RobbinHood is named after the medieval outlaw, only with a different spelling – the Robin Hood of Sherwood Forest only has one ‘b’
RobbinHood ransomware first came to the attention of cybersecurity experts in April 2019. Its initial high-profile attack targeted the municipal offices of Greenville, North Carolina, and just a month later, it struck again, crippling critical systems in the City of Baltimore, Maryland. These incidents quickly brought RobbinHood into the spotlight as a significant threat to public institutions and organizations reliant on uninterrupted IT operations.
RobbinHood primarily targets Windows computers, a common trait among ransomware strains. What makes it particularly dangerous is its exploitation of a deprecated low-level kernel associated with Gigabyte motherboards. This kernel, known for its vulnerabilities and instability, allows the malware to embed itself deeply within the system, far beyond the reach of standard removal tools.
Once a system is infected, victims cannot simply decrypt files or restore basic operations. Full remediation requires a complete reinstallation of the operating system, and often resetting the BIOS, to eliminate all remnants of the kernel exploit. Paying the ransom may provide a decryption key to access files, but it does not resolve the underlying vulnerability, leaving affected systems potentially exposed to future attacks unless thorough remediation steps are taken.
The reliance on this outdated kernel highlights both the sophistication of RobbinHood’s design and the challenges organizations face when attempting recovery. Its persistence demonstrates the evolving nature of ransomware threats, emphasizing the need for proactive cybersecurity measures, including regular system updates, patch management, and comprehensive risk mitigation strategies to guard against emerging attacks.
Where does RobbinHood come from?
RobbinHood isn’t part of a ransomware family, nor is it the product of a known hacker gang. Cybersecurity analysts don’t know anything about the group that created RobbinHood or where they reside. However, there is a clue in the ransom note created for RobbinHood. The second paragraph ends with: “So do not waste your time and hurry up! Tik Tak, Tik Tak, Tik Tak!”
Clocks say different things in different languages – in English, we hear clocks saying “Tick tock.” In Japanese, clocks say “Kachi kachi,” in Chinese, it’s “Dida dida,” and in Korean, clocks say “Ttok ttak.” Clocks say “Tik tak” in Dutch and Russian. Given that most of the ransomware in the world is produced in Russia, it is more likely that RobbinHood is Russian rather than Dutch.
Another indication that this is the work of Russians is that the code for one of the modules, Steel.exe refers to a user directory with the name Mikhail.
How does RobbinHood ransomware get onto a computer?
RobbinHood ransomware uses several different methods to get onto a computer. The primary way the ransomware appears is as an attachment to a phishing email. This will entice the user to download and run the attachment. Another method is through infected websites. This malware adds a popup to the site that tells the user that the browser is out of date. Click OK on the popup causes a download, which, when run, installs the first part of the RobbinHood attack instead of the promised browser update. One other method of distribution is through file-sharing systems. The installer masquerades as a desirable video to trick people into downloading and opening it.
The first part of the installer is a legitimate program that has a security flaw. This is a driver for a Gigabyte motherboard. The driver is what is known as a kernel. It interprets operating system commands into actions on the physical components of the computer. Unfortunately, this driver has a bug, and it has been deprecated by Gigabyte. However, PCs don’t know that the file is no longer valid because it has all the necessary security clearances.
Once this driver is on the computer, it makes an entry point available to the hacker through the known bug. The driver lets other system files get loaded and replace existing systems. This gets under the file management system of Windows and allows the hackers to remove locks on files. It also enables hacker batch files to kill off processes.
What happens in a RobbinHood ransomware attack?
The batch files that the installer loads in kill many running processes, including anti-virus systems. Without the AV running, the malware can run without detection. It also kills any editor that might have a file open. This would include Word and Excel. Any file that is open for editing can’t be overwritten with an encrypted version.
Surprisingly, the malware disconnects any attached drives. This seems to be a lost opportunity to spread onto other computers. However, it seems that the workflow of the encryption process needs to deal with one computer at a time. A replication service within the ransomware bundle is expected to spread the encryption executable to other computers across the network. So, each endpoint will be encrypted separately.
The ransomware has been very successful at possessing the entirety of the corporate system that it infects. It doesn’t implement the encryption immediately but waits until many computers have been infected. Analysts don’t know how the controller for the ransomware knows when enough endpoints have been reached. It may use a standard network monitoring tool to generate a list of all endpoints connected to the same network as the initial target.
The RobbinHood ransomware seems to cross over to other computers on a network using the Remote Desktop Protocol (RDP). Some sites don’t require a password for this protocol implemented as a utility in the Windows operating system. Another security failure for this system is to use an easy-to-guess password, such as password or 123456789.
The last phase in preparation is a cleanup, which deletes all log files and removes the shadow copies that AutoSave functions create. This pre-attack finale also disables the startup recovery mode of Windows.
The RobbinHood encryption process
After performing all of these tasks to spread around a network and alter the kernel of each compromised computer, the attack might still be called off. The hackers have built-in a last-minute on-site control mechanism.
The encryption uses two layers of encryption with the outer wrapper performed with RSA, a public key encryption system. Before beginning the encryption routine, the ransomware looks for a stored RSA encryption key in the Windows Temp directory. The dropper probably installed this file for the ransomware package. However, if the encryption process cannot find it, the whole ransomware procedure is called off.
Given that the whole system is installed together by the same dropper, why could it be that the key file would not be there? It is possible that one of the earlier processes optionally deletes the encryption key file. Russian hackers won’t attack computers that have Russian as the system language. That courtesy extends to the languages of all of the nations of the former USSR, except for the Baltic States. The reconnaissance process may delete the key file if it detects a protected nationality.
The encryption process uses an AES cipher with a new key for each file. The original name of each file and the key used to encrypt it are then stored in a file, which is encrypted with the RSA cipher using the 4096-bit key discovered in the Temp directory. So, each attack can be identified by the same RSA key, which protects many AES keys.
As each file is encrypted, its name is changed to be Encrypted_.enc_robbin_hood. In this schema, the random string is 21 characters long and represents the AES key used to encrypt the file, modified by the RSA encryption. In addition, the latest version of RobbinHood has a new file naming convention. In this system, the original file name remains but with an extra .rbhd extension.
The RobbinHood ransom
RobbinHood drops four copies of the ransom note in text format on the encrypted drive and generates an HTML version displayed on the victim’s screen. This demand note includes a link through to a contact form. However, the target page can only be opened in a Tor browser. The hackers give the victim four days to pay the ransom, or it will increase by $10,000 per day if not spent. The note also explains that once ten days have passed without payment, the record of the decryption key will be deleted, and all chances of recovery will be permanently lost.
Reports suggest that hackers honor their pledge and deliver a decryptor and the key to those who pay. The original ransom ranges between 0.8 Bitcoin and 13 Bitcoin, depending on how many computers were infected.
Sorting out the problem will end up costing more than just the ransom. For example, the City of Greenville calculated that their total recovery costs amounted to $18.2 million – including the ransom, which they paid.
Preventing RobbinHood ransomware attacks
As with all malware, prevention is better than cure. The big problem you will face is not losing data but the mess the buggy kernel installation causes. You will need to strip down each computer and reinstall the whole operating system from the metal up.
You can quickly immunize any computer against the RobbinHood encryption, thanks to that key file check. Unfortunately, different versions use different names for that file. For example, it could be pub.key or key.pub. However, it is always in the C:\Windows\Temp folder. So, create an empty file for each of those names and write-protect them. That way, the installer for RobbinHood won’t be able to copy in the key file, and when the encryption process starts, it will not find the key and therefore fall over.
However, you will still have that kernel problem to deal with. A complete malware protection system is a better plan than a quick fix to block one specific ransomware strain. Here are two systems that you should consider for defense against RobbinHood ransomware and all malware.
1. ManageEngine DataSecurity Plus (FREE TRIAL)
ManageEngine DataSecurity Plus is an essential tool for businesses with a data privacy standard, such as GDPR, PCI DSS, or HIPAA. It is a sensitive data protector.
Key Features:
- File integrity monitoring
- Permissions analysis
- Data loss prevention
- Quarantining
Why do we recommend it?
ManageEngine DataSecurity Plus offers four units to analyze file permissions and protect data locations, control data movements, track user activity, and monitor file changes. RobinHood is an exceptional ransomware system because it replaces a low-level driver, which this system wouldn’t spot. However, DataSecurity Plus would kick in as soon as file encryption begins.
Fortunately, RobbinHood doesn’t steal and publish sensitive data. However, other malware does. The threat to publish stolen data is increasingly becoming a standard extra threat in ransomware to encourage the victim to pay up.
DataSecurity Plus has an eDiscovery module that searches the network for sensitive data stores. Once it finds them, it categorizes the data in each location. This enables you to heighten security in those places. The package also includes a file integrity monitor that will raise an alert if protected files are touched. This tool can also reverse the damage by restoring from backup. It can also kill processes and isolate the device from the network.
Who is it recommended for?
There are many different ransomware strategies and like with all types of malware, there are new attack vectors being invented all the time. The important action of all ransomware, though is to attack data. DataSecurity Plus just focuses on that fact and triggers if data is touched.
Pros:
- Provides a detailed account of file access, allowing sysadmin to understand the context of the file change
- The platform can track access trends over time, allowing for better malicious behavior detection
- Supports built-in compliance reporting for popular standards such as HIPAA, PCI DSS, and FISMA
- Can integrate with numerous helpdesk solutions, notification platforms, and backup systems
Cons:
- Requires a sizable time investment to fully explore all the platforms features and tools
ManageEngine DataSecurity Plus is available for a 30-day free trial.
2. CrowdStrike Falcon Insight
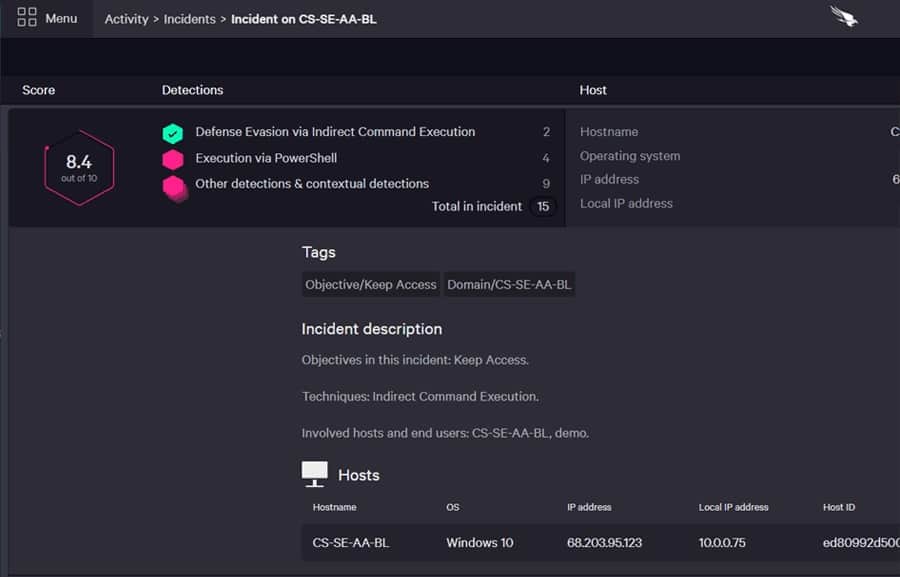
CrowdStrike Falcon Insight is a good security package for guarding against a wide range of malware, including RobbinHood ransomware. Unfortunately, RobbinHood has been through four versions, and the latest software for the system only has 23 percent of the original code in it. This highlights a problem with traditional AVs that just look for specific file names or processes to detect malware – even the same malware evolves over time, making those telltale signs out-of-date. Instead, Falcon Insight uses an adaptable detection system that spots new malware.
Key Features:
- Multi-layer solution
- Continued protection when offline
- Network-wide threat intelligence
- Dual-level threat hunting
- Automated responses
Why do we recommend it?
CrowdStrike Falcon is a good solution to prevent any type of ransomware, including RobinHood. This system maintains a local antivirus system on each end, which can continue to protect the device if the computer gets disconnected from the network. The cloud-based controlling unit shares warnings with all unaffected endpoints.
The Falcon Insight system is a next-generation endpoint detection and response (EDR) service. This tracks all activity on an endpoint and identifies regular activity for each user account. The system raises an alert if non-typical behavior suddenly emerges. The RobbinHood trick of installing a new kernel would fit into that category of abnormal behavior.
The CrowdStrike Falcon Insight service is a coordinator for endpoint-resident detection systems. These modules are available separately as a product called Falcon Prevent.
The Insight service is a cloud-based module that receives activity reports from endpoint agents and scans through them for suspicious behavior. This gives the CrowdStrike system two points of detection. The first looks at one endpoint’s activity, while the other looks for linked activities across endpoints. This is useful for spotting ransomware activity that spreads from one endpoint to another.
The cloud system also receives a threat intelligence feed and communicates recommended actions down to the endpoint modules. In addition, the EDR service includes remediation systems that can instantly block an evolving attack. For example, the EDR can quarantine software or kill processes that seem threatening. It can also isolate a device from the network to stop an infection from spreading.
Who is it recommended for?
This package is suitable for a large organization. Its endpoint agent is also available as a standalone on-device next-gen antivirus package, called Falcon Prevent. The addition of the cloud-based Insight unit extracts reports from these endpoint systems, collects them, and searches for company-wide threats.
Pros:
- Excels in hybrid environments (Windows, Linux, Cloud, BYOD, etc)
- Intuitive admin console makes it easy to get started and is accessible in the cloud
- Can track and alert anomalous behavior over time, improves the longer it monitors the network
- Lightweight agents take up little system resources
Cons:
- Would benefit from a longer trial period
You can get a 15-day free trial of Falcon Prevent.