Ransomware continues to rank among the most disruptive cybersecurity threats today, impacting organisations, public sector bodies, and individual users. Sigma ransomware is one variant that has attracted particular attention due to its advanced techniques and ability to evade conventional security controls.
Here is our list of the best Sigma ransomware protection systems:
- ManageEngine Log360 EDITOR’S CHOICE This is a megapack of ManageEngine modules that implements log collection and SIEM threat hunting with options for automated remediation of discovered security issues. Available for Windows Server. Download a 30-day free trial.
- ManageEngine Endpoint Central (FREE TRIAL) A monitoring and management package for workstations running Windows, macOS, and Linux, with a mobile device management option. Offered as a SaaS platform or a software package for Windows Server. Get a 30-day free trial.
- CrowdStrike Falcon Insight A hybrid package with an on-device unit for continuity and a cloud-based central SIEM-style threat hunter.
- BitDefender GravityZone Provides a package of malware protection and backup services in a range of editions for different business types.
First identified in October 2017, Sigma ransomware has been linked to a cybercriminal group known as The Conti Group, which has also been associated with other significant attacks. It has primarily been used against large organisations, especially in sectors such as healthcare, finance, and manufacturing, where encrypted data can severely disrupt operations and lead to major financial consequences.
What makes Sigma particularly dangerous is its use of advanced evasion methods, including polymorphic encryption, which continuously alters its code structure to avoid detection by signature-based security tools. This makes it difficult for traditional antivirus systems and firewalls to identify and stop before infection occurs.
Distribution typically occurs through phishing campaigns, malicious email attachments, or compromised software updates, all of which make it challenging to block using standard perimeter security alone.
This guide takes a closer look at Sigma ransomware, explaining how it operates, the potential impact of an attack, and the most effective defence strategies. It explores common attack vectors and techniques used by threat actors, along with practical measures such as threat detection, endpoint protection, and incident response planning to strengthen organisational resilience.
Understanding the behaviour and characteristics of Sigma ransomware is essential as these attacks continue to evolve. Whether securing enterprise environments or individual systems, this guide provides the insight needed to help reduce risk and limit the impact of an infection.
Where does Sigma ransomware come from?
The latest version of Sigma was discovered in mid-2020, and security researchers noticed similarities with the Shade ransomware. Shade is one of the oldest and longest-running ransomware systems in the world. It mainly attacked victims in Germany, Russia, and Ukraine. The Shade ransom note was written in Russian and English. This pool of victims shows that Shade, and therefore possibly also Sigma, is not from Russia or Ukraine.
Russia is probably the largest producer of ransomware in the world, closely followed by Ukraine. Hackers from those two countries put routines into the launch code of their ransomware that kills execution of the attack if the system language of the infected computer is set to Russian or one of a former Soviet nation (except for the Baltics).
Shade was also known as Troldesh, and Encoder.858, first emerged in 2014, and it shut down in August 2020. With its end of campaign announcement, the hackers controlling the software released 750,000 decryption keys for its remaining victims. Kaspersky Labs produced a free decryptor from this database.
The Shade gang never published or sold the programs for its ransomware suite. So, it is possible that the very similar version of Sigma that began circulating mid-2020 was just a revamped version of Shade. However, Sigma has been known since 2017, so for several years, these two ransomware systems broadcast simultaneously and then were consolidated. Another possibility is that the Shade gang had nothing to do with Sigma ransomware but decided to appropriate its name for a rebrand of its existing ransomware.
How does Sigma ransomware get onto a computer?
Sigma is currently circulated by spam email. In the past, it has also been hidden in downloads from infected websites, where a popup offered a free software package or through download repository sites for free software.
In earlier versions of Sigma ransomware, the spam email attempt masqueraded as an application for a job advertised on Craigslist. The current incarnation is formatted as a warning email from Mastercard, telling the victim that they are being sued to recover a $3,000 unpaid debt. Some versions of Sigma even include the name of the victim in the email.
The credit card email explains more details of the legal action in an attached Word document. On opening the document, a system popup asks the user to enable macros. With that, the infection is released, placing a Trojan on the computer. This, in turn opens a connection to a command and control server (C&C), downloading the entire ransomware package.
What happens in a Sigma ransomware attack?
The Sigma ransomware system doesn’t trigger encryption straight away. Instead, modules in the package attempt to spread to other computers on the same network by using the remote desktop protocol (RDP).
The RDP system is a native Microsoft service that enables a computer user to access a remote computer and use it locally. This is useful for telecommuting or roaming staff and also for support technicians.
Not all businesses use this system. However, there is often a service active on many PCs that listens for RDP connection requests and accepts them. This service might have been activated unintentionally, or it might require a specific software package. Even if you remove a piece of software, uninstallers only remove the code and registry entries for that package – they don’t research what settings that software changed and reverse them.
RDP can be accessed without a password. However, if a software installer has been set up, the port is probably password protected but with an easy-to-guess and universal passwords, such as password or guest.
The Sigma ransomware will replicate itself around a network, and this phase might last for weeks. Unfortunately, there is no information on how the ransomware decides that enough computers on the network have been compromised before it triggers encryption.
The Sigma encryption process
Sigma ransomware only encrypts data files, so system files and executables are not affected, and the computer will continue to function. The ransomware uses two encryption ciphers. The first of these is AES with a 256-bit key. This encryption transforms each file, using a different key for each file. The name of each compromised file and the encryption key used on it are then written to a file.
AES uses the same key to encrypt and decrypt data. So, getting access to that file will enable the decryption of all encrypted files. The second encryption system used by Sigma ransomware prevents that discovery, however. This is the RSA cipher, used with a 2048-bit key.
The combination of AES for file encryption and RSA for a key locker file is prevalent with ransomware. This is because RSA uses a different key to decrypt data than that used for encryption. Therefore, there is no risk to the strength of the attack if the RSA encryption key is found on the local computer. However, RSA encryption is slow. This is why AES is used for the heavy workload of encrypting all of the files.
While earlier versions of Sigma did not alter the names of encrypted files, the latest version adds an extension of four random characters. So, a file called Expenses.txt would become something like Expenses.txt.gFte.
The Sigma ransom
The Sigma ransomware generates an attack ID. This is included in the ransom note, left on the Desktop as a file called README.txt. The note, with its errors of grammar and punctuation, reads:
What has happened to my files ? Why i am seeing this ?
All of your files have been encrypted with RSA 2048 Encryption. Which means, you wont be able to open them or view them properly. It does NOT mean they are damaged.
Solution
Well its quite simple only we can decrypt your files because we hold your RSA 2048 private key. So you need to buy the special decyption software and your RSA private key from us if you ever want your files back. Once payment is made, you will be given a decryptor along with your private key , once you run that , All of your files will be unlocked and back to normal.The note instructs the victim to install a Tor browser and then use that to go to a specific site, which has payment instructions. The ransom note also includes a reference code required in the Tor site to identify the attack.
The ransom is set at $1,000 paid in Bitcoin. That sum doubles to $2,000 if the ransom is not paid within seven days.
Preventing Sigma ransomware attacks
A Sigma attack always starts through user action. So, your main vulnerability to this ransomware lies with your user community. Institute, an information campaign, aims to dissuade users from opening attachments from unknown sources or downloading free software sites.
You need to check that your RDP ports are either closed or protected by specific rotated passwords that are not initially set by any software that opened the port.
Tools for protection against Sigma ransomware
There are three types of security software that you need to prevent or detect and block Sigma ransomware. These are:
- Next-generation AV to spot unusual behavior on endpoints and shut it down
- A vulnerability manager that includes a port scanner to spot open RDP ports
- Competent backup management software that scans for viruses before uploading files
For four examples of suitable security packages to guard against Sigma ransomware, try the following four tools.
Our methodology for selecting Sigma ransomware protection systems
We reviewed the market for ransomware protection tools and analyzed the options based on the following criteria:
- Anti-malware packages that protect Windows computers
- Email scanning to discover infected attachments
- Blocks unauthorized programs from accessing the CPU to launch
- File integrity monitoring to alert for file name changes or encryption
- Detection of lateral movement
- A free trial or a demo service to enable cost-free assessments
- Value for money from a service that has a fair price considering the functions that are on offer
With these criteria in mind, we have selected a range of solutions that should be able to defend your Windows computers against the next incarnation of Sigma ransomware.
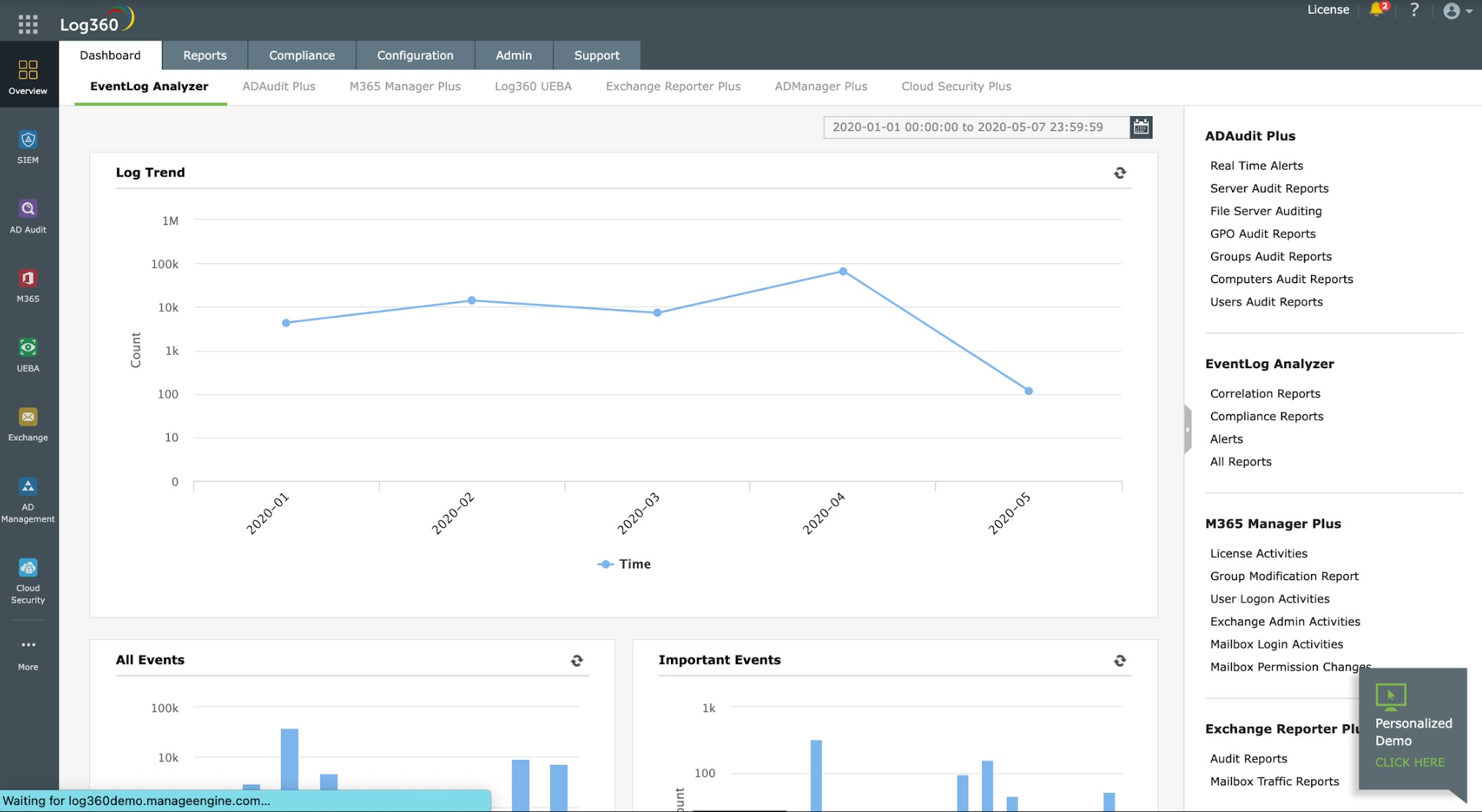
1. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 includes a combination of security systems, called a threat intelligence platform. The “platform” part of that term doesn’t imply that this is a cloud service as it installs on-premises. Instead, the tool operates as a SIEM by examining all of the log files produced by the equipment and software on your system. This capability isn’t limited to logs generated on Windows computers. It is also able to gather information from Linux systems and cloud services.
Key Features:
- SIEM: Collects logs and scans them for threats
- AD Auditing and Protection: Cleans up abandoned accounts
- File Integrity Monitoring: Can block file changes automatically
- Data Loss Prevention: Identifies sensitive data and tracks its files
- Security Orchestration, Automation, and Response (SOAR): Interacts with other security tools
Why do we recommend it?
ManageEngine Log360 is a large package of security and compliance tools. It includes a SIEM to spot threats and a file integrity monitor to protect files. The initial actions of ransomware involved copying and renaming files before encrypting them. The file integrity monitor will spot when that phase begins, trigger the SIEM and provoke preventative measures.
The Log360 also analyses and monitors Active Directory. It identifies incorrect or lose permissions structures and then watches the activity on each account. The system is also able to interact with firewalls to gather information and also to block malicious traffic.
The threat detection procedures in Log360 will detect Sigma ransomware activity before it starts its encryption phase. A threat intelligence feed constantly updates the service, so it will know what to look for. The Log360 system will then interact with other services to block Sigma ransomware processes and shut them down.
Who is it recommended for?
This is a large package of tools and it can provide most of the systems that a security operations center (SOC) needs. So, this is a bundle that will appeal to a large organization that is tooling up a central system management team. All of the software runs on Windows Server.
Pros:
- Great Dashboard Visualizations: Ideal for NOCs and MSPs
- Integrate Multiple Threat Data Streams: Provides multiple perspectives simultaneously
- Automated and Manual Log Analysis: Search through live events and analyze past logs
- Provides Cross-Platform Monitoring: For Windows, macOS, Linux, and Unix systems
- Configuration Change Monitoring: Prevents privilege escalation
Cons:
- No SaaS Option: This package is only available for on-premises installation on Windows Server
Log360 installs on Windows and Windows Server There is a free version that is limited to monitoring five devices. The full version can be assessed on a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Log360 is our top pick for a Sigma ransomware protection system because it includes file integrity monitoring, which will trigger an alert if files are renamed or encrypted. The service can set up shadow copies for unauthorized changes on protected files, which means that destroyed files can easily be restored through processes that are built into the operating system. The package also implements log collection for threat hunting. This will identify threats on any part of the system and can also spot attempts at lateral movement or rogue connections that attempt to contact C&C servers. The package also provides automated remediation actions that are managed through playbooks and it can call in third-party security systems to achieve that goal.
Download: Download a 30-Day Free Trial
Official Site: https://www.manageengine.com/log-management/siem-solution-log360.html
OS: Windows Server
2. ManageEngine Endpoint Central (FREE TRIAL)
ManageEngine Endpoint Central is a monitoring and management package that tracks the performance of computers and mobile devices. The system is designed for use by IT departments. ManageEngine provides an Anti-Ransomware unit, which is an add-on to the Security Edition. There are five editions for Endpoint Central and the Security Edition is the highest of these. It includes all of the features of the four lower plans.
Key Features:
- File Backup Service: Automatically recovers damaged files
- Security Scanning: Continuous vigilance
- Spots Ransomware: Detects all malware activity
- Protects Windows PCs: Will guard against Sigma ransomware
Why do we recommend it?
ManageEngine Endpoint Central provides extensive task automation for setting up and supervising endpoints. The Anti-Ransomware unit is an add-on for the Security Edition of the package, so you get a full system security and data protection service with this package. The Anti-Ransomware service is currently free to use.
The Anti-Ransomware add-on is built around a file backup service. The tool provides constant process scanning looking for unknown programs that could be malicious. The system simultaneously watches file statuses. If a process changes a file, it is killed and the original file is restored. This procedure automatically mitigates the damage of ransomware.
Endpoint Central will manage computers running Windows, macOS, and Linux. It also manages mobile devices and IoT equipment that run Linux, Chrome OS, iOS, Android, and tvOS. However, not all functions are available for every operating system. The Anti-Ransomware service will only run on Windows.
Who is it recommended for?
Endpoint Central has a server and endpoint agents. The server is available as a SaaS platform or as software for Windows Server. Small businesses can opt for the Free edition to protect up to 25 endpoints. However, this does not qualify for the Anti-Ransomware unit. You have to opt for the top paid plan, the Security Edition to get the Anti-Ransomware add-on.
Pros:
- Live Monitoring: Constantly scans endpoints for suspicious processes
- Supplements Data Loss Prevention Software: Controls file movements
- Logging for Compliance Reporting: CIS, ISO 27001, PCI DSS, GDPR, HIPAA, and NIST
- Free to Use: Currently is in Beta release
Cons:
- Only Operates on Windows PCs: However, this is the target for Sigma ransomware
The Anti-Ransomware unit is currently in pre-release and is currently free to use. The company will charge for the add-on once it has passed its Beta phase. You can only get the tool as an add-on for the Security Edition, which is the most comprehensive and most expensive edition of Endpoint Central. You can get Endpoint Central as software for Windows Server or as a SaaS package. ManageEngine offers the Security Edition of Endpoint Central on a 30-day free trial either as the SaaS version or for installation. The free trial gets you access to the Anti-Ransomeware service.
3. CrowdStrike Falcon Insight
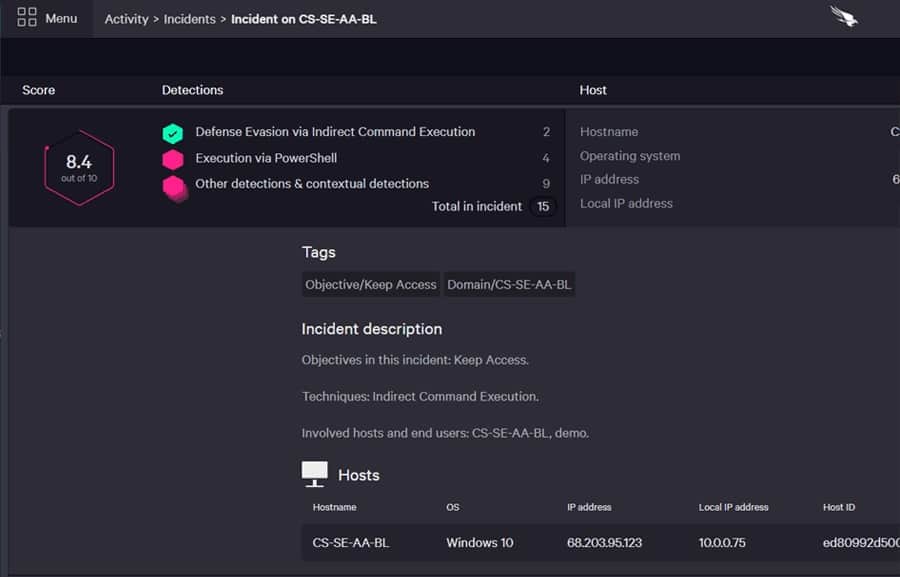
CrowdStrike Falcon Insight includes Falcon Prevent, which is a next-generation antivirus system. First, you install the Prevent module on each endpoint. This will monitor activity, establishing a baseline of normal behavior. If unusual activity occurs, such as the routines of Sigma ransomware, Prevent will shut down those processes and isolate the device from the network to stop the malware from spreading.
Key Features:
- Hybrid System: On-device and cloud
- Autonomous Endpoint Protection: Implemented by Falcon Prevent
- Company-Wide Threat Hunting: Centralizes activity data from all endpoints
- Blocks Lateral Movements: The central unit informs all endpoints if one is attacked
Why do we recommend it?
CrowdStrike Falcon Insight is a company-wide threat detection and response system. The package is split between an on-device antivirus unit and a cloud-based threat hunting service. However, the two levels interact as the on-device system, called Falcon Prevent, can continue working independently if it is disconnected from the network.
What makes Insight better than Falcon Prevent is a cloud-based controller. This acts as a SIEM service, gathering log files and activity reports uploaded by each Falcon Prevent instance. A threat intelligence feed informs the Insight service, and it performs secondary scans of activity by looking through the log files.
Insight passes on threat information between endpoints and also threats identified centrally. Each Prevent instance can carry on working even if the device is disconnected from the network. The endpoint protection extends to remediation actions to stop Sigma ransomware from progressing to its encryption phase.
Who is it recommended for?
This system is suitable for mid-sized to large organizations. The package is easy to expand as you just need to buy another copy of Falcon Prevent to get another endpoint included in the coverage of the Insight threat detection service. Responses can be implemented by coordinating with third-party tools.
Pros:
- Excels in Hybrid Environments: Windows, Linux, cloud, BYOD, etc
- Intuitive Admin Console: Makes it easy to get started and is accessible in the cloud
- Cumulative Activity Monitoring: Can track and alert anomalous behavior over time, improves the longer it monitors the network
Cons:
- Would Benefit from a Longer Trial Period: The free trial only lasts for 15 days
You can get a 15-day free trial of Falcon Insight.
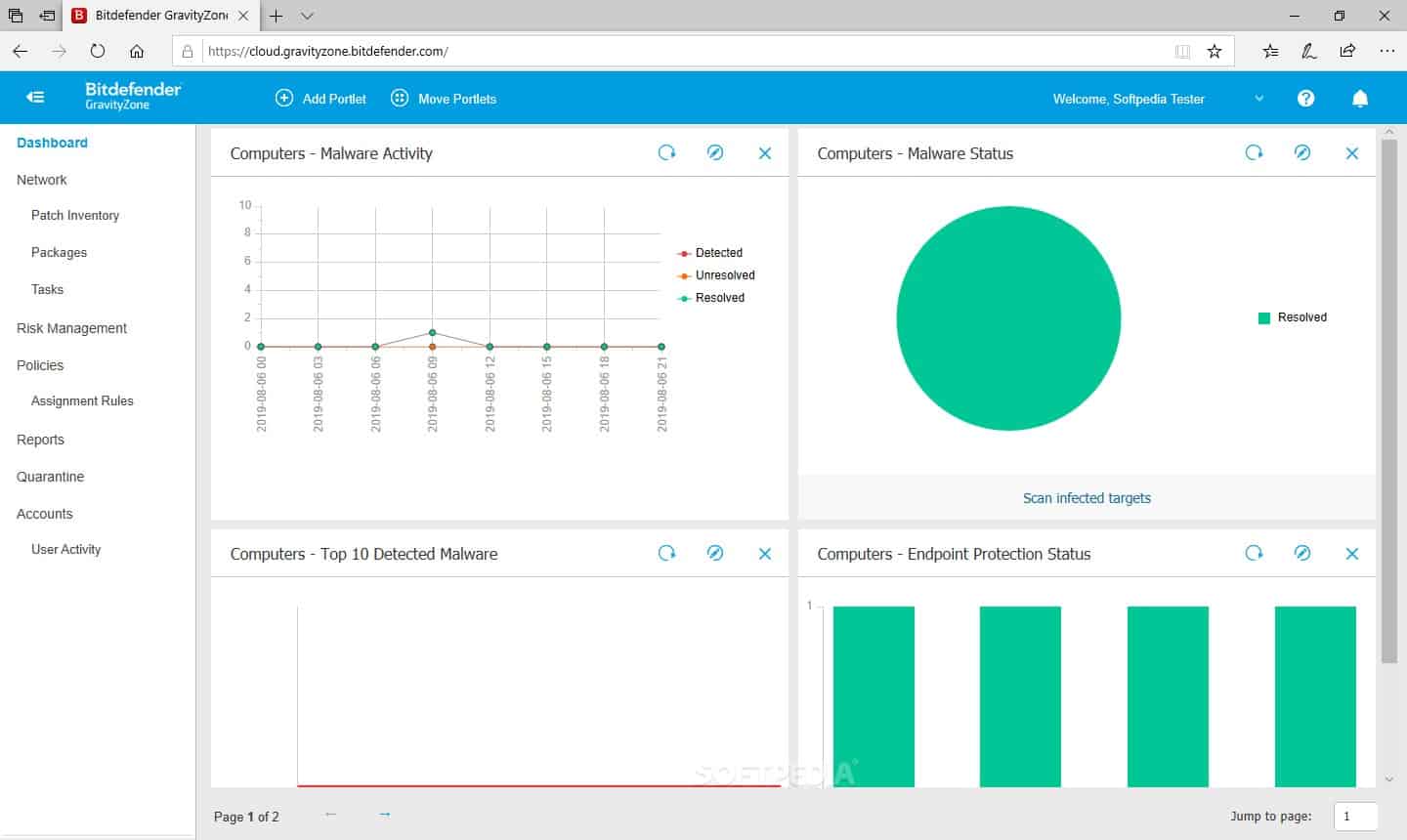
4. BitDefender GravityZone
BitDefender GravityZone is a bundle of several security systems. This includes antivirus packages that are deployed at several points on the system, including endpoints. There is also a vulnerability scanner and patch manager in the bundle and a service to scan ports. These systems will block Sigma ransomware from getting on an endpoint and spreading around the network.
Key Features:
- Security for Email: An add-on unit
- Anti-Malware: Blocks ransomware as well as other malware types
- Backup Service: Stores copies of files so that they can be restored
Why do we recommend it?
BitDefender GravityZone is a package of security systems that are ideal for combating ransomware. The vulnerability manager and port scanner ensure that your system is resistant to attack and fixes for discovered problems are partially addressed by the automated patch manager in the package. An antivirus service spots and removes ransomware before it triggers.
The processes of GravityZone aren’t designed just to catch Sigma ransomware. Instead, the service can block all types of malware from causing damage and will continue to be effective whenever new threats emerge.
An essential service in the GravityZone bundle is its backup manager. This scans each file for infection before uploading it. With a safe backup of all of your files, you can safely recover from any ransomware attack without having to pay the ransom.
Who is it recommended for?
BitDefender markets GravityZone for small to medium-sized businesses. The package is priced per device and there is no minimum order quantity, so even a single-screen home office is catered for. The package can be extended by add-ons, such as an Email Security service.
Pros:
- Multiple Detection Rules: Uses both signature-based detection and behavior analysis to identify threats
- Patch Management: Deals with discovered weaknesses in supplied software
- Includes Device Control Options: Locks down USB ports
Cons:
- Could Use More Documentation: Would help users get started quicker
GravityZone operates as a virtual appliance, and it is available for a one-month free trial.