeywell Forge Cybersecurity platform works to secure every endpoint in the IoT chain and bring that data together in a way that makes business safer and more efficient. Honeywell offers solutions for virtually any sized business or level of cybersecurity maturity.
Honeywell Forge Cybersecurity’s Key Features:
- Follows NIST and Industry-Standard Guidelines: Ensures compliance with leading cybersecurity frameworks and standards.
- Features Risk Scoring: Provides risk assessments and scores for each device in the network.
- Real-Time and Historical Data Collection: Collects and analyzes both current and past network data.
Unique Buying Proposition
Honeywell OT security solutions provide a full-suite approach to securing industrial environments. With advanced threat intelligence, asset visibility, and compliance support, Honeywell integrates security directly into industrial operations, reducing both cyber and operational risks.
Feature-in-Focus: Industrial Threat Intelligence and Risk Management
Honeywell leverages its deep industry expertise to offer real-time threat intelligence tailored for OT environments. Its risk management framework helps businesses assess vulnerabilities, implement proactive security measures, and maintain compliance with industry regulations like NIST and IEC 62443.
Why do we recommend it?
Honeywell Forge Cybersecurity discovers all equipment on a network and creates an asset inventory. It then performs a risk assessment on each device. The package then implements continuous monitoring for anomalous network traffic. Two multi-site systems add on the management of communicating remote monitoring over the internet.
With scalability in mind, Honeywell uses NIST SP 800-82 and other leading international standards to ensure your company is within compliance and leveraging best practices against OT security threats.
At a glance, Honeywell Forge provides insights into your network by creating events paired with a risk score. From this score, you can drill down and identify exactly what your risk factors are, and see what predetermined security policies may be in violation. This methodology helps IT security teams quickly view and prioritize assets that may be the most vulnerable.
Remote access into your industrial network can be standardized and audited through role-based and device-specific privileges. This extends into securing OT-centric files or data with built-in threat detection that inspects and monitors files in transit.
Proactive monitoring allows for both real-time alerting and historical data collection that can be integrated into a SIEM product. Different alerts can be set up depending on the type of event. For example, security events can be routed to the security team, where maintenance events such as a low oil level can be routed to a maintenance team member.
Who is it recommended for?
Honeywell is a solid brand and this system will appeal to existing customers of the company’s IT systems. This is a straightforward traffic monitoring system that has been applied to industrial sites. The Fircepointr and SCADAfence systems offer more innovative security solutions.
Pros:
- User-Friendly Interface: Features an intuitive interface ideal for NOC dashboards and teams.
- NIST Standard Reporting: Offers comprehensive reporting and vulnerability prioritization based on NIST standards.
- Real-Time Data Collection: Supports real-time data integration with SIEM products for enhanced monitoring.
- Versatile Integrations: Provides various integration options for alerting and notifications.
Cons:
- General OT Vendor: More suited for general OT applications compared to more specialized security solutions.
Pricing and further information can be provided by the Honeywell sales team.
5. Kaspersky Industrial CyberSecurity
Best For: Endpoint Protection and Network Security
Relevant For: Critical infrastructure sectors that require endpoint security, anomaly detection, and industrial network protection against cyber threats
Price: Negotiated price
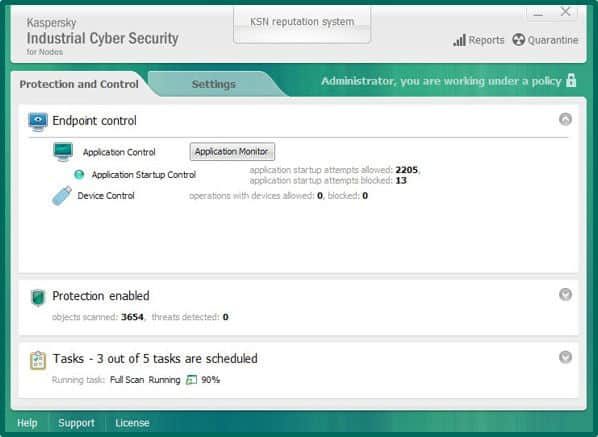
Kaspersky is known for its suite of security products that cover dozens of different threats and business needs. Industrial CyberSecurity aims to connect processes, people, and technology in a way that is both safe and easy to manage.
Kaspersky Industrial Cybersecurity’s Key Features:
- Education for In-House Teams: Provides training programs to increase cybersecurity awareness for IT, OT, and executive staff.
- SCADA Specific Monitoring and Protection: Offers targeted security measures for SCADA systems.
- Holistic Monitoring Based on Sensors: Utilizes sensors for comprehensive monitoring and business intelligence.
Unique Buying Proposition
Kaspersky Industrial CyberSecurity (KICS) secures endpoints, monitors network traffic, and detects anomalies in real time. It provides deep visibility into industrial networks while minimizing the risk of cyberattacks disrupting operations.
Feature-in-Focus: ICS-Specific Threat Detection and Response
KICS uses behavior-based anomaly detection to identify and mitigate threats within OT environments. It continuously monitors ICS networks for suspicious activity, unauthorized changes, and malware.
Why do we recommend it?
Kaspersky Industrial CyberSecurity is a complicated platform of multiple units. This system covers devices and networks and it also ties in with Kaspersky’s office systems security products. This is a difficult system to set up because it has a lot of moving parts but once it’s working, the system console makes sense of everything.
With over a dozen integrations and partnerships, Kaspersky Industrial CyberSecurity offers OT security for enterprise-level industrial businesses. The platform holistically uses sensors and systems to monitor key assets as well as provide business intelligence.
Designed to secure every layer of the industrial network, Kasperksky has security solutions for monitoring and protecting SCADA servers, human interface machines, programmable logic controllers and endpoint workstations.
Through industrial endpoint protection on each sensor, Kapsersky can monitor for breaches, anomalous behavior, and insider threats. Outside of the OT security service, Kaspersky also provides training for IT, OT, and C-level members for your organization to increase cybersecurity awareness and assist teams in-house.

Who is it recommended for?
This system is suitable for large organizations that have a lot of technicians on staff. It is particularly useful for companies that need to flow information back and forth between the office and the shop floor because all of the movements present opportunities for malicious intervention.
Pros:
- Comprehensive Endpoint Support: Protects industrial endpoints and IoT devices.
- Suitable for Smaller OT Networks: Ideal for smaller OT networks needing robust security.
- Extensive Tool Repository: Offers a wide range of tools and resources for new users.
Cons:
- Visual Interface: Could benefit from a more user-friendly visual interface for easier navigation.
You can reach out to the Kaspersky team for a demo of their platform.
6. Darktrace Industrial Immune System
Best For: AI-driven security for converged IT and OT environments
Relevant For: Organizations in manufacturing, energy, utilities, and transportation sectors that require unified visibility and proactive protection across both IT and OT infrastructures
Price: Negotiated price
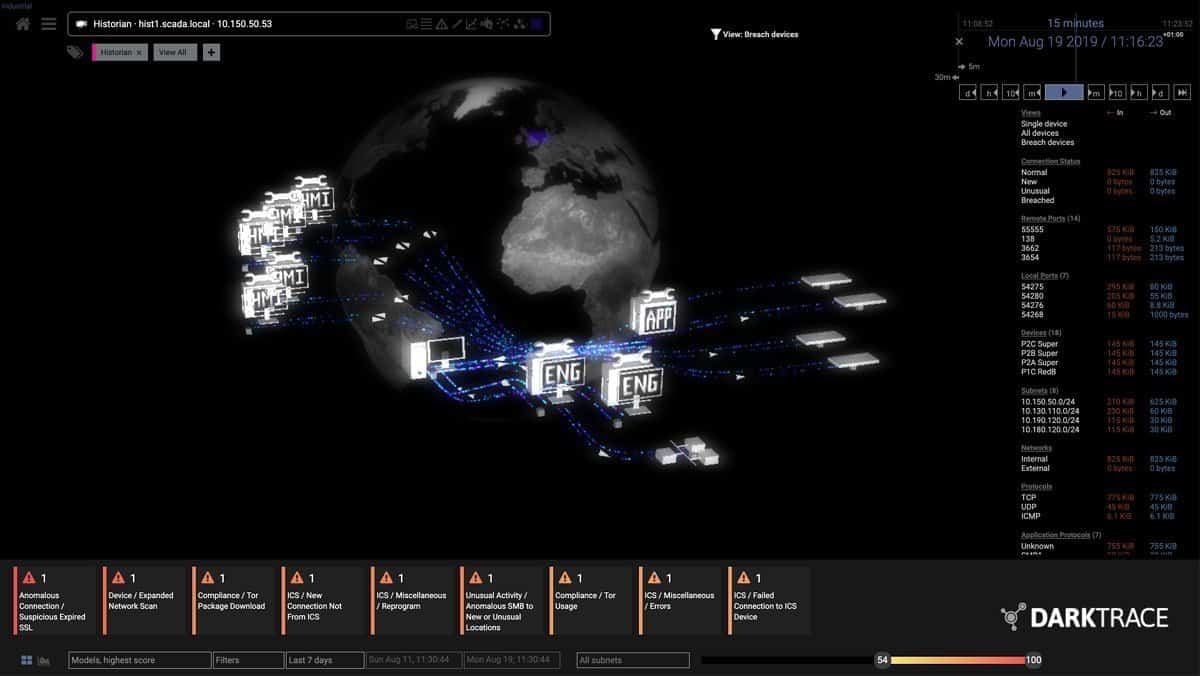
Darktrace is a cloud-based OT security platform that uses self-learning artificial intelligence to cover entire networks, including IoT assets. For industrial security, the Darktrace Industrial Immune System works by monitoring the baselines of hundreds of networks in the industrial space to see what “normal” looks like.
Darktrace Industrial Immune System’s Key Features:
- Leverages Artificial Intelligence: Utilizes self-learning AI to monitor and secure networks.
- Integrates with Older Technology: Compatible with legacy systems and older technology.
- Suite of Additional Security Features: Provides a comprehensive range of security tools and features.
Unique Buying Proposition
Darktrace uses Self-Learning AI to autonomously detect and respond to both known and unknown threats in real time. It continuously learns the ‘patterns of life’ for every device and operator within an industrial environment to provide unparalleled visibility and security across all levels of the network.
Feature-in-Focus: Unified Visibility Across IT and OT
It offers continuous identification and visualization of all assets across IT and OT protocols. This holistic approach enables you to manage risk effectively from a single unified platform without compromising productivity.
Why do we recommend it?
Darktrace Industrial Immune System is part of an anomaly detection system that uses AI to profile each user and each device on a network. This is a technique that is known as User and Entity Behavior Analytics (UEBA). Darktrace was a pioneer of this methodology, which is now widespread.
It uses this information to track and detect anomalous behavior as it plays out. Each time an attack is found and stopped the system learns what to look for next time, remembers how it operated, and how it can defend against it.

The system takes this same learning approach for every device, controller, and user. A pattern of life is recognized over time by the Darktrace system, and deviations are alerted to. Outside of cyberattacks, the system can also identify internal threats, operator error, and mechanical malfunctions.
Since Darktrace uses AI to recognize and understand patterns, the entire platform is protocol agnostic, meaning that it can be used to monitor virtually any protocol or technology. The platform can fully support any business looking to increase its security posture and can integrate with old PCLs or devices without current sensor support.
Outside of OT security, Darktrace can offer security services for email, cloud-based applications, and standard IT network security monitoring.
Who is it recommended for?
Darktrace is known for insider threat detection in office systems. This is now also applied to OT devices. Darktrace can spot unexpected activity, such as changes to the settings of industrial equipment and looks for unauthorized instructions. This is a good option if you want to unite your office and shop floor security systems.
Pros:
- Advanced Threat Visualizations: Offers detailed visualizations of data and threats for better insight.
- AI-Powered Monitoring: Uses AI to effectively monitor complex networks and detect anomalies.
- Baseline Analysis: Detects threats by analyzing deviations from established network baselines.
Cons:
- Enterprise Focus: Primarily suited for larger enterprise networks, potentially overkill for smaller setups.
You can test out Darktrace through a free 30-day trial.
7. Dragos
Best For: Advanced industrial cybersecurity and threat intelligence
Relevant For: Energy, manufacturing, water utilities, and transportation that require specialized OT threat detection and incident response
Price: Negotiated pricing
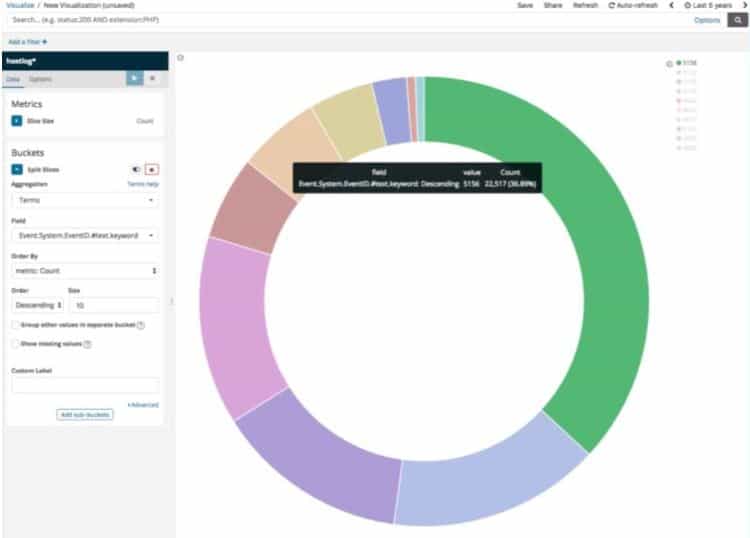
Dragos is a robust OT/ICS cybersecurity platform designed to provide professional OT security services as well as platform and threat intelligence training. Designed by ICS practitioners, the Dragos platform starts with best practices out of the box and works to constantly protect and monitor your IoT environment.
Dragos’ Key Features:
- Global Intelligence Sharing: Leverages global threat intelligence to enhance detection and response.
- Managed Service Option: Provides a managed service for comprehensive security monitoring and management.
- 21+ Partnerships: Integrates with numerous partners to extend and enhance security capabilities.
Unique Buying Proposition
Dragos provides deep OT threat intelligence combined with asset visibility, vulnerability management, and proactive threat detection. With a focus on ICS and OT-specific threats, it helps organizations mitigate risks before they impact operations.
Feature-in-Focus: OT-Specific Threat Intelligence
This platform delivers intelligence-driven insights tailored to industrial environments. Its extensive library of adversary Tactics, Techniques, and Procedures (TTPs) helps security teams proactively defend against cyber threats in OT networks.
Why do we recommend it?
Dragos is a specialized OT security platform that includes preventative measures and security monitoring. This service includes a vulnerability scanner that checks on misconfigurations in OT devices and identifies outdated firmware. The security monitoring looks for intrusion and it is informed by a threat intelligence feed.
While some platforms just provide alerts to OT security events, Dragos takes it a step further by providing step-by-step instructions on exactly how to handle a threat or security incident. These are called Key Takeaways and are designed to give your security team actionable items to complete to rectify any issues.
There are also labeled Indicators of Compromise (IoC) which are forensic breadcrumbs that can be traced to help identify malicious behavior. IoCs are important when not only documenting threats but also building a legal case against an attacker.
IoCs along with detailed reporting gives you an inside look into adversary behavior and the techniques that were attempted on your network. This information can be used to correct vulnerabilities and identify other possible avenues of attack.

Who is it recommended for?
Any system manager will understand the Dragos methodology because it performs the same techniques on industrial systems that are regularly implemented for office endpoints. This is a thorough solution that ensures OT systems are hardened against attack and it also adapts security monitoring to current attack campaigns.
Pros:
- Intuitive Graphics: Uses simple, intuitive graphics for clear network visibility and monitoring.
- Extensive Partnerships: Integrates with over 21 partners, broadening its security ecosystem.
- Global Threat Intelligence: Utilizes shared intelligence to stay ahead of emerging threats.
- Forensic Tools: Offers tools for documenting and investigating threats, useful for legal and forensic purposes.
Cons:
- Enterprise Focus: Primarily designed for large enterprise networks, potentially too complex for smaller environments.
Dragos provides powerful OT security by not only leveraging its global intelligence sharing but through its 21+ strategic partnerships. For companies who are looking to manage their OT Security off-site, Dragos provides OT security as a managed service through its Neighborhood Watch program. This lets the Dragos team manage and stop security threats, update and patch endpoints, and conduct threat hunting on your network.
Our Methodology for Choosing OT Security Vendors
Our cybersecurity experts evaluated the top tools against the below criteria to come up with a list that can work well for most organizations. These criteria are:
1. Physical Security Integration
OT environments involve physical assets like machinery and sensors. We considered platforms that integrate with physical security systems like surveillance cameras, badge access systems, and environmental monitoring to provide a holistic security approach.
2. Resilience Against Supply Chain Attacks
Many industrial cyberattacks originate from compromised third-party software or hardware components. To safeguard your organization from such attacks, you need a platform that monitors software integrity, detects unauthorized firmware changes, and tracks supply chain vulnerabilities.
3. Customizable Security Policies
Every industrial setting has unique security needs. This is why we prioritized platforms that support custom security policies tailored to specific operational requirements, rather than relying on rigid, one-size-fits-all solutions.
4. AI-Driven Predictive Maintenance
As a part of our evaluation, we looked for platforms that use AI-driven analytics to predict equipment failures due to cyber threats or operational anomalies, reducing downtime and preventing cascading failures.
5. Coexistence with IT Security Tools
Many organizations run both IT and OT environments that necessitate a comprehensive security solution. To address this need, we selected platforms that seamlessly integrate with IT security tools like SIEMs, EDR solutions, and cloud security platforms to provide unified security management.
Besides the above factors, we also considered platform reliability, vendor support, user reviews, and usability to ensure that the tools we present have high adoption rates and good ROI for your business.
B2B Software Selection Approach
Choosing an OT security platform involves assessing the credibility and long-term reliability of the vendor. When analyzing and comparing different solutions, we consider:
- Balance between cost and the value delivered
- Vendor’s experience in securing industrial environments
- Customer feedback, real-world deployment performance, and case studies
- Company’s transparency regarding product limitations and capabilities
- Vendor’s commitment to continuous updates and long-term security support
While not every factor may be covered in each review, we highlight key strengths and potential drawbacks to help you make informed decisions.
Learn more about our B2B software selection approach.
Vendor Support Evaluation for OT Security
A strong support system is essential for OT security platforms, as they protect critical infrastructure and industrial processes. Our evaluation of vendor support includes:
- Availability of 24/7 dedicated support teams
- Responsiveness and expertise in handling OT-specific security incidents
- Frequency of security updates and patches to address emerging threats
- Access to self-service resources such as technical guides and training modules
- Vendor’s track record in resolving security vulnerabilities and providing long-term assistance
Each vendor is assessed based on these criteria, with a focus on real-world impact on operational continuity, security resilience, and customer experience.
Why Trust Us?
Selecting the right OT security platform is a critical decision, and we understand the complexities involved. Our evaluation process is built on extensive industry knowledge, real-world testing, and a commitment to transparency. Here’s why you can rely on our insights.
- Industry Expertise: Our team has deep experience in industrial cybersecurity, compliance, and risk management. We understand the security challenges unique to operational technology (OT) environments.
- Hands-On Analysis: We assess platforms based on their real-world performance in industrial settings, not just marketing claims. Specifically, we looked into how well they integrate with legacy systems, SCADA, and industrial protocols.
- Objective and Unbiased Reviews: Security effectiveness, usability, and long-term value are our key pillars. Our goal is to provide practical insights that can help you make informed decisions.
- Comprehensive Research: Our evaluation covers key security capabilities, compliance alignment, and vendor reliability. We analyze customer feedback, case studies, and independent security tests to validate our assessments.
- Commitment to Continuous Updates: Cyber threats evolve, and so does our research. We continuously refine our recommendations to reflect the latest advancements, vulnerabilities, and regulatory changes in OT security.
With this rigorous approach, we provide trusted guidance to help organizations secure their industrial environments effectively.
OT Security FAQs
What is OT cybersecurity?
OT security, or OT cybersecurity, defines a range of technologies, processes, and best practices that combine to protect office and industrial systems and the connections between them. Inputs to the security management service can also include sensor and video detection systems that enable physical protection to be woven into the security system.
What is OT and IoT security?
OT security is designed to protect premises and industrial equipment as well as office networks and their attached devices. Premises equipment extends to IoT devices, so IoT and OT security measures are very closely linked.
What is OT in NIST?
The National Institute of Standards and Technology (NIST) in the USA has created a Special Publication that is entitled Guide to Operational Technology and this explains to businesses how to go about implementing OT security. The code for the publication is SP 800-82r3.











this is mostly wrong and doesnt reflect industry views or in several cases the actual product information/view is wrong
It’s amazing to me that an article like this can get past editors while leaving out the four actual leading ICS Cyber Security solutions with the largest footprint (Claroty, Forescout, Microsoft, and Nozomi Networks). How does this happen?
Nozomi Networks is a worthy contender. Added – thanks.